Welcome to the third blog in a series designed to accompany the launch of ReliaQuest’s new, globally available GreyMatter Phishing Analyzer (GMPA)—which facilitates automated, efficient analysis of potential malicious emails. To support the launch, and provide that all-important context and threat intelligence about phishing and its impact on defenders, the ReliaQuest Photon Research team recently published a piece looking at phishing campaigns orchestrated by the initial access broker “Exotic Lily.” Prior to that, we released an overview of a popular technique called HTML smuggling, which threat actors use to deploy remote-access trojans (RATs), banking malware, and other malicious payloads. Although HTML smuggling is not new, adversaries are still using the methodology because of its continued effectiveness and because the topic appears frequently on cybercriminal forums that threat actors use to learn about new attack methods. In this blog, we’ll look at examples of cybercriminal forum chatter about HTML smuggling and the ways in which users seek to push the boundaries even further and develop alternatives to the technique.
The Popularity of HTML Smuggling
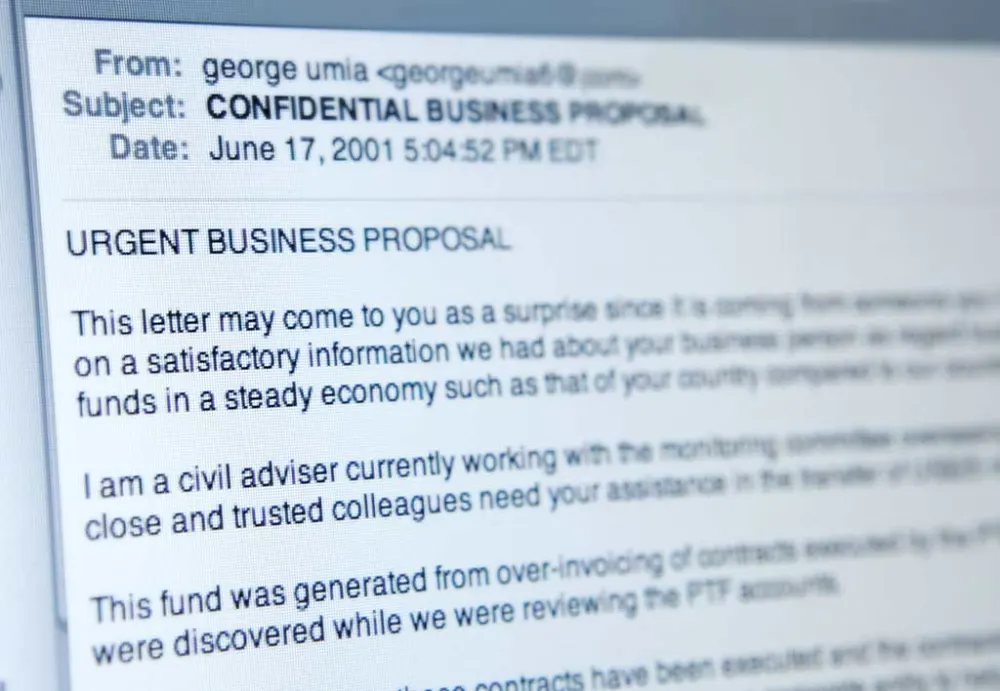
One of the reasons for the continued popularity of cybercriminal forums—despite their outdated technology and obvious operational security risks—is that they provide a way for threat actors to ask for help and to crowd-source solutions to their problems. Forum sections dedicated to phishing and spamming are often some of the most popular on these platforms, with users advertising phishing and spamming services, providing tutorials, sharing email databases, or seeking guidance on ensuring emails land in inboxes and not junk folders. We’ve repeatedly observed cybercriminals discussing the advantages of using HTML smuggling to conduct phishing campaigns, with users describing the technique and sharing technical articles about different variations of the methodology.
For example, a post on a prominent Russian-language cybercriminal forum, from January 2023, recommended using “a combination” of redirects, encoding, and HTML smuggling to “protect” a “scampage” from a “red flag;” i.e., so that the phishing email ends up where it should. (See Figure 1 below.)

On another forum, in September 2022, a user sought methods to “spread” a malicious link “over email.” A respondent suggested using HTML smuggling combined with the XOR Cipher encryption method. Other users immediately expressed interest, requesting tutorials for the technique, sharing related articles and guides, and exploring variations to the methodology. (See Figure 2 below.)

“QakBot” spam campaigns leveraging malicious OneNote files have been in the news a lot lately. These types of attacks use Microsoft’s OneNote to deliver malware that grants initial access to a victim system. Our research across the cybercriminal underground revealed users on multiple dark-web forums sharing information and articles about QakBot’s operators using HTML smuggling techniques to deliver malware using SVG images embedded in HTML email attachments towards the end of last year (see Figure 3). Media articles like this tend to generate discussion and further TTP development on cybercriminal platforms; forum users may be inspired by the QakBot operators’ example to find further uses for HTML smuggling techniques.

Developing Alternatives to HTML Smuggling
HTML smuggling appears to be such an established methodology among the cybercriminal community that threat actors have even started to take the next step, building on this technique and searching for alternatives in case defenders have wised up. We noted an advertisement on a top-level cybercriminal forum in November 2022 that promoted an alternative to HTML smuggling for attackers “who send only links.” The vendor explained that their service consists of a “PDF landing page” that “combines both the layout and a link to your payload, which is automatically delivered when clicked on in any browser.” They offered landing pages relating to multiple well-known services, including DropBox, Office365, Microsoft Office, and Adobe Acrobat—even providing an example of the latter (see Figure 4.)
The vendor emphasized the service’s ease of use: All adversaries need do is select a clickbait title, upload malicious attachments, select a landing page, and provide the payloads. The phishing emails only contain an image and a link that allegedly ensures all mail providers will accept the email. All the text on landing pages would reportedly be translated into the target language by a native speaker, increasing the appearance of legitimacy. The vendor priced the offering at $800 for a weekly subscription to the service and also offered to design bespoke infrastructure to suit clients’ needs. Responses from other forum members were generally positive: Users left good feedback about working with the vendor and expressed enthusiasm about the technique. One threat actor highlighted that this technique was also gaining traction on Twitter. Not all such offerings are so well-received on cybercriminal platforms…

A Reliable Technique
As recently as February 2023, a user of the English-language cybercriminal forum BreachForums—the forum that emerged after the seizure of the popular English-language cybercriminal forum RaidForums—initiated a thread seeking advice about an “infection stage 1 tool” they were developing. The tool was intended to pack malicious scripts into Hypertext Markup Language Applications (HTAs), as well as optical disc image (ISO) files. The threat actor developing the tool also noted that there is an option to implement HTML smuggling into the tool. As discussed earlier, the fact that threat actors are still considering implementing and using HTML smuggling indicates that the technique still trends and is still considered a reliable method for executing phishing and spamming attacks.
Minimizing Risk
The key takeaway is that older techniques such as HTML smuggling are still relevant and popular among cybercriminals. There are clear indications that threat actors continue to utilize and improve HTML smuggling, which is why it’s important to update detections and review previous detections. The ReliaQuest Photon Research team continues to monitor HTML smuggling, providing intelligence to stay up-to-date with current developments and to further reduce HTML smuggling risks. In our previous blog about the subject, we provided crucial steps you can take to minimize risks related to HTML smuggling.
GreyMatter Phishing Analyzer
The GreyMatter Phishing Analyzer eliminates the struggles of monitoring abuse mailboxes, and allows you to identify and remove email threats before it’s too late.
Watch Phishing Analyzer in Action
To learn more about the email phishing landscape (presented by our Photon Research Team) and see GreyMatter Phishing Analyzer in action, register for our webinar on March 22, 2023.