Updated February 26, 2024
On February 24, 2024, the LockBit ransomware group reestablished a data-leak website, which contains 16 victims as of 10 a.m. ET, February 26, 2024. This website contains announcements from the group’s administrators, reporting that the law enforcement exploited vulnerabilities in the group’s PHP servers to conduct Operation Cronos; however, backup servers were reportedly unaffected.
LockBit clarified that it would make improvements after its “personal negligence and irresponsibility.” The new data-leak site also identifies the reason why the group believes it was targeted, referencing the attack against Fulton County, that posed the risk of leaking certain sensitive information.
LockBit reportedly plans to upgrade security for its infrastructure, while switching to manually releasing decryptors and trial file decryptions. The affiliate panel would also be hosted on multiple servers, providing partners with access to different copies, based on their trust level.
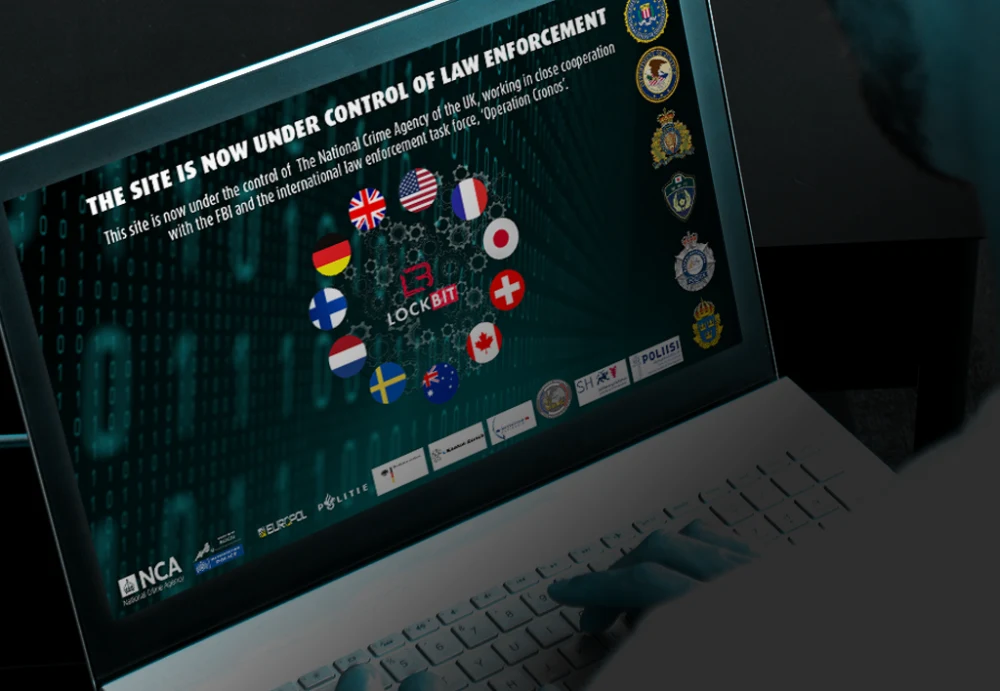
On February 20, 2024, in an internationally coordinated operation, a law-enforcement taskforce headed by the United Kingdom’s National Crime Agency (NCA) and coordinated in Europe by Europol and Eurojust, targeted the LockBit ransomware group, the most active ransomware group in the world.
This law enforcement operation against LockBit has the potential to be the most significant action taken against ransomware so far.
The task force—named Operation Cronos—began in April 2022, and resulted in the following:
The takedown of 34 servers in Netherlands, Germany, Finland, France, Switzerland, Australia, the United States and the United Kingdom.
The identification and seizure of more than 14,000 rogue accounts reportedly responsible for launching LockBit’s operations.
The seizure of over 200 cryptocurrency wallets.
Retrieval of over 1,000 decryption keys from seized LockBit servers.
The arrest of two LockBit members based in Poland and Ukraine.
The issue of three international arrest warrants and five indictments targeting other LockBit members.
What is the Likely Impact of This Operation?
The impact of the operation is likely to be substantial, particularly over the next few months. These seizures came shortly after another seizure of a large ransomware group named ALPHV in December 2023, during which the FBI seized the dark web leak sites of ALPHV and provided a decryption tool to as many as 500 victims. However, the ALPHV seizure did not go as expected, as the group managed to reclaim its dark web sites and continue operations under a new infrastructure.
Although recent actions by law enforcement against ALPHV may not have significantly disrupted the group’s long-term activities, the confiscation of a large portion of LockBit’s infrastructure is likely to represent a significant victory for law enforcement in planning and executing future operations. Given the group has remained the most active ransomware group for several years, its removal will have a significant impact on the entire ransomware threat landscape. In 2023, LockBit named more than 1,000 victims, accounting for 21.5% of ransomware attacks. Therefore, any disruption to LockBit could be considered a major victory over the global threat landscape as a whole.
Importantly, the release of a decryption tool via law enforcement is likely to help hundreds of organizations recover their systems from LockBit attacks. This free decryption tool is now available via the ‘No More Ransom’ portal.
This tool will only assist companies who have been targeted in the leadup to NCA’s operation. Producing alternative encryptors is a simple task for LockBit’s developers, if they are able to restart operations.
It is also unclear if the decryption tool will only assist organizations that were targeted after a certain date or those affected by a specific version of LockBit. Lockbit’s 3.0 operation started in June 2022, and likely uses different encryptors than their previous versions. In addition, it is likely that the group has upgraded its decryption tool over time, releasing several versions of LockBit, including LockBit Black (3.0), LockBit Red (2.0), and LockBit Green (using Conti Source code).
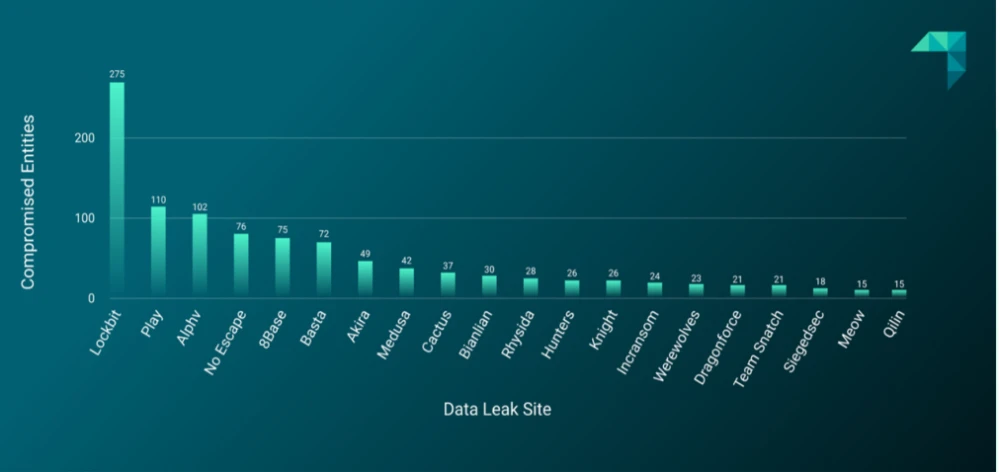
Figure 1: Number of compromised entities listed on data-leak sites by threat group in Q4 202
While the seizure of this substantial infrastructure represents a significant victory, the potential for LockBit to resume operations cannot be discounted. It’s unclear what backup systems and resources they may have available, but it is possible that they could attempt to restore operations, similar to the ALPHV ransomware group after its take down.
Cybercriminal Community Reaction
This operation has resulted in significant discussion within cybercriminal communities, with several themes emerging.
Cybercriminal forum users are particularly concerned about the potential disclosure of the identity of one LockBit forum administrator’s identity. Chatter speculated that “LockBitSupp”— the LockBit forum representative on the prominent Russian-language cybercriminal forum XSS —is collaborating with law enforcement and will “deanon” (deanonymize) the forum administrator. Other users suggested this could risk the anonymity of the rest of the forum’s membership. Other users suggested this could risk the anonymity of the rest of the forum’s membership.
Members on cybercriminal forums believe that law enforcement will eventually give out decryption keys to the victims. However, one user raised a question about the keys that the group might have kept offline. If LockBit has stored keys offline and out of reach of law enforcement, this could make it difficult for officials to help companies that have been attacked by LockBit.
Users quoted a LockBit admin message claiming that while the FBI had indeed seized PHP servers, servers that were not written in PHP remained untouched. It is possible to conclude from this discussion that law enforcement’s operation may have its limitations and has not gained access to all of LockBit’s “flawed infrastructure.” This likely refers to a direct quote left by law enforcement on LockBit’s affiliate panel.
What Comes Next?
The recent operation comes after a long list of similar operations against other ransomware groups. In 2023, law enforcement actions targeted the Hive and ALPHV ransomware groups with varied outcomes: Hive ended its operations, while ALPHV managed to stay active.
The difference with this particular operation is likely to be the scale of infrastructure taken down by the National Crime Agency, including servers, cryptocurrency wallets—likely used to launder LockBit’s ransom payments—and accounts. The NCA has indicated that further law enforcement actions are likely to be undertaken in the future; the infrastructure that has been seized represents a goldmine of opportunity for further activity targeting LockBit.
The impact of the decryption tool on this operation is also likely to be much more significant than the similar decryption tool made to assist companies impacted by ALPHV. Reports in December 2023 indicated that the decryption tool assisted over 400 companies impacted by ALPHV activity. This recent operation is likely to be far more impactful to a greater number of victimized organizations.
It is likely that many threat actors will feel apprehensive about continuing their involvement with LockBit. After the FBI’s crackdown on ALPHV, LockBit attempted to recruit members of the disbanded group, including its developers. However, this strategy has been criticized by fellow cybercriminals (see Figure 2), who suspect that these new recruits might have been undercover agents—a factor that could have contributed to LockBit’s own security breach. Therefore, this law enforcement operation is likely to affect LockBit’s ability to collaborate with other groups and continue operations.
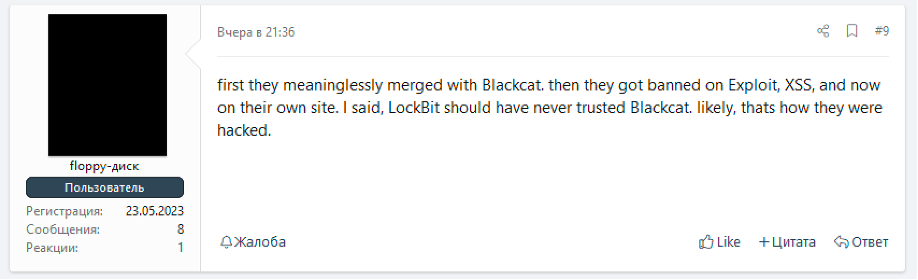
Figure 2: User on Russian cybercriminal forum criticizing LockBit for merging with ALPHV (aka BlackCat)
It is possible that many affiliates of LockBit will, however, simply take their experience to flee to alternative ransomware groups, or start their own operations. This has often been observed after similar law enforcement actions targeting ransomware groups in the past.
Next Steps for Cybersecurity Teams
Companies should not become complacent following LockBit’s seizure. Ransomware is expected to continue to thrive, and other ransomware groups will likely seek to become the new leaders in the ransomware business.
It is imperative for organizations to maximize visibility across their security environments by integrating their various cybersecurity technologies through a security operations platform, ideally one that is integrated with real-time threat intelligence.
The ransomware threat landscape is expected to undergo significant changes in the coming months; it is critical to stay informed. Proactive and automated threat hunting can help security teams stay ahead of threats, which move at an increasingly rapid pace.
ReliaQuest will continue to monitor this story as it unfolds and provide updates to this blog. In the meantime, learn more about LockBit and other high-profile ransomware groups by reading our Ransomware & Data-Leak Extortion blog covering Q4 2023, which includes a comprehensive overview of the most common TTPs used by ransomware groups, as well as mitigation techniques. We also recently issued a report detailing a new infection chain associated with the SocGholish malware loader, commonly favored by ransomware groups.
For further ransomware-related stories and weekly cybersecurity news, listen to our threat research podcast, ShadowTalk, where we discuss the latest ransomware trends and news.
You can review the latest content from ReliaQuest’s Threat Research team below.
Content
Product