Break Free from MDR Limitations. Take Control with ReliaQuest GreyMatter.
Managed Detection and Response (MDR) providers focus on threat detection and response with 24/7 monitoring and analysis of security events. They can seem like a quick fix, but their endpoint-focused approach often creates more gaps than it fills. Limited visibility, reactive support, and dependency on external teams can leave your organization exposed.
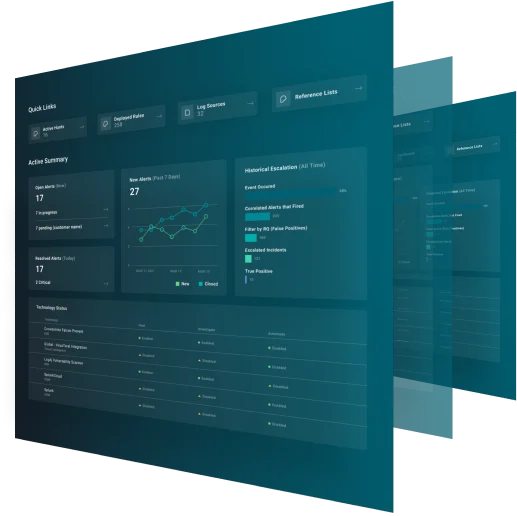
GreyMatter, the agentic AI security operations platform, goes beyond MDR to provide full visibility across your environment, business-specific detections, and autonomously handles investigations by containing threats in under 5 minutes.
Breaking Down the Difference
See what sets ReliaQuest GreyMatter apart from traditional MDR solutions.
Capability | ReliaQuest GreyMatter | MDR |
|---|---|---|
Goal | To provide proactive, continuous threat detection and response, reducing the burden on your security team. | To provide proactive, continuous threat detection and response, reducing the burden on your security team. |
Architecture | Interchangeable architecture enables direct connection with all of your security technologies, eliminating data silos. | Limited integrations, primarily focused on endpoint detection and response (EDR). |
Detection | Detects threats across all technologies or vendors in your technology stack, leveraging API capabilities. | Generic detection rules with a one-size-fits-all approach. |
Investigation | Agentic AI autonomously conducts full investigations from alert triage to execute response actions. | Limited alert context from other security tools reduces alert fidelity, increases volume, and hampers investigation time. Operates as a “black box” with little to no visibility for the customer. |
Containment and Response | Automatically contains threats in under 5 minutes by executing response actions across any technology or vendor in your security stack. | Containment is heavily reliant on an EDR agent installed locally, limiting response actions that could be taken. |
AI | Scale your team with fully autonomous agentic AI handles Tier 1 and Tier 2 tasks, so your team can prioritize high-level tasks. | Generative AI assists with incident summaries but lacks full operational capabilities. |
Threat Hunting | Fully automated hunts across all technologies and environments, including cloud, and OT. | Sometimes available as a costly add-on but is typically limited to endpoint focus, which limits the view of its true impact. |
Threat Intelligence | Full threat actor, vulnerability, and campaign profiles with real-time threat feeds built directly into the platform. Continuously monitors the deep, dark web, distributing the latest IOCs to your technologies to block threats proactively. | Typically, does not implement custom threat feeds and lacks visibility into external threats from the deep, dark web. |