Editor’s note: This blog is part of our ongoing Email Threats series. Click here to read part one on HTML smuggling.
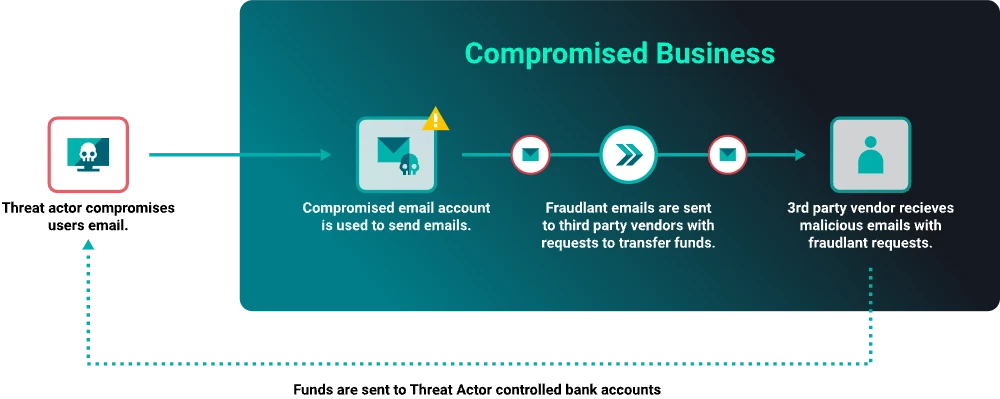
Remember working life before email? It seems nearly impossible now. Email messages between staff and outside contacts have become critical to business operations, and cyber-threat actors are only too aware of that dependence. By interfering with email, that critical medium of communication, they’re able to perform one of the most common methods of exploiting an organization: business email compromise (BEC). It’s not new, but it’s a significant threat.
How Does BEC Work?
In its simplest form, a BEC operator sends phishing emails that lure a business’s employees into paying fraudulent bills. These emails appear to be sent from a known business affiliate, vendor, or colleague, so the recipient tends to trust the sender. Most businesses experience BEC throughout any given year, and the malicious messages are often reported by vigilant users and escalated to a company’s security team, who run playbooks to eliminate any risk to the environment.
Business email compromise attacks are different from other types of cyber attacks because they seek to manipulate a human rather than exploiting a technical vulnerability.
These tactics exploit human emotions like curiosity, fear, and trust to persuade employees to take actions that they wouldn’t normally take. Since humans are often the weakest link in an organization’s security defenses, attackers will try to bypass technical controls by targeting individuals with access to valuable resources.
Types of BEC Attacks
Email Spoofing
Attackers can use various methods to pose as someone trustworthy in the instance of a business email compromise attack. One common method is email spoofing, where an attacker creates a fake email address that appears similar to the legitimate one. For example, they might create an email address like instead of .
Social Engineering
Another method is social engineering. Attackers may conduct research on their target organization and create a pretext that seems believable. For example, they might gather information about a particular vendor’s billing cycle and then send a fake invoice that seems legitimate.
Phishing Attacks
Attackers also use phishing techniques to trick employees into thinking they are someone trustworthy. They may send an email that appears to be from someone within the company, such as a colleague or a supervisor, and ask the employee to perform an urgent task like initiating a wire transfer. The phishing email will usually contain a link that takes the victim to a fake login page, which the attacker uses to steal their username and password.
Let’s take a look at some of the insights the ReliaQuest threat research team gathered over 2023 in our analysis of clients’ BEC-related events. They feed into key steps you can take over the next two months to shore up your defenses.
Business Email Compromise Examples in 2023: Looking Out for Lures
Example 1
In one BEC case, the finance team at a third-party company (Company A) reached out to one of our clients (Company B) to inform their security team that Company A had been receiving fraudulent emails purportedly coming from Company B.. ReliaQuest analyzed the email chain, which showed social engineering tactics. The sender instructed the victim (Company A) to switch from processing payments by check and begin going through the Automated Clearing House Network, a network used for electronically moving money between bank accounts.
In a follow-up email to Company A, the threat actor asked for a response about the payments, stirring up a sense of urgency. But Company A, thankfully, didn’t fall for the lure. Despite the emails not containing links, attachments, or artifacts in the headers that typically trigger prevention or detection measures, the recipient notified our client’s security team at Company B and remediation followed.
Example 2
In another recent BEC event, ReliaQuest investigated a threat actor who successfully compromised an email account through a credential harvester. After establishing initial access to the account, the threat actor quickly created new email rules to move their own sent messages to the junk folder. This hid the fraudulent activity from the account owner, but it did trigger alerts that enabled mitigation before any emails could be sent or reputation damage done.
ReliaQuest responds to a high daily volume of BEC-related attacks. The malicious emails are usually sent to the staff of finance departments or high-ranking employees. The phishing emails often make it to the victim’s inboxes successfully because the messages lack sophistication and rely on social engineering to trick unsuspecting victims into performing fraudulent actions.
BEC Protection: Step by Step
BEC attacks present challenges for young and mature cybersecurity programs alike. Identifying instances is tough: There are few detection opportunities, and defense often relies on the vigilance and savvy of the target. Below, we offer a plan to defend against this threat by developing strategies that will better secure your network over two months.
What Can You Do Now?
Enable employees in high-risk departments to identify potential phishing emails. Run security awareness programs and highlight examples or case studies. Inform staff that they may be targeted by BEC emails and that attackers could use their email account credentials to send malicious messages to other businesses.
Ensure that multifactor authentication (MFA) is enforced for all employees.
What Can You Do Within 30 Days?
Create a playbook to alert third-party providers and partners if you receive BEC phishing emails. Think about the example we explored earlier; ensure that a speedy notification can trigger responses that limit the scope of the compromise.
Consider implementing a dual authorization policy in which a manager or co-worker must authorize large payments or banking changes.
What Can You Do Within 60 Days?
Develop detections on high-risk users when inbox rules are created. This will probably result in a lot of false positives, but a tuning period of at least 30 days should increase the fidelity of the rule.
Establish a policy for large money transfers or updates to client banking account information, requiring verification through an additional means other than email (e.g., phone call or other verbal communication).
Is your team drowning in reported phishing emails? The Phishing Analyzer, part of the ReliaQuest GreyMatter security operations platform, can automate the evaluation, remediation, and notification process, leaving your analysts free to focus on higher-priority tasks.





