Security operations (SecOps) struggles to keep up with today’s threats. Security teams still rely on manual security processes, face skill shortages, and non-standardized workflows. All the while, adversaries increasingly leverage automation to scale attacks.
Secops automation enhances security measures, streamlines processes, and reduces human error. Security teams can then handle a large volume of threats quickly and scale their security posture to proactively defend against malicious actors.
What Is SecOps Automation?
Automation in security operations refers to the use of advanced software, technology, and artificial intelligence (AI) to perform and enhance repetitive, routine, and complex security operations tasks without human intervention. This includes predefined rule-based actions, workflow automation, and the integration of various security tools, as well as the use of machine learning algorithms and advanced analytics to detect, analyze, and respond to security threats in real-time. Automation leverages both deterministic processes and adaptive intelligence to ensure speed, accuracy, consistency, and scalability in managing an organization’s cybersecurity posture.
Here are some examples:
Automated Threat Detection and Response
A security operations platform integrates AI and automation to provide a centralized solution for managing threat detection and response. A security operations platform uses AI to aggregate and analyze data from multiple security tools such as SOAR, SIEM, email, or cloud technology, providing a unified view of the organization’s security posture. When an anomaly is detected, the platform may be able to automatically trigger predefined responses, such as isolating compromised systems, blocking malicious IP addresses, and notifying the security team—all without human intervention.
Automated Threat Intelligence and Incident Enrichment
An AI-powered threat intelligence platform enhances security incident data by providing deeper insights and context. It automatically aggregates threat intelligence from sources like open-source feeds, commercial providers, and dark web monitoring. The AI system analyzes this data to identify relevant threat indicators and correlate them with ongoing security incidents. When an incident is detected, the platform enriches it with contextual information, such as known malicious activities associated with suspicious IP addresses and recent threat actor campaigns. The enriched data is compiled into a detailed report and shared with the security team, with automated alerts sent to relevant stakeholders. This process ensures that security teams have the necessary context to respond effectively to threats.
Phishing Detection and Email Filtering
An AI-driven email security solution analyzes incoming emails for signs of phishing attacks, such as anomalous sender behavior or suspicious links. When a potential phishing email is detected, the system automatically quarantines the email, preventing it from reaching the user’s inbox, and sends an alert to the security team for further investigation.

Automation vs AI in SecOps
While automation and AI are closely related and often used interchangeably in the context of cybersecurity, they are distinct concepts with unique roles and functionalities. Here is why both are important and how they work in secops automation:
Automation in SecOps
Automation in secops refers to the use of software and technology to perform repetitive and routine security tasks without human intervention.
How It Works
It operates on predefined rules to quarantine devices, block IPs, or notify administrators when security alerts are triggered. It also automates tasks like log analysis, patch management, and compliance checks to ensure consistency and efficiency. Platforms like SOAR integrate various security tools, such as SIEM, firewalls, and endpoint protection, to create a cohesive and automated response mechanism.
Benefits
Automated systems react to threats in real-time, significantly reducing response times and ensuring that security protocols are applied uniformly across the organization. By handling routine tasks, automation allows security teams to focus on more complex and strategic activities, enhancing overall resource efficiency.
Artificial Intelligence (AI)
AI in secops automation involves the use of machine learning algorithms and advanced analytics to identify, understand, and respond to security threats with minimal human intervention.
How it Works
AI systems use machine learning to detect patterns and anomalies in historical data, predicting potential threats through trend analysis and enabling proactive vulnerability management. They adapt responses based on threat context, escalating actions for sophisticated attacks, and utilize natural language processing to analyze unstructured data, extracting relevant insights from threat reports and security logs.
Benefits
AI enhances detection by identifying complex and emerging threats that traditional systems might miss. It reduces false positives through contextual understanding and historical data learning, ensuring security teams focus on genuine threats. Additionally, AI systems scale to handle large data volumes and adapt to the growing complexity of modern IT environments.

Overcoming Challenges with SecOps Automation
While the benefits of secops automation are clear, it comes with challenges that organizations must navigate.
Integration with Existing Systems
Integrating new automation tools with existing security systems can often prove to be a complex and intricate process that requires thorough planning and execution. It is essential to carefully evaluate the compatibility of the new automation tools with the current security systems to ensure seamless integration.
This may involve conducting detailed assessments of the existing infrastructure, identifying potential areas of overlap or conflict, and developing comprehensive strategies for integrating the new tools effectively.
Additionally, considerations must be made for potential disruptions to operations during the integration process and plans put in place to mitigate any risks or issues that may arise.
New secops automation technology such as bi-directional APIs and data stitching allow you to leverage existing tools and successfully implement security automation.
Balancing Automation and Human Oversight
Finding the right balance between automated processes and human oversight is essential. While automation can handle many tasks, human expertise is still needed for complex threat analysis and critical decision-making:
The ability to interpret and contextualize data, think critically, and understand the nuances of various threats is a skill that is uniquely human.
Years of training and practical knowledge allow analysts to see patterns and connections that may not be immediately apparent.
Human analysts can anticipate potential threats and vulnerabilities by understanding the motivations and tactics of malicious actors. They can also provide a level of creativity and adaptability that technology may lack, enabling them to respond effectively to unexpected or unconventional threats.
Keeping Automation Systems Secure
Ironically, automation systems themselves can become targets for cyber-attacks. These systems, consisting of interconnected and IoT devices and software, are vulnerable to malicious actors seeking to disrupt operations, steal sensitive information, or cause damage. As technology advances and more devices become connected to the internet, the potential for cyber-attacks on automation systems continues to grow.
What Does a SecOps Automation Engineer Do?
The role of a secops automation engineer is primarily in relation to the integration, automation, and streamlining of security processes. The key responsibilities of this role include:
Integration: Engineers identify repetitive and error-prone tasks and integrate various security tools and systems ensuring that the tools work cohesively to address security incidents faster and more effectively.
Automating Routine Security Tasks: Engineers are responsible for automating tasks such as monitoring, threat detection, and incident response. Manual tasks are streamlined through automation platforms like SecOps Platforms, SOAR and XDR.
Playbook and Workflow Development: A key responsibility of security engineers is to build and implement security playbooks. These workflows define how automated systems respond to different types of security events, reducing the need for manual intervention.
Continuous Improvement: Engineers are responsible for ongoing improvements, ensuring that automated processes evolve to keep pace with emerging threats. They create continuous improvement models to refine automation logic and enhance security systems.
Best Practices for Implementing SecOps Automation
Implementing security automation requires careful planning, skilled personnel, and the right tools. To maximize benefits, consider these best practices:
Apply Automation to Known Processes: Use automation for trusted processes rather than every source in the environment. It requires intimate knowledge of incident response and access to systems.
Focus on Quick Wins: Automate impactful, easy tasks like data enrichment and low-impact threat remediation to free up experts for strategic projects. Automation should support, not replace, security professionals.
Inventory and Deploy Available Playbooks: Review and deploy existing configurable playbooks for different response scenarios to achieve rapid impact.
Automate High-Fidelity Alerts: Automate responses to regularly escalated, consistently true-positive alerts to avoid manual, repetitive tasks.
Use Existing Tools: Leverage existing security tools and integration capabilities for better ROI and quicker impact. Bi-directional integrations enable platforms to ingest data and take action through the same tools.
Accelerating SecOps Workflows
SecOps automation enables security teams to upscale, expand, and accelerate their cyber defenses. This need will only continue to grow in the future. Simply increasing your security staff or using more tools won’t suffice to achieve a mature security posture. Automation and AI have become capable assistants in defending against the rapidly evolving threat landscape.
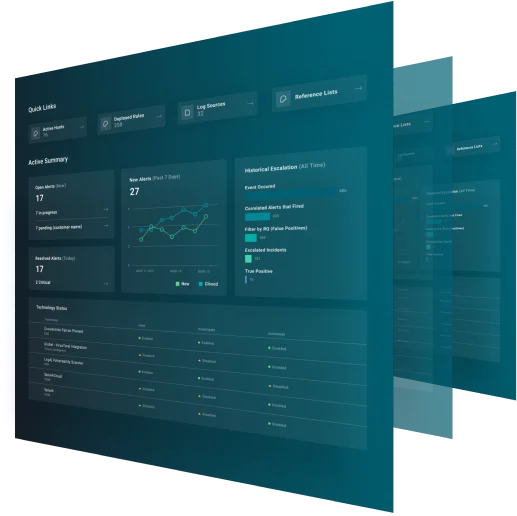
Applying secops automation throughout your security operations workflow accelerates threat response, helps solve the tool sprawl issue, and frees up your team for more meaningful work. The GreyMatter security operations platform applies automation throughout the detection, investigation, and response process and provides playbooks that leverage bi-directional integrations to take response actions through your existing tools.