In July, we reported on ReliaQuest’s most commonly observed attacker techniques. Now, three months on, it’s time to revisit and reflect on what we’ve observed across our customer networks and ask: what can we do to manage risk?
If you know it’s going to rain, putting on a waterproof jacket is a sensible step, right? Similarly, when it comes to your network security, taking proactive steps to secure your network can help prevent or mitigate the impact of potential security incidents. Identifying the most likely and relevant attacker techniques enables security teams to put the right controls in place.
Phishing and Malware Lead the Way
In Q2 2023, spearphishing-related techniques represented the three most observed methods of attack. This remained true in Q3 2023, accounting for a total of almost 65% of all true-positive incidents. This trend will almost certainly continue.
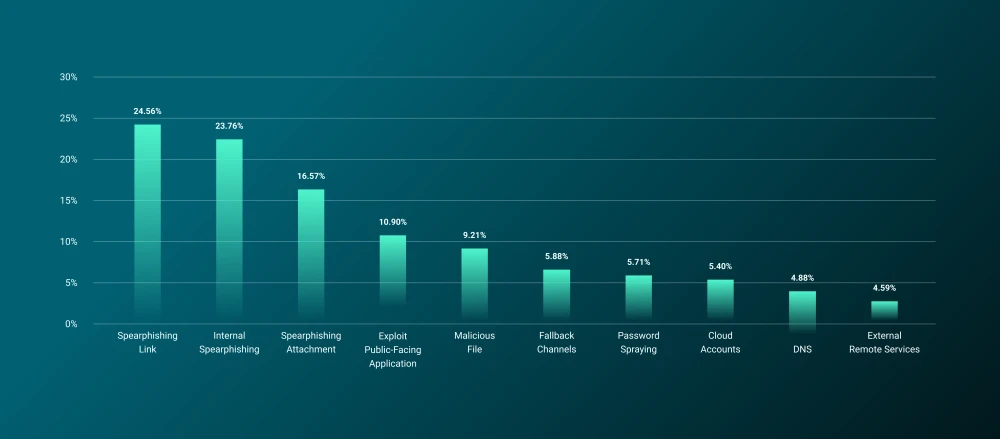
Figure 1: Most observed techniques in Q3 2023
The continuing prevalence of these techniques largely stems from perennial problems:
Human fallibility
Businesses’ failure to keep up with developing attacker techniques
A low barrier to entry for would-be phishers
Another highly observed technique during Q2 2023 was User Execution: Malicious File (T1204.002), indicating that adversary-controlled malware ran on a local or remote system. Attempts to distribute malware are common in various attack types, but frequently follow spearphishing. For examples of malware we’re commonly observing, read our blogs on common and .
Steps You Can Take
Correctly configure email gateways to quarantine suspicious emails.
Keep security-awareness programs up to date with the latest phishing and social-engineering techniques.
Use multifactor authentication (MFA) in the event that employees’ credentials are compromised.
Block inbound emails that have file extensions typically used for malware delivery (e.g., those on executable files, such as .exe and .msi).
Configure a Group Policy Object (GPO) to change the default execution engine of JavaScript files from WScript to Notepad and any additional script files you see fit. This will prevent these files from being executed on the host.
Implement USB access control and GPOs to prevent autorun command executions. Consider disabling any removable media access if business conditions allow.
Attack Path of Least Resistance: Applications
We’ve often referred to the importance of by closing as many avenues of approach into your network as possible. Think of it as securely closing and locking your home’s doors and windows as you’re leaving. That’s exactly what you need to do with your network—ensuring there aren’t any unnecessary weak points that can be exploited to facilitate initial access.
We’ve discovered that exploiting public-facing applications (T1190) is the fourth most-prevalent technique. This involves threat actors attempting to exploit weaknesses, such as software vulnerabilities or misconfigurations, in systems or hosts that are accessible via the internet. Typically, adversaries use this method to gain initial access to a network. However, they may also employ it for other purposes, such as lateral movement within a system or evading detection.
Web servers are the primary target for this technique, but adversaries may also target databases, network administration or management protocols, or any other systems that have internet-accessible ports.
Of course, this is an agnostic threat to all sectors and geographies, but one that particularly impacts companies with poorly managed external-facing infrastructure. For an example of the ways threat actors attempt to exploit public-facing applications, check out our blog on common .
Steps You Can Take
To maintain clear visibility of assets, establish and consistently update an inventory of all assets. This enables system administrators to conduct regular risk assessments and promptly address any vulnerabilities or misconfigurations that may arise.
Ensure robust logging of assets to detect any suspicious activity. This enables a timely response to potential threats.
Harden MFA implementations by enforcing a certificate-based authentication policy, limiting the lifespan of MFA tokens, and educating users about common social-engineering techniques.
Persistence via Fallback Channels
The fifth most commonly observed technique was the use of fallback channels. These allow threat actors to use alternative communication channels if the primary channel intended for an attack is compromised or inaccessible. It ensures the uninterrupted flow of reliable command-and-control (C2) and helps avoid data transfer limitations. In the past, threat actors have exploited established fallback channels through the misuse of Cobalt Strike, a popular penetration-testing framework, to enable C2 over compromised devices.
We’ve frequently observed that remote management and monitoring (RMM) software, such as AnyDesk, Splashtop, and TeamViewer, are commonly used for persistence and C2 capabilities. Although these remote desktop applications are often used by system administrators for legitimate purposes, it’s crucial to exercise vigilant monitoring and caution when encountering unexpected installations of such tools.
Steps You Can Take
We recommend embracing a defense-in-depth (DiD) strategy, which involves a multilayered approach. This can be achieved by implementing the following technical and organizational measures:
Employ firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), and endpoint protection solutions. These tools safeguard your network and endpoints by continuously monitoring and blocking any suspicious activities.
Implement strong access controls, such as two-factor authentication (2FA), to add an extra layer of protection against unauthorized access to sensitive systems and data. 2FA requires users to provide two types of authentication credentials, such as a password and a unique code or biometric authentication.
Restrict company assets from establishing arbitrary connections with the internet using firewall or proxy configurations and ensure that only authorized connections are allowed. This will minimize the risk of malware infections and C2 activities.
By combining these measures, you can establish a comprehensive security posture that addresses different layers of your environment, enhancing its resilience against potential threats. ReliaQuest offers a suite of detection rules specifically designed to identify common threats, available through our GreyMatter .





