On October 7, 2023, the militant group, Hamas, fired rockets and sent fighters into border regions of Israel, resulting in large-scale casualties and hostages. These developments represent Hamas’s most ambitious attack on Israel to date and coincide with the 50th anniversary of the Egyptian-Syrian surprise attack on Israel in 1973 that preceded a major war in the Middle East. The world’s hacktivist gangs and nation-state–aligned groups, along with other cyber threat actors who are highly influenced by global geopolitical events, will likely react to the conflict in the coming days. This blog summarizes what we know so far about the conflict’s cyber repercussions and explores the threats organizations should look out for.
How Have Hacktivists Reacted?
Initial reactions from hacktivists have been overwhelmingly sympathetic to Hamas. The official Telegram channel of the pro-Russia hacktivist group “Killnet” posted a photo pledging the group’s support for Hamas’s operation and promising anti-Israel attacks, writing: “Government of Israel, you are to blame for this bloodshed. Back in 2022, you supported the terrorist regime of Ukraine. You betrayed Russia. Today Killnet officially informs you about it! All Israeli government systems will be subject to our attacks!”
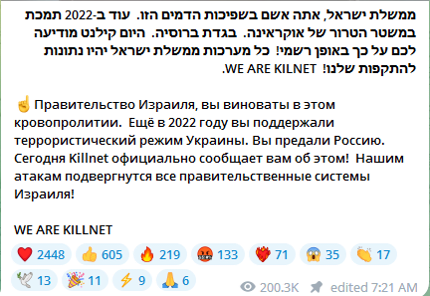
Figure 1: A post in the Killnet Telegram channel expressing support for Hamas
Killnet’s declaration was echoed by the pro-Russian hacktivist group “UserSec,” which claimed to have targeted several Israeli government websites with distributed denial-of-service (DDoS) attacks. Another hacktivist group, “Anonymous Sudan,” which likely supports the Kremlin despite its name, alleged it had obtained unspecified “zero-day vulnerabilities from Romania” to use in anti-Israel attacks. Other posts on Anonymous Sudan’s official Telegram channel and related Telegram chats discussed targeting the Iron Dome defense, a crucial Israeli defense mechanism to prevent indirect-fire munitions from impacting Israeli cities, and named Anonymous Sudan’s target as the pro-NATO Israeli government.
The Krypton network, which advertises DDoS services for hire, also offered to sell its services to hacktivists wishing to target Israeli organizations. DDoS attacks, which usually flood websites with traffic to render them unusable, have become a mainstay of hacktivist groups and will likely be one of the most common cyber threats that Israel and pro-Israeli organizations will face. The Anonymous Sudan Telegram channel has promoted the DDoS tools Mhddos, Ru DDoS C2, Hulk, and Krypton.
Other hacktivist groups are promising attacks in defense of Israel. The pro-Israel group “ThreatSec” has reportedly compromised the Palestinian internet services provider AlfaNet.
What Have We Seen from Nation-State Actors?
Nation-state reactions to the conflict have naturally been much more obfuscated and difficult to attribute. However, it is highly likely that Iranian cyber threat groups in particular will have an interest in influencing the conflict via the cyber battlespace; Hamas has publicly stated that its attacks on Israel were backed by Iran.
Several domestic threat groups operate from Iran and have the potential to conduct successful attacks against organizations with even the most mature security programs. Given that Iran-linked threat groups typically focus attacks on countries that have a strained geopolitical relationship with Iran, such as the US and Israel, it is realistically possible that activity associated with Iran-linked cyber threat groups will increase in response to these events. However, potential attacks would likely be strategic and targeted, impacting government-linked Israeli businesses or companies working in Israeli critical infrastructure or government, telecommunications, and defense.
It is also possible that Russia- and China-aligned nation-state groups will capitalize on the chaos resulting from Hamas’s operation and seek to conduct espionage to track the West’s response to the conflict or to push desired narratives in support of one side of the conflict.
What Should You Be Doing?
The Hamas–Israel conflict will likely have a significant impact on organizations in Israel and globally. Organizations that partner with Israeli companies or otherwise express support for Israel could be considered a legitimate target for anti-Israel hacktivists and other threat groups responding to developing events. Western organizations will likely be considered an extension of Israeli infrastructure, due to the support that the US and other NATO-aligned countries have provided to Israel.
Organizations should take the following proactive steps.
To protect against DDoS attacks—hacktivist groups’ most common tactic—organizations should implement anti-DDoS solutions. Other DDoS mitigation steps can be found within our recent blog on the resurgence of hacktivism.
Conduct a risk assessment of external-facing infrastructure and ensure that any weaknesses—including high-risk vulnerabilities and misconfigurations—are addressed in a timely fashion. Reduce your organization’s internet-facing footprint to minimize the attack surface.
Ensure that incident response teams are aware of the heightened risks from threat groups reacting to the conflict, ranging from hacktivists to Iranian nation-state-aligned groups. Organizations should update callout lists and put incident response plans in place to react accordingly.




