The ReliaQuest Threat Research Team specializes in monitoring the deep, dark corners of the internet—keeping tabs on threat actor groups, lurking on dark web forums, and analyzing the events that crop up in the ReliaQuest GreyMatter security operations platform.
The time period between February 1, 2022, and February 1, 2023, was eventful, to say the least: it saw Russia’s invasion of Ukraine, a higher incidence of ransomware attacks than ever before, and an avalanche of high-risk vulnerabilities. The Threat Research Team has kept a close eye on all these events and everything in between, analyzed their findings, and presented it in the first-ever .
In this blog, we’ll summarize a few of the key findings of the 30-page report.
At-Risk Industries: Construction and Transportation
Over the reporting period, we saw the most true-positive incidents occur in the environments of our customers in construction and transportation.
These industries are uniquely vulnerable to disruption, and with their perceived lack of cybersecurity maturity, controls, and tools, they are being targeted by threat actors more than any others.
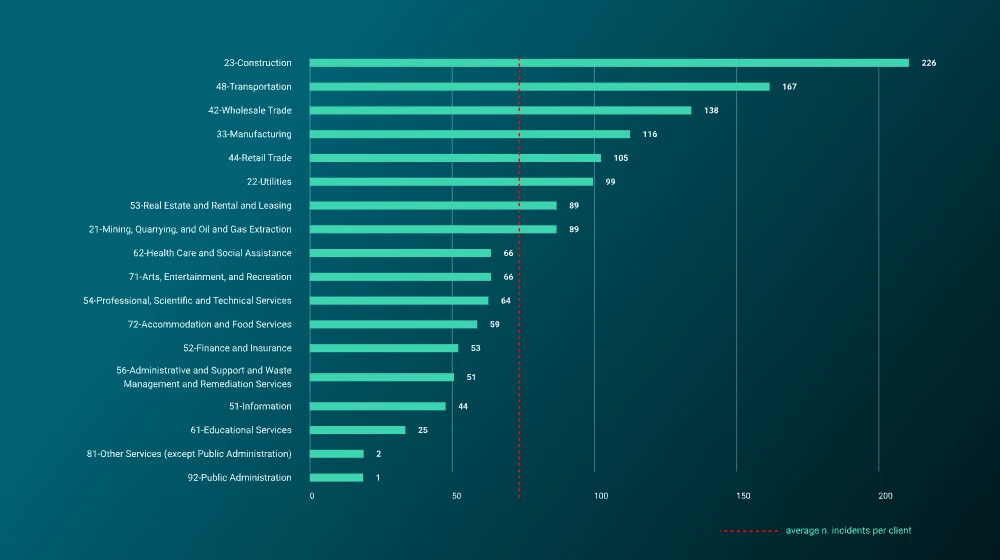
Average number of incidents per customer sector
As for ransomware, the companies named on data leak sites were most commonly from the manufacturing sector.
Ransomware Trends and Most-Active Groups
Speaking of ransomware—it continues to pose a growing problem. During the reporting period, ransomware activity spiked and dipped with a fair bit of fluctuation. The most active month was April 2022, followed by a dropoff in May.
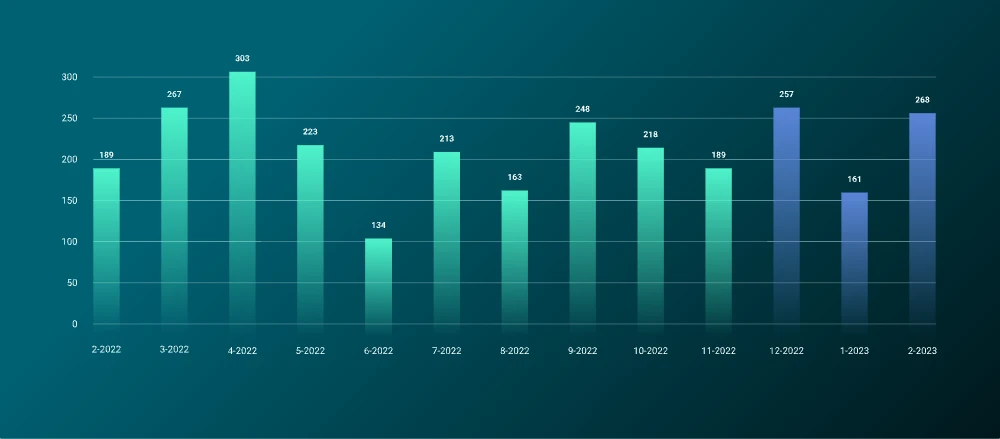
Number of victims named on ransomware data-leak sites, by month
The most active group, by far, was LockBit. The group put out almost a thousand posts naming victims on its data-leak site over the year. (Download the full report for an in-depth look at LockBit’s activity.)
The next-most-prolific group was AlphV, but it wasn’t even close. They had relatively few posts, with 273 for the year.
Initial Access Broker (IAB) Trends
Initial access brokers (IABs) act as the middlemen of the cybercrime world, providing ransomware operators with victims to compromise. They find vulnerable organizations and sell access to their environments to the highest bidder on dark web forums.
The most common access type listed by IABs over the reporting period was remote desktop protocol (RDP), which allows a computer to control another computer over a network connection. About 24% of all ReliaQuest tippers published in the reporting period referred to RDP. It was also the costliest type of access being offered, at about $1000 apiece.
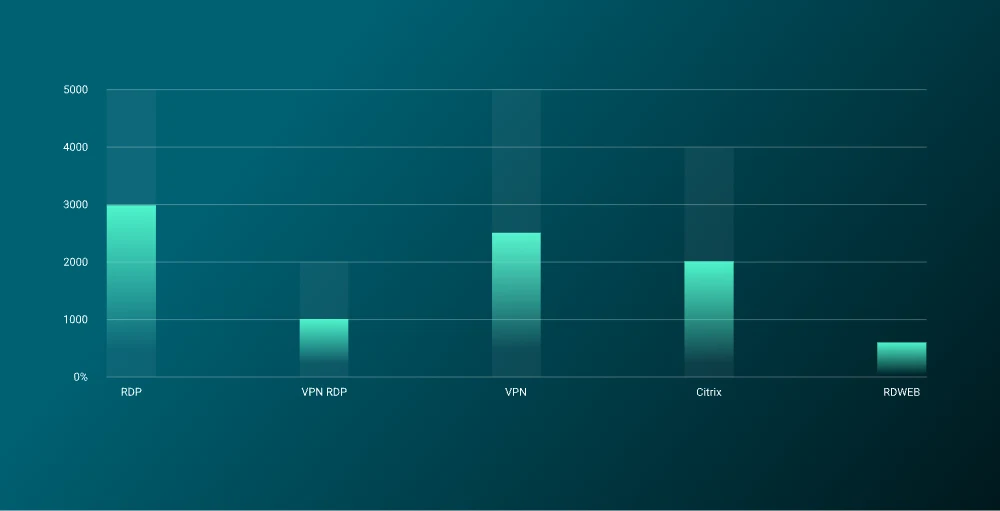
Most common IAB access types listed for sale, and price ranges, 01 Feb 2022–01 Feb 2023
The country most targeted by IAB activity? Overwhelmingly, the United States. Some cybercriminals frequently perceive US-based companies as offering large financial rewards, while others may focus on the United States for political reasons.
Each sector faces unique challenges, many of which are highly dependent on a company’s business model or operating requirements. Some risks will be more pertinent for certain sectors; however, any organization can take steps to minimize possible impact. Visibility and context is key—understand what specific threats your business faces and apply compensating controls where appropriate.
Ransomware remains the biggest risk facing business in 2023. Ransomware actors are agile, resourceful, and capable of reacting to defenders’ actions in changing their tactics. It is likely that the ransomware ecosystem will become more saturated in 2023, with the introduction of several new groups. Keeping abreast of the latest developments in TTPs of ransomware activity, in addition to tracking groups known to be targeting your sector, is the best way to stay ahead of the curve from this pernicious activity.
The exploitation of remote services will continue to represent arguably the most common abuse point for entering your network, by both cybercriminals and nation-state aligned threat actors, across all sectors. Ensure that remote services are not unnecessarily external facing, patched with strong authentication measures in place, using the principle of least privilege to ensure only individuals who need to do their job can access them.
How ReliaQuest Can Help
Put our threat intelligence technology to work for you. With the ReliaQuest GreyMatter security operations platform, you can get unparalleled visibility into your entire ecosystem—and beyond.
The capability is fully configurable; use our pre-defined set of threat feeds or even add your own. We’ll take that data and return actionable insights on threats and IoCs. And with (DRP), you can be sure your data is safe outside your environment too.