Note: This piece is a follow-up on our previous blog, Emotet Disruption: What it Means for the Cyber Threat Landscape, expanding on significant law enforcement actions since the start of Jan. 2021.
While many of us have spent the beginning of 2021 at home, shamelessly hitting the “yes I’m still watching” button, international law enforcement has been busy tackling cybercrime. But “busy” might even be an understatement. In the last two months, law enforcement took down a major dark web marketplace, arrested operators of a prolific malware variant, and disrupted two infamous ransomware groups. Now is an ideal time to look back at all this activity and consider the question: what difference do these actions make in the cybercriminal threat landscape?

A Timeline of Takedowns, Cybercriminal Arrests, and Disruptions
Dark Market
In mid-January, Europol issued a press release to its website letting us know that the dark web marketplace DarkMarket had been taken offline in an international law enforcement operation. According to Europol, DarkMarket had almost 500,000 users, more than 2,400 sellers, and had facilitated money transfer equating to more than €140 million. Taking the lead, officers in Germany arrested an Australian citizen, allegedly the operator of DarkMarket, and seized more than 20 criminal servers in Moldova and Ukraine. Officers from Denmark, the UK, and the US were also involved; international collaboration at its finest.
Emotet
On 27 January 2021, Europol was again issuing another press release detailing the technical take over of Emotet infrastructure. Machines compromised by Emotet malware were redirected to infrastructure controlled by law enforcement. Ukrainian officials also arrested two individuals believed to be part of the criminal group responsible for operating Emotet. As if that wasn’t enough, law enforcement is also planning a mass uninstall of Emotet from all compromised devices on 25 April 2021.
You might think this delay seems odd (aren’t they leaving victims vulnerable unnecessarily?) but, it’s pretty savvy. Emotet is a well-known dropper of other malware. The extra time means that security professionals can hunt for the presence of Emotet within their network. If they discover it, they can go on in search of other malware typically dropped by Emotet. Without the initial Emotet clue, any further infection may have gone undetected for weeks, months, or even years.
NetWalker
The following day, Bulgarian officials announced they had seized a server used by NetWalker ransomware operators. Meanwhile, US officials indicted a Canadian national who allegedly made at least $27.6 million as a NetWalker “affiliate,” demanding ransom payments from companies whose networks they had encrypted with NetWalker. The server hosted websites the NetWalker group used to communicate with their victims, negotiate ransom demands, and leak data stolen from compromised companies who refused to pay up.
Egregor
To end this flurry of activity, news outlets in France reported in mid-February that officials had arrested affiliates of the Egregor ransomware-as-a-service (RaaS) program. At the time, the arrest was unconfirmed by law enforcement, but the Egregor website was already offline. Confirmation didn’t take long to come: On 17 Feb 2021, the Ukrainian Security Service (SBU) stated they had arrested individuals and seized computer equipment associated with Egregor, with the help of law enforcement organizations from France and the US.
The SBU statement said, “members of the specified hacker group, including the organizer, were informed about the suspicion of…criminal offenses” and estimated losses as a result of Egregor activities to be more than $80 million. Interestingly, the Ukrainian website was down when I tried to access it last week. This week, it transpired that the website was suffering a distributed denial of service attack that originated from Russian networks. Researchers have commented that unknown threat actors may have conducted these DDoS attacks in retaliation to the Egregor arrests.

Image provided by Ukrainian officials from the Egregor arrests
What is with the Continued Absence of Emotet?
After the announcement, we published a blog on Emotet’s supposed closure where we detailed cybercriminal reactions to the takedown and predicted how it might affect the cybercrime marketplace. A month has nearly passed, and Emotet has been noticeably absent from the cyber news sphere.
While it’s not unusual for Emotet to take a break from activities, February’s hiatus is likely a direct result of their operational disruption. Law enforcement targeted Emotet’s infrastructure from the inside, redirecting traffic to law enforcement-controlled infrastructure and enabling a mass uninstall. This approach has caused a catastrophe for Emotet’s operators, wiping out their entire botnet in the blink of an eye. Emotet has been in operation since at least 2016, and a single infection could lead to multiple device compromises, so the loss of its entire infrastructure is significant. It is likely that the effects of this takedown, or takeover, will be felt by Emotet’s operators for months to come. Attacking from the inside has also likely given law enforcement a unique insight into the botnet’s inner workings. This knowledge will better prepare law enforcement for the fight against whatever appears in the marketplace to take Emotet’s crown-—it’s not a matter of if, but when.
Let’s not forget, some, but not all, of Emotet’s operators, were also arrested as part of this coordinated effort. In my view, arrests are essential in conjunction with technical takedowns to ensure a long-term impact. For example, the attempted takedown of Trickbot was purely technical, therefore Trickbot was back up and running with minimal delay. These arrests will likely have hit the Emotet group hard, and those left behind will be carefully considering their next move. There is always the outside chance that these criminals might decide to hang up their cybercriminal boots and sail away into the sunset with their billions of dollars, but I’m confident that they’ll be back. Whether that’s with a new and improved Emotet or with the next big thing, building that enterprise will take time, giving us a little respite.
Inevitably, the absence of Emotet will give other existing threats a chance to grow. The malware and ransomware variants previously dropped by Emotet will find a new way to reach their intended victims. While Emotet dropped both Trickbot and Qbot (or Qakbot), both can compromise victims in their own right and deploy multiple ransomware variants post-compromise. Ransomware operators can also turn to initial access brokers to gain a foothold on a victim network. Researchers had hoped Emotet’s demise would lead to a decrease in ransomware attacks; no such luck.
Read our new report, “Initial Access Brokers: an Excess of Access”, here.
What is the Difference Between Ransomware Affiliates and Operators?
Both NetWalker and Egregor ransomwares operated a RaaS model. RaaS works like this:
A threat actor or group have control of a ransomware variant; they are its operator/s
Affiliates rent the ransomware from its operator/s for a fee, usually a percentage of the ransom payment
Affiliates use the ransomware to encrypt a victim and demand a ransom payment
Once the affiliate receives that ransom payment, the agreed percentage is returned to the operator/s while the affiliates keep the remaining amount
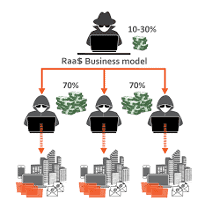
RaaS business model (Source: KnowBe4 )
This model provides the operators with several benefits. The number of victims that the ransomware variant encrypts increases exponentially using an affiliate network (many hands make light work). It also means that profits will rise at the same rate. As the affiliates conduct and carry out the majority of ransomware attacks, the operators are often absolved of incriminating action. This distance reduces their risk of being subjected to arrest by law enforcement.
In both examples of law enforcement action above, it was reportedly only affiliates arrested. However, the SBU also claimed they apprehended the organizer of Egregor, but it is still unclear whether the whole of the Egregor network is dismantled or not. Infrastructure was also seized in both examples, cementing law enforcement’s readiness to take a holistic approach to takedown operations.
Many of the same considerations I raised with Emotet apply here, but this time it will depend on who the arrested individuals were. If, as suggested, the SBU arrested the operator of Egregor, then there is much to celebrate. However, if it turns out to be an affiliate, the operator remains at large. Time will tell. If Egregor is gone for good, it will be interesting to see what comes next.
Egregor was widely reported as a successor to Maze, with many Maze affiliates reportedly moving to deploy Egregor. When Maze closed itself down, its (slightly odd) press release did allude to a return with some additional capabilities.
With their main competitors removed, perhaps the Maze operators will now take their opportunity to return to prominence in the ransomware market. Alternatively, an existing ransomware operator could capitalize on Egregor’s absence. Whoever the next key operator may be, the threat from ransomware is unlikely to cease. Despite the law enforcement interruption of ransomware gang activities deterring some operators, the potential profit is too high to cybercriminals to neglect this model.
Get our review, Ransomware: analyzing the data from 2020, here.
What is the Impact of Law Enforcement on Cybercriminal Forums?
As a quick aside, there have been some unintended outcomes from the law enforcement surge of 2021. Arrest news always creates a ripple within online cybercriminal forums, with some discussing who might be next. The Ziggy ransomware variant operators have shut down their operations, citing law enforcement action as one reason. Joker’s Stash has also announced that it will close permanently later this year. At the end of 2020, Joker’s Stash was targeted in an alleged law enforcement operation. However, officials never publicly claimed the takedown, but some of the Joker’s Stash domains did display seizure notifications. As operators become aware of the additional scrutiny on them or the market they operate in, the best course of action for some is closure.
Predictions for Cybercriminal Crackdowns in 2021
Whether malware, ransomware, or another cyber threat, scolded operators, if not detained, will eventually return. They have the skills, experience, and intent to create a new successful enterprise. They also have connections within the criminal community that will allow them to rebuild their infrastructure and social networks that they may have lost due to law enforcement action. So long as they use new tactics, new infrastructure, and new names, they will likely operate uninterrupted by law enforcement for months, if not years.
That shouldn’t be a deterrent to law enforcement, though. They must build on the momentum gained during 2021 to sow discord and distrust throughout the cybercriminal community. For some, the fear of law enforcement intervention will be enough to cease operations. For others, it won’t, and therefore law enforcement needs to use the knowledge they have gained from these takedowns. Use the detailed technical knowledge gained about Emotet to spot the early warning signs of a new significant tool and act before it becomes unwieldy: Use arrests and infrastructure in conjunction to have a longer-term impact.
<c/enter>




