Editor’s note: This is part four of a series on applying automation to security operations.
Part one: A Practical Approach to Automating Cybersecurity Playbooks
Part two: Automating Your Phishing Playbook
Part three: Automating Your Malware Playbook
Part four (this blog): Automating Your Compromised Credential Playbook
Introduction
This marks the fourth and final installment in our blog series on taking a practical approach to secops automation. So far, we’ve covered automation playbooks in relation to phishing and malware. Today, we will be wrapping up this series with a review of compromised credentials.
Similar to our previous blogs, we’ll cover the use of automation in several scenarios to respond to the threat of compromised credentials. As a reminder, the three distinct phases we will review are containment, investigation, and remediation.
Containment:
When it comes to compromised credentials, the initial containment can take many forms. This depends heavily on the nature of the incident. For instance, in the case of credential harvesting scenarios like phishing campaigns, the goal is to protect users by automatically removing suspicious emails from their inbox. Similarly, if a domain spoofing attempt is identified, blocking access to this site is critical.
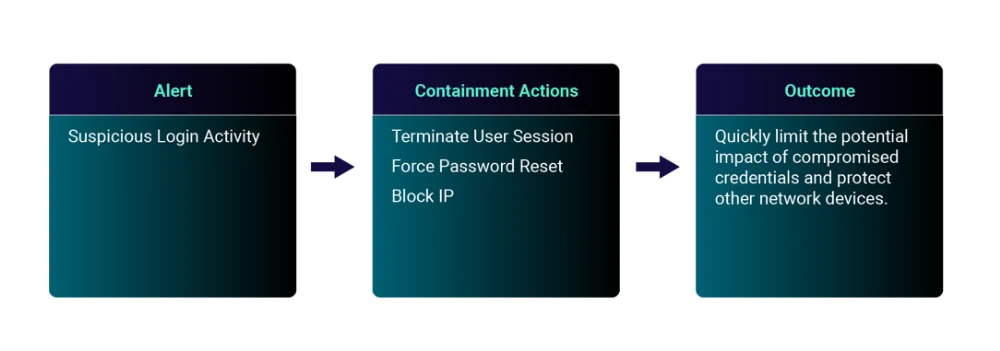
If credentials have already been compromised and suspicious login activity is detected, automation can assist in quickly containing the threat by terminating the user’s session and forcing a password reset. This could be in response to brute force password guessing, remote logins from high-risk countries, impossible travel, MFA fatigue attacks, or other similar threats. Prior to automating, be sure to review the key considerations outlined in .
Detection: Credential Harvesting Identified
Action | Description | Configuration Options to Further Minimize Risk |
Quarantine or delete email | Automatically delete or move phishing emails to a quarantine folder to prevent users from accessing malicious content. | Configure the automatic response action to soft-delete or quarantine the email instead of executing a permanent deletion |
Block domain | Automatically block the domain for both inbound emails and outbound network connections. | Create an email sender and email domain allowlist that prevents the response action from automatically blocking legitimate domains. |
Detection: Suspicious Login Activity
Action | Description | Configuration Options to Further Minimize Risk |
Terminate user session and force password reset | Automatically terminate user session(s) and execute a password reset for the affected user account(s). | Create a user account allowlist that prevents the automatic response action from locking out mission-critical service accounts. |
Block IP | Automatically block suspicious IP addresses from the network. | Define a list of critical customer/vendor infrastructure that should not be blocked automatically. |
Isolate host | Automatically isolate the affected device from the network to prevent further communication with malicious actors. | Define a list of critical infrastructure that should not be isolated automatically. |
Investigation:
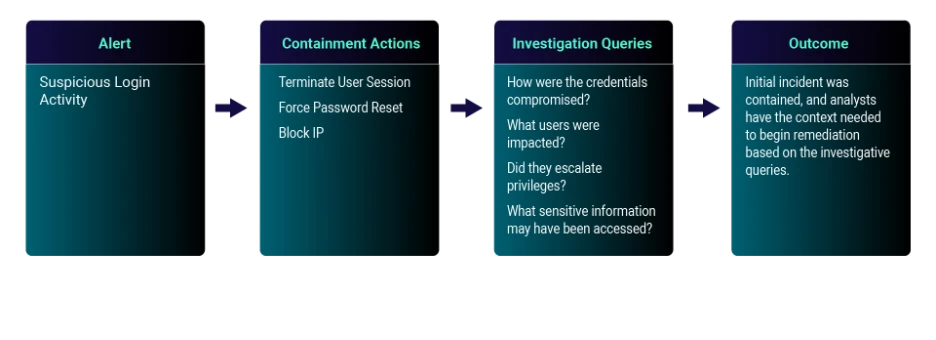
Now that the initial threat of compromised credentials has been contained, the investigative phase will help uncover the full scope of the potential incident. In this phase, automation is key in enabling analysts to be more efficient and consistent in their investigative process.
To properly apply automation within the investigative phase, you must first begin by identifying the questions that need to be addressed. While these questions may depend on the original alert, they generally follow the same format. With the right platform, this process occurs automatically at machine speed through targeted queries across the organization’s interconnected technologies.
Before initiating automation, you must first have a clear understanding of the organization’s tech stack and the various data repositories available for the investigating incidents of compromised credentials. These could include SIEM(s), EDR(s), and even several data lakes. Additionally, review the key considerations outlined in the initial blog of this series.
Query to Automate | Insight | Typical Data Source |
How were the credentials compromised? | Identifying the source of the initial compromise (phishing email, spoofed domain, malware, etc.) provides insight into the attack timeline and scope. | Network perimeter (e.g., firewall, proxy, etc.), email gateway, SIEM, EDR, digital risk protection (DRP) |
What users were impacted? | Identify if this is an isolated incident or part of a larger credential harvesting campaign. | User activity monitoring, network perimeter (e.g., firewall, proxy, etc.), SIEM |
Did they escalate privileges? | For the impacted user accounts, identify whether there was successful login activity and any signs of privilege escalation. | User activity monitoring, SIEM, EDR |
What sensitive information may have been accessed? | This information will inform response efforts and determine the need for involvement of legal counsel. | User activity monitoring, SIEM, data loss prevention (DLP) |
Remediation:
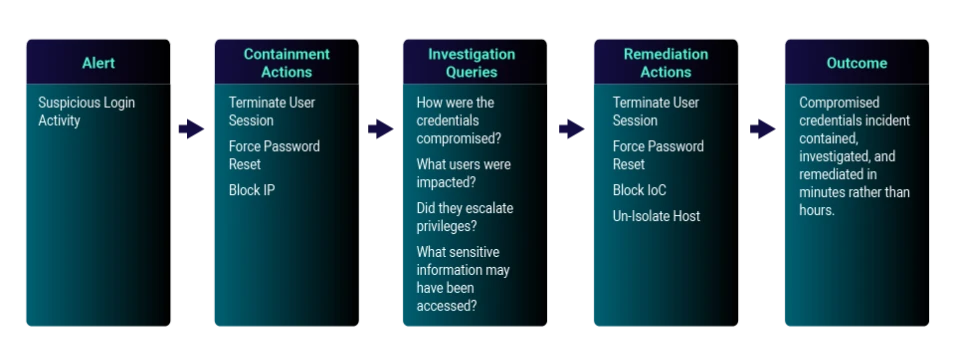
As the final phase, remediation is responsible for recovery of affected user accounts and prevention of future incidents. Based on the findings of the investigation, the analyst should now understand the scope of the incident including which credentials were impacted and any sensitive data that may have been accessed.
The chart below outlines the various automated actions that can be taken as part of the remediation phase for Credential Harvesting Identified and Suspicious Login Activity detections. These automated actions can either be platform- or human-initiated. Prior to automating, review the key considerations outlined in the initial blog of this series.
Detection: Credential Harvesting Identified
Action | Description | Configuration Options to Further Minimize Risk |
Take down domain | Deactivate malicious domains to prevent future credential harvesting. | While waiting for domain to be deactivated, use internal security controls to continue blocking domain. |
Automatically enroll users in education | Use this incident as an opportunity to educate users on the risks of phishing and domain spoofing. | Ongoing training and testing can prepare users for future spearphishing campaigns. |
Detection: Suspicious Login Activity
Action | Description | Configuration Options to Further Minimize Risk |
Terminate user session(s) and force password reset | With an updated scope based on the investigative findings, reset credentials for all affected users. | Automatically notify impacted users and provide instructions for creating a new password. |
Block IoC | Based on the investigative findings, block any associated IoCs (e.g., email sender, attachment, IP, etc.) | Ensure all stakeholders are notified prior to blocking. |
Un-isolate host | Restores full network connectivity for the affected device(s). | Ensure incident forensics and remediation steps have been completed prior to restoring network connection. |
Conclusion
By integrating automation into your compromised credential playbook, you can swiftly and consistently respond to threats. Utilizing a unified security operations platform provides the opportunity to accelerate the entire process of containment, investigation, and remediation. With GreyMatter’s automation capabilities, response times can be reduced from hours to mere minutes, all while minimizing the risk of human error.





