Editor’s note: This is part two of a four-part series on applying automation to security operations. It was last updated on February 7, 2025.
Part one: A Practical Approach to Automating Cybersecurity Playbooks
Part two (this blog): Automating Your Phishing Playbook
Part three: Automating Your Malware Playbook
This is the second installment of our blog series on taking a practical approach to security operations (SecOps) automation. In our initial blog, we set the stage by exploring the foundational concepts of automating the response playbook for common cyber threats.
Today, we prove that automation is not just a buzzword, but a vital tool against a cyber threat that’s all too familiar to both security practitioners and organizations: phishing. Its insidious nature and constantly evolving tactics demand an agile and rapid response to effectively reduce the mean time to resolve (MTTR). According to our 2025 Annual Cyber-Threat Report, implementing automation and AI can reduce MTTC for threats like phishing to as little as 3 minutes. While some organizations may hesitate to embrace automation in addressing this threat, this blog will highlight why automating the phishing playbook is not just a prudent choice but a necessary one.
To help alleviate the hesitation, we’ll show practical ways to minimize the risk associated with automation. We’ll prescribe the practical strategy security practitioners, incident responders, and cybersecurity leaders can adopt to automate the three critical phases of a cybersecurity response playbook: containment, investigation, and remediation.
Containment: Swift Response to Stop the Spread
The initial defense line against threats, the containment phase, swiftly isolates and limits the impact of a security incident, essential in responding to phishing attacks. By automating containment, organizations can reduce the mean time to contain threats from hours to minutes, enabling rapid response and effective damage control. Below are automated actions that can be configured within a security operations platform to execute automatically after known-bad phishing-related detections like Allowed Malicious Email or Phishing Link Clicked. Prior to automating, be sure to review the key considerations outlined in .
Detection: Allowed Malicious Email
Action | Description | Configuration Options to Further Minimize Risk |
Quarantine or delete email | Automatically delete or move phishing emails to a quarantine folder to prevent users from accessing malicious content. | Configure the automatic response action to soft-delete or quarantine the email instead of executing a permanent deletion. |
Block sender | Automatically block the email sender to prevent receiving emails from the address again. | Create an email sender and email domain allowlist that prevents the response action from automatically blocking legitimate senders like customers, partners, internal addresses, third-party vendors, etc. |
Detection: Phishing Link Clicked
Action | Description | Configuration Options to Further Minimize Risk |
Temporary account lock | Automate the temporary lock of user accounts associated with the phishing incident to prevent unauthorized access. | Create a user account allowlist that prevents the automatic response action from locking of high-ranking positions like the CEO, president, and other executives. |
Block URL and domain | Automatically block the phishing URL and/or domain that was clicked to prevent others from accessing the site and risking network compromise. | Create a URL and/or domain “safelist” that prevents the automatic response action from blocking of legitimate sites and domains associated with the business payroll portals, vendor and supplier sites, partners, industry specific sites, etc. |
Reset user password and notify user | Automatically execute a password reset to the impacted user after they’ve clicked a phishing link to prevent potential credential compromise. | Clearly and frequently communicate the password reset policy to users and notify them automatically after a reset. The notification should include an email template that outlines clear instructions on their next steps. |
Isolate affected system | Automatically isolate the affected device or user account from the network to prevent further communication with malicious actors or the spread of malware. | Only isolate user devices rather than servers. Create a list of devices that can only be isolated during non-business hours. These devices could be business critical devices that only operate during business hours, like executive machines, POS systems, etc. |
Investigation: Gain Insight for Informed Decisions
After the phishing threat has been contained, the investigation phase delves deep into the incident to understand its scope and impact, providing the context analysts need to make informed decisions. Automation expedites analysis, uncovering critical information for timely action.
The chart below shows some common questions posed by human analysts during investigations of Allowed Malicious Email and Phishing Link Clicked alerts, which are prime candidates for automated investigations. These automatic queries should be initiated by the platform after a detection has triggered.
Prior to automating, ensure there’s a clear grasp of the organization’s technologies and the data locations required for investigating a phishing attack. Additionally, review the key considerations outlined in .
Detection: Allowed Malicious Email
Query to Automate | Insight | Typical Data Source |
What are the malicious IOCs associated with email (e.g., links, attachments, sender, etc.)? | Understanding what email characteristics made it malicious helps to pinpoint the threat and shapes attack scope. Applying threat intel helps determine attack severity. | Email threat protection, email gateway, threat intelligence |
Did the recipient interact with the email (e.g., open, click links, download attachments)? | Knowing user actions indicates the level of risk and potential compromise. | Email threat protection, email gateway, user activity monitoring, endpoint detection and response (EDR), network perimeter (firewall, proxy, etc.) |
Who else received the email? | Helps to assess the scope of the threat and determine appropriate response. | Email, email threat protection, email gateway |
Has the malicious email been reported by other users? | Identify whether it’s a widespread threat or a targeted attack. | Abuse mailbox, ticketing system |
Has the email sender emailed anyone else in the organization before? | Identifying patterns can indicate whether this is part of a larger campaign, an internal email that was compromised, or a one-off. | Email ticketing system |
Detection: Phishing Link Clicked
Query to Automate | Insight | Typical Data Source |
What is the content of the phishing link or website? | Analyzing the malicious URL or website aids in identifying the specific threat (i.e., is this a credential harvesting site or a drive-by download link?) | Threat intel, URL sandbox, web analysis, web proxy |
Did the user provide any credentials to sensitive information on the phishing page? | Assessing whether the user divulged sensitive data helps determine potential data breaches. | Endpoint detection and response (EDR), web proxy (form submissions) |
How did the user access the phishing link (email, social media, etc.)? | Understanding the delivery method can provide insight into the threat source to help with root cause analysis. | Email, email threat protection, social platform, EDR |
Have other users in the organization received the same phishing link? | Identifies whether this is a targeted attack or a part of a larger campaign. | Email security, web proxy, EDR |
Remediation: Recovery and Prevention
Focused on recovery and prevention, the remediation phase removes phishing threats and restores systems. Automation accelerates this process, ensuring swift response and consistent recovery in the event of a phishing attack.
The chart below outlines the types of actions that can be automated within the remediation phase for the Allowed Malicious Email and Phishing Link Clicked detections, along with configuration options to further minimize the risk. These automated actions can be platform-initiated or human-initiated after the investigation confirms the threat. Prior to automating, review the key considerations outlined .
Detection: Allowed Malicious Email
Action | Description | Configuration Options to Further Minimize Risk |
Reset user password and notify user | Execute a password reset to the impacted user after they’ve clicked a phishing link to prevent potential credential compromise. | Clearly and frequently communicate the password reset policy to users and notify them automatically after a reset. The notification should include an email template that outlines clear instructions on their next steps. |
Temporary account lock | Temporarily lock all user accounts associated with the phishing incident to prevent unauthorized access. | Create a user account allowlist that prevents the automatic response action from locking of high-ranking positions like the CEO, president, and other executives. |
Block IOC | Based on the investigation results, block the IOC that made the email malicious (e.g., link, attachment, sender, etc.) | Ensure all stakeholders are notified prior to blocking. |
Detection: Phishing Link Clicked
Action | Description | Configuration Options to Further Minimize Risk |
Initiate host scan | Initiate a scan on the hosts that received the phishing link to determine if there were malicious files downloaded or suspicious activity. | Notify impacted parties in case of performance issues. |
Isolate all affected systems | Isolate the devices and servers that received the phishing link from the network to prevent further communication with malicious sites or the spread of malware. | Only isolate devices and servers that were confirmed to receive the link. Ensure that the link is at a risk level aligned to the organization’s risk tolerance. Provide notices to impacted users. |
Delete file | Delete the downloaded file(s) associated with the phishing link to prevent malware spread and host compromise. | Notify the impacted parties in case of performance issues. |
Ban file hash | Ban the hash of the malicious file(s) associated with the phishing link to prevent others from interacting with the malware. | Ensure the file hash matches the malicious file. |
Human-Initiated Detections: Comprehensive Monitoring
While automating the phishing playbook based on platform-driven detections is essential, it’s equally crucial to consider additional detection avenues to create a comprehensive and robust defense against phishing attacks. In some cases, phishing emails manage to bypass email threat protection layers and reach a user’s inbox undetected. In such scenarios, the responsibility falls on users to identify and report these suspicious emails for further analysis. While the initial detection is driven by human observation, there are methods to automate the subsequent email analysis and execute containment actions based on the analysis results.
Automating the Abuse Mailbox
The GreyMatter Phishing Analyzer, purpose-built for reliability and efficiency, automatically conducts a thorough analysis of reported emails through a process known as email deconstruction. This entails disassembling the various components of an email, scrutinizing each element, and determining its threat level.
Once it has reached a verdict, the Phishing Analyzer executes corresponding actions autonomously. These actions may include deleting the malicious email, executing investigative queries, documenting the analysis findings, and providing a response to the reporting user. This automation not only accelerates the mean time to respond (MTTR), but also alleviates the administrative burden associated with managing abuse mailboxes, allowing security operations teams to focus on higher-priority tasks.
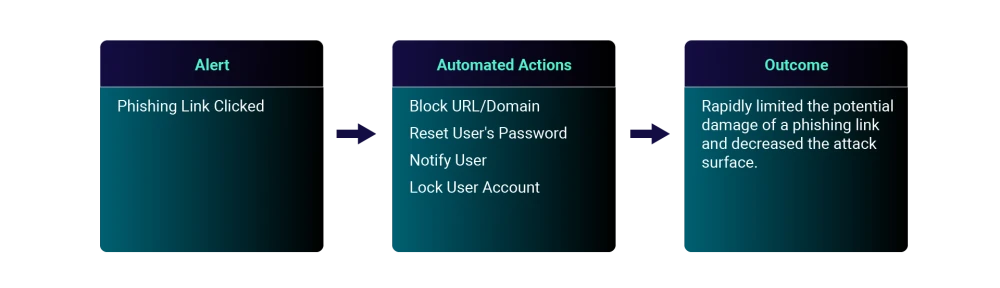
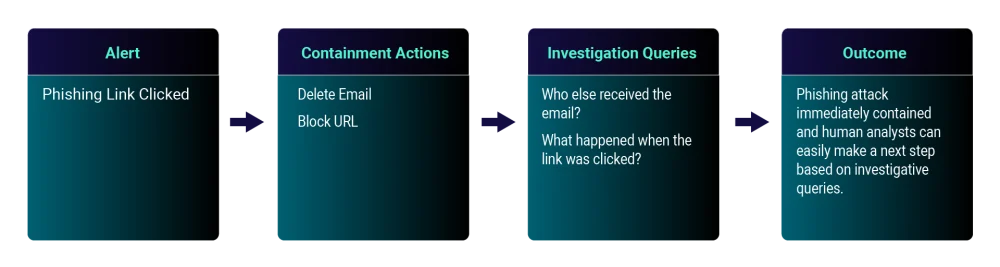
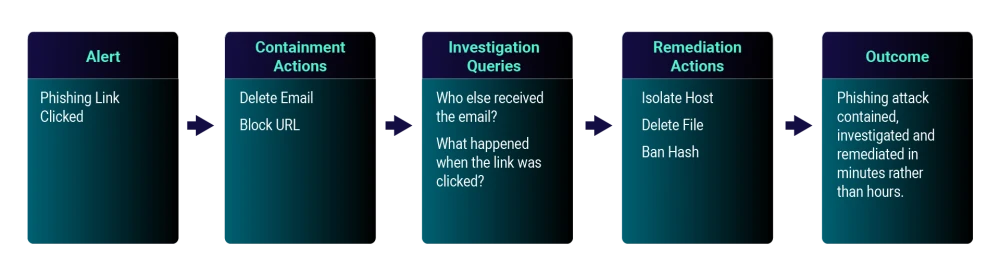
Automation In Action
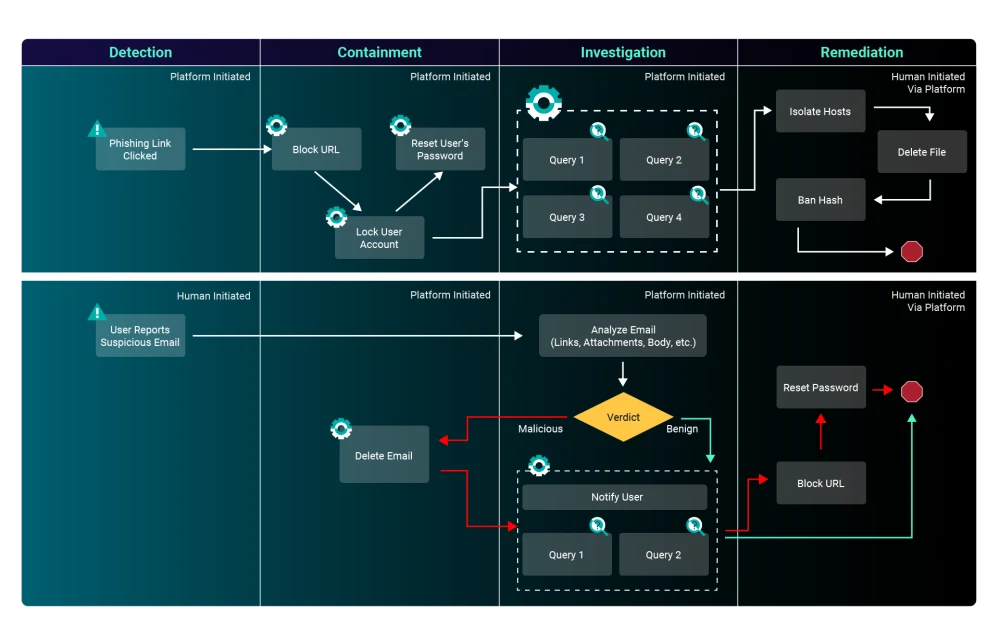
To see this in action, we’ve outlined two practical use cases, depicted in the workflow diagram below, that illustrate the power of automation in addressing real-world cybersecurity challenges.
Use-case one: A user clicks on a link to a credential harvesting website. As shown in the top half of the diagram, the “Phishing Link Click” detection will trigger, and the automation will begin.
Use-case two: A user reports a suspicious email. As shown in the bottom half of the diagram, the “User Reports Suspicious Email” detection will trigger, and the automation will begin.
These scenarios are common in today’s threat landscape, and automating the containment, investigation, and remediation phases for them is a game-changer. This showcases how automation can swiftly and effectively respond to security incidents.
Conclusion
Incorporating automation into your phishing response playbook isn’t just an option; it’s an imperative in modern cybersecurity. Automation brings a powerful blend of speed, consistency, resource optimization, and scalability to your defense strategy. When confronting phishing threats, every second matters. GreyMatter’s automation capabilities can trim response times from hours to mere minutes, all while reducing the risk of human error.