One of the key tenets of cyber threat intelligence is the ability to work proactively, identifying current threats and assessing what might be coming over the horizon. We’ve previously referred to this as staying “left of boom”—taking actions to minimize and disrupt malicious activity before it occurs. After all, prevention is always a better approach than remediation.
While the security community has been focused on the fallout from the , it’s also important to look at what’s occurring across the rest of the cyber threat landscape.
The following blog is a summary of some of our findings on the most common MITRE ATT&CK tactics and techniques that we have observed in customers’ alerts from Jan – Jun 2023. This report also covered the most common GreyMatter Digital Risk Protection (GMDRP) alerts, which detail common exposures and threats related to a company’s assets.
Most-Observed Technique: Phishing
We observed that Phishing (T1566), including Phishing for Information (T1598) and Internal Phishing (T1534), was the most common technique involved in alerts triggered in customer environments between January 1, 2023, and June 30, 2023. This can be seen in Figure 1 below, highlighted as a percentage of all detected techniques. Despite advancements in email security solutions, phishing remains one of the most common methods of obtaining initial access and is used by a variety of threat actors, including financially motivated cybercriminals and nation-state-aligned threats.
Phishing—in addition to a raft of other social engineering attacks—works because it’s simple, cheap, and can easily be adapted to the target; of course, with the introduction of artificial intelligence, it’s likely that this will only become simpler. There are many approaches an attacker could take, and the methods to entice a user into interacting with a phishing email are only limited by the threat actor’s creativity.
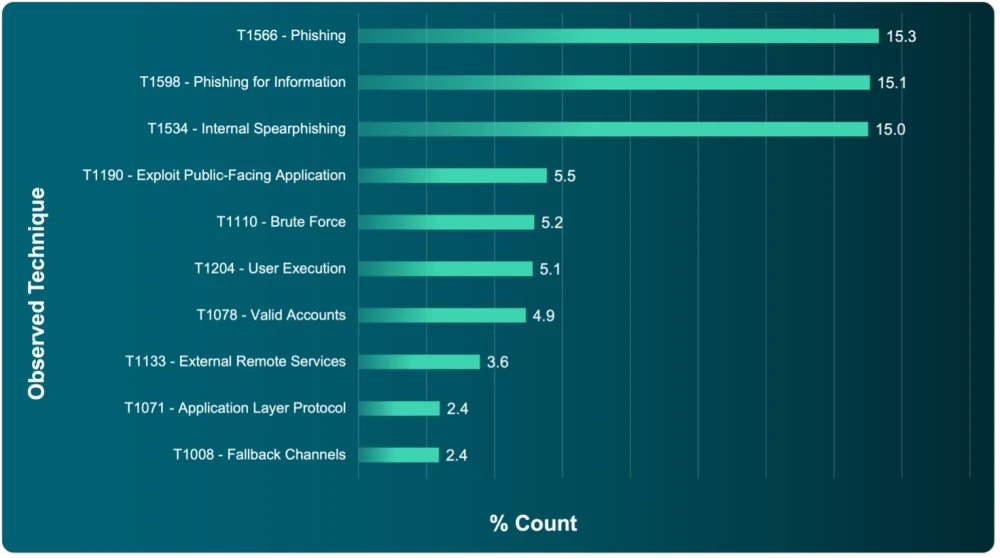
Figure 1: Most commonly observed MITRE ATT&CK techniques during the reporting period
Case in point: Threat actors have developed phishing-related techniques in response to the changing cyber threat landscape. Microsoft’s February 2023 decision to block macros in Office documents by default preceded an increase in HTML smuggling, whereby a threat actor leverages legitimate HTML5 and JavaScript features to deliver malware, remote access trojans (RATs), or other payloads to targeted mailboxes via phishing emails. The emails contain a specially crafted HTML attachment or web page that, when opened, downloads the payload to the victim’s device. At the start of 2023, we noted a that redirected the recipient to a convincing spoofed Microsoft website, almost certainly in a ploy to harvest credentials.
Steps You Can Take
The key takeaway here is that phishing is easy and effective. A combination of human curiosity and control failures leaves a significant opportunity for a huge range of threat actors. Don’t get caught out—Here are a few things you can do to make it more difficult for them.
Ensure email gateways are correctly configured to quarantine suspicious mails.
Run security awareness programs.
Make sure that multi-factor authentication is enabled, in case the worst occurs and employees’ credentials are stolen.
Exposed Remote Services Leave the Door Open for Attackers
Although not the highest entry in our data set, another noteworthy and commonly seen technique relates to the attempted exploitation of exposed remote services (T1133). This is also something we’ve frequently named as one of the , affecting instances of Virtual Private Networks (VPNs) and Remote Desktop Protocols (RDPs) alongside other technologies, like Citrix and TeamViewer. We also identified exploitation of remote services as the most common technique in our .
Our research on high-profile cybercriminal platforms also indicates that exploiting externally exposed remote services is a popular technique among cybercriminals. This is a common but effective tactic for gaining initial access to internal enterprise network resources from an external location or for establishing persistence. Initial Access Brokers (IABs) perpetuate a flourishing market in remote service credentials to a variety of organizations, particularly in an age of increased hybrid working. Some IABs employ brute-force attacks that exploit weak or default credentials, while others take advantage of unpatched vulnerabilities to gain access.
Ransomware groups remain one of the most common buyers of stolen remote service credentials, including Lockbit, who continue to hold the largest market share of all ransomware activity. identified significant use of RDP for internal lateral movement in a targeted network. If extortionists steal your RDP service credentials and you fail to detect the theft in time, you could soon be dealing with a highly impactful incident.
Steps You Can Take
Reducing the attack surface of remote services is critical to lowering an organization’s cyber risk.
Ensure that remote services aren’t unnecessarily exposed to the internet or have weak or default credentials.
Make sure they can only be accessed by those who need to, e.g., by implementing an access control list (ACL) for your RDP instances to limit who can access these services. You wouldn’t leave your home’s doors unlocked at nighttime, so why do the same on your network?
Firing From the Hip: Password Spraying
A commonly observed sub-technique relates to the use of Password Spraying (T1110.003) and Password Guessing (T1110.001). Adversaries can try to guess passwords to access accounts, either by systematically using a repetitive or iterative mechanism or a list of commonly used passwords; the resultant repeated authentication failures may lead to account lockouts. Password spraying, on the other hand, uses a single or small list of commonly used passwords against many different accounts, to avoid account lockouts resulting from targeting a single account with many passwords.
Password guessing and spraying can affect any region, sector, or technology, depending on an organization’s rules for the number of permitted authentication attempts. These techniques’ success, even among low-skilled attackers, results from:
The endemic issue of password re-use (particularly mixing credentials across corporate and personal accounts)
Weak and easily guessable passwords
Failure to change default passwords
This is nothing new: , we investigated factors behind and rates of credential theft, discovering an alarming increase in the number of exposed credentials that were collated within our repository. By June 2022, this collection contained over 24 billion credentials, representing a substantial 65% increase from 2020.
It’s possible that the introduction of PassKeys—which include biometric sensors like facial identification and fingerprints—will make a big difference on lowering the risk associated credential use. These changes are however slow to be introduced, with the majority of logins still being conducted through traditional username and password-based authentication. This demonstrates why password spraying and guessing are still widely used techniques.
Steps You Can Take
Password spraying and similar attacks can be easily remediated with a few simple controls.
Create strong passwords capable of withstanding rudimentary cracking techniques.
Store credentials in a single safe location, while being regulated for their use—including changing if detected within a breach.
The best way of achieving these goals is A password manager is a dedicated online service or locally installed software that stores all your passwords. This is typically protected by a strong master password that you need to enter to gain access to all your other credentials. These useful pieces of software can assist in mandating sufficient password complexity, while also alerting users to any known detections of a breach of their username or password. They’re typically either free or purchasable for a small price, which is well worth the cost.
Improving Your Resilience to Common Threats
Within our GreyMatter security operations platform, ReliaQuest customers benefit from a robust detection library of commonly used attacker techniques, including the three mentioned above. This enables our customers to work towards comprehensive coverage, which exists within a defense-in-depth model.
Regularly reviewing limitations to proactively address them enables ReliaQuest customers to maximize their security operations. ReliaQuest GreyMatter can take the blinders off the eyes of your security teams, providing greater insights into which techniques you need to prioritize for remediation.
To learn more, visit www.reliaquest.com. Set up a custom demo to walk through your environment and learn how ReliaQuest can help.





