Consistency is the first word that springs to mind when assessing ransomware activity throughout the Q1 of 2021. There have been consistent double extortion ransomware activity levels, with key players in the threat landscape continuing where they left off in 2020, regularly adding data stolen from victims to their data leak websites. Consistent pressure from law enforcement has disrupted certain ransomware groups leading to drops in activity. Other groups have continued to vary their attack methods sustaining the high level of threat posed to global organizations.
Recently, the security world has had a heavy focus on impactful supply chain attacks, such as the SolarWinds software compromise and exploitation of Microsoft Exchange Server vulnerabilities. Still, ransomware continues to dominate the threat landscape for 2021. Let’s take a look at some of the key trends and emerging techniques observed by the Photon Research Team in our Q1 Ransomware Roundup.
“New” Beginnings for Ransomware in 2021
Following the quietest Christmas period in memory, the security community returned to work in early January more refreshed than in previous years. 2021 began much in the same way that 2020 had ended—with the emergence of a new double extortion-focused ransomware variant. Ransomware operators clearly didn’t get into the festive spirit but likely prefer to use this time for more malicious purposes.
On 03 Jan 2021, researchers reported on the newly discovered ransomware variant Babuk Locker. Like the variants that had paved the way, Babuk used a strong encryption mechanism, targeted large enterprises perceived as being able to pay hefty ransoms, and sought to leak the data stolen from its victims to coerce payment. Babuk began by leaking this data to cybercriminal forums. Still, the operators stated that they intended to establish a data leak website, the must-have accessory for any modern ransomware extortion outfit. Approximately two weeks later, the Photon Team began monitoring “Babuk Locker Leaks,” a dedicated site owned by Babuk’s operators to name and shame its victims.
Unsurprisingly, this trend continued into 2021. Since January 2021, there have been several other ransomware groups added to the team’s monitoring list. Variants such as “Cuba” and “Phoenix CryptoLocker” have emerged with similar modus operandi. Each new wave of ransomware continues to inspire the next, and each emerging group will likely reap the benefits of the highly lucrative double extortion method. Most operate in this way relatively uninterrupted for a while before the law inevitably catches up with them.
Increasing Crackdowns on Ransomware Operators
Although it may seem that ransomware groups have been running wild over the last 12-18 months, there has been a consolidated effort from international law enforcement agencies to crack down on these threat actors. Disrupting ransomware groups is no easy task, given that they are likely made up of various sub-groups and affiliates dispersed across several countries. Thankfully, law enforcement agencies are not entirely powerless, and collaboration between agencies has led to successful disruption.
On 27 Jan 2021, law enforcement agencies in Bulgaria and the US successfully disrupted infrastructure associated with the “NetWalker” ransomware. Authorities seized a server reportedly used to host dark web pages for victims to communicate with Netwalker’s operators; the same server hosted Netwalker’s data leak site. There was a significant drop in Netwalker activity since this operation, and the data leak site is still inactive.
On 12 Feb 2021, affiliates of the “Egregor” ransomware were reportedly arrested in Ukraine. Investigators had seemingly tracked Bitcoin transactions made by the individuals, which led to their arrest among other associations to Egregor operations. Egregor’s data leak website then saw a period of inactivity much in the same way that Netwalker’s did.
Both Egregor and Netwalker were among the most active ransomware groups in Q4 2020, but this had changed when we looked back over our Q1 reporting.
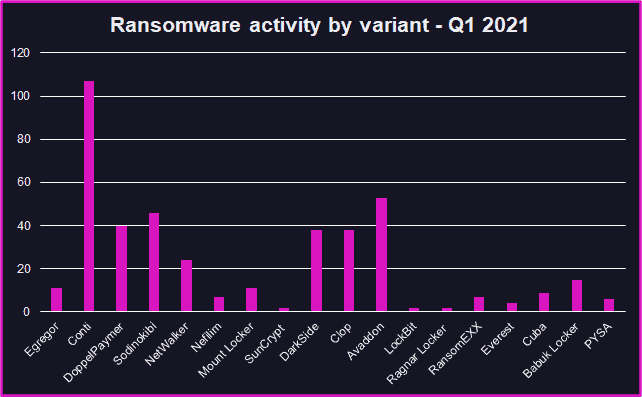
Intel Updates relating to new posts on ransomware data leak sites – Q1 2021
The disparate nature of membership or association with these cybercriminal enterprises means those remaining members may sometimes continue operations once the heat is off. It is no guarantee that law enforcement operations, such as those against Netwalker and Egregor, spell the end for these groups. However, this disruption is welcome and is likely to ruffle a few feathers among other prolific ransomware groups. It is realistically possible that these operations have even put some groups off continuing their attacks (see our interesting pick on Ziggy ransomware below).
Increasing Professionalization of Ransomware
Towards the end of 2020, the Photon team discussed the growing professionalization among ransomware groups. These groups had developed from low-level cybercriminals into established malicious enterprises with a range of methods used to extort their victims.
Increasing professional methods include:
Data leak sites
Social Media campaigns for extortion
Outsourced non-technical services (i.e. call centers for victim relations)
Outsourced technical services (i.e. bulletproof hosting)
The data leak websites were the beginning, before groups waged social-media advertising campaigns to publicize their attacks and reportedly used call centers to further harass their victims. The outsourcing of criminal services, such as anonymous domain registration and bulletproof hosting providers, helped to obfuscate ransomware attacks and gave operators a chance to splash some cash made from their endeavours.
These operational capability advancements have narrowed the gap between organized cybercriminal groups and state-associated advanced persistent threat (APT) groups. So much so that ransomware operators are now beginning to emulate the TTPs (tactics, techniques, and procedures) usually attributed to nation-state APTs.
Increasing Prominence of Supply Chain Attacks
State-associated APT groups typically favor supply chain attacks given the increased resources and capability needed to conduct these attacks successfully. However, growing professionalization across the ransomware threat landscape has led to greater involvement in supply chain compromise from the more advanced ransomware groups. Upon disclosure of the zero-day vulnerabilities affecting Microsoft Exchange Servers, existing ransomware variants such as “Black Kingdom” began exploiting the vulnerabilities. Moreover, a new ransomware variant named DearCry had targeted vulnerable Exchange Servers shortly after a proof of concept (PoC) attack had been published to Github on 10 Mar 2021.
Going after suppliers through the exploitation of zero-days is not novel for ransomware groups, but the extent to which these groups have successfully conducted this exploitation is certainly growing. In March 2021, the high-profile “Sodinokibi” (aka REvil) ransomware group demanded a USD 50 million ransom from the technology firm Acer, the highest recorded ransom demand to date. Although it was unconfirmed via independent sources, researchers stated that Acer had been targeted using the Exchange Server vulnerabilities.
The eye-watering amount of money being made by ransomware groups will likely fuel further expansion and a move towards more advanced TTPs that will sustain the success of ransomware operations. As this occurs, the gap between ransomware extortion groups and state-associated APTs will likely lessen even further.
Emerging Ransomware TTPs in Q1 2021
If you hadn’t already guessed, ransomware will continue to flood your feeds and news reels for the foreseeable future. Ransomware groups continue to grow in stature and capability, with no signs of slowing down anytime soon.
Q1 2021 was filled with interesting developments and new TTPs used by ransomware groups. The full extent of these details is available in the form of curated intelligence updates to ReliaQuest GreyMatter DRP clients (you can request a demo here), but here are some highlights.
Ransomware x DDoS: In a time where it would appear that extortion operations cannot get any worse, ransomware operators have begun to incorporate Distributed Denial of Service (DDoS) into their attacks. This threat was first observed in October 2020 when the “SunCrypt” ransomware conducted DDoS against its targets, and we discussed the possibility that more groups would adopt the tactic. In Q1 2021, both the “Avaddon” and Sodinokibi groups used DDoS in attacks to further extort their victims. This likely increases the pressure on victims, especially those who are not intent on paying the ransom, as they attempt to restore their systems. Any moves to back-up encrypted areas of the network will be exceedingly more difficult following a DDoS attack; this tactic will likely appeal to more ransomware operators given increasing pressure to not pay ransom demands.
Nefilim and “Ghost” credentials: No account is safe from compromise, including those belonging to deceased employees. The “Nefilim” ransomware group reminded us of this in January 2021, when the group compromised an administrator account for an employee that had passed away three months prior to the attack. This account’s access was then used to gather system information to support the deployment of the ransomware payload. Accounts that retain administrator privileges should be continuously reviewed to avoid any unwanted use of their access.
Ziggy ransomware shuts down and offers refunds: That’s correct, the Ziggy ransomware shut its operations down in February, released 922 decryption keys, and then started offering refunds to its victims. Moving from the unusual to the bizarre, Ziggy’s operators stated that they wished to turn towards ransomware hunting instead of conducting the operations themselves. It’s probable that increased pressure from law enforcement incentivized this move; however, given that the original ransom value was being refunded and Bitcoin prices have recently risen, the operators are still due to make a profit.
If ransomware is a threat not already on your radar, or if you are interested in learning more, we recommend a 7-day free trial of Threat Intelligence with SearchLight. ReliaQuest GreyMatter DRP clients receive real-time, actionable intelligence updates regarding ransomware activity, including analysis from our team of global analysts and intelligence on new posts to ransomware data leak sites across open and closed sources.
Note: This blog is a roundup of our quarterly ransomware series. You can also see our Q2 Ransomware Trends, Q3 Ransomware Trends, Q4 and 2020 Ransomware Trends blogs or get our free weekly threat intelligence writeup delivered to your inbox here.





