Malware loaders are tricky business for SOC teams. Mitigation for one loader may not work for another, even if it loads the same malware. And they’re one of the most common tools for a cyber-threat actor to secure initial access to a network, then help drop payloads (remote-access software and post-exploitation tools are popular choices).
ReliaQuest has uncovered a load of loaders causing havoc for defenders. The seven that we observed the most in customer environments so far this year are shown in Figure 1.
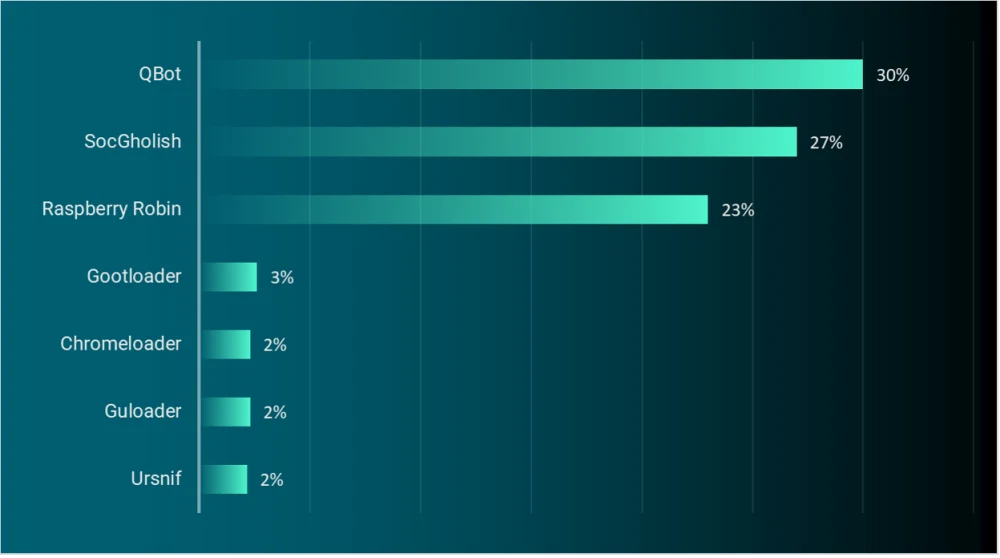
Figure 1: Top 10 most observed malware loaders, January 1–July 31, 2023, by percentage of all loaders observed
Let’s break down those results:
“QakBot” (aka QBot, QuackBot, Pinkslipbot), “SocGholish,” and “Raspberry Robin” were overwhelmingly the most popular loaders. This accounted for 80% of incidents involving malware loaders that were observed by ReliaQuest.
Other strong contenders were “Gootloader,” “Guloader,” “Chromeloader,” and “Ursnif.”
Bear in mind that just because a malware loader was detected, it doesn’t mean the targeted network was compromised; in the majority of cases we observed, the malware loader was detected and stopped early in the kill chain. But it’s crucial to not look away from the car-crash threat of any loader, especially the three most popular.
QakBot: The Agile One
Like other versatile and common malware, QakBot was designed as a banking trojan, then upgraded with new capabilities. Other than permitting initial access to targeted networks, QakBot delivers other remote-access payloads, steals sensitive data, and helps lateral movement and remote code execution.
QakBot is most associated with the “Black Basta” ransomware group that splintered off from the “Conti” ransomware syndicate. (Remember our previous reporting on Black Basta about QakBot to facilitating an initial foothold in the targeted environment?)
How is QakBot delivered? Well, it’s that age-old story: A phishing email offers the recipient tailored lures—work orders, urgent requests, invoices, file attachments, or hyperlinks. These lead to the download of payloads, typically as PDF, HTML, or OneNote files. QakBot then uses WSF, JavaScript, Batch, HTA, or LNK files that, when executed, typically establish persistence via scheduled task or registry run keys.
Now it’s time for QakBot to perform discovery commands and begin command-and-control (C2) communication, to relay system/domain information and drop additional payloads (commonly, the remote-access tools “Atera” or “NetSupport”, along with “Cobalt Strike”) for post-exploitation objectives.
QakBot’s Threat
QakBot is an evolving, persistent threat used to opportunistically target any industry or region. Their operators are capable and resourceful in adapting to change, and they’re likely to be here for the foreseeable future
QakBot’s agility was evident in its operators’ response to Microsoft’s Mark of the Web (MOTW): they changed delivery tactics, opting to use HTML smuggling. In other instances, QakBot operators have experimented with file types for their payloads, to evade mitigation measures. This included OneNote files, in an aggressive February 2023 campaign targeting US-based organizations.
SocGholish: The Easy Trap
The infamous SocGholish (aka FakeUpdates) is a JavaScript-based loader that targets Microsoft Windows-based environments. The malware is delivered via drive-by compromise (downloaded without user interaction). Visitors to a wide network of compromised websites are tricked into downloading “updates,” typically through outdated-browser prompts or other update lures for Microsoft Teams and Adobe Flash.
SocGholish has been linked to the notorious “Evil Corp,” presumed to be a Russia-based group waging financially motivated cybercrime since at least 2007. Common SocGholish targets are accommodation and food services, retail trade, and legal services, primarily in the US.
SocGholish is also linked to “Exotic Lily,” an initial access broker (IAB) active since at least September 2021. The IAB conducts highly sophisticated phishing campaigns to gain initial access to organizations and sell it to other threat actors, such as ransomware groups.
SocGholish’s Threat
SocGholish has been posing a threat since 2018 but really came into fruition in 2022. Its vast malware distribution network runs on compromised websites and social engineering; just four user clicks can affect an entire domain or network of computer systems within days.
In the first half of 2023, SocGholish’s operators conducted aggressive watering hole attacks. They compromised and infected websites of large organizations engaged in common business operations with lucrative potential. Unsuspecting visitors inevitably downloaded the SocGholish payload, leading to widespread infections.
SocGholish’s social engineering is convincing and can bring a significant impact, even if only one user is tricked. User awareness and defense in depth is key to minimize this threat.
Raspberry Robin: The All-Rounder
Last, but by no means least, is Raspberry Robin, a highly elusive worm-turned-loader that targets Microsoft Windows environments. Its exceptional propagation capabilities kick in after initial infection via malicious USB devices, when cmd.exe runs and executes a LNK file on the infected USB.
The LNK file contains commands triggering native Windows processes, such as msiexec.exe, to initiate an outbound connection to download the Raspberry Robin DLL. Once the Raspberry Robin payload is running, additional processes are spawned using system binaries, such as rundll32.exe, odbcconf.exe, and control.exe, to run malicious code. This code injects itself into system processes (e.g., regsvr32.exe, rundll32.exe, dllhost.exe) to create scheduled tasks for persistence, to initiate C2 communication, and to deliver other payloads.
Raspberry Robin is tied to various highly capable, malicious groups. This includes the aforementioned Evil Corp, plus “Silence” (aka Whisper Spider): a financially motivated threat actor targeting financial institutions in Ukraine, Russia, Azerbaijan, Poland, and Kazakhstan.
Raspberry Robin has also been used to deliver multiple ransomware and other malware variants, such as “Clop,” “LockBit,” “TrueBot,” and “Flawed Grace,” in addition to the Cobalt Strike tool. In 2023, Raspberry Robin operators have targeted financial institutions, telecommunications, government, and manufacturing organizations, mainly in Europe, although the US has had its fair share of attacks.
SocGholish’s operators used Raspberry Robin in the first quarter of 2023 when heavily targeting legal and financial services organizations. This shows the increased collaboration between crime syndicates and operators of various types of malware.
Raspberry Robin’s Threat
Raspberry Robin is a highly useful addition to a threat actor’s arsenal, helping carve out an initial network foothold and delivering multiple forms of payload.
The loader’s operators have used it to load various malware for other cybercrime groups, which will probably boost Raspberry Robin’s development and opportunities in future campaigns.
Defending Against Loaders
Based on recent trends, it’s highly likely that these loaders will continue to pose a threat to organizations in the mid-term future (3–6 months) and beyond. In the remainder of 2023, we can anticipate other developments in these loaders—whether in response to organizational mitigation or through collaboration among threat actors.
For now, there are several steps that you can take to minimize the threat from malware loaders:
Configure a GPO (Group Policy Object) to change the default execution engine of JS files from Wscript to Notepad, and any additional script files you see fit. This will prevent these files from being executed on the host.
Block inbound emails that have file extensions typically used for malware delivery.
Restrict company assets from making arbitrary connections to the internet, via firewall or proxy configurations, to minimize malware and C2 activity.
Limit the use of remote-access software unless absolutely required for an individual's job; alternatively, enhance monitoring to detect misuse. Cybercriminals—notably IABs and ransomware operators—love using this software to gain and maintain access to networks.
Disable ISO mounting, which is increasingly a solid way to bypass antivirus or endpoint detection tools.
Implement USB access control and GPOs to prevent autorun command executions. Consider disabling any removable media access if business conditions allow.
Train staff to identify social-engineering tactics employed on the web, and open up an appropriate channel for them to report suspicious emails or other activity.
At ReliaQuest, we understand the importance of staying one step ahead of the malicious threats that can impact your organization. That’s why our security operations platform, GreyMatter, uses advanced detection rules we’ve specifically designed to identify malware, including the chronic offenders named and shamed in this blog.
GreyMatter automates the high-time, low-brain activities of your security teams, leaving them free to focus on strategic improvements to your security posture that can help you better defend against ransomware.




