Take one look at the headlines, and it becomes evident that the current threat landscape demands swift and decisive action across security operations. With adversaries constantly evolving and accelerating their attacks, the dynamic nature of today’s threat landscape presents a critical challenge for both CISOs and their organizations. Agility, achieved through the judicious use of automation, can help to minimize risks and free up time for more impactful work.
In this blog, we will discuss how to navigate the ever-changing threat landscape by leveraging automation and how security leaders can determine the best use cases for automation within their organization.
Evolving Threat Landscape
“When seconds count, the Change Control Board’s approval is weeks away.”
ReliaQuest has seen threat actors accomplish their objectives in a matter of days, and sometimes even hours. As a result, CISOs must reassess their automation strategy. The fear of potentially blocking a user or device must be reevaluated, considering the speed of attacks. Actions that require configurations or rule changes may need approval, but when seconds count, the Change Control Board’s approval is weeks away.
The status quo of relying on existing manual processes and traditional change control procedures is no longer sufficient to combat the evolving threat landscape. Defenders must adopt an agile strategy to keep up. Acting with a sense of urgency and leaning forward on automation can streamline security operations to effectively combat the speed of adversaries and minimize potential damage from threats.
Automation enables accelerated capabilities across prevention, detection, investigation, and response. It provides opportunities to gather incident context, isolate infected systems, block relevant IPs/domains, and reset credentials. Using automation expedites response times, reduces the risk of human error, and enables organizations to stay ahead of adversaries, protecting critical assets from threats.
Key Considerations When Applying Automation
While implementing automation has many benefits to an organization’s security operations, it’s crucial to approach the implementation with careful consideration. Leaning forward on automation is not simply a matter of turning on response playbooks and expecting immediate success. Using a measured approach helps prevent unintended disruptions and ensures a smooth adoption. It requires evaluating potential risks and trade-offs, assessing whether the degree of automation aligns with the organization’s risk tolerance level. Automation is not something to run headlong into.
Each organization has its own unique risk tolerance, which is based on factors such as its industry, regulatory requirements, and overall risk management strategy. Strategic planning and careful evaluation of risk tolerance are crucial in determining the appropriate amount of human involvement and decision-making in automated actions. CISOs should collaborate with their leadership and IT peers throughout this automation journey, communicating the goals, benefits, risks, and automation methodology. This is not an initiative that should be done in isolation, as mistakes in automation have the potential to be a “career limiting move” for CISOs.
“We have enough problems with denial of service from adversaries. We don’t need to do a denial service on ourselves.”
When evaluating a playbook, it’s important to consider whether it should require human involvement or can be fully automated. For example, when handling high-fidelity alerts, organizations may choose to automate the response process without human intervention, whereas in other scenarios, human execution of a playbook may be preferable. It’s essential to avoid misapplying automation and inadvertently causing self-inflicted denial-of-service (DOS) situations.
It’s also worth noting that the automation strategy can be dialed up or dialed down depending on the business environment and threat landscape. For example, in a situation where ransomware actors are actively targeting a specific sector, there may be an increased appetite to automate prevention and isolation use cases.
Identifying Use Cases to Accelerate Automation
In the ongoing process of improving security operations, it’s crucial to identify optimal use cases for automation. By pinpointing these use cases, CISOs can effectively implement automation to address key areas, thereby improving response efforts and enhancing an overall security posture.
Analyze Top Alerts and Incidents
To begin identifying some specific use cases for automation, a valuable starting point is to conduct an analysis of the top alerts encountered within the past year. By examining these top alerts, organizations can identify areas that would benefit from implementing automated processes to optimize their security operations. One important question to consider during this analysis is: Where is the team spending the most of their time?
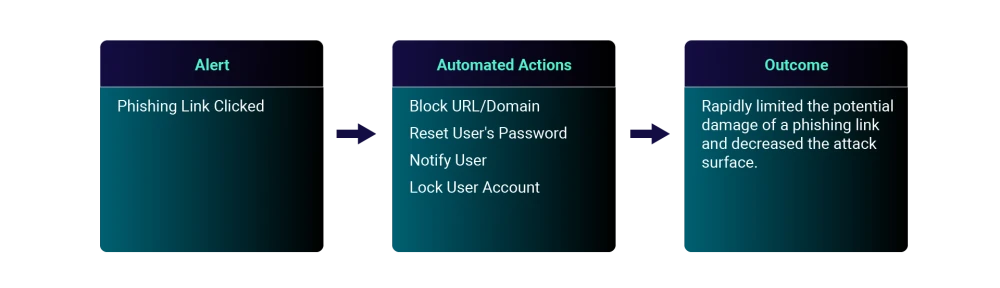
For example, organizations should evaluate their top true-positive alerts. Let’s assume that a “phishing email clicked” is a frequent true-positive, which can be deemed as a high-fidelity alert. In this case, the organization can implement a phishing response play, as shown below.
In addition to phishing, we’ve observed other common top true-positive alerts in customer environments, such as compromised credentials and malware incidents. The responses to these alerts are highly actionable, making them prime use cases for automation. By implementing automation to respond to these alerts, organizations can be more agile in responding to threats.
Maximize Existing Technology Investments
There is not a CISO or security leader that I speak with today that is not interested in maximizing their security investments and rationalizing their security stack. While at Forrester Research, I wrote about the term “expense in depth,” which I described as the multilayered approach to ensuring minimal return on investment. Understanding the technology stack is crucial for organizations to align their automation efforts with existing infrastructure, optimizing processes and improving efficiency. This approach is designed to achieve long-term scalability and compatibility. It allows for smooth integration and minimizes any potential challenges or disruptions that may arise. Organizations can make informed decisions by identifying redundancies across their toolsets and selecting automation solutions that seamlessly fit within existing tech stacks, thereby maximizing their return on investment (ROI).
To uncover opportunities for automation, it is essential to conduct a comprehensive analysis that considers various components, including integrations, APIs, and the complexity of the technology stack. Start by identifying specific pain points or challenges to provide a basis for identifying potential use cases for automation. During this identification stage, it’s helpful to ask questions such as: What integration options exist? What can you start to stack together to build a playbook?
Organizations must also understand the different components involved in a specific use case, such as email security, network security, cloud security, and more. This understanding helps in determining the complexity of the tech stack and the number of consoles that need to be accessed to solve a problem.
After identifying the components, assess the effectiveness and complexity of handling them manually. This assessment can involve evaluating the documentation and determining the level of expertise needed to successfully manage these components. As this process can sometimes prove to be overly complex or time-consuming, outsourcing to a security operations platform could be a viable option.
Seek Input from the Team
Interviewing the broader security team is an effective approach for organizations to uncover additional use cases for implementing automation. With their firsthand experience working in the security environment, they have a deep understanding of the organization’s needs and can provide valuable insights for improvement.
One approach is to analyze the number of steps or pivots that analysts and engineers must go through in different tools to complete a specific task. By deconstructing the steps involved in routine tasks, we can identify opportunities to streamline the workflow by consolidating these steps. This analysis also helps us understand the manual effort and time spent on each task to pinpoint specific areas where automation can be effectively applied. As a result, we can reduce overall effort required to complete these tasks and determine the value of automation in terms of savings.
Quantifying the hours spent on specific tasks also allows us to better understand the potential efficiency gains and resource allocation benefits that automation can offer. For example, the top five incidents and alerts that analysts spent time doing manually in the past year could represent a substantial amount of time savings that could be allocated elsewhere. The goal is to automate low-complexity, time-consuming tasks, freeing up analysts to focus on more strategic and valuable activities.
When assessing automation use cases with the security team, consider asking questions such as:
Will this action stop the ongoing threat from spreading?
Does a human analyst do this action every time this detection triggers?
Will this action disrupt critical business operations?
Does this action correspond with the organization’s risk tolerance?
Can this action be easily reversed or modified?
By asking these questions, organizations can evaluate whether automation is suitable for particular use cases and ensure that the automated actions align with the organization’s goals and requirements. There are added benefits to soliciting this feedback. Firstly, implementing automation can make the day-to-day lives of security teams easier, leading to improved morale. Secondly, automation frees up resources within the security team, allowing them to focus on other less mundane areas. This enables them to shift their focus towards improving their skillsets and careers. Lastly, CISOs are getting “ground truth” from the staff in the security operations trenches, which is an invaluable perspective.
Pulling It All Together
CISOs can no longer afford to apply security operations strategies from previous decades to address today’s threat landscape. The lower barriers to entry, combined with the increasing sophistication of adversaries, require a more proactive security operations strategy. Automation can prevent threats, accelerate threat detection, reduce response times, mitigate human error risks, and maintain an edge against adversaries. CISOs don’t want to conduct a post-ransomware after-action review only to discover that the integrations and playbooks necessary to prevent the attack existed but were not implemented. Such a scenario may not be well-received by leadership, who expect proactive measures to be in place to prevent such incidents.
However, the implementation of automation requires careful deliberation. Each organization has its own unique risk tolerance, which must be considered to ensure an appropriate level of human involvement and decision-making in automated actions. To identify specific use cases for automation, organizations should analyze their top alerts and incidents, maximize their technology stack integrations, and gather feedback from their security teams to provide valuable insights for effective automation deployment. By Implementing automation for use cases specific to their organizations, CISOs can navigate the dynamic threat landscape, enhance incident response capabilities, and protect critical assets from evolving threats.





