As we embark on the final months of 2020, ransomware has been the main topic of conversation once again. Throughout Q3, it seemed like not only was there a new attack reported every day, but that new variants and new data leak sites were popping up each week. Even further, Mount Locker ransomware was identified in the wild, Conti ransomware operators created new data leak sites, and attackers targeted the University of York in a ransomware attack. The list goes on and on.
We additionally saw several well-known ransomware operators creating data leak sites to extort victims further. To add to the already stressful situation of encrypted files and locked systems, organizations face the panic of having sensitive data leaked to the public through these sites. The “pay or get breached” trend took off like a rocket and gained popularity with ransomware groups once again in Q3.
While monitoring the ransomware activity throughout Q3, I started thinking about what my grandfather always said to my cousins – “monkey see, monkey do” – which seems to be precisely the game that ransomware groups are playing. In Q3, we identified an additional seven data leak sites created. Rather than list all the new websites and their alleged victims (which we know can be boring), we wanted to focus on some of the latest ransomware news we’ve seen throughout Q3 2020 – here’s what we found:
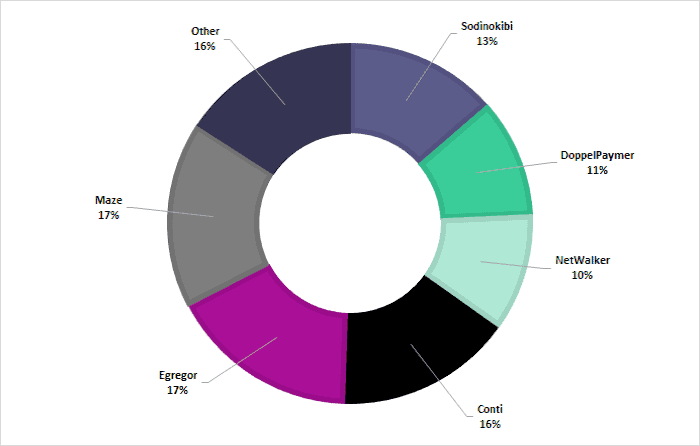
In Q2 2020, Maze, DoppelPaymer, and Sodinokibi made up 80% of our alerts related to ransomware dump sites; however, in Q3 2020, DoppelPaymer decreased their activity while other groups entered the ransomware landscape and hit the ground running.
Conti and NetWalker ransomware groups made their entrance to the ransomware landscape and accounted for 29% of the our alerts related to ransomware dump sites. This scenario may pave the way for new or less well-known groups that are looking to get into the ransomware business.
Over time, initial access brokers have enabled ransomware operators by acquiring network access. This service removes the complex process of gaining network access, figuratively unlocking and opening the door for ransomware groups to carry out their attacks.
A Sodinokibi spokesperson updated an Exploit post in late September 2020, detailing the group’s interest in recruiting more team members, specifically those with penetration testing skills.
The Exfiltration Saga Continues
In the second quarter of 2020, Maze, DoppelPaymer, and Sodinokibi seemed to rule the ransomware scene with reports of ransomware attacks every day. In Q3 2020, Maze continued to make news headlines; however, more ransomware operators joined in on the data leak site trend.
Our intelligence team has been tracking when the data leak websites name specific companies, which indicates they are likely to have been a victim of attacks related to respective variants.
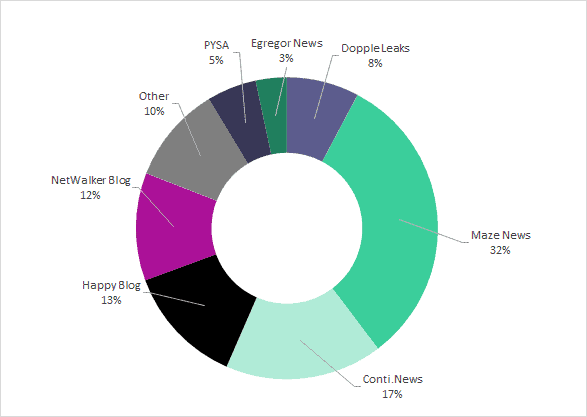
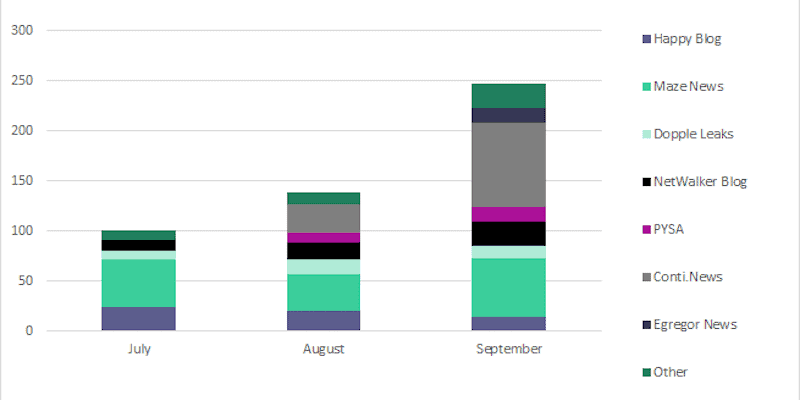
Most popular ransomware blog locations in Q3 2020, as reported in Digital Shadows (now ReliaQuest) Intelligence
While Dopple Leaks saw fewer postings in Q3 than in Q2, NetWalker Blog saw an increase in postings. The Conti.News site was identified during Q3 2020, and hit the ground running when they started the site. Other sites accounted for 10 percent of Digital Shadows (now ReliaQuest)’ alerts and consisted of Ako, Avaddon, Ragnar Locker, SunCrypt, LockBit, Mount Locker, and Clop ransomware operators’ data leak sites.
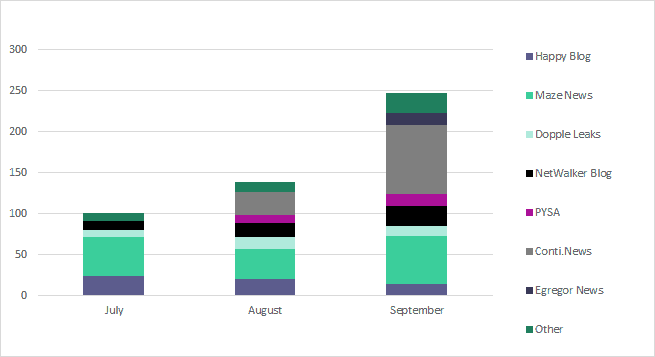
Distribution of ransomware blog sites across July, August, and September, as reported in Digital Shadows (now ReliaQuest) Intelligence
Monkey See, Monkey Do
Digital Shadows (now ReliaQuest) tracks a large number of ransomware dump sites, as you can see above, and has added even more sites since our last update for Q2 2020. Security teams can use this visibility to identify suppliers or third-party vendors referenced on ransomware dump sites.
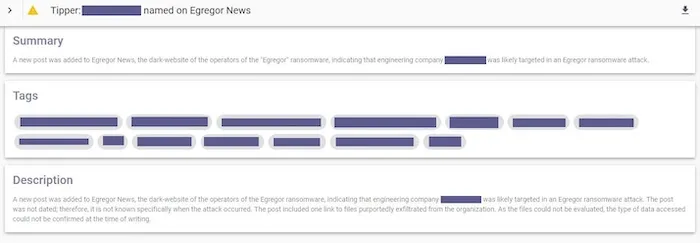
A screenshot of a tipper intelligence alert reporting on affected companies
In Q2, we reported that 80% of the Digital Shadows (now ReliaQuest)’ intelligence tippers were associated with just three of the ransomware data dump blogs – DoppelPaymer (Dopple Leaks), Sodinokibi (Happy Blog), and Maze (Maze News). In Q3 2020, Maze News, Happy Blog, Conti.News, and NetWalker Blog make up 80% of the alerts published.
**NetWalker.**Active since April 2019. NetWalker operates as closed-access ransomware-as-a-service (RaaS), whereby cybercriminals sign up and undergo a vetting process before being granted access to a web portal that they can build custom versions of the ransomware. In March 2020, the NetWalker group’s nature shifted: from cybercriminals specializing in mass-distribution methods to those specializing in targeted attacks against the networks of high-value entities. NetWalker gained notoriety after a ransomware attack that targeted Toll Group in March 2020.
In July 2020, the FBI released a flash alert warning of NetWalker ransomware attacks on US and foreign government organizations, educational institutions, private companies, and health agencies. The alert warned that the NetWalker group was utilizing COVID-19 themed phishing emails that contained a malicious attachment.
The NetWalker ransomware group maintains the NetWalker Blog site, where they leak victims’ data when a ransom demand goes unpaid. Posts on the dump site typically include screenshots of documents and file directories, purportedly exfiltrated from the victim organization’s network.
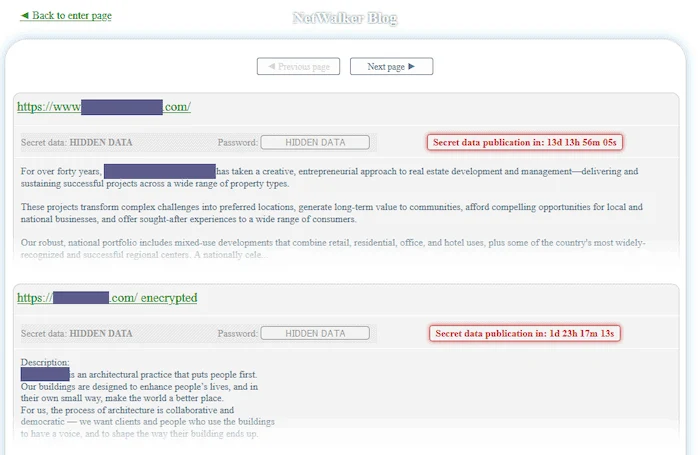
Screenshot of NetWalker Blog
**Conti.**Active since December 2019. Conti is believed to be derived from the “Ryuk” ransomware variant. Ryuk and Conti share the same code and similar attack methods; however, the two variants’ link is unconfirmed. Conti has been observed targeting multiple sectors that include construction, manufacturing, and retail. The Conti ransomware operators do not appear to target any specific geography and have been observed targeting organizations in the US, the UK, Spain, France, Germany, and Canada.
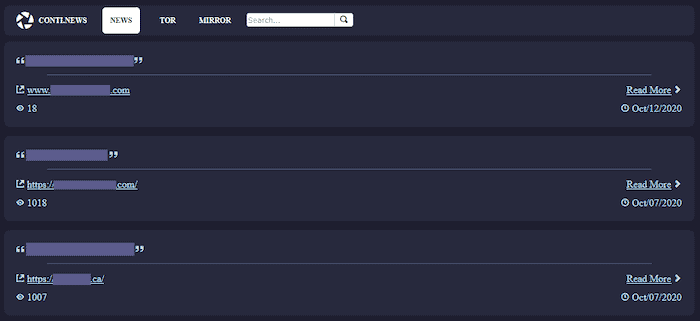
Screenshot of Conti.News home page
Cybercriminals Tend to Take the Path of Least Resistance
In our last quarterly ransomware report, we provided an overview of vulnerabilities commonly used by ransomware groups to gain initial access to a network. Since the vulnerabilities remain the same, we wanted to focus on tactics other than vulnerability exploitation: initial access brokers and account takeover.
Initial Access Brokers
The NetWalker ransomware, unlike other variants, is a closed-access group, where affiliates are vetted before being granted access. One of the affiliates’ requirements is to have pre-existing access to large networks, thus giving initial access brokers the perfect target audience for their accesses and posts.
Ransomware developers continue to update and create variants, creating a cybercriminal platform saturated with RaaS variants. Thus, prominence and notoriety are vital to the success of a ransomware group. Ransomware operators hire affiliates to identify and target victims, which has shifted attention to initial access brokers.
Initial access brokers attempt to gain access to vulnerable organizations that they can then sell on criminal marketplaces. Many advertised accesses encompass remote access through Remote Desktop Protocol (RDP) or a compromised Virtual Private Network (VPN). Ransomware groups have been observed using RDP as a common attack vector. Once an initial access broker moves through the network, attempting to escalate privileges, they determine a reasonable price at which they can sell their access.
Account takeover
Credential harvesters use a combination of techniques to acquire victims’ details. While many account takeover attacks are conducted on social media or financial accounts, we’ve also seen some criminal advertisements for domain administrator accesses. This scenario raises the access from a single user account to a complete network compromise. Network-wide account takeover can enable a threat actor to change system configuration settings, read and modify sensitive data, and exfiltrate sensitive or proprietary data. These accounts are precious in the criminal underworld and can offer network access to ransomware groups and their affiliates.
It is not uncommon to see credential lists and network accesses mentioned across criminal forums, as shown below. Understanding how often these appear in criminal discussions gives security teams useful context on current attack vectors and vulnerabilities exploited to prioritize patching, security training, and other tasks.

Screenshot of network accesses advertised on criminal forums
How to Stay in Front of the Eight Ball
For teams seeking to find earlier information about new and upcoming variants or identify when known groups start new programs, it is possible to locate adverts across criminal forms. For example, a Sodinokibi ransomware spokesperson updated a post in September 2020, offering three new positions in their affiliate program. To show their commitment and offer “peace of mind” to potential recruits, they deposited USD 1 million into their account on the Russian-language cybercriminal forum, XSS. Additionally, we identified an advertisement for an affiliate program with an unnamed ransomware variant in July 2020. These posts typically provide details on the variant and the type of benefits the group offers to affiliates. Tracking these conversations and offers can aid security teams in identifying the most popular and successful variants.
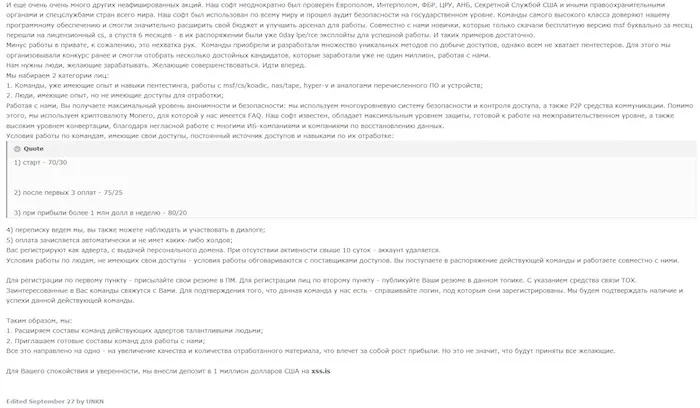
Post advertising new affiliate positions with Sodinokibi group updated in September 2020
Advertisement for an unnamed ransomware affiliate program in July 2020
SearchLight’s Intelligence on Ransomware Trends
With ransomware seemingly lurking behind every corner, the task of tracking these trends can be overwhelming, and it is easy to get lost in information overload. By highlighting specific use cases, you can focus on gaining actionable insights from ransomware trends.