Editor’s note: This is part three of a series on threat detection.
Part one - Detection 101: Top 5 Detection Data Sources
Part two – Detection 101: Top Detections for Malware and Ransomware
Part three (this blog) – Detection 101: Top Detections for Email Phishing and BEC
This marks our third and final installment in our Detection 101 series. So far, we’ve covered the foundational data sources and corresponding threat detections in our initial blog, as well as detections for malware and ransomware in our second installment. Today, we delve into the important detections needed to locate email phishing and business email compromise (BEC) attacks.
Email phishing refers to a fraudulent attempt to obtain sensitive information, such as usernames, passwords, and credit card details, by posing as a trustworthy entity through electronic communication. In a BEC attack, a scammer uses email to trick someone into sending money or disclosing confidential business information.
BEC is a focus area for most enterprise security teams given the potential risk. According to the most recent data from the FBI’s Internet Crime Complaint Center (IC3), the total domestic and international exposed dollar loss attributed to BEC between October 2013 and December 2022 exceeds $50 billion.
Phishing Detections: Starting the DIR Process
Email phishing and BEC attacks both rely on email communication, so an email security tool is integral to protecting your environment. However, while an email security tool plays a central role in detecting phishing attempts, it’s not the sole solution.
To effectively detect phishing and BEC incidents, it’s important to take a holistic approach, which requires gathering telemetry data from various sources throughout the network and security tool spectrum. The data sources beyond email security solutions include:
Email Security
Email Server
User Behavior Analytics
Forward Proxy
Cloud security access brokers (CASBs)
Network Intrusion Detection
Endpoint Detection and Response (EDR)
Business Applications
Multi-factor Authentication (MFA)
Threat Intelligence Platforms (TIPs)
Network Firewalls
Web Security Gateways
The initial step in detecting phishing and BEC attacks usually involves an email security tool. In Table 1 below, you will find the foundational detection rules for email security tools.
Table 1: Baseline Detection Rules and Data Sources for Phishing and BEC: Email Security Solution Focus
Detection Rule | Data Sources |
Potentially Malicious Phishing Email | Email security |
Allowed Impostor Email | Email security |
Malicious Email Wave from Internal User | Email security |
Suspicious Email [Client] Rule Created | Email security |
Allowed Malicious Email | Email security |
Different security tools can combine to provide optimal protection against phishing and BEC, but also provide detection-in-depth to prevent a threat slipping through a single protective layer.
Enterprises typically have multiple layers of defense against email-borne attacks. Applying a tuned detection rule across those data sources increases the likelihood of locating and isolating a phishing attack before damage can be done. For example, a “Phishing Link Clicked” event detects a malicious URL in an email that was clicked by a user and allowed. This event can be detected using logs from email security, CASB, network intrusion detection, threat intelligence, and EDR security solutions. In Table 2 below, you will find the baseline detections rules you should use when you have multiple data sources.
Table 2: Baseline Detection Rules and Data Sources for Phishing and BEC: Multiple Data Sources
Detection Rule | Data Sources |
Allowed Attachment with Suspicious Extension | Email security, email server, or network intrusion detection |
Typosquatted Company Domain Request | Forward proxy |
Phishing Link Clicked | Email security, cloud application security broker, network intrusion detection, or endpoint detection |
Email Forwarding Rule to External Domain | Network intrusion detection, email server, business application, cloud application security broker, or user behavior analytics |
Email Send as Permission Assigned for Critical User | Business application or email server |
Suspicious Email Inbox Activity- Signature Detected | CASB, email security, or user behavior analytics |
Phishing Link Clicked Followed by Multifactor Authentication | Email security and MFA; CASB and MFA |
Combining multiple data sources for multi-point detection helps combat recent threats attempting to overcome MFA. One of the few ways that an attacker can bypass MFA is to phish a user. The attacker tricks the user into submitting their credentials into a fake website and then prompts them to enter their MFA. The rule below takes a step beyond a “Phishing Link Clicked” rule that used a single tool to add an MFA event. The rule combines two steps. First it detects a malicious URL in an email that was clicked by a user and allowed. Then, it requires the user to authenticate successfully via MFA.
Table 3: Baseline Detection Rules and Data Sources for Phishing and BEC: Multi-point Detection
Detection Rule | Data Sources |
Phishing Link Clicked Followed by Multifactor Authentication | Email security and MFA; CASB and MFA |
Threat intelligence informs and improves detection by leveraging the latest phishing indicators of compromise (IoCs) such as malicious URLs, credential harvesting sites, and bad email senders. Incorporating good intelligence that aligns with your existing countermeasures improves your defensive layers against phishing and BEC.
An optimal approach to detecting phishing and BEC uses as many relevant data sources and rules as possible. Making certain detections are deployed across all elements of the attack surface that might have visibility to phishing or BEC ensures that you detect and mitigate threats promptly.
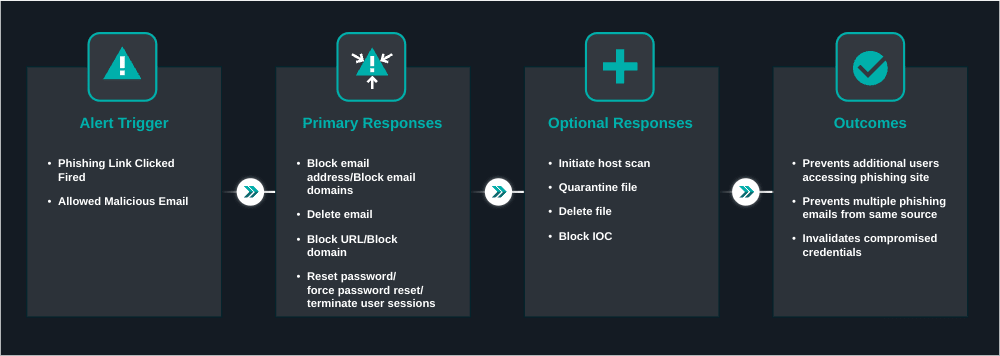
Accelerating Phishing Response: Playbook Automation
When one of these detections trigger, it’s important to quickly act to prevent an adversary from executing malicious actions in your environment. Automating the typical response actions for phishing or BEC attacks can close that window of vulnerability. These response actions may include resetting user credentials, deleting an email, blocking a URL or domain, or blocking an email address or email domain.
Having an analyst review an alert and execute a playbook can be time-consuming, and time is precious when an adversary is executing their malicious actions in your environment. Automating response actions for alerts can close that window of vulnerability and frees up time to work on higher priority projects and tasks.
Indeed, phishing campaigns often target more than one user, making the potential impact even greater. By automating a response, you can take multiple potential incidents off the table. If a threat actor uses the same URL in their campaign, by quickly blocking that URL, you can mitigate the risk of users visiting that malicious site.
To prevent an automated action wreaking havoc in your environment due to false positive, it’s important to focus only on phishing alerts that are of high fidelity and have proven to produce high true–positive rates. Additionally, when selecting actions to be taken for these alerts, it’s important they don’t disrupt business operations. Using an automated response that fires when the alert is received frees up time.
For example, you can save yourself time and accelerate response action with an automated response play for the following scenario:
“Phishing Link Clicked” detection alert originates from your email security, CASB, EDR, or network security solution.
Credentials are reset in Identity solution.
Email is deleted from user(s) mailbox(es).
Email address or email domain is blocked in email security solution.
The detections mentioned above provide a technology-driven method of detecting threats, however, phishing emails continually evolve and are crafted to slip past technology detection layers. It’s important to educate users about email-borne threats so those users can become “detectors” and promptly report suspected phishing attempts to an abuse email box. While the initial detection may be driven by a human, having an automated way of processing user-reported phishing and BEC emails saves valuable time.
The diagram below shows have the GreyMatter security operations platform would execute this Automated Respond Play for a phishing alert.
To dive deeper into how to best respond to phishing attacks, visit our Automating Your Phishing Playbook blog.
Measuring Detection Effectiveness
The previous blogs in this series explained the importance of measuring the breadth and diversity of data sources along with measuring the mean time to resolve (MTTR) incidents. Beyond those baseline metrics, to better understand how your security operations are performing when detecting phishing and BEC, you should also examine:
MITRE ATT@CK coverage: MITRE ATT@CK helps you understand your detection coverage, particularly when it comes to techniques for credential access, a key target for phishing and BEC. This coverage measures how well your deployed detection rules align with the techniques in the MITRE ATT&CK framework. This comparison is done by evaluating the deployed techniques against the total possible techniques based on the technologies in use.
**False-**Positive rates: False–positive alerts are those that have been adjudicated as 100% non-malicious and require rule tuning. Keeping an eye on false–positive rates helps to tune out noise so you can focus on meaningful detection events.
Conclusion
Detecting and preventing phishing and BEC attacks requires a multi-layered approach using various tools and data sources. Email security solutions are crucial but should be supplemented with other tools like user behavior analytics, threat intelligence platforms, and network intrusion detection. By combining multiple data sources and applying detection rules across them, organizations can enhance their defense against these attacks.


