With the decline of the “Anonymous” hacking group, hacktivism was commonly thought to be a diminishing threat, confined to a handful of attacks that caused only minimal and temporary damage to targeted networks. But, since the start of the Russia–Ukraine war in February 2022, the landscape has changed dramatically.
The war has created an increasingly permissive—and even government-sanctioned—arena for hacktivists. The Ukrainian government, for example, created the “IT Army of Ukraine” to tackle the growing cyber threat from Russia, meaning its volunteers operate with legality. Of course, with any action there is a reaction. The ” now routinely conducts distributed denial of service (DDoS) attacks against companies based in NATO-aligned countries. This blog will explore the current state and likely future of hacktivist activity.
Hacktivism in 2023: Permitted, Amorphous, Crowdsourced
The revival of hacktivism has largely been facilitated by one event: Vladimir Putin’s “special military operation,” or Russia’s invasion of Ukraine. Much has been written on the conflict and its impact on the cyber-threat landscape; however, nowhere is this more evident than in its influence on hacktivist activity:
The lines of attribution between threats are blurring. It’s becoming increasingly difficult for security researchers and defenders to distinguish between cybercriminal, nation-state, and hacktivist activity, with many of these groups using similar techniques or deliberately obfuscating their identities.
For example, in May 2023, the “Malas” ransomware group, which practices double extortion, demanded donations to a charity rather than a ransom payment to the group. Nation-state threat actors have also been exploiting hacktivism trends to hide their motives, with varying levels of success.
Hacktivism has become crowdsourced. Simple DoS tools are distributed online, enabling threat actors with minimal technical knowledge to conduct cyber attacks. The IT Army of Ukraine, Killnet, and other hacktivist collectives have directed tens of thousands of online followers to conduct attacks via their Telegram channels.
Within the context of the war, hacktivism has also been endorsed by the state, encouraging activity that can harm adversaries. This has dramatically changed the perception of hacktivism, moving away from the notion of hacktivism being solely a harmful act and instead toward a perception of defiance and self-defense.
ReliaQuest previously observed the introduction of , established for the purposes of training and facilitating hacktivist activity. These locations greatly lower the barrier of entry for actors wishing to engage in future hacktivist activity.
Analysis of Hacktivist Activity
From February 16 to July 31, 2023, ReliaQuest observed more than 650 website domains named on the Telegram channels operated by Killnet and “Anonymous Sudan.” Despite its name, it is realistically possible that Anonymous Sudan is composed of pro-Russia hackers who are operating under the guise of Sudanese geopolitical issues to mask their true agenda—we told you attribution was becoming trickier. Killnet is the best-known and most-active group to become prominent since the Russia–Ukraine war began.
Some domains were named more than once during the reporting period, sometimes on consecutive days, suggesting that the groups launched protracted and disparate campaigns against individual targets.

Figure 1: Number of domains listed on Killnet/Anonymous Sudan Telegram channels,February 16–July 31, 2023
A month-by-month analysis provides insight into how groups’ priorities change, as well as insight into key trends and targeting preferences. Activity peaked in April 2023, likely because Anonymous Sudan claimed responsibility for DDoS attacks against Israeli targets, including the websites of two Israeli ports, the National Insurance Institute, and the Institute for Intelligence and Special Operations (aka Mossad). Anonymous Sudan claimed to be showing support for the people of Palestine, in the context of the Israeli-Palestinian conflict.
Most-Targeted Sectors
Killnet and Anonymous Sudan often target healthcare organizations (see Figure 2), likely for the substantial disruptive impact that such attacks can inflict. Hacktivist groups prefer targeting entities that can’t afford to face significant downtime, particularly those involved in critical national infrastructure; technology, government, and media organizations are also popular targets for hacktivist groups.
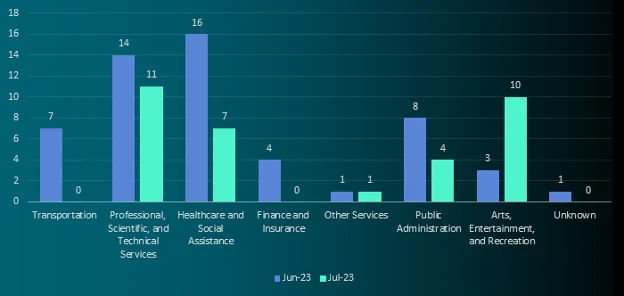
Figure 2: Number of domains listed on Killnet/Anonymous Sudan Telegram channels by sector,June–July 2023
One notable finding from our analysis was the absence of a large number of attacks against finance and insurance companies. In June 2023, Killnet, Anonymous Sudan, and the now-defunct “REvil” ransomware group—again, likely a play on obfuscation—allegedly formed an alliance to conduct attacks on European banks. In a video posted online, they threatened to conduct the “most powerful cyber attacks [much more serious than DdoS] in the recent history of the world.” Killnet claimed that the goal was to prevent funds from reaching Ukraine. The figures in the above graph seemingly contradict those claims.
However, it is realistically possible that these attacks were conducted but not announced on Telegram. Exactly why this would occur is unclear. It is realistically possible that Killnet conducted the attacks in an impulsive manner or otherwise did not want to provide a warning for its impending activity. We can also deem it realistically possible that other companies targeted by Killnet were similarly not posted on Telegram, so the group’s overall activity level is likely to be greater than represented in the graph above.
Future Outlook
The war in Ukraine looks set to continue over the long-term future (beyond 12 months), and as a result, it is likely that related hacktivist activity will continue, perhaps influenced by additional geopolitical drivers and flashpoints. Other developments that could take place include the following.
The tactics, techniques, and procedures (TTPs) used by these groups have remained relatively consistent since Anonymous activity peaked (approximately 2012–17)—predominantly DDoS, but also targeted data breaches and defacement/doxxing. It is realistically possible that this will change in the long-term future.
Given the ease with which budding threat actors can access commodity malware—and the introduction of dedicated locations for training new hacktivists—it is likely that this will be a space that hacktivist actors could move into. While hacktivism is absolutely a threat right now, the introduction of ransomware or destructive malware would significantly increase the risk associated with hacktivist actors.
It is also likely that nation-state groups will similarly obfuscate their activity by masquerading as hacktivists, either from the outset or by leaving hacktivist-aligned artifacts to throw off defenders’ attempts at attribution.
What Should You Be Doing Now?
With most hacktivist activity being conducted via DDoS attacks, ensuring that you have a robust DDoS mitigation service in place is absolutely essential. To improve your resilience in the face of such activity, you can start with the following steps.
Reduce your organization’s internet-facing footprint to minimize the attack surface.
Use load balancers to minimize the risk from DDoS attacks, in addition to web application firewalls (WAFs) with dynamic blocking based on rate-based rules.
Use network appliances and host-based security software to block network traffic that is not necessary within the environment, such as legacy protocols.
Apply extended access control lists (ACLs) to block unauthorized protocols outside the trusted network.
Filter boundary traffic by blocking the IP addresses from which attacks originate, blocking ports being targeted, or blocking protocols being used for data-packet transport. To defend against SYN floods, enable SYN cookies.
Enforce proxies and use dedicated Domain Name System servers and other services, and allow those systems to communicate only over the respective ports/protocols, instead of all systems within a network.
The ReliaQuest Threat Research Team continues to monitor the Telegram channels of Killnet and its affiliate groups, reporting any targeted domains as they appear. GreyMatter Digital Risk Protection (GMDRP) automatically collects data from the Telegram channels of other hacktivist groups; a GMDRP customer will be alerted if a domain associated with their organization’s assets is named on one of these channels.
These early indicators and warnings can make all the difference in a response to a hacktivist attack, enabling customers to act proactively.





