Updated July 28, 2023, 10:00 a.m. ET
Clop is still adding organizations to its victim list. As of today, the total count is over 250 organizations, which makes this ransomware campaign one of the most impactful we’ve ever seen.
As this has proved to be a long-term campaign, we will no longer be updating this page. For a deep-dive into Clop and their methods, check out our , which we released today. We also sum up the campaign so far in the , also new today.
July 5, 2023, 1:00 p.m. ET
Clop isn’t done yet. Since our last post, Clop has named 36 additional organizations, including 10 just today, spanning the insurance and technology industries, as well as others. The US majority has held: over 80% of the newly named organizations do business in the United States.
As for leaks, Clop has tended to release data in the same order as it’s named organizations, with about 10 days between the initial naming and the release of data. That’s (sort of) good news for the newly named organizations as they’ll have a little bit of time to plan—but for those named earlier in the cycle, the pressure is on.
A few organizations have been redacted as well, so we won’t expect to see leaks from them.
We have yet to see signs of slowing down on the Clop front. We’ll continue to update here until things stabilize, when we’ll release a post covering the whole situation.
June 26, 2023, 5:00 p.m. ET
Since our last update, Clop has continued carrying through with its ransom threats. As of now, they have leaked the business information of six more of the named organizations.
There have been no new organizations added to its ransom list so far.
June 23, 2023, 3:00 p.m. ET
Since we last posted:
Two new organizations were named on the Clop data-leak site, bringing the total number of named organizations (including redactions) to 58. While that number is not as high as the total victim count of Clop’s GoAnywhere attack, the organizations themselves are larger, indicating that Clop may be going for quality over quantity this time around. That said, the full story of the MoveIT vulnerability has yet to unfold—we don’t yet know exactly how many organizations have been affected.
As we expected, Clop has continued leaking proprietary data belonging to the organizations it has named so far. Today, five companies saw their business data leaked.
We’re still watching the situation closely and will continue to provide updates here.
June 22, 3:00 p.m. ET
Clop has been busy today. At the time of writing, they’ve added four new organizations to the ransom list, including two accounting firms and one technology company.
They’ve also resumed leaking data from two organizations, and they’ve newly begun leaking data from one other. We expect to see the leaks continue—Clop has claimed that they have terabytes of data from the organizations they’ve listed.
Updated June 21, 5:00 p.m. ET
Since we last posted:
One new organization was named on the Clop data-leak site but was then promptly removed. No other organizations have disappeared from the ransom list.
Clop has released the data of two more organizations.
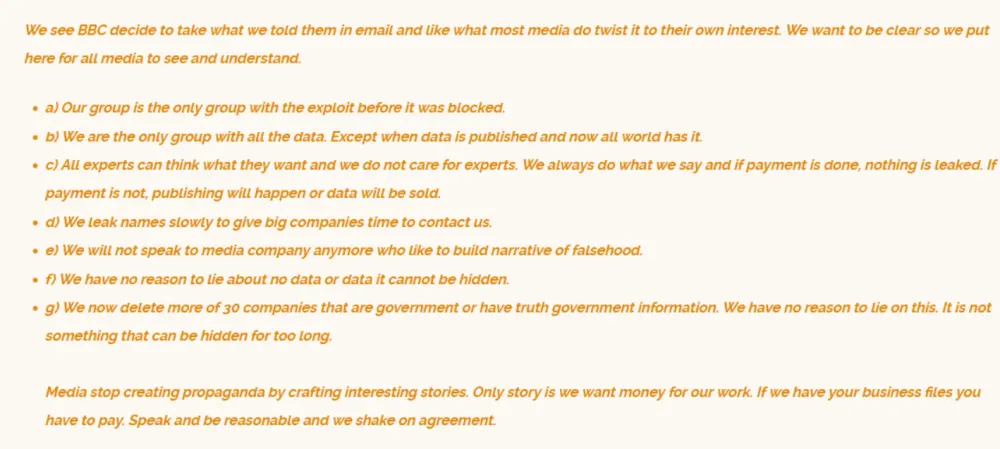
Additionally, Clop posted a message (shown below) on their site claiming they were misrepresented by the media. “Only story is we want money for our work.”
June 20, 2023, 4:00 p.m. ET
Clop has not listed any new organizations on its ransom list as of today.
Clop has removed one more organization from the list and confirmed that they’ve deleted all the company’s data, bringing the total number of redacted organizations to 5.
They also claim to have leaked data for a third company today—interestingly, instead of leaking it piecemeal as they have with the others, they leaked the full dataset all at once.
We’ll update here as new details emerge.
June 19, 2023, 1:00 p.m. ET
Clop listed 11 additional organizations since our last update on June 16, 2023. In addition, they also leaked data allegedly belonging to one of the newly named organizations. This is the second instance of a data leak related to the MOVEit MFT exploits and the first time Clop leaked data at the time of publicly naming the organization. This is likely the result of failed negotiations. The latest list also included the first named Australian organization.
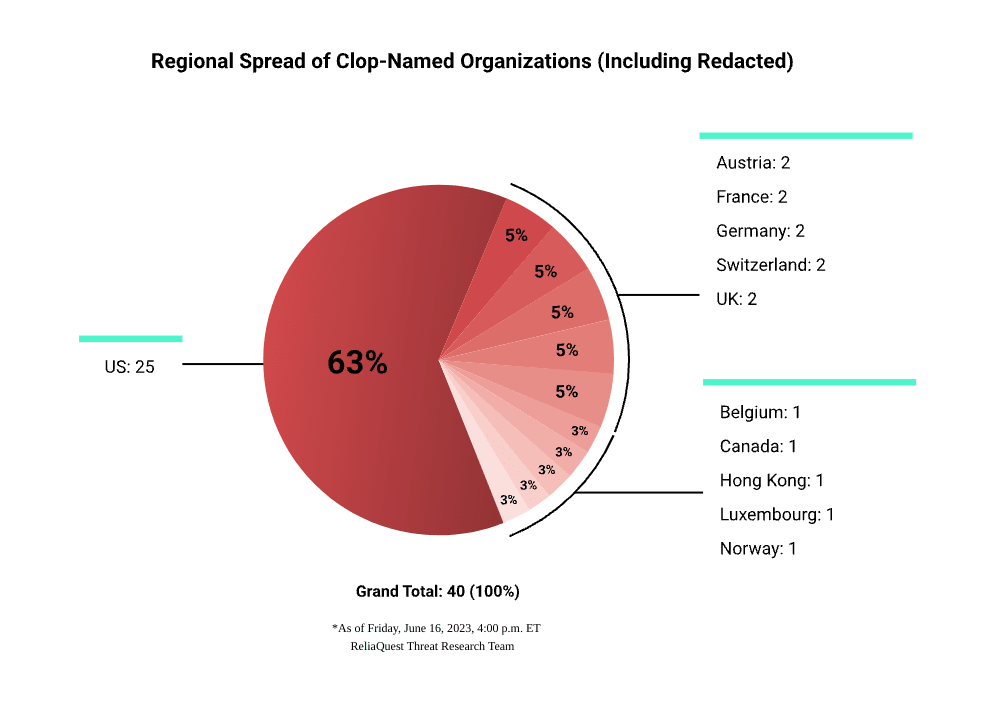
Updated June 16, 2023, 4:00 p.m. ET
Since our last post, Clop has listed three new organizations and removed two others, bringing the running total to 40 organizations on its list. We also saw the first possible instance of leaked data after one named organization apparently refused to engage in negotiations, according to the Clop site.
It’s possible that we will continue to see leaks from other organizations as the Clop-instituted deadlines come and go or as companies decline to work with Clop.
June 16, 2023, 10:30 a.m. ET
Clop has named 10 additional organizations as being impacted by its attack, including the first listed from Asia.
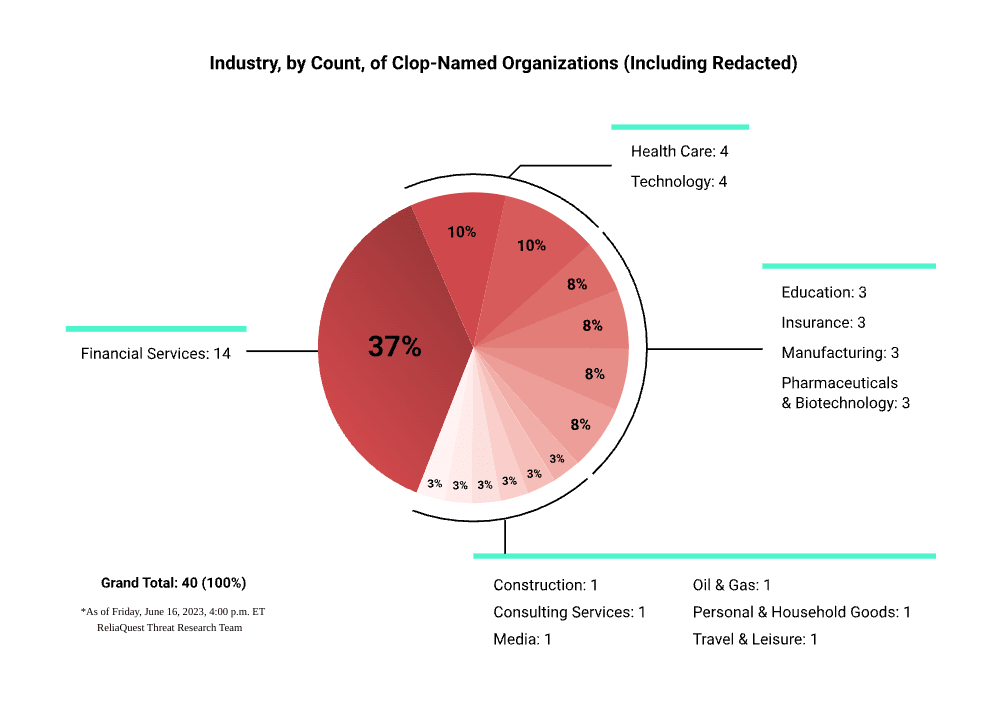
In the past two days, Clop has listed a total of 37 organizations spanning most of the northern hemisphere, with most in the US (23). Organizations named also represent a broad swath of industries, including financial services (14), healthcare (4), and pharma/biotech (4). (Note that these are not final numbers and may have changed since the time of posting.)
We believe this to be a large-scale attack, with the potential to surpass Clop’s previous GoAnywhere and Accellion attacks, and there could very well still be more named organizations to come.
We’ll continue sharing additional information here as it’s released.
June 15, 2023, 1:15 p.m. ET
14 additional organizations listed. No data leaks yet.
As of 1 p.m. ET, Clop has named 14 new organizations, bringing the total number to 27. Of the newly named organizations, 11 are from the US and 3 are from Europe (one each from France, Switzerland, and Luxembourg). The organizations listed are predominantly operating in financial services, followed by healthcare, pharmaceuticals, and technology. The list of company names has been published on Clop’s dark-web data-leak site, >_CLOP^_-LEAKS, although the group has removed one name. As of this update, we are not aware of any leaked data.
The number of potentially breached organizations so far is significantly greater than the initial number named as part of Clop’s last MFT exploitation: the Fortra GoAnywhere MFT campaign (CVE-2023-0669). Clop named 7 organizations in the first week of posting GoAnywhere victims, compared to 13 MOVEit Transfer victims in the first 24 hours of release.
Although we haven’t yet seen any of the major organizations that previously disclosed MOVEit Transfer breaches named on >_CLOP^_-LEAKS, it is highly likely that Clop is just getting started naming possibly compromised organizations. Clop continuously ramped up naming GoAnywhere victims, releasing 26 between March 13 to 20, 2023. From March 17 to 31, 2023, it named an additional 91 organizations, 52 of which were named in a single day on March 24th, 2023.
It’s possible that we’ll see similarly large dumps of organization names in the coming weeks. According to Shodan, over 2,500 MOVEit Transfer instances were vulnerable to exploit, more than double the 1,000 exposed instances of GoAnywhere. On the flip side, though, there’s hope that companies have implemented some lessons learned from the GoAnywhere MFT compromise, which would minimize the extent of the MOVEit Transfer attacks. For more information on mitigating the risks posed by MFT solution, see our blog MOVEit Vulnerability Update: Clop Claims Responsibility.
June 15, 12:20 p.m. ET
Clop has begun adding new organizations to their list of ransomware victims. At the time of writing, there are 11 new organizations named from across the US and Europe. We will continue to update this space as new information breaks.
June 15, 2023, 9:00 a.m. ET
We have observed no new activity. We may see further updates later today, so we will continue to watch closely and provide analysis at that time.
June 14, 2023, 8:00 p.m. ET
We have no additional information at this time. We’ll continue to monitor the situation and our next update will be at 9:00 a.m. ET.
June 14, 2023, 6:00 p.m. ET
We haven’t seen any further activity since our last update. We are watching closely and will continue to provide the latest news in this post.
June 14, 2023, 4:00 p.m. ET
Since our last update, Clop has disclosed one additional organization and removed another from its ransom list. We can only speculate why Clop removed the organization, but it could be that the organization engaged in ransom negotiations.
We continue to monitor the situation and will provide regular updates here.
June 14, 2023, 1:00 p.m. ET
All eyes have been on the “Clop” ransomware group’s data-leak website since the group took credit for attacks exploiting the MOVEit Transfer zero-day vulnerability (CVE-2023-34362). On June 6, 2023, the data-stealing extortionists stated that MOVEit Transfer victims had one week to contact the group and begin negotiations. The group threatened to publicly name and shame victims if no ransom was paid, and then leak their data on the data-leak site, >_CLOP^_-LEAKS.
On June 14, 2023, Clop named its first batch of 12 victims. No victim data has been leaked at the time of writing. As the ReliaQuest Threat Research Team continues to monitor the site for more updates, let’s dig into what we’ve seen so far.
Clop data leakage website as of 1:00 PM EST on June 14, 2023
What We Know So Far
As of 1 p.m. EST on June 14, 2023, Clop has named 12 victims on its dark-website, but the group is actively adding new victims. So far, the majority of victims named are from the US. Other victims are from Switzerland, Canada, Belgium, and Germany. Expect to see more of Clop’s new victims named throughout the day.
Traditionally, Clop mostly targets organizations in the US, followed by Canada, the UK, and Germany. So far, the MOVEit Transfer victims have been consistent with Clop’s previously targeted victims. Before the MOVEit Transfer leaks, most victims named on its data-leak website were involved in manufacturing (66 entities named), followed by technology (41) and healthcare (33) providers. We will continue to update on target sectors in the MOVEit Transfer leaks as victims are named.
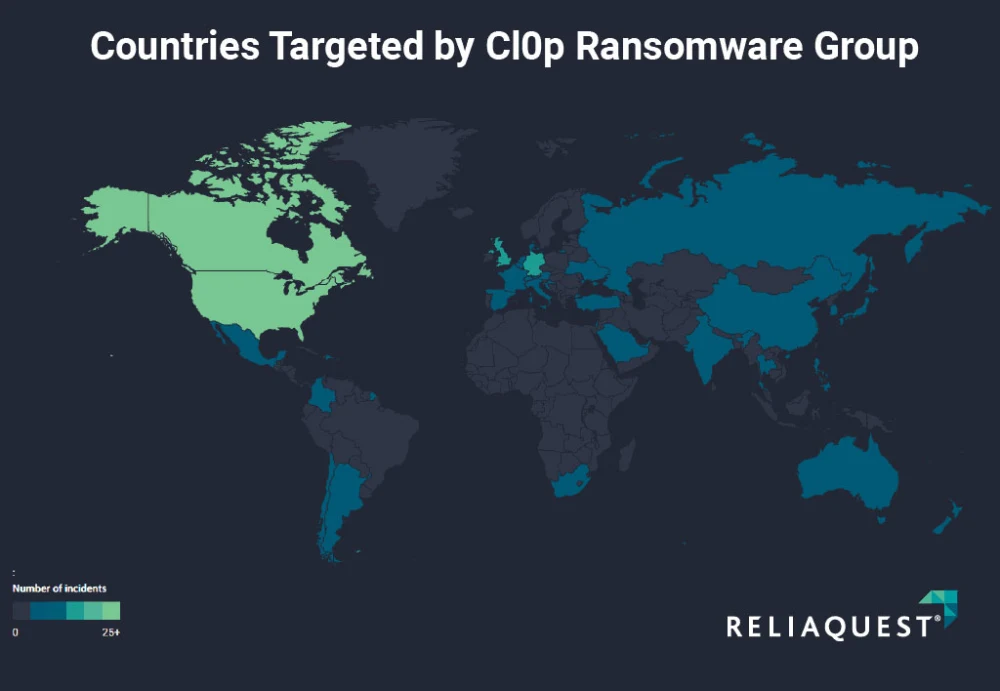
Clop’s victims shown by country on ReliaQuest’s GreyMatter platform
Clop Strays from Its MO—Sort Of
This is the third time that Clop has exploited major vulnerabilities in enterprise managed file transfer (MFT) software to target third-party victims. The previous two times were:
In February 2023, the group claimed responsibility for more than 130 attacks exploiting a zero-day vulnerability in Fortra GoAnywhere MFT (CVE-2023-0669).
In December 2020, Clop exploited zero-days in Accellion’s legacy file-transfer application software, stealing data from more than 100 companies.
In all three campaigns, Clop did not deploy its eponymous ransomware. Instead, the group conducted data extortion: It didn’t encrypt victim systems but threatened to publicly release sensitive data stolen from MFT software. These supply-chain attacks are ruthlessly efficient, allowing Clop to target hundreds of victims at once.
One area where Clop strayed from its modus operandi (MO) was in posting a mass ransom notification on >_CLOP^_-LEAKS. Usually, the group attempts to extort victims one by one. In the case of the Fortra GoAnywhere attacks, Clop opted out of mass notification to victims, instead the group individually named at least 100 victims over one month on its site.
Company named on Clop data-leak site
This change in tactics is likely to improve efficiency. Notifying victims individually is time-consuming. By putting the onus on victims to figure out if they’ve been breached and then get in touch with their extorters, Clop saves time and weeds out companies that won’t negotiate with ransomware operators from the get-go.
Although Clop has diverged from its MO when notifying victims, the group will probably operate as usual in the following ways:
Negotiations occur via a private chat room on the dark web.
The group names victims on its data-leak website (if negotiations are unsuccessful).
Data is leaked in parts until the full data set is exposed.
What’s Next?
By targeting vulnerable enterprise MFT software, Clop can efficiently compromise many organizations, even those with cybersecurity teams and budgets. We expect more companies to be named on >_CLOP^_-LEAKS in the immediate future. For those organizations that refuse to pay a ransom, we’d expect data to be leaked in stages.
With even more MOVEit Transfer vulnerabilities being released (CVE-2023-35036), future MOVEit attacks by Clop and other groups are a realistic possibility. With the group having added supply-chain attacks targeting MFT software to their arsenal, we expect similar Clop attacks in the next three to 12 months.
At the time of writing, we don’t know what percentage of all Clop MOVEit Transfer victims have been publicly named. About 2,500 vulnerable MOVEit Transfer servers were exposed on Shodan. But recent reports point to Clop having knowledge of the MOVEit Transfer vulnerability since as early as July 2021. The latest name dump may be only a drop in the bucket of the total MOVEit Transfer victim count.
After the second negotiation deadline passes (seven days after negotiations begin—meaning a fluid timeline depending on victim engagement), we should expect to see Clop out even more victims. But the real moment of truth, and opportunity to gauge the impact of the breaches, will come when Clop starts posting leaked data. Ransomware groups sometimes try to hoodwink victims into paying a ransom, falsely claiming that they’ve exfiltrated sensitive data. Until Clop starts leaking data, ReliaQuest will keep a close eye on the data-leak site.
How to Respond
In our June 7, 2023, blog, MOVEit Vulnerability Update: Clop Claims Responsibility, we outlined several ways for potential Clop victims—or any company worried about ransomware—to respond. Any organization with MOVEit Transfer versions pre-dating May 31, 2023, are vulnerable and should assume compromise if the instances were exposed online.
Clop has repeatedly targeted MFT services, making it fundamental for organizations to understand their MFT solution’s public footprint and take steps to harden their defenses. This includes restricting public MFT access to authorized users, setting up firewall rules to exclude unknown IP addresses, and quickly applying software patches.
Where ransomware is concerned, always expect the unexpected. But it’s a good bet that Clop’s exploitation of zero-days will continue in the coming year and other ransomware groups will play copycat. It’s not possible to prevent the exploitation of zero-day vulnerabilities, but effective detection and response are the best options for organizations to manage the ransomware threat.




