Every year, the FBI puts out a report compiling the data from its Internet Crime Complaint Center (IC3). The Internet Crime Report has become a barometer for the state of cybercrime, particularly as it relates to the public sector.
In addition, our threat research team monitors threats to businesses, based on both what we see in our customer environments and on observed cybercriminal chatter from the open, deep, and dark web.
Examining our data alongside the IC3 report provides additional context to the trends in cybercrime and how they affect organizations as well as individuals.
In this blog, we’ll look at some of the major themes in this year’s IC3 report, and what you can do to protect your organization.
The Persistent Threat of Phishing
Phishing stands out as the most-reported cybercrime in the IC3 report, with nearly six times the number of reports than the next most common type. Despite a 7.7% decrease in phishing reports from its peak in 2021, the frequency of these incidents has skyrocketed by 160% since 2019.
ReliaQuest data reveals that phishing methods were the most observed true-positive Tactics, Techniques, and Procedures (TTPs) in 2023, with spearphishing being particularly noteworthy. Over 70% of observed phishing incidents involved spearphishing tactics, including targeted links, attachments, and internal campaigns. We also observed evolving phishing tactics like drive-by compromise (some of which used new persistence methods) and QR code phishing.
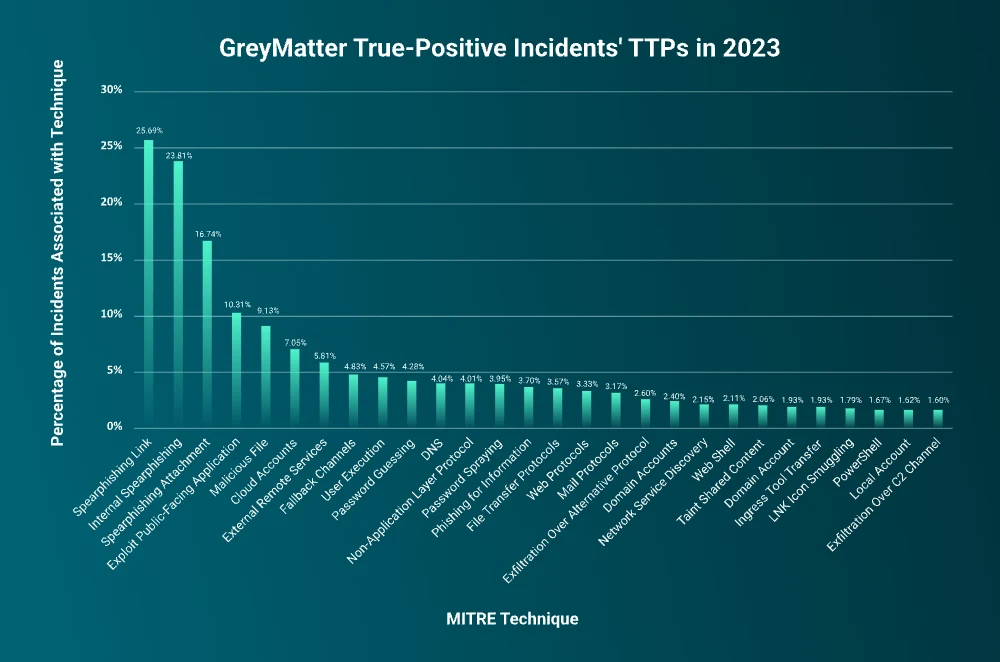
Because spearphishing targets specific individuals perceived to have higher access, organizations need to take particular care against phishing. Even fundamental controls can help, like implementing strong email filters and MFA. Education is also beneficial, but technology is your first and last line of defense. Automation in particular can be helpful in combating phishing.
Business Email Compromise Attempts Surge
Business Email Compromise (BEC) attacks, while constituting just 2.4% of the total complaints received by the FBI in 2023, emerged as a notably lucrative avenue for cybercriminals, trailing only behind investment-related crimes such as cryptocurrency scams in terms of financial impact. Despite its profitability, the FBI noted a slight decrease in BEC complaints by 1.5% compared to 2022.
The ReliaQuest data shows a larger growth trend. This year, we saw a 246% surge in BEC attempts in our customer environments compared to 2022. This discrepancy can be attributed to a few factors:
The IC3 likely reflects only reports of successful and publicly acknowledged attacks , while the ReliaQuest figures encompass all observed BEC attempts within our database of customers.
IC3 data is primarily derived from individual complaints, whereas ReliaQuest data originates from the environments of its business customers.
BEC self-reporting tends to be low, which means the IC3 number almost certainly represents only a fraction of total BEC events.
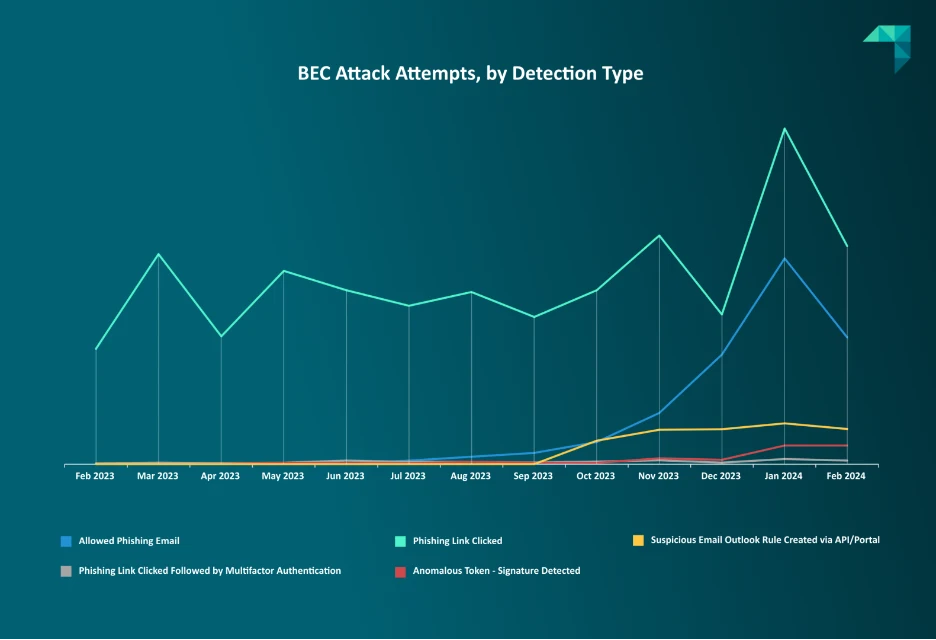
We predict that BEC attacks against organizations will continue to grow as attackers get more sophisticated and bring in new tools like generative AI and phishing kits tailored for BEC.
To protect your organization against BEC, we recommend securing administrative accounts, enforcing strict location-based access, adopting advanced multifactor authentication, and regularly refining access policies.
Ransomware Has Higher Cost per Attack
The IC3 report from 2023 highlights an alarming trend in the ransomware landscape, noting an 18% increase in incident reports alongside a 74% surge in financial losses due to these attacks. This suggests that ransomware groups are demanding, and likely receiving, higher ransoms per attack. ReliaQuest data supports this view—we’ve observed ransomware groups using new methods to pressure their victims: ALPHV went to the SEC to report data exfiltration they themselves perpetrated in an attempt to shame the affected company into payment.
The IC3 states that the health care and public health sector felt the brunt of this wave, reporting the highest number of incidents. According to the ReliaQuest fourth-quarter ransomware report from 2023, industries such as manufacturing; professional, scientific, and technical services; and construction also faced significant challenges from ransomware attacks.
Both the IC3 and ReliaQuest identify LockBit as the year’s most active ransomware group, indicating its widespread influence across industries.

Mitigation strategies for ransomware include:
Implementing application allowlisting to prevent unauthorized software from running
Ensuring operating systems and applications are fully patched
Raising security awareness among staff
Utilizing advanced threat detection tools
Maintaining properly configured firewalls and intrusion-prevention systems
Juxtaposing the FBI’s IC3 report and ReliaQuest data provides a multifaceted view of the current cybercrime landscape. While the IC3 report offers a valuable perspective on cybercrime trends within the public sector, ReliaQuest insights shed light on the broader spectrum of threats to organizations across various industries and highlight critical areas where organizations can focus their defensive strategies.
As cybercriminals continue to innovate and exploit new technologies, understanding these trends and implementing robust security measures becomes indispensable. Vigilance, education, and cutting-edge technology are paramount in fortifying defenses against the ever-growing wave of cybercrime.




