What is MDR?
Managed detection and response (MDR) is an outsourced cybersecurity service where a trusted third party remotely manages Security Operations Center (SOC) functions like threat monitoring, detection, investigation and incident response for the organization. This makes the third party responsible for monitoring the security ecosystem 24/7 in real time, detecting various threats, and investigating them. Additionally, they may proactively hunt for unknown threats and either respond to them or provide the necessary information so the organization’s security team can act.
What Are the Benefits of MDR
MDR services provide a strategic advantage for organizations aiming to strengthen their cybersecurity without having to manage it internally. By outsourcing it their security needs, organizations can benefit from:
A Team of Security Experts
Not all organizations have robust IT security teams who can manage their threat detection and response requirements internally. Amid the ongoing cybersecurity skills gap, many organizations have trouble hiring professionals to fill out their teams. MDR can help to address these challenges by amplifying the reach of organizations’ security teams.
Improved Security Posture
MDR can help to improve team members’ visibility of the network, reduce the number of false positives, and help them focus on true threats and meaningful projects that augment their employer’s security posture.
A Cost-Effective SOC
MDR may also be a more cost-effective option than building an in-house security operations center (SOC). Instead of setting aside the effort, budget, and time to establish an internal SOC, they can pay a monthly operating expense for the MDR platform and get immediate access to a fully built SOC.
What Are the Limitations of an MDR Provider?
Lacks Customization
Traditional MDR providers are often tech driven, using their own or white-labeled solutions to achieve those different functionalities in a turnkey fashion. In such cases, the MDR may or may not leverage the customer’s existing security tools and technologies.
Not Outcome Focused
With limited customization, security outcomes mostly depend on the MDR provider’s tools, approach to security monitoring, the processes they use, and the threat intel and data they use. If an organization wants to build on its existing security technologies or needs a partner to help them mature their security operations, a one-size-fits-all approach might not cut it.
Why Do Organizations Choose an MDR Provider?
Some of the most common challenges and reasons that lead companies to employ an MDR provider instead of building an in-house SOC include:
Overburdened security teams
Limited expertise
Low cybersecurity maturity
Inability to adapt to rapid business changes
However, the decision between opting for an MDR service or establishing in-house security operations to address these challenges is largely dependent on various factors unique to each organization, including the size, budget, and other specific needs. The table below explores these considerations further.
Factor | Considerations for MDR vs. In-House Security Operations |
|---|---|
Organization Size | Smaller firms can supplement their security programs using expertise from an MDR provider; larger firms may be able to staff their own SOC. |
Budget | MDR services provide a cost-effective solution for limited budgets, while enterprises with larger budgets might afford the up-front costs of in-house setups. |
Flexibility | Unique operational requirements might necessitate custom solutions, which can influence the choice between an MDR that may limit tool choices or a more tailored in-house approach. |
How Does MDR Work?
An MDR solution uses a combination of various technologies, best practices, and analysts to deliver its threat detection and response services. The basic technologies typically include security information and event management (SIEM) technology and endpoint detection and response (EDR) or endpoint protection platforms (EPP). These technologies form the foundation for real-time monitoring and detection of ransomware, malware, and other security attacks, enabling rapid incident response to address and eliminate the threats.
MDR Services
Some important services an MDR may provide include:
24/7 monitoring: MDR providers continuously monitor for potential threats using technologies like a SIEM or EDR to minimize the window of opportunity for attackers.
Detection: They leverage advanced technologies and analytics to identify anomalies and potential threats for quick detection of threats.
Investigation enrichment: Once potential threats are detected, MDR providers correlate data from various sources, including threat intelligence, to gain a complete understanding of the incident.
Threat hunting: MDR providers offer proactive threat hunting to search for hidden threats within the organization’s environment before they can be exploited.
Response and remediation: More advanced MDR providers can execute out-the-box response actions to minimize damage and restore normal operations as quickly as possible.
The quality of service provided by MDRs depends on the strength of their tools and technology, as well as the expertise and support of their security professionals. Only advanced MDRs offer certain services listed above, so it’s important to consider this when evaluating a provider.

What Does MDR Automation Look Like?
Advanced MDR providers may offer automation capabilities like automated response actions, commonly known as “MDR playbooks.” While these playbooks are effective for addressing certain threats, they tend to be general and may not align with an organization’s unique needs or risk tolerance. The lack of customization can also limit their ability to integrate with a diverse set of existing security technologies, preventing the development of tailored automations that address specific operational requirements. For more tailored response automations, organizations should consider solutions like a technology-agnostic security operations platform.
How Outsourced MDR Compares to Other Security Services
MDR vs. MSSP
A managed security services provider (MSSP) functions similarly to an MDR service provider in that it monitors a customer’s network security. The difference is that the former merely provides alerts when it spots anomalous activity indicative of security incidents in the latter’s managed systems. It doesn’t launch an investigation, and it does not respond to any threats that it uncovers in the process. It tags alerts—including false positives—and sends them to their customer’s IT team for review. By contrast, MDR detects, investigates, correlates, and responds to security alerts depending on the provider. In addition, an advanced MDR provider would conduct threat hunting operations as well as manage your security operations tools.
Outsourced MDR vs. In-house Security Operations
Many organizations might opt for in-house security operations where they build their own tech stack and manage the various tools. This initiative requires the right resources and skills to not only conduct incident response—from detection to response—but also administer and manage the various tools and keep them optimized against a dynamic threat landscape. In many cases, an outsourced MDR provider is a viable option since this allows the in-house security team to leverage outside expertise without having to hire them, ensure 24/7/365 monitoring, and focus on more strategic initiatives and high-value tasks. Here are some common technology options used to build out an in-house tech stack:
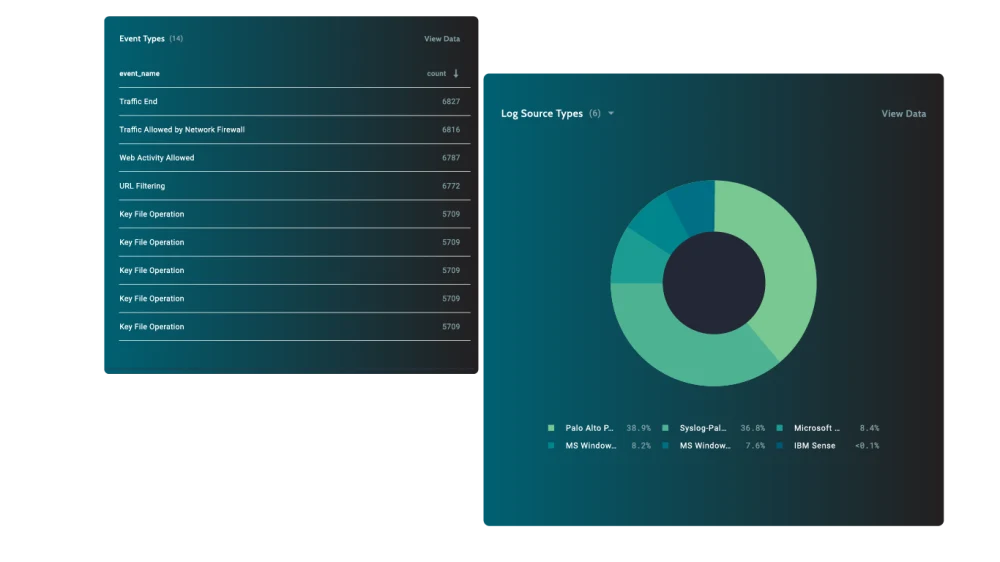
MDR vs. SIEM
In most cases, a Security Information and Event Management (SIEM) technology is the predominant technology to operationalize security operations. SIEM technologies specialize in ingesting, aggregating, and correlating data from network security devices, provide real-time monitoring and analysis of events and help with compliance by logging data. In many cases, SIEMs require analysts to write rules or scripts with specialized languages. While SIEMs have matured over the years, there could be architectural challenges with ingesting all the necessary data and requires specialized skills to manage, optimize, and operate.
MDR vs. EDR
As the threat landscape evolves, endpoint detection and response (EDR) technologies are becoming more of an imperative. They offer continuous threat monitoring and detection as well as automated response to digital threats. But EDR brings this functionality to the endpoint level only, falling short of contextual focus on threats. While they promise timely response to attacks, EDR tools are very resource-intensive and require specialized skills.
MDR vs. XDR
Extended detection and response (XDR) is a cross-platform threat detection and response strategy and is the next evolution in the answer to cut across security silos in an organization. The benefit of MDR is that it enables organizations to take a proactive approach to their security by delivering visibility across endpoints, applications, cloud workloads, and the network. In some cases, MDR providers are starting to leverage XDR technologies, given their advantages. But XDR technology requires integrations with disparate tools and can be resource-intensive for an early-stage organization that might lack the right talent.
How to Select an MDR Provider
As discussed earlier, MDR providers vary in the services, technologies, and capabilities they offer. To determine which MDR provider is the right fit, organizations should consider the questions below to help evaluate if a provider aligns with their specific needs and security goals.
1. Is the cost predictable and straightforward?
Organizations need to know if the cost for an MDR offering enables them to scale or change their service as their business requirements change. They also need to know if 24/7/365 coverage really means continuous monitoring or whether it applies only to a limited number of security events.
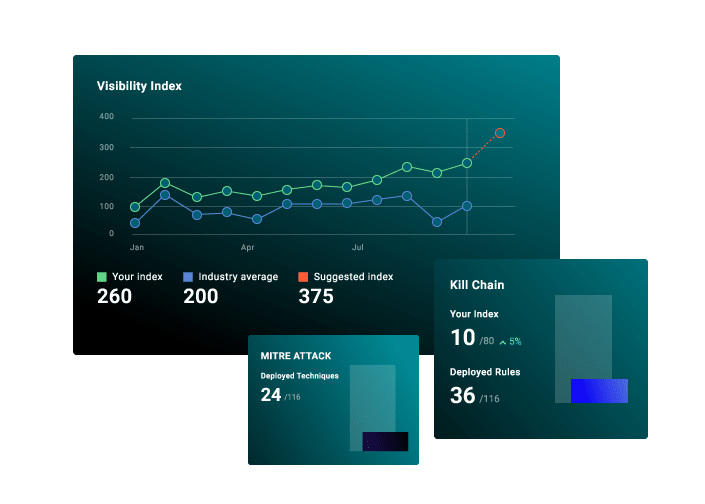
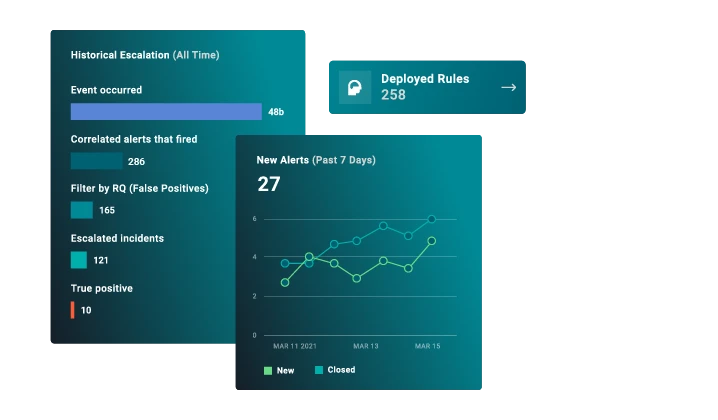
2. Are reporting and measurement included?
It’s difficult for organizations to evaluate their security programs if they have no way of determining where they stand. That’s why it’s helpful when MDR platforms come with measurements that can help security teams demonstrate how they’re decreasing risk and facing up to the threats they care about while saving time and money. Otherwise, they’ll need to implement measurements on their own outside of the MDR platform, thus creating more work for their security personnel.
3. How does the MDR provider assess threats in a customer’s environment?
MDR is helpful only if it works with organizations to address their unique security requirements. As such, the best MDR arrangements are those where the provider uses best practices based on customers’ industry, business, or department goals along with relevant frameworks to prioritize risks along with detection content.
4. Can the MDR provider work with their existing security tools?
As they work with an MDR provider, organizations might see redundancies and find themselves in a position where they can optimize their security stack. They might also eventually decide to bring on new security tools. The MDR should be able to accommodate the customer’s requirements based on their maturity—either bring the tech stack necessary to deliver services or leverage the existing investments to do so.
5. Who owns the detection content?
Organizations need to consider the prospect of parting ways with their MDR provider. If this happens, will they keep the detection content that the provider generated from them? Or will they need to start over while they look for another provider, leaving themselves exposed in the process?
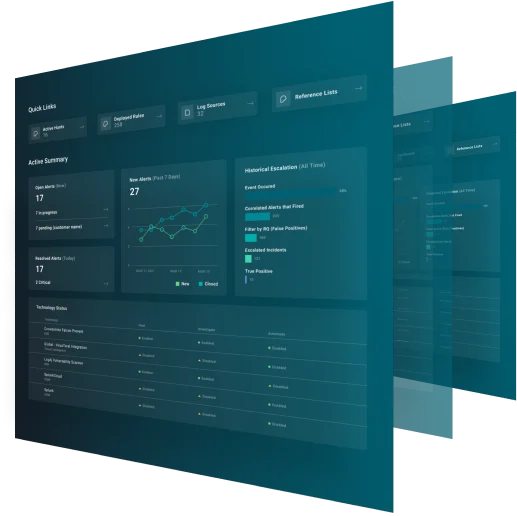
6. Will the MDR provider give them a unified view of their environment?
Organizations need a unified view of their data and tool inputs if they want their security teams to be able to make decisions in a timely manner. If an MDR provider can’t give this level of visibility, then it is difficult to make informed decisions on subsequent actions to take.
7. Does the provider offer MDR automation capabilities?
Speed is everything when it comes to response. Hence the need for automation. Specifically, an MDR provider who comes with validated automated response playbooks and who allows for the creation of custom playbooks as new threats emerge can really make a difference.
8. Is threat hunting included in the cost?
The logic behind MDR is to take a proactive approach to cybersecurity. With that in mind, advanced MDRs offer threat hunting and attack simulation capabilities to their customers. Organizations need to determine whether these services are available with a potential provider and whether they cost an additional fee.