Over the course of 2020, ReliaQuest detected over 500 cybercriminals’ listings advertising network access across a multitude of industry verticals. In our recent research piece, Initial Access Brokers: An Excess of Access, we analyzed the role played by this emerging figure in the broader criminal infrastructure of ransomware.
Our monitoring of Initial Access Brokers (IABs) goes back as far as 2014, as we’ve been tracking the sale of access to systems since the practice first began making ripples in the cybercriminal underground. Initial access brokership isn’t a business model spun off the COVID-19 pandemic; its popularity and profitability have simmered beneath the surface since the early days. However, since ransomware has continuously been making headlines throughout 2020, understanding the roles various actors play in this ecosystem is crucial to preventing and mitigating IABs as a severe threat.
What is an Initial Access Broker (IAB)?
Initial Access Brokers (IABs) do the technical dirty work by providing ransomware operators with a wealth of victims to compromise. A symbol of cybercrime professionalization, Initial Access Brokers act as a middleman by finding vulnerable organizations and sell accesses to them to the highest bidder on dark web forums. Their rise in popularity follows the trend of lowered barriers to entering the world of cybercrime.

Threat actor advertising an OOB RCE for a Portuguese bank on a cybercriminal forum
As shown in one of our blogs on IAB’s supporting role to ransomware operators, initial access brokers gain network access to vulnerable organizations, likely identifying targets indiscriminately through publicly available scanning tools. Once they set foot inside the victims’ network and establish the access’ value, IABs then turn to their cybercriminal forums of choice to advertise the access and cash in on their work.
Outright naming the targeted organization was common practice in the beginning in order to give authenticity and prove value for the accesses. Now, the listings are usually heavily redacted of company names and logos in order to avoid detection by law enforcement or threat intelligence providers such ReliaQuest.
This practice is a testament to the Operational Security (OPSEC) developments among cybercriminals who are increasingly more aware of security researchers’ presence within these forums. By avoiding to name the victim and instead rely on their size, region, and industry, IABs can still offer clients an indication of the potential target without offering Cyber Threat Intelligence (CTI) teams an easy chance to stop their operations.
An Excess of Accesses: 2020 by initial access brokers
ReliaQuest analyzed more than 500 listings in 2020 and observed that initial access brokers could exploit various access types for their activities. A reason for this is because IABs have a vast spectrum of sophistication and technical expertise. However, their potential lack of technical knowledge doesn’t make these actors any less of a threat. Because they’re also less specialized, they tend to be customer agnostic and sell their accesses to the highest bidder.

Popular access types and their average prices
As a consequence of diffused remote working models enforced in 2020, Virtual Private Network (VPN) accesses were among the top three accesses listed in cybercriminal forums. This fact shouldn’t come as a surprise—unpatched software and weak credentials are unfortunately present on corporate laptops, making organizations vulnerable to external cyber threats. ReliaQuest observed that the average price for a VPN access is set around $3,000, with prices varying based on the organizations’ size, geographical location, and industry (see full report for more data).
Industry breakdown of initial access broker targets
After having spent tons of hours with our noses in the data, one thing is sure: IABs will target anyone. Listings varied enormously in terms of the victim being advertised on cybercriminal forums. No industry is safe from their tools scanning for unpatched vulnerabilities and reused credentials. The graph below shows it quite nicely:

Breakdown of listed accesses by industry with respective average prices
According to our data, the technological sector maintains the highest prices per access on average ($13,607). There are plenty of reasons why this industry is the most sought-for among cybercriminals. The SolarWinds compromise has demonstrated the risks connected with third-party providers and supply-chain attacks. Technology providers can be compromised to pivot towards their users across all verticals; that’s why selling access to these companies can be an extremely rewarding experience for initial access brokers.
Geographical breakdown of initial access broker targets
The targeted organization’s geography is another crucial discriminating factor when initial access brokers decide the selling price of their accesses. Throughout the data analyzed, we’ve seen much variety in terms of targeted countries.
However, companies located in the United States were by far the most compromised ones in the general landscape, accounting for roughly a third of all the listings observed. Make sure to check our report for a thorough breakdown of the impact of IABs by geographical region.
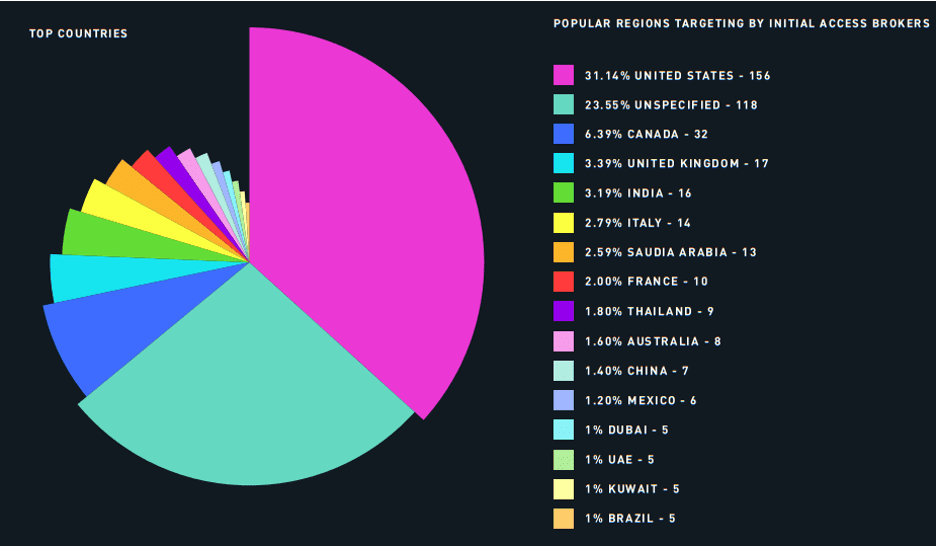
Countries most affected by initial access brokers’ listings
Mitigation of Initial Access Brokers
Mitigation strategies depend on the type of access being listed by the threat actor. Along with access type-specific tips, ReliaQuest has also identified some critical advice that your organization can use to prevent these listed accesses from being exploited by malicious actors.
The prominence of IABs in the attack chain offers an opportunity for defenders to thwart potential attacks. Although not a foolproof measure, identifying an IAB listing that affects your organization may open up a door to stopping an attack before it happens.
Having an in-house or out-sourced Cyber Threat Intelligence team monitoring the surface, deep, and dark web can go a long way in identifying relevant listings and observing access trends. If provided with timely, relevant, and actionable intelligence, defenders can prioritize security efforts toward the most significant threats.
Preventing cybercriminals from getting access to your organization should be the priority. However, having a dedicated team monitoring the IAB landscape can provide defenders with an additional tool to avoid more impactful incidents from happening.




