Phishing is the practice of stealing credentials by masking malicious intent behind the appearance of something innocuous. An email that looks like it’s from a social network asking you to reset your password is one of the most common versions. Once a user submits their credentials, attackers then use the victim’s account to spread the infection to new victims or share sensitive materials.
Common phishing tactics
Phishing works all too well because it takes advantage of our innate trust in our fellow human beings. If Facebook is telling me that I need to reset my password, who am I to argue? If a family friend needs money, why wouldn’t I help? Bad actors will take advantage of human nature through a technique known as social engineering.
The most valuable thing phishers are after is our information, a cat that never really gets back in its bag. We only get one birthday and mother’s maiden name, both of which fraudsters can use to steal our identities or spread malicious software.
How to spot a phishing attempt
Source: itgovernance.co.uk.
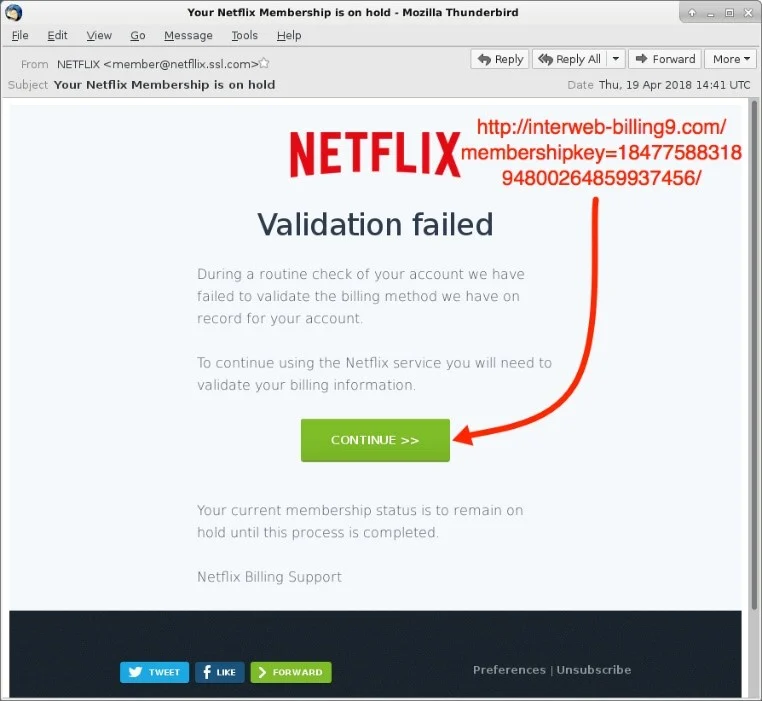
Always verify that somebody asking you for sensitive information is who they say they are. You’re not the first person to get an email claiming to be from Facebook that’s coming from a burner email address with a domain name you don’t recognize. While the systems we want to have our sensitive information, like our bank or hospital, are getting better about protecting our information, there’s always the chance that Dave from Facebook is not Dave and not from Facebook.
Here are a few ways you can :
Typos and grammatical errors: Phishing emails are often poorly written. If you get an email claiming to be from a large company and the message is riddled with errors, it’s likely fake.
Fake domains: If the sender claims to be from Facebook, but the domain of the sender address isn’t facebook.com, it’s a good bet the email is fraudulent.
Too-good-to-be-true offers: Nobody is giving away a free Apple Watch to random email accounts. The old axiom is relevant here: If it sounds too good to be true, it probably is.
For more dead giveaways that a message is a phishing attempt, check out the GreyMatter Phishing Analyzer.
Does your security team need help with your anti-phishing measures? ReliaQuest GreyMatter integrates with email security tools to examine URLs, email accounts, and other phishing indicators so your team is free to focus on higher-value tasks.




