Key Points
Phishing activity accounted for the majority of tactics, techniques, and procedures (TTPs) ReliaQuest observed in the past year, and it’s no less popular today. By analyzing data from the first month of 2024, we have identified patterns of increasingly sophisticated phishing methods currently in use.
Cybercriminals are using automated systems to create disposable Azure email accounts for phishing, necessitating advanced detection methods rather than simply blocking individual senders.
Files included in phishing emails often are named strategically, sometimes with double extensions, to appear credible. Current event–based keywords are also being used to encourage trust.
Phishing operators are abusing the InterPlanetary File System (IPFS), WordPress websites, and dynamic web application hosting.
In an unusual tactic, threat actors embedded Amazon Web Services (AWS) access keys in phishing links.
Pre-emptive mitigation steps include monitoring and controlling web access, employing advanced threat detection systems, and training individuals to identify common social-engineering tactics.
It will come as no surprise that phishing was the most popular way for threat actors to initially access a targeted network in 2023—representing a staggering 71.1% of all tactics, techniques, and procedures (TTPs) observed in ReliaQuest customer true-positive incidents. Phishing has become ubiquitous and deeply ingrained in cybercrime. That such an old technique continues to dominate the first stage of the attack chain illustrates its effectiveness and constant threat, despite advancements in cybersecurity and newer, more sophisticated attack vectors. Its success is rooted in its simplicity and exploitation of the most vulnerable link in any security system: humans.
To provide current insights into threat actors’ use of phishing, we analyzed data from January 2024 activity in the environments of ReliaQuest customers, spanning multiple sectors and regions. We aimed to examine real-world examples and uncovering the latest patterns in phishing attacks. The result is actionable advice provided throughout this report, enabling defenders to proactively safeguard against this threat.
Azure Email Account Abuse
Our data showed that phishing campaigns against organizations frequently use disposable email accounts set up with Azure, Microsoft’s cloud computing platform, all with similar naming conventions. This indicates that the creation of the accounts is likely automated and occurring on a very large scale, and that the popular recommendation to block individual senders is ineffective.

Figure 1*: Sample of abused onmicrosoft.com emails*
The addresses of malicious sender accounts seem to follow a naming pattern: [word]_[random string]@x[6 random characters].onmicrosoft.com. Attackers seem to be exploiting the Microsoft 365 ecosystem by creating numerous trial accounts with that software suite, which inherently offers access to Exchange Online. The latter is a key component of the Microsoft 365 suite, providing email hosting and enabling users to manage their email, calendar, and contacts.
Threat actors can automatically enable Exchange Online, likely by using a script, and use the legitimate platform to launch their phishing campaigns. Taking advantage of a trusted corporate service to distribute phishing messages lends authenticity to the malicious activity. And it can be very effective: Phishing campaigns will persist until the trial period ends or the account is shut down to prevent malicious activity.
The use of Azure for temporary phishing email accounts is notable because of the domain containing “microsoft.com”. The recipient of a message from such an account may mistake it for a Microsoft email, especially if the subject line conveys urgency—and quickly click a phishing link or malicious attachment. Compared to other free email providers, such as Gmail, this tactic is more challenging to identify as phishing, making it an ideal strategy for threat actors. It is highly probable that the abuse of Azure email accounts will continue to see an upward trend.
To counter the use of Azure accounts sending phishing emails, establish a detection method that targets the common naming convention. Specifically, set up an email quarantine policy to isolate messages sent by an address including @x.onmicrosoft.com. This will capture suspicious emails before they reach users’ inboxes, in a dynamic, pre-emptive defense approach.
Malicious Attachment Techniques
According to our data set, phishing operators are choosing from multiple techniques to deliver malicious files. Here are some of the most common ones we saw:
Double extensions: Filenames with double extensions (e.g., pdf.exe) masquerade as benign, and can trick users into executing a malicious file. Most email security solutions successfully block such activity, as there are very few legitimate use cases for double extensions in business.
ISO image: An ISO file (extension: .iso) is a copy of an optical disk in a single file. ISO images are automatically mounted to the host upon opening, making it a more enticing option to deliver malware than creating a malicious ZIP or RAR file, which require decompression to view the contents.
Fake voicemail notification: Attackers are sending emails whose subject lines claim the recipient has received a voicemail. A typical message features an HTML file masquerading as a voicemail notification, which contains a link directing the user to a credential harvester or prompting them to download the malicious file. Voicemail notification emails are almost always fake (and malicious), so this technique is easy to mitigate if the recipient knows what to look for.
Encryption and naming with password: Attaching an encrypted file with a password in the name (e.g., rar) helps prevent email security tools from scanning the contents. By including the password in the filename, the user can open the file and execute the malicious contents.
Approximately 50% of the attachment file types we identified were HTM/HTML or PDF, suggesting that HTML smuggling and malicious redirection remain favored tactics to harvest credentials. Files are strategically named to seem credible and pressing; ReliaQuest has pinpointed the five most frequently used keywords in our data set’s phishing filenames, which were intended to entice recipients to open attachments:
Insurance
Benefits
Payment
Order
Invoice
There was also a 10% increase in emails mentioning “tax” and “taxes” from December 2023 to January 2024, aligning with the onset of tax season in many countries. During that timeframe, staff are more likely to expect tax-related communication. Threat actors are very likely considering current events when devising phishing emails, aiming to boost the likelihood that an unsuspecting user will interact with the email.
Phishing Infrastructure Options
Threat actors can choose from options when seeking a host for their malicious content (such as the notable ones described below). Once the fraudulent webpage is live, the attacker distributes links to it, through phishing emails, social-media messages, or other digital communication channels, targeting unsuspecting users. Interaction with the link directs the user to the counterfeit page. Here, they might be prompted to either download a file or enter sensitive information, such as login credentials, personal data, or financial details, believing they are complying with a legitimate request.
IPFS
To circumvent email and network security, phishing operators are increasingly abusing the IPFS: a protocol and network that enables a content-addressable, peer-to-peer method of storing and sharing hypermedia in a distributed file system. Attackers are crafting phishing attacks by embedding fraudulent forms within HTML files, which they then upload to the IPFS. On this distributed network, the malicious HTML files can be accessed via IPFS gateways—specialized web services that allow anyone with a web browser to retrieve files from IPFS without special client software. Phishing operators send emails that include links to these gateways. When recipients click on the links, they are directed to the deceptive forms hosted on the IPFS, and may unwittingly input sensitive details.
We’ve seen an increase in use of the IPFS system in phishing campaigns, which can dynamically adapt to the target: changing a page’s content and simulated branding to whatever is appropriate to trick that particular page visitor. This makes the phishing extremely difficult to detect. Using the IPFS is highly attractive for cybercriminals looking to publish content on a network without establishing their own infrastructure. As a bonus, a distributed file system like IPFS lets them minimize the costs associated with hosting malicious phishing pages.
The gateway provider ipfs[.]io has been used the most to facilitate this phishing technique. We’ve also identified other IPFS services linked to phishing activities, such as cloudflare-ipfs[.]com and dweb[.]link. These webpages that host IPFS content seem to exhibit similar patterns, typically following this format: https://[gateway]/ipfs/[CID Hash].
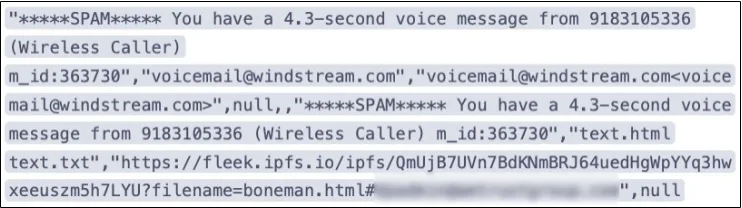
Figure 2*: IPFS phishing email log example*
To counter phishing activity abusing the IPFS, gateway providers try to identify and remove links to malicious files, disrupting the accessibility of these fraudulent resources. For organizations, ReliaQuest recommends configuring email filtering rules to flag and isolate messages containing URLs that follow the patterns typically used by IPFS gateways. Or, if IPFS services are not used within the business, block them altogether.
WordPress
Some threat actors are using compromised legitimate WordPress websites to host malicious content—although a less common practice than creating new infrastructure and one requiring more effort than using IPFS, for example. Various techniques can be employed, but compromised WordPress sites are typically associated with drive-by compromise.
Upon gaining access to a WordPress website, the attacker creates a fraudulent webpage, without the site owner’s knowledge. The page either mirrors a well-known page, such as a Microsoft login page, or at least matches the colors and font of the compromised site to appear legitimate.
The likelihood of traffic to a compromised WordPress page being blocked is much lower than it is for IPFS infrastructure, owing to the legitimate root domain. Trust in the root domain’s authenticity leads users to be less suspicious of the content, increasing the chances that they’ll interact with it. This makes compromising WordPress sites an attractive method of conducting covert operations.
Dynamic Web Application
Dynamic web application hosting is increasingly popular; platforms such as Netlify and Cloudflare R2 enable attackers to upload web application code and execute it within a temporary sandbox, which can host credential-harvesting pages. These dynamic phishing pages are adept at evading detection while presenting seemingly legitimate content to gain users’ trust—a blend of stealth and authenticity that appeals to cybercriminals.
Dynamic hosting services are highly available and scalable; when used maliciously, threat actors can rapidly create and distribute links to phishing sites. In addition, without the need to maintain a dedicated server, attackers can quickly adapt and change their tactics with minimal effort and cost. They can also exploit the reputations of these well-known hosting platforms to bypass unsophisticated security filters that block only unknown or disreputable domains.
For most standard business applications, there is often little reason to permit access to content from r2[.]dev (Cloudflare) or netlify[.]app. If those domains aren’t applicable to business operations, restrict access to them at the network’s edge.
Embedding AWS Credentials
In one noteworthy strategy, a threat actor embedded AWS credentials within a phishing link. As illustrated in the example below, the URL included the AWS access key required to access the contents of the AWS instance where the malicious content was hosted. This approach is quite rare and is probably designed to hinder public scanners from detecting and eliminating phishing pages. This prolongs the lifespan of the phishing infrastructure and ensures that only individuals possessing the access key can visit the site.
Notably, it can be difficult for recipients to identify the URL as phishing due to the legitimate root domain. Since public scanners are unable to flag the content as phishing, adversaries can increase the likelihood of bypassing email security and directing successful traffic to the malicious infrastructure, thereby increasing the chances of successfully harvesting credentials. We’ll likely continue to see this tactic, given that AWS is a highly prevalent domain and it’s difficult to employ dynamic detections on the infrastructure.
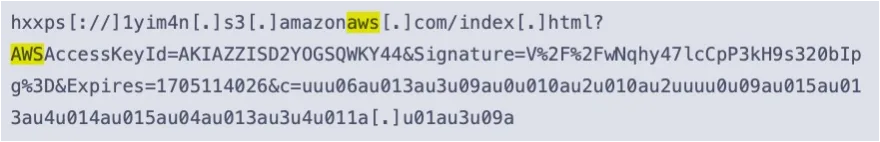
Figure 3: Amazon AWS URL access key example
Mitigation: Recommendations and Best Practices
In addition to the tailored mitigation steps mentioned throughout this report, we offer the following inexhaustive list of recommendations and best practices. These actions will help establish a secure foundation against phishing-related TTPs we have observed recently.
Monitor and control web access, blocking lesser-known dynamic web application-hosting domains, such as dev or netlify.app if not essential for business operations. This limits the reach of phishing attacks using these platforms.
Employ advanced threat detection by configuring detection systems to identify and flag emails containing URLs that follow the patterns typically used by IPFS gateways or compromised WordPress sites. Blocking IPFS services altogether may be necessary if they are not used by the organization.
Employ multifactor authentication (MFA) for all accounts, for an additional layer of security that can help reduce unauthorized access.
Educate and train users, regularly, to recognize phishing attempts—especially those that mention current events or contain urgent-sounding keywords like “tax,” “invoice,” or “payment.” Educated users can report potential phishing emails to an abuse mailbox, which can be used for analysis and preventative measures.