To say that 2021 was a turbulent year for security teams would be a massive understatement. Last year, we observed paralyzing ransomware operations against critical infrastructure, supply-chain attacks impacting hundreds of organizations, and state-sponsored espionage campaigns leaving no company—even those with expensive firewalls—feeling safe.
Within this messy ecosystem, initial access brokers (IABs) have established themselves as a pillar of cybercrime in 2021. The rise of cybercrime has created fertile ground for IABs, who have been able to exploit the constant demand for readily available accesses. In 2021, we observed more IAB listings than any year before. The IAB market has been able to adapt to the ever-changing conditions of the cybercriminal ecosystem and maintain business continuity.
In 2021, the Photon Research Team observed a 57.45% growth in the number of IAB listings advertised in cybercriminal forums, compared to 2020
In our 2020 research report Initial Access Brokers: An Excess of Access, we stated that the IAB market was heading towards an unprecedented level of business maturity. IABs were selling access to a wider-than-ever range of victims, regardless of size, industry, country, or revenue. One year later, we can confirm this trend and further claim that this market is close to reaching full potential, given the consistency of quantity and quality of high-level accesses sold by IABs.
To better understand how these threat actors evolved in 2021, we’ve analyzed almost 800 listings advertising access to organizations, posted 01 Jan 2021 to 31 Dec 2021. The sections below dive into the research findings;, here are the key points:
The retail sector has been the most targeted by IABs, which is likely exacerbated by the number of e-commerce websites with poor security.
Access to government-like organizations ranked highest in terms of average sum requested for them ($4828 per access).
Despite experimenting with new access methods, IABs have consistently used RDP and VPN solutions to access vulnerable organizations (62.8% of the observed listings featured one of them).
The US remained the country most targeted by IABs in 2021; other notable victims included France, the UK, Brazil, and Australia.
How do IABs operate in the cybercriminal ecosystem?
In past years, we published quite a few blogs on the topic of IABs. Our monitoring of them goes back as far as 2014, and we’ve been tracking the sale of access to systems since the practice first began making ripples in the cybercriminal underground. Initial access brokership isn’t a business model spun off the COVID-19 pandemic; its popularity and profitability have long simmered beneath the surface. However, in the past two years IABs have established a profitable business model garnering significant attention for its interconnection with other cybercriminal activities.
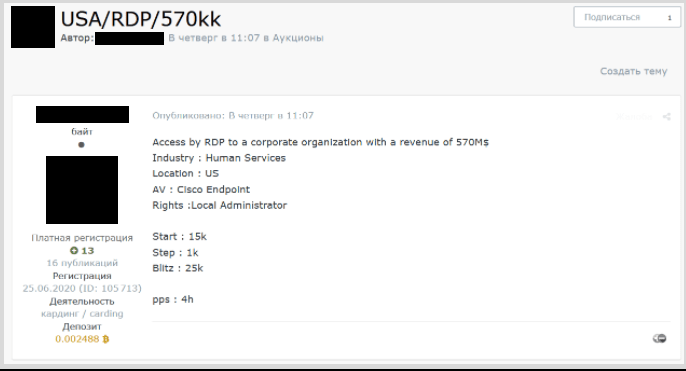
Sample of a recent IAB access listing for a US organization
IABs have acquired a significant cybercriminal role by doing the technical, dirty work and providing others with a wealth of victims to compromise easily. They are a symbol of cybercrime professionalization: a phenomenon that has malware commodity and task separation at its core. These actors are both victim and customer agnostic―something that makes them even more dangerous, from a certain point of view.
IABs gain network access to vulnerable organizations, establish the access’s value, then turn to cybercriminal forums to advertise the access and cash in on their work
These threat actors have been forced to adapt to the conditions of dark-web forums. In May 2021, IABs endured a considerable setback when cybercriminal forums XSS, Exploit, and RaidForums banned from their platform all things ransomware. The decision came after the “DarkSide” attack against Colonial Pipeline and impacted what is likely to be the IABs’ most profitable clients. Regardless, the bans have not been strictly policed, and IABs continued to operate mostly undisturbed while improving their operational security (OPSEC) measures. This translated into giving away fewer victims’ details to avoid alerting security researchers or law-enforcement authorities, for example.
Right now, IABs’ market is as mature as ever. In 2021, we observed access listings targeting a wider number of sectors and countries than any previous year. Additionally, although the usual suspects remain at the top of the list, IABs seem to be experimenting with exploiting a bigger number of software and applications to gain—and then sell—initial access to victims’ environments.
Methodology Disclosure
Before delving into the research itself, it’s important to acknowledge the methodology used to build the data set supporting it. Recognizing intelligence gaps and collection biases is critical when dealing with threat intelligence, and ReliaQuest is committed to building a transparent process when disseminating internal data.
The data set analyzed for this research does not include every access listing published on any cybercriminal platform in 2021. Our analysts implemented a structured methodology to manually triage listings on a select subset of cybercriminal platforms, prioritizing offerings that were: posted by threat actors with high reputation scores, related to key geographies and sectors, and potentially relevant to our clients. The resulting data set is significantly reliable and representative of the IAB ecosystem.
Which sector was targeted most in 2021?
Despite the increase in access listings over 2021, the most targeted sectors remained similar over time. As you can see from the graph below, cybercriminals routinely targeted retail more than any other sector. This is likely explained by the presence of many e-commerce websites that employ weak security measures and make easy targets for opportunistic threat actors, such as IABs. These websites also tend to host information that can be easily monetized, which is useful for cybercriminals in the carding business.

The most targeted sectors in 2021 and their relative change compared to 2020
Other key sectors widely targeted by IABs include technology and industrial goods, which featured heavily in our 2020 data set but jumped to 2nd and 3rd position, respectively, in 2021. Access to tech companies can be used in a variety of ways, including to acquire sensitive data and move laterally to networks of connected organizations (similar to what happened with REvil and Kaseya). Companies in industrial goods are also at risk from IAB operations given the high number of Operational Technology (OT) and Industrial Control System (ICS) devices that may be vulnerable to offensive attacks.
However, the most targeted sectors are rarely the most valuable when it comes to selling those accesses. Analyzing the average price per access for every sector paints a very different picture. At the top of this special pyramid, we find—somewhat surprisingly—the government sector (average of $4828 per access). Access to public institutions or organizations cooperating closely with governments can offer malevolent actors the potential to snap up highly valuable data, such as personally identifiable information (PII). The podium for the most expensive access is then completed by organizations operating in the financial services and retail sectors (respectively averaging at $3949 and $3062 per access).

The most targeted sectors with their relative average price
Why do IABs care about victims’ geography?
Analyzing the 2021 data set shows that the US remained IABs’ favorite target and one of the most valuable in terms of access. North American companies often operate high-value networks that may strongly interest threat actors looking to infiltrate profitable organizations; such accesses were priced at an average of $2893 in 2021. Even above North America, the most valuable regions to target for IABs in 2021 were Europe (average of $3552 per access) and the Middle East ($3390).
Other countries highly targeted by IABs include France, the UK, Brazil, and Australia. On one hand, the geographical diversity indicates that IABs will target organizations in almost any country, making them a considerable threat for most companies. But on the other hand, the top five targeted countries in 2021 are all among the wealthiest and most developed in the world, implying that IABs may focus their efforts on them to snag what they perceive is more valuable access.

Targets of worldwide IAB activity in 2021
Observing the map above, some key observations can be made about those countries in gray that were not compromised. As you can see, most countries belonging to the Commonwealth of Independent States (CIS) region were completely unaffected by IAB activity during 2021.
Why is that? Most IABs operate on Russian-language cybercriminal forums and these forums formally prohibit their members from targeting CIS-based organizations. This is one of the most reliably enforced rules in this environment; users advertising services and products targeting that region are quickly banned and have their threads removed. According to chatter we observed, cybercriminals adhere to this rule because of a longstanding belief that avoiding CIS victims will help them avoid scrutiny from local law-enforcement bodies.
As we all know, nothing is eternal. The past few weeks have shattered many perceptions about the role of law enforcement in Russia, after several arrests―including REvil gang members. And if Russia actually ends up invading Ukraine, will certain countries be excluded from the untouchables list? Ultimately, IABs are still respecting that rule but it’ll be interesting to observe how this situation will evolve.
How did IABs gain access in 2021?
IABs can get creative when it comes to gaining access to organizations. Although the most used access methods used in 2021 remained very similar to those from 2020, in recent months we’ve observed IABs experimenting with innovative means to compromise companies and maintain persistent access.
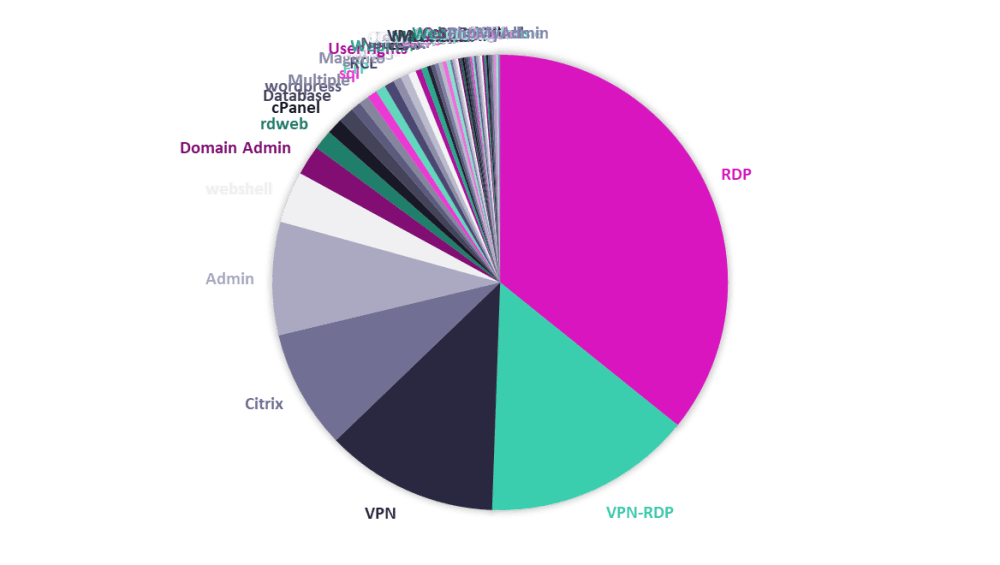
Most frequent means of access used by IABs in 2021
Out of every ten observed listings, six were for access via remote desktop protocol (RDP) and/or virtual private network (VPN) applications. These applications remain the favorites for IABs for their relative ease with which they enable compromise through default or stolen passwords obtained via brute-force attacks. As we described in our 2020 report, the use of RDP and VPN has greatly expanded since the beginning of the pandemic, without any major security improvements. Consequently, threat actors have been able to compromise these applications and drive more malicious activity.
While experimenting with innovative ways to compromise organizations, IABs relied on tried-and-tested vulnerable RDP and VPN applications for 62.8% of observed listings.
To study access price, we used a statistical method called box plot. For those of you unfamiliar, the box plot allows us to visualize the spread of data across multiple groups and compare their distributions. Using this method enabled us to focus on the median price at which an access is sold and thus reduce the weight of the most extreme results on both sides of the spectrum.
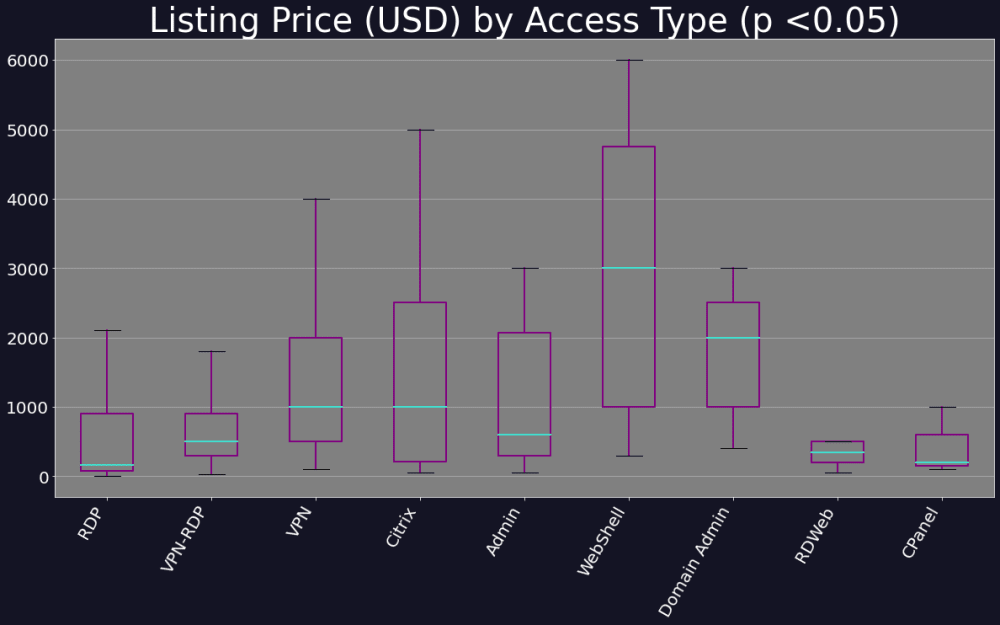
A graphical representation of median prices for the most popular access types in 2021
In this instance, the position of the box plot indicates the median price for which each access type is being advertised, as well as the general range of the market value of the particular exploit. From this graph, we can see that web-shell is, on average, the most valuable initial access type overall. It also has a wide spread, likely because of the range of privileges ascribed to web-shells. On the other hand, although RDP is the most common listing, this graph shows that its low median value likely indicates that most of its listings may often grant access to low-privileged machines.
How to monitor for the growing risk of IAB activity
IABs are playing an increasingly important role in facilitating access for a variety of threat actors. By outsourcing some malicious activity to IABs, threat actors can minimize the time it takes to identify and exploit a target of interest. They can also obfuscate their identity by avoiding many of the “noisier” steps associated with the earlier stages of the cyber kill chain.
IAB’s access prices are cheap and likely to become cheaper still, as additional brokers further saturate the market. RDP and VPN will almost certainly continue to represent the access means of choice, owing to the flexibility and capabilities afforded to buyers.
Having an in-house or out-sourced cyber-threat intelligence team monitoring the surface, deep, and dark web can go a long way in identifying relevant listings and observing access trends. If provided with timely, relevant, and actionable intelligence, defenders can prioritize security efforts to address the most significant threats. If you’d like to gauge your exposure, access a threat intelligence library of actors/groups relevant to your industry and geography, and learn how to mitigate, get a seven-day trial of ReliaQuest GreyMatter DRP™ for free here.
Additionally, our newest Vulnerability Intelligence solution can be an incredible asset for fine-tuning your vulnerability management process and monitoring many of the potential flaws targeted by IABs. By understanding the context behind individual vulnerabilities, security teams can move away from solely using CVSS scores and instead focus on what matters to your organization.
Too many vulnerabilities and far too little time are common complaints in the security community; at ReliaQuest, we pride ourselves in enabling our clients to reduce the noise and focus on what matters. Taking a risk-based approach is the most effective method of targeting vulnerabilities, and will ultimately have the most significant impact on reducing your overall cyber risk.