Updated December 20, 2023
As of today, the FBI and ALPHV are engaged in a tug-of-war over the ransomware group’s data-leak site. “SEIZED” and “UNSEIZED” have flickered across the homepage several times over the last 24 hours, causing confusion among cybercriminals and threat researchers alike.
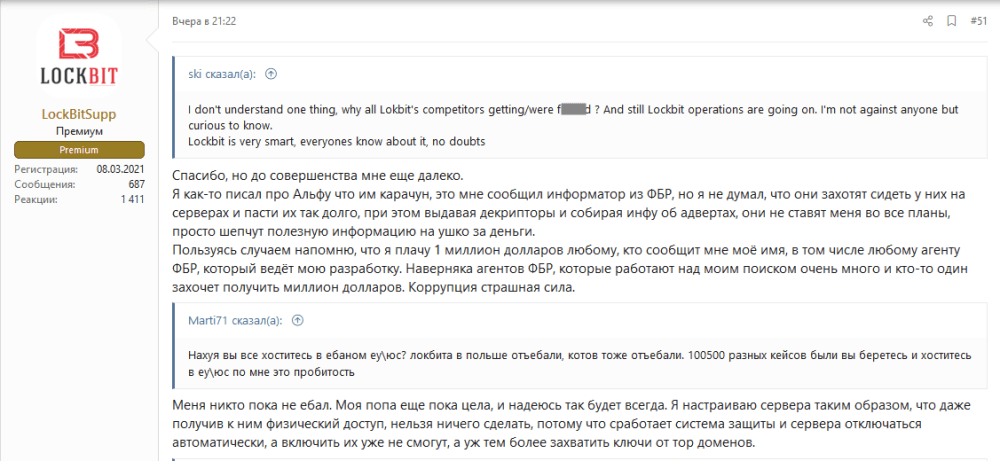
Other ransomware groups seem to be feeling the pressure as well. A LockBit representative has offered $1 million to any FBI agent who might be working on exposing LockBit: “Let me take this opportunity to remind you that I pay $1 million to anyone who tells me my name, including any FBI agent who is leading my development. Surely there are a lot of FBI agents who are working on my search and one of them will want to get a million dollars. Corruption is a terrible force.”
Nevertheless, ALPHV has remained active on its new data-leak site and even posted a new victim over the past 24 hours, suggesting that the group intends to continue its operations, even with some optimism.
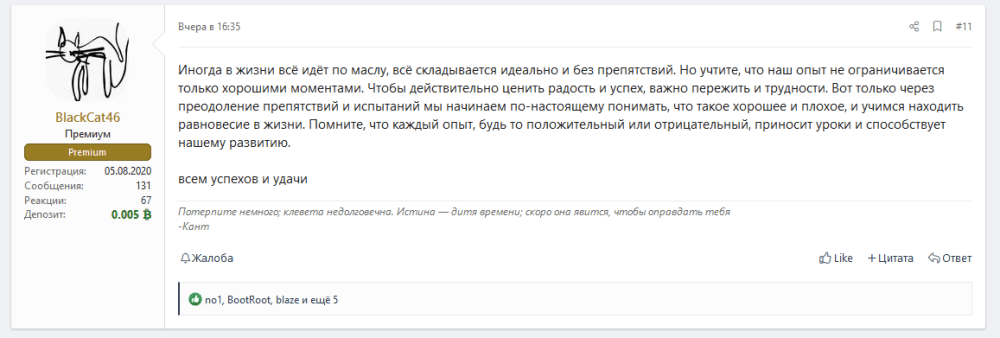
An ALPHV forum representative said “Sometimes in life, everything goes smooth like butter, everything turns ideally and without obstacles. But keep in mind, that our experience is not limited to just the good times. To truly appreciate joy and success, it is important to [experience] the hard times. It is only through overcoming obstacles and trials that we truly begin to understand what is good and bad and learn to find balance in life. Remember, that every experience, whether positive or negative, brings lessons and contributes to our development. Success and good luck to everyone.”
Fortunately for the rest of us, while the FBI and ALPHV continue to battle it out, ALPHV is too occupied to continue targeting new organizations or supply chains.
We are still monitoring the ongoing situation and will provide relevant updates here.
December 19, 2023, 3 p.m. ET
ALPHV allegedly reclaimed its website after the FBI takedown earlier today. Plastered across the front page of the data-leak site is an update stating, in all caps, “THIS WEBSITE HAS BEEN UNSEIZED.”
ALPHV has been known to post commentary around takedown rumors before, and they’ve done so this time, going into detail about how the FBI gained access and how ALPHV is going to prevent future takedowns.
Further down in the note, ALPHV states that they are doubling down on their threats in response to the takedown. According to the note, they’re “removing ALL rules,” newly allowing encryption of “hospitals, nuclear power plants, whenever and whatever you want.”
There is also speculation among cybercriminals that the entire post could be part of the FBI operation—agents posing as members of the group as a lure for ALPHV affiliates. The entire saga has sown doubt and mistrust within the cybercrime community.
As of 4 p.m. EST, the data-leak site is once again showing the FBI seize page, although the new leak site created by ALPHV remains active.
This is a fast-moving situation with a lot of back-and-forth. We’re watching everything closely and will make an update tomorrow morning Eastern Time.
December 19, 2023
The Justice Department has today confirmed law enforcement has disrupted the operations of the notorious ALPHV/Blackcat ransomware group. This explains the recent extended outage on the group’s infrastructure, with only sporadic activity of victims being named. The law enforcement action announced today serves as a body-blow to the ransomware ecosystem but it is by no means a knockout punch.
In the aftermath of such large-scale law enforcement disruptions, uncertainty permeates criminal organizations. In previous similar cases, the targeting of a ransomware group has typically resulted in operations ceasing, before members moved to other ransomware programs, or formed new groups. It is likely that this will spell the end of ALPHV as a criminal outfit. However, as noteworthy as this disruption is, there is no mention of any corresponding arrests.
It is significant however, that the FBI has helped as many as 500 victims with a decryption tool. Decryption tools allow victims to potentially avoid paying significant ransom amounts and enables them to restore systems to normal activity. The ability for the FBI to do this undermines the credibility/capability of cybercriminal organizations and bolsters the FBI’s plea for victims to report potential compromises as soon as possible. The Department of Justice continues their “hack the hacker” campaign to demonstrate the law enforcement community has offensive tools at their disposal and will not rely on a solely defensive posture.
The biggest impact of a potential permanent removal of ALPHV is likely to be a significant short-term disruption to ransomware globally. ALPHV is one of the more prominent ransomware groups in operation, tracked by ReliaQuest as the third most active in Q3 2023. The removal of ALPHV from the ransomware landscape will undoubtedly leave a temporary void before members flock to other groups. This is unfortunately a common outcome following law enforcement operation, reflecting the ongoing game of Whac-A-Mole in law enforcement attempting to provide a meaningful impact against this pernicious form of cybercrime.
December 18, 2023
It looks like ALPHV isn’t out of the game yet. We’ve seen continued activity on the ransomware group’s data-leak site, including four more named entities. Two of these organizations were named on the data-leak site before the outage, one was previously leaked by REvil, and one is new.
ALPHV has yet to comment on the cause of the outage.
December 13, 2023
A small update that could have big implications: The ALPHV ransomware group has published details on a newly compromised entity to its data-leak site. At this time, this new post is the only item hosted on the site since none of the previously hosted data has been repopulated.
Regarding law enforcement rumors, ALPHV has not made a statement, but we’ve seen them react to negative rumors, so it’s realistically possible that they will release an update from them soon. It may also be that they are trying to maintain the appearance of normalcy, even if they were affected by some law enforcement action.
December 12, 2023
As of December 11, 2023, the ALPHV data-leak site is back up—but not quite running. The page is live, and it has some functionality, but as of now, it is not showing any posts or listing any compromised companies.
It’s unclear what this might mean. This doesn’t necessarily indicate whether or not there was law enforcement activity, as has been speculated—it could be that there was law enforcement activity during which some servers were seized, but the group is still attempting to recover. Or, of course, it could indicate that the outage was a result of the group’s ongoing connectivity issues after all.
We’re still monitoring the situation and will provide updates here if we see content populated or another outage.
What We Know So Far
On December 07, 2023, the data-leak website for the notorious ransomware group “ALPHV” (aka “BlackCat”) went offline and has remained offline for more than 30 hours. Since its creation in November 2021, ALPHV has listed over 650 companies on its data-leak site, establishing it as one of the most prominent and successful data-leak sites active today. While ALPHV’s site has a history of connectivity issues, with periodic outages, this 30-hour downtime marks one of the longest disruptions the group has faced.
What We Don’t Know
At the time of writing, the cause of this outage remains uncertain—whether it is a result of a technical hosting issue by ALPHV operators or something else. However, speculations have emerged, indicating that the downtime may have been a consequence of a law enforcement operation aimed at ALPHV. At the time of writing, no law enforcement agencies have made any statements, and no seizure notice is present on any of ALPHV’s websites. It is also unknown whether this outage is currently affecting other ALPHV operations, such as ongoing attacks and servers used for hosting data leaks.
Potential Impact
Disruption to Ongoing Attacks
ALPHV is a prolific ransomware-as-a-service (RaaS) group whose ransomware is deployed by many affiliate threat actors. The group has become known for its unique extortion methods, such as creating impersonating domains of victims to leak data, and more recently, reporting a victim to the SEC following an attack. If the group’s public infrastructure were to be seized by law enforcement, this disruption would likely result in disruption for many threat actors, such as the group “Scattered Spider“, which has been known to deploy ALPHV ransomware in some of its attacks
Formation of New Affiliate Programs
This disruption would force affiliates to move on to other ransomware affiliate programs or develop their own. Previously, these types of law enforcement actions have resulted in affiliates spreading into new affiliate programs, bringing in experience from previous programs. For example, ALPHV themselves are believed to have been formed from previous affiliates of the ransomware groups “DarkSide” and “BlackMatter”.
Possible Asset Recovery
If the disruption was indeed caused by law enforcement, decryption keys and associated cryptocurrency wallets might have been extracted. For instance, in June 2021, the Department of Justice recovered $2.3 million from the DarkSide ransomware group, and in September 2021, the FBI breached REvil’s servers, obtaining decryption keys for Kaseya victims. Moreover, even if a campaign doesn’t fully dismantle a ransomware group, agency pressures often lead to shutdowns, due to fears of additional law enforcement campaigns and arrests.
What’s Next?
ReliaQuest will continue to monitor the story as it unfolds and provide updates to this blog. In the meantime, you can learn more about ALPHV and other high-profile ransomware groups by reading our latest Ransomware & Data-Leak Extortion report for Q3 2023, which includes a comprehensive overview of the most common TTPs used by ransomware groups, as well as mitigation techniques. We have also recently published a blog breaking down an attack by the Scattered Spider threat group, who is known for using ALPHV ransomware. For further ransomware-related stories and weekly threat news, you can listen to our threat-research podcast, ShadowTalk, where we discuss the latest ransomware trends and news.




