You may have read about the recent attack affecting motoring powerhouse General Motors (GM), that resulted in significant numbers of GM’s customers having their accounts compromised. Wedding planning company Zola was also impacted by a similar attack in the same week of May 2022, with the attackers using the compromised accounts to redeem gift cards. Exactly how did this happen? Well, it turns out that customers’ accounts were impacted by a credential stuffing attack, in which attackers took previously compromised credentials and scanned the wider internet to verify if these credentials are used across other services. In our previous blog, we likened credential stuffing to an attacker obtaining a bag full of keys and trying to unlock a series of doors; if you try long enough, you might just find one that fits. Credential stuffing is a simple yet effective attack, which we’ll detail in the following blog.
Credential stuffing lifecycle:
We all love a good flow chart, right? A credential stuffing attack works first by an attacker gaining access to a tranche of credentials—i.e. username and password combinations—which can be input into a credential stuffing tool. These accounts might be your social media accounts, your work portal, or a login to your online bank account. Our recent research report covering the wider topic of account takeover (ATO) covers many of the methods actors use to initially steal accounts, which are mostly conducted through social engineering, malware, or simply by purchasing or renting off other threat actors. This initial step is represented on the attack lifecycle graph below.

Credential stuffing attack lifecycle
Once an actor has accounts—which often involves tens of thousands of accounts at a time—they can kick start their credential stuffing tool of choice. The example provided in our research report was OpenBullet, which is one of the most commonly used; there are however a huge number of alternative credential stuffing tools available for cybercriminals, which are typically available either for free or for as little as $20.
As you’d expect, making repeated login attempts in a very short space of time is likely to set off all kinds of alarm bells on online services, so threat actors are required to use proxy IP addresses to obfuscate the nature of their activity. Proxies essentially allow actors to make multiple login attempts using different IP’s, thus making it more difficult to identify that your service is under an attack. Without proxies, a credential stuffing attack would fail pretty quickly. This also applies to password spraying attacks, which involve testing multiple commonly used passwords against a user account, rather than applying a known credential combination that has been identified as in use at another service. While we’re on the topic, credential stuffing should also be thought as separate to brute forcing attacks, which rely upon guessing the password combination for a given username, and has no prior context before the attack is conducted. With that in mind, it’s likely that credential stuffing will encounter more success than brute forcing or password spraying attempts.
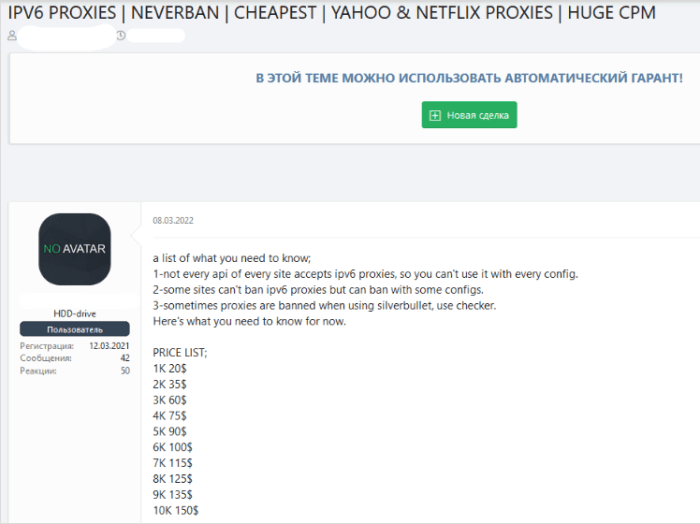
As you’d expect, proxies are typically sold for fairly cheap prices on cybercriminal forums. Actors will often be required to use certain proxies across individual services (dependent on the security processes of the service being targeted), which can also be seen reflected in the example below.
Another absolutely vital component of a credential stuffing attack is the attacker gathering configs for the target service. Config files contain instructions for automating certain actions, usually for web resources. They include metadata (like a name, an author, and an icon) that acts as a README file showing how to use it or what it’s for, some settings, and instructions. In
essence, a config tells the credential stuffing tool where to direct its usernames and passwords, and how to determine whether it has successfully logged in or not. Session cookies are also often required in order to ascertain that the login attempt has not been made to a new device; if purchasing configs from another actor, they’ll usually provide these in the same package.
Once the configs have been established for a targeted service, the threat actor can initiate their attack, firing thousands of username-password combinations to the desired website, reporting any success within seconds. Once there’s a match, the attacker can utilize the credentials manually, crack into accounts to commit online fraud, or sell onto another third party for profit. Ultimately, with the keys to your account, they can do as they please.
Why credential stuffing works
We’re probably starting to sound like a broken record, but as outlined by our recents blogs and research report, credential stuffing—and several other account based attacks—work because of the inherent risks users are taking with their accounts. Using weak and guessable passwords, reusing passwords across multiple services—both corporate and personal—and failing to implement sufficient controls to manage the risk and identify abuse as it occurs.
Keeping credentials in a safe, solitary, place where they can be managed and audited is another area where users are falling short. There’s a really easy and obvious solution to remediate this problem, by simply using a password manager. A password manager is a dedicated online service or locally installed software, which stores all your passwords. This is typically protected by a strong master password that you need to enter to gain access to all your other credentials. These useful pieces of software can assist in mandating a sufficient password complexity, whilst also alerting users to any known detections of a breach of their username or password. They’re typically either free or purchasable for a small price, which are well worth the cost.
If there’s one thing that I would recommend taking away from this blog, its starting to use a password manager.

Final thoughts
Our last blog on weak credentials and ATO outlined several steps that users and organizations can take to minimize credential risk. This includes increasing password complexity, using a password manager, using a multi factor authentication (MFA) wherever possible, and implementing a rate limiting service for online services.
There’s other alternative defences that we could also mention with regards to credential stuffing specifically. Use of IP blocklisting can assist in removing addresses that are used by less sophisticated attackers trying to stuff your credentials (who clearly didn’t read our section on the importance of proxies). CAPTCHAs are, let’s be honest, pretty annoying when you log into a service, however can also add an additional layer of complexity and slow down an attacker conducting automated attacks. To improve usability, it may be desirable to only require the user to solve a CAPTCHA when the login request is considered suspicious.





