To coincide with our new, globally available GreyMatter Phishing Analyzer (GMPA) product—which will enable a much more efficient method of automating analysis of potential malicious emails—we’re starting a new series in which the ReliaQuest Photon Threat Research team will highlight several of the most common methods threat actors are using to bypass traditional email security controls to compromise targets.
First in the series is a common yet effective technique called HTML smuggling, an evasive malware-delivery mechanism. This allows threat actors to leverage legitimate HTML5 and JavaScript features to smuggle malware, remote-access trojans (RATs), or other payloads to targeted mailboxes. This is delivered through a specially crafted HTML attachment or web page, which, when opened, uploads the payload to the victim’s device. Check out our observations on this technique below.
HTML Smuggling: How It Works
HTML smuggling is a commonly used technique associated with a wide variety of threat groups, including cybercriminals and nation-state actors. This is not a novel technique; however, it has become more commonplace following Microsoft’s decision to block macros in Office documents by default. Many would suggest this decision was overdue; however, threat actors, rather unsurprisingly, quickly adapted.
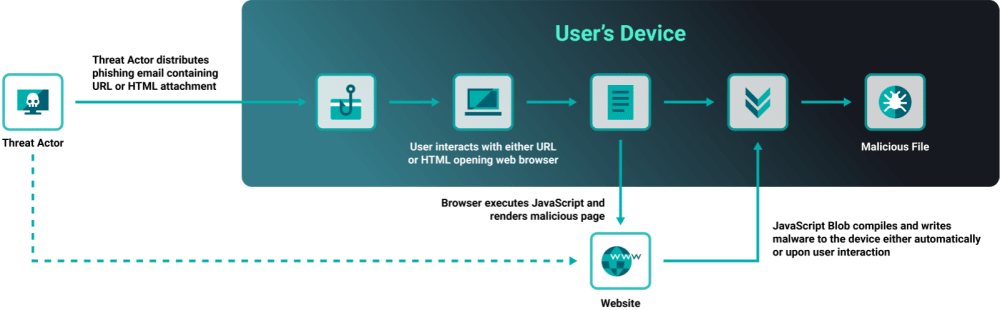
HTML smuggling works by allowing threat actors to deliver a phishing email with a URL or HTML attachment, permit execution upon the user interacting with the file, which is then decoded by a browser before loading a website. JavaScript binary large object (BLOB)—which acts in this case to embed/reconstruct large files—then downloads the payload and assembles on the targeted device. This can bypass traditional email security controls, which typically only check emails for the usual suspicious attachments—such as executables and ZIP files—or through traffic-based analysis. One more important thing to note: the reconstructed file is built client-side, and therefore the download event will not be logged by firewalls, forward proxies, or Windows event logs.
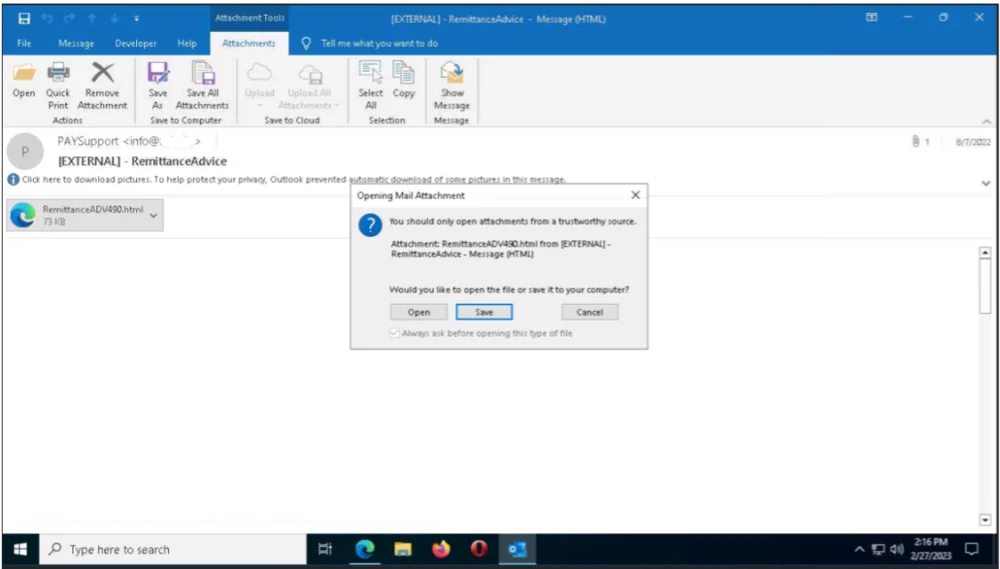
A good example of this can be seen in the screenshot below (Figure 2), which was recently delivered to a ReliaQuest client mailbox. This HTML file requests that the user interact with its content, using a theme of “Remittance” as the bait.
This then redirected the user to a convincing spoofed Microsoft website (see Figure 3 below), which in this case was almost certainly used to harvest credentials. As we previously observed during our research report on account takeover, credential harvesting is often pretty simple, but it works.

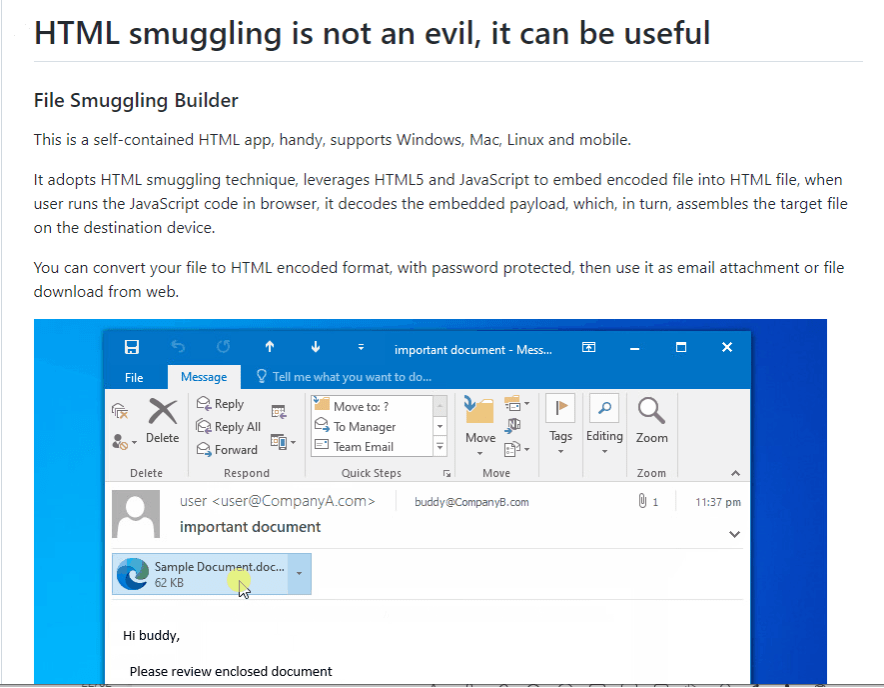
How easy is this to achieve? The bar is low, and through some simple searching, we identified several open-source and builders dedicated to HTML Smuggling and how it can be achieved. The example below (Figure 4) was developed in the program and leverages HTML5 and JavaScript to embed encoded file into HTML file. This self-contained application works on most operating systems and, judging by the title, appears to have been designed for legitimate uses—possibly for testing the strength of developers own controls. Of course, since the file is available in open source, the developer doesn’t discriminate who can use it, whether that’s malicious or benign users.
Minimizing the Risk of HTML Smuggling
There are several steps you can take to minimize the risks associated with HTML smuggling.
Establish a group policy object (GPO) that forces commonly abused files—in this case HTML—to open by default in a text editor like Notepad instead of a browser. Testing of these controls is recommended to ensure they don’t impact business function.
User awareness: As we commented earlier, victims can be socially engineered, so make sure your security training adequately details the risks of clicking links. Training needs to include executive-level employees and departments that are frequently phished, including finance and human resources.
Enable employees to proactively report suspicious emails. In many campaigns, multiple victims in an organization will receive the same phishing email. Even if just one employee reports a suspicious email, it will increase the likelihood that your security team can act before someone else makes the mistake of clicking the link.
Harden perimeter security to restrict company assets from making arbitrary connections to the internet. This may be accomplished through firewall or proxy configurations.
Monitor for newly constructed files via JavaScript, developing rules for the different variants, with a combination of different encoding and/or encryption schemes, may be very challenging. Consider monitoring files downloaded from the Internet, possibly by HTML Smuggling, for suspicious activities. Data and events should not be viewed in isolation, but as part of a chain of behavior that could lead to other activities.
GreyMatter Phishing Analyzer
GreyMatter Phishing Analyzer takes the burden of monitoring abuse mailboxes off your plate, and it provides the ability to identify and remove email threats from inboxes before they can cause damage. You don’t want the HTML smuggling technique to be the beachhead that allows initial access into your environment.
Watch Phishing Analyzer in Action
To learn more about the email phishing landscape (presented by our Photon Research Team) and see GreyMatter Phishing Analyzer in action, register for our webinar on March 22, 2023.