Key Points
Ransomware activity is down 18% compared to the fourth quarter of 2023. This slow start to the year was likely influenced by the holiday period as well as recent law enforcement operations against ALPHV and LockBit.
The most active groups in the first quarter of 2024 (Q1 2024) were LockBit, Black Basta, and Play. Black Basta saw the most growth in activity—41% quarter-over-quarter.
During Q1 2024, the ALPHV group conducted an exit scam to defraud its affiliates out of an alleged $22 million ransom payment taken from a healthcare organization. It is realistically possible that some affiliates have since moved to the RansomHub group, which emerged in February 2024.
A law enforcement operation targeting LockBit in February 2024 significantly impacted the group, which, despite showing resilience in restoring operations, has not met its previous operational output.
LockBit has faced significant reputational setbacks among affiliates. Cybercriminal forum chatter showed that users were apprehensive about working with a group compromised by law enforcement. The DarkVault ransomware group is a possible successor group to LockBit.
The US and the manufacturing sector were the primary targets of ransomware attacks in Q1 2024, consistent with the previous quarter. This is likely due to the perception of financial rewards afforded by US-based companies, and manufacturing’s susceptibility to ongoing outages.
In the coming months, we expect to see a return of the Clop group in targeting susceptible enterprise file transfer software, increased use of generative artificial intelligence and automation in ransomware campaigns, and adaptations to the transfer and storage of decryption keys amongst ransomware members.
In Q1 2024, ReliaQuest identified 1,041 organizations posted to ransomware data-leak sites (DLS), representing an 18% decrease from Q4 2023. While Q1 2024’s figures indicate somewhat of a slowdown in ransomware activity, it likely only represents a temporary lull. We expect ransomware to rise in the second quarter of 2024, a trend we’ve seen in previous years.
A law enforcement crackdown on the LockBit ransomware group in February of this year likely contributed to a dip in overall ransomware activity. While LockBit, the most prolific ransomware group in recent years, showed resilience in the aftermath of this operation, it was short-lived: The group saw a 21% decrease in activity this quarter compared to Q4 2023.
Q1 2024 also saw an ALPHV exit scam, in which the group posted a potentially fake law enforcement takedown notification on its DLS. We suspect this was conducted to scam its affiliates out of a $22 million ransom payment allegedly taken from UnitedHealth’s Change Healthcare unit. Several ALPHV members have likely moved to other ransomware operations following this (including the RansomHub group, which emerged in February 2024).
These events contributed to a tumultuous first three months of 2024 for the ransomware ecosystem; however, the threat these groups pose remains. This report outlines some of the key takeaways from this period.
Ransomware Activity in Q1 2024
In Q1 2024, ransomware activity trended down, with monthly figures failing to reach 400 organizations posted to ransomware DLS pages, which is typically the average.
Compared to Q1 2023—which saw 860 victims posted to leak sites—Q1 2024 represented a 20% increase, highlighting that while this is a slow period for ransomware activity, the overall activity is trending upwards. This is likely due to the continued success for ransomware actors and a continuation of endemic security failings that facilitate these threats. A slow start to the year is likely due to the celebration of Orthodox Christmas in many Russian-speaking regions on January 7, 2024. It is also realistically possible that the start of the new year represents a planning phase for ransomware groups, identifying who they will target in the coming months and other operational changes. This is consistent with our findings for Q1 in previous years.

Figure 1: Number of compromised organizations listed on data leak sites, Q1 2024
In terms of delivery mechanisms, the tactics used by ransomware groups remained consistent. Phishing, exposed remote services, and exploitation of public facing vulnerabilities remain the most common methods of obtaining initial access to targeted organizations. The majority of this activity appears opportunistic, exploiting the many endemic security failings that are present across businesses.
Targeted Geographies
In terms of target geography, unsurprisingly, the US remains the most targeted, followed by Canada and the UK. This is likely due to the perception that organizations in English-speaking countries are financially able to pay ransoms to restore their operations. There is also likely a nationalistic driver in targeting organizations in countries whose policies are perceived to be opposed to Russian interests—many ransomware operators are based in Russian-speaking parts of the world—however, this is likely secondary to the pure financial motivation behind their activity.
Targeted Sectors
Manufacturing was the most common target for ransomware activity in Q1 2024, followed by the Professional, Scientific, and Technical Services (PSTS) sector; Construction; Healthcare; and Retail. The top five sectors remained almost identical to the previous quarter, consistent with earlier findings in Q4 2023. These sectors are not only more vulnerable to ransomware attacks, but also likely to experience the most significant impact from prolonged outages. In particular, manufacturing suffers from extended outages due to the correlation between impact on IT and operational technology (OT). Without working IT processes, manufacturing cannot continue operations, which may drive manufacturing companies to pay the ransom rather than continue to see downtime.
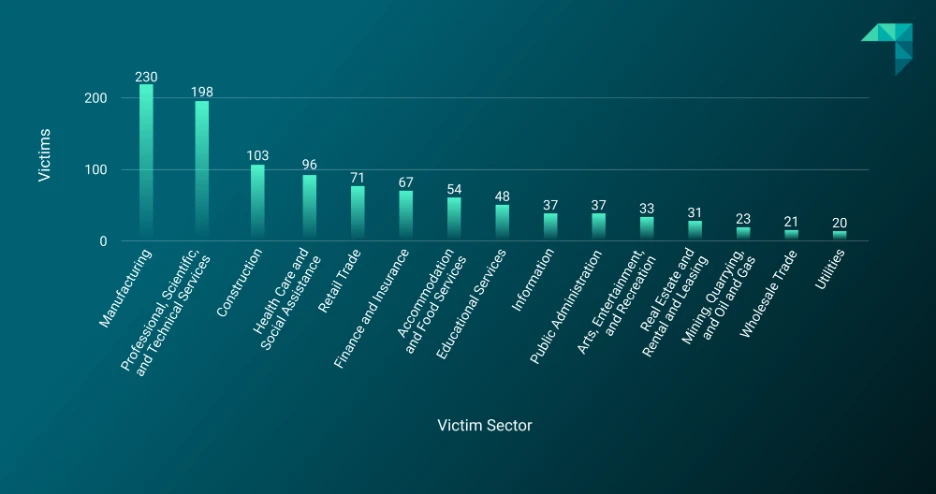
Figure 2: Ransomware targets by sector, Q1 2024
Most Active Groups
The most active groups can be seen on Figure 3. Despite the law enforcement operation targeting it in February 2024, LockBit was still the most active group. The next four most active were Black Basta, Play, ALPHV, and Akira.
This was similar to the previous quarter, which saw LockBit, Play, ALPHV, No Escape, and 8base as the most active groups. The biggest change since the last quarter was the shutdown of the NoEscape ransomware operation. The group’s DLS closed in December 2023, with affiliates of NoEscape alleging that the group conducted an exit scam to cheat affiliates out of millions of dollars in ransom payments. Reportedly, LockBit recruited several NoEscape and ALPHV affiliates, who conducted their own exit scam in February 2024.
This turbulence emphasizes the boom-and-bust nature of ransomware activity, with groups shutting down as quickly as they start up. It also underscores the untrustworthy nature of cybercriminal activity, with members more than willing to scam their fellow members out of payments.
Most ransomware groups, including LockBit, Play, ALPHV, and Akira, all saw smaller numbers of victims than in Q4 2023. On the other hand, Black Basta saw a 41% growth in activity, posting 72 targeted organizations in Q4 2023 but 102 in Q1 2024.
Black Basta has been in operation since early 2022 and has consistently been one of the most active groups. The group is widely believed to be an offshoot of the prolific Conti group, which disbanded in 2022. It is likely that the group’s output at the end of 2023 was affected by the takedown of the Qakbot loader malware, which was targeted by law enforcement in August 2023 but resurfaced in December; Qakbot was one of the primary tools used by several ransomware groups, particularly Black Basta.
A newer version of Qakbot is now in operation, reportedly leveraging malicious versions of OneNote notebooks. In January 2024, Black Basta was observed using Pikabot malware as a replacement for Qakbot. The spike in activity in Q1 2024 indicates that the group has adapted to a new malware, either Pikabot or use of the new Qakbot variant. We predict that Black Basta will continue to be a ransomware frontrunner in the second quarter of this year.
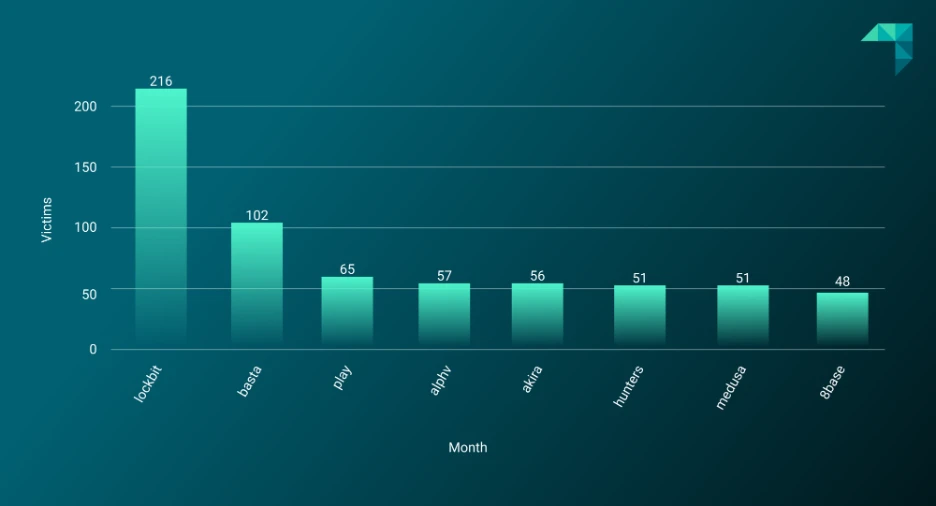
Figure 3: Most active ransomware groups, Q1 2024
Major Events in Q1 2024
Tango Down: Law Enforcement Operation Targets LockBit
The biggest event affecting the ransomware ecosystem in Q1 2024 was the law enforcement operation targeting LockBit. This internationally coordinated operation—named Operation Chronos—took place on February 20, 2024, resulting in the takedown of significant sections of LockBit’s infrastructure, two arrests, and most importantly, the production of a decryption key to help previous LockBit victims restore their files.
LockBit quickly recovered its activity and began new attacks after the operation. The group’s overall activity numbers are significantly down for the quarter, however, from 275 in Q4 2023 to 216 in Q1 2024. This drop is likely attributable to LockBit having to renew its seized infrastructure but also the inevitable blow to its reputation among affiliates.
On February 19, 2024, cybercriminal forum chatter speculated that “LockBitSupp”—the LockBit forum representative on the prominent Russian-language cybercriminal forum XSS—was collaborating with law enforcement and would “deanon” (deanonymize) the forum administrator, raising concerns that the anonymity of the rest of the forum’s membership was also at risk.
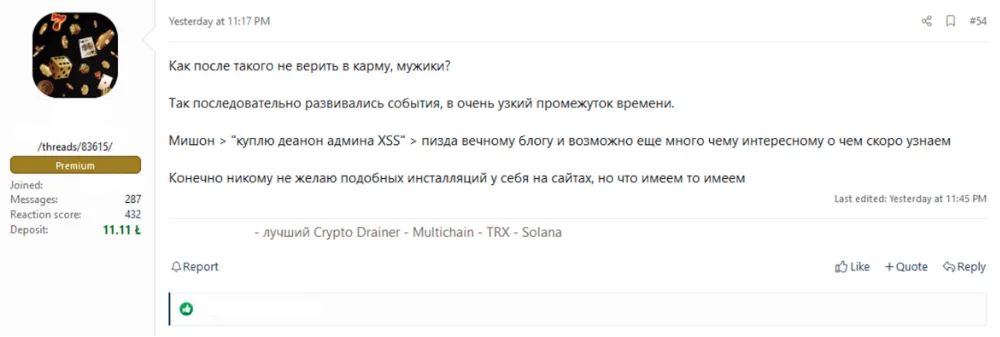
Figure 4: Post on Russian-language cybercriminal forum related to Operation Chronos
The operation was a significant success for law enforcement because it not only produced the decryption key to help victims but also supplied a wealth of intelligence that will shape law enforcement efforts in the future.
The future for LockBit remains unclear. While the group may be able to recover its infrastructure to start operations again, many affiliates likely feel apprehensive about their involvement with a group that has seemingly been compromised by law enforcement. The most likely outcome is that LockBit will attempt a rebrand, potentially to the “DarkVault” group identified in early April 2024. On the launch of the new DarkVault DLS, researchers noted several similarities with LockBit’s branding, including the font, use of red and white, and even the format of the group’s ransom demand countdown clock. It is likely that these design similarities were not intentional, as they soon disappeared. Given these mistakes, it is likely that DarkVault’s developers have had previous involvement with LockBit, although it’s unclear to what extent. DarkVault has posted a limited number of organizations to its DLS; whether it can step into the void left by its alleged predecessor remains to be seen.
ALPHV Scams Affiliates Following Change Healthcare Attack
After ALPHV solicited a $22 million ransom payment from Change Healthcare, on March 3, 2024, one of the group’s affiliates made a public statement claiming that they had been cheated out of their cut. Two days after that, ALPHV’s public DLS displayed an FBI takedown notice. This turned out to be a fake taken from a previous law enforcement operation, likely the group’s attempt to keep the ransom rather than pay affiliates.
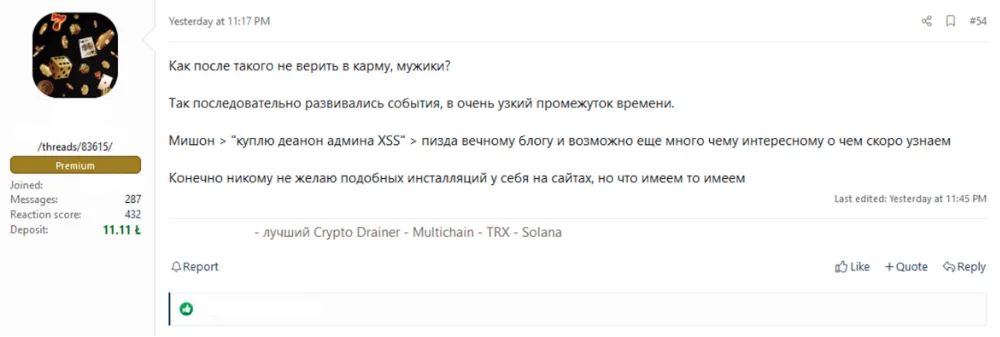
Figure 5: ALPHV affiliate claims the group scammed its affiliates out of their cut of a ransom payment
The exit scam indicates that, after receiving the $22 million payout, ALPHV chose to either retire or rebrand—a strategy frequently adopted by ransomware groups to evade law enforcement. ReliaQuest has not observed any activity from ALPHV since this incident.
Despite reportedly paying a ransom, Change Healthcare soon faced another attack by RansomHub, a group that surfaced in February 2024 and is possibly a rebranded version or offshoot of ALPHV. ReliaQuest found forum posts indicating that several ALPHV affiliates have joined RansomHub, though it’s also possible that the two groups were once distinct entities.
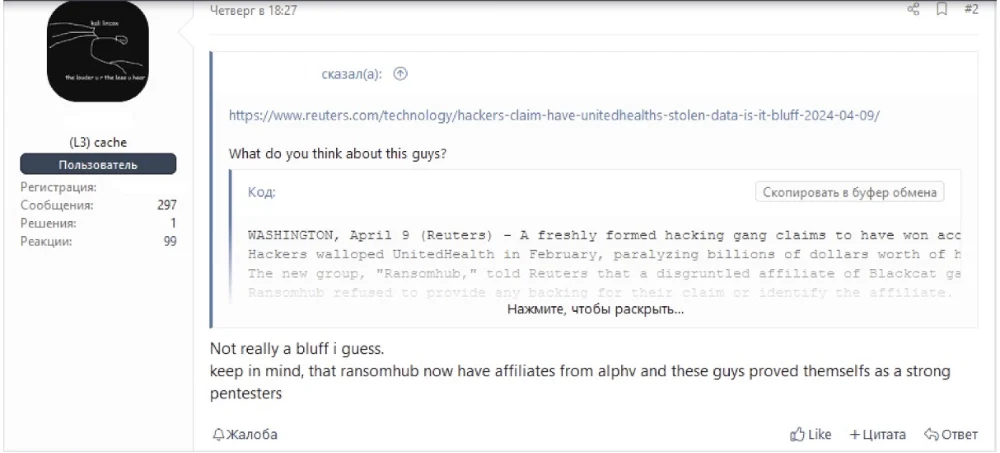
Figure 6: Forum user claiming that RansomHub has former members of the ALPHV operation
RansomHub takes a unique approach to payment between the group’s developers and the affiliates who are carrying out attacks. RansomHub allows affiliates to receive 100% of the proceeds from attacks, but the affiliates must then send 10% of those earnings to RansomHub’s developers. This model reverses the strategy taken by most other ransomware groups, placing greater responsibility on the affiliates to provide profits.
Given that many of RansomHub’s members have reportedly moved over from ALPHV—and presumably, many who were affected by the exit scam—it is possible that this arrangement was a demand from membership, to avoid being similarly defrauded in the future. This move will likely be popular to new members, which could lead RansomHub to become a significant force within the ransomware ecosystem.
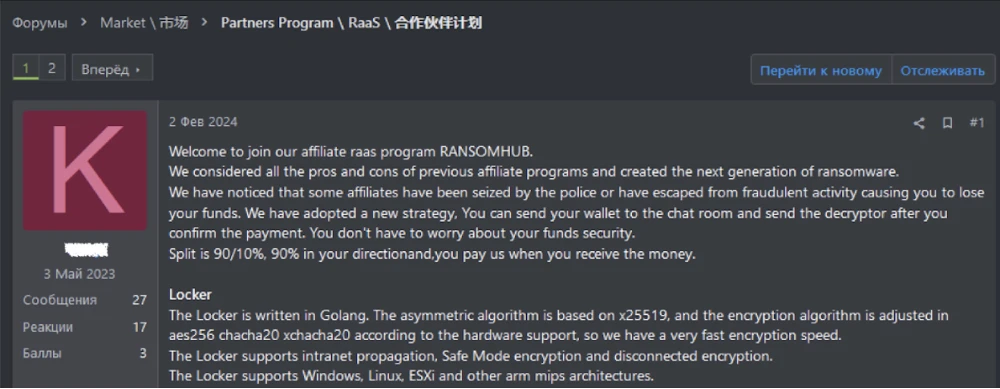
Figure 7: RansomHub ransomware-as-a-service (RaaS) program advertisement
The Change Healthcare attack—which some commentators suggested was the “Colonial Pipeline moment in healthcare”—will have ongoing implications. The attack has had a broad impact, since the company is connected with most hospitals in the United States and holds vast amounts of patient data. ALPHV, along with RansomHub, will probably have sold the data to other cybercriminals who might then use this information to commit further fraudulent activities— the social engineering attacks that have plagued healthcare companies in Q1 2024 are almost certainly related.
Forecast for Ransomware in 2024
While Q1 2024 has seen a dip in overall activity, we expect numbers to trend upward for the rest of 2024. Here are a few more of our predictions for the remainder of the year.
Clop’s Return
The return of the Clop ransomware group was something we predicted in the previous quarter. Clop had enormous success in 2021, 2022, and 2023 in targeting commonly used file transfer software, exploiting zero-day bugs to facilitate data theft. This includes the MOVEit, GoAnywhere, and Accellion file transfer software.
In Q1 2024, the group only named eight organizations on its DLS, the same number it had posted in Q4 2023. However, Clop typically works in bursts, going quiet for several months before impacting thousands of organizations in one big campaign.
The last such campaign, which targeted MOVEit, began in July 2023 and ended around November 2023. It brought enormous success for Clop. Given the amount of time that has passed since this campaign, we believe the group will return soon, likely targeting other susceptible file transfer software.
Increased Targeting of Cloud and SaaS Platforms
As businesses continue to migrate to cloud services and software-as-a-service (SaaS) platforms, attackers are likely to follow. Expect ransomware to exploit vulnerabilities specific to these environments, possibly targeting misconfigurations and weak access controls to encrypt data stored on cloud services.
Exploration of AI and Machine Learning
Generative artificial intelligence (AI) is set to revolutionize many aspects of our daily lives, including the world of security. Our recent Annual Threat Report identified that organizations using AI and automation in their incident response saw a 98.8% improvement in their mean time to resolve (MTTR) incidents.
While this technology is game-changing for defenders, generative AI is also likely to enhance the efficiency and timeliness of commodity threats, like ransomware. Attackers might leverage AI and machine learning (ML) to automate target selection, customize phishing messages, and optimize the encryption process. This could lead to more efficient and targeted attacks, increasing the success rate of ransomware campaigns.
Adapting to Law Enforcement Operations
In several recent law enforcement operations, including Operation Chronos and the ALPHV and Hive operations, law enforcement groups created a decryption tool by collating decryption keys shared within the groups’ infrastructure. To prevent this going forward, ransomware groups will probably change the way they share and store decryption keys, potentially moving them to offline infrastructure.
What ReliaQuest Is Doing
ReliaQuest comprehensively tracks the developments in the ransomware scene—profiling new groups, monitoring daily activity, and watching for changes in threat actor tactics, techniques, and procedures (TTPs). We use these findings to create custom detections that improve customers’ resilience to ransomware activity.
Recommendations and Best Practices
We recommend taking the following steps to minimize the risk from ransomware.
Introduce multifactor authentication (MFA): MFA adds a layer of security that makes it significantly more challenging for attackers to gain unauthorized access to systems and data, even if they manage to obtain a user’s credentials. This reduces the risk from one of the most common methods ransomware actors use to gain initial access to their targets.
Employ the principle of least privilege: This limits access rights for users to the bare minimum necessary to perform their duties, thereby reducing the potential attack surface that ransomware groups can exploit.
Harden “joiners, movers, leavers” (JML) policies: JML policies can reduce the risk of ransomware by ensuring that access rights are promptly updated or revoked as employees change roles or leave the organization, thus minimizing the risk of attackers exploiting expired or unnecessarily privileged accounts.
Prioritize defense in depth: This plays a pivotal role in halting ransomware attacks by layering multiple security measures, ensuring that if one defense is breached, others stand ready to thwart the attack.
Implement and test backups: Backups provide a critical safety net that enables organizations to restore lost data, commonly impacted through encryption attacks, without yielding to the demands of attackers.
Monitor external-facing assets: External-facing vulnerabilities are often easily identifiable for ransomware actors aiming to obtain initial access. Remedy any accidental exposures and patch services with known, exploitable vulnerabilities.
Restrict PowerShell use: Use Group Policy Objects (GPOs) to restrict PowerShell use to only those users who need it for their role. This will restrict ransomware actors from abusing PowerShell by writing malicious scripts.
Prioritize patch management: Regularly update and patch all operating systems, software, and firmware. This should be undertaken with a risk-based approach, tackling the highest risk vulnerabilities first.




