Editor’s note: This blog has been updated with the latest information as of March 21. Please see the “Update: March 21” section for details.
BreachForums Arrest: What Happened?
On March 17, 2023, security researchers started to report that the FBI had arrested a 21-year-old man in New York City on suspicion of being the founder and administrator of the prominent English-language cybercriminal forum BreachForums. The arrest reportedly happened on March 15, 2023, when the FBI, Homeland Security, and local city police were seen removing several bags of evidence from the house while arresting a man.
The arrested man is a 21-year-old male from New York. According to the FBI’s agent affidavit, the man operated online under the username “pompompurin” and was the owner and administrator of BreachForums. The criminal complaint accuses pompompurin of one charge of conspiracy to commit access device fraud.
Fast forward to today, March 20, 2023, pompompurin’s BreachForums cannot be accessed through any of its mirrors. The popular forum has been traditionally reliable on the accessibility front; it is then highly likely that the current downtime is associated with last week’s arrest.
Given the crucial role played by BreachForums in the current cybercriminal threat landscape, it is essential to monitor any further developments happening on this front. For this purpose, this blog will go through the history of BreachForums and analyze the potential implications of a prolonged downtime of this high-profile platform.
What Is BreachForums and Why Was It Created?
To understand the role played today by BreachForums, it is crucial to spare a few words about its predecessor in the English-language cybercriminal community, “RaidForums.” RaidForums was an English-language cybercriminal forum launched in March 2015. The forum was popular among cybercriminals trading account credentials, databases, and network access. However, RaidForums’ content was not limited to accounts and credentials; users also discussed many cybercrime specialties on topics such as gaming, social engineering activities, cryptography, and hacking.
A rare example of reliability in the cybercriminal community, RaidForums was considered one of the world’s biggest hacking forums, and, at the peak of its activity, it could count on a community of over half a million users.
However, on January 31, 2022, RaidForums’ founder and chief administrator was arrested by American law enforcement. A few days later, the forum was shut down and its infrastructure seized as a result of Operation TOURNIQUET, a complex law-enforcement effort coordinated by Europol to support independent investigations of the United States, United Kingdom, Sweden, Portugal, and Romania.
The takedown of RaidForums left a considerable power vacuum within the English-language cybercriminal community, with many of Raid’s members seeking alternative platforms. It is exactly within this context that pompompurin decided to create BreachForums, a platform with the ambition to replicate RaidForums’ success by maintaining very similar functionalities and looks.
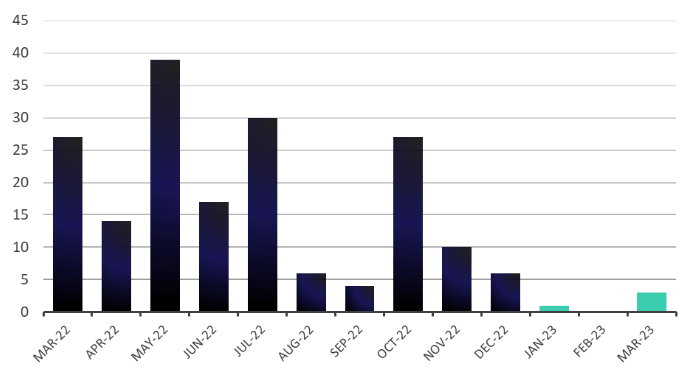
BreachForums officially launched in March 2022. Owing to its prominent members and associated cybercriminal activities, BreachForums quickly became the most reliable alternative to the now-defunct RaidForums, attracting much of its user base. In a relatively short amount of time, pompompurin managed to establish the new platform as the most prominent English-language cybercriminal community.
About pompompurin
Active in the cybercriminal community since at least October 2020, pompompurin was a member of RaidForums, where they earned a significant reputation for consistently sharing high-profile databases, data leaks, and access offerings. In November 2021, pompompurin gained widespread acclaim across the cybercriminal community when they successfully identified a vulnerability in an email server owned by the FBI and used it to send thousands of fake emails about a cybercrime investigation. Pompompurin then reached high prominence when they decided to create and administer BreachForums.
Cybercriminals React to the Arrest
Users of Russian-language cybercriminal forums were quick to read and discuss news about this arrest. Most of the commentary around this story blamed pompompurin’s poor operational security (OPSEC) measures, highlighting the technical mistakes that may have led to their arrest. Other users instead focused on pompompurin’s geographical location and the impact it may have had on the arrest. One user commented, “The first problem is his location. When you get involved with this stuff, it is very dangerous to be in the states.”
What Will Happen Next?
At the time of writing, it is not possible to access BreachForums. It is highly likely, although unconfirmed, that this relates to the arrest of this individual and that the FBI has seized infrastructure affiliated with pompompurin. We still don’t know whether this is a temporary downtime or whether we’re currently witnessing the final takedown of this platform. However, let’s use our intelligence skills to do a quick scenario forecasting and see how the situation would unfold in any of those two cases.
Scenario 1: Momentary Downtime
It is realistically possible that BreachForums’ downtime is momentary and that the platform will be back soon. However, if that were to be the case, forum users would likely be suspicious of any law enforcement infiltration into the platform. Law enforcement agencies have conducted this kind of operations in the past, where they operated a seized platform’s infrastructure with the purpose of collecting further intelligence. Reputation and credibility are arguably the most important features for any cybercriminal enterprise. If BreachForums’ reliability were to be affected by its founder’s arrest, it is likely that its users wouldn’t trust it enough to use it to publicize their activities in the future.
That said, we’re already observing BreachForum admins active on Russian-language cybercriminal forums claiming that the forum infrastructure in undergoing a migration and that BreachForums will come back online soon. According to one user, the current downtime is due to their attempts to “take extra consideration to not accidenly [sic] reveal any part of our infrastructure without something or someone scanning the internet 24/7 discovering the true hosts of our infra by chance.”
Scenario 2: Permanent Farewell
Another realistically possible scenario is that BreachForums downtime will be definitive. The arrest of its founder and main administrator, along with the likely seizure of documents and infrastructure, is likely to give law enforcement the opportunity to close this forum forever. Even if the forum remains operational, it is likely that it may no longer have its users’ trust after its founder’s arrest. When the FBI seized RaidForums, the login page for the forum remained operational for a short time, and many threat actors believed that law enforcement used the login page to harvest credentials. Therefore, it would likely be difficult for new owners of BreachForums to gain users’ trust and keep the forum operational.
Scenario 3: A New Forum from the Ashes
If BreachForums’ farewell turns out to be permanent, it is highly likely that new and existing English-language cybercriminal platforms will emerge in the short term (one to three months) to take its place. The cybercriminal community is notorious for its flexibility; when one prominent forum or marketplace gets taken down, a multitude of alternatives emerge soon after as contestants for that top spot. For example, BreachForums was created from the ashes of RaidForums, and Alphabay was created to replace Silk Road. This cycle has happened countless times in the past, and it is highly likely that this story holds no exceptions. Prominent users and admins of BreachForums are likely to be among the first to take this initiative in case of a prolonged downtime.
The Threat Remains High
The closure of BreachForums will likely result in English-speaking cybercriminals moving to underground dark web forums such as XSS and Exploit to leak large databases and engage in criminal discussions. While XSS and Exploit are primarily Russian-speaking, these forums have English-speaking sections with a large user base. The threat to enterprises is likely to remain high—threat actors will find other ways to leak data publicly. Other methods that threat actors may explore include leaking data on Telegram and IRC channels. Some threat actors have also used social media like Twitter to advertise data dumps. Therefore, enterprises should remain vigilant of the activity of threat actors on the clear and dark web.
Curious to see what will happen next? ReliaQuest leverages threat intelligence to support security operations, now with the added benefit of Digital Risk Protection. Click here for more details about ReliaQuest Threat Intel. To see how we’re harnessing Threat Intel to monitor the developments of BreachForums, request a demo here.
Update: March 21
The second scenario became a reality as the new administrator of BreachForums, Baphomet, released a statement on their website announcing that they were taking down BreachForums. Baphomet stated that they believed BreachForums to be compromised by law enforcement and that the site was no longer “safe” for users. The admin also said they would set up “another Telegram group” for those who wanted to follow the situation and that they planned on working with other competitor forum admins to create a new community with “the best features of Breached.”
The reaction in Russian-speaking cybercriminal forums was mixed. Some users openly welcomed new members into their forums, while others were concerned about an influx of low-level and unskilled cybercriminals joining their forums. The reaction from these forums suggests that many BreachForum users have begun using underground Russian forums as a temporary replacement, while Baphomet, or another user, likely create another English-speaking forum to replace BreachForums. Chatter will likely pick up over the coming days and weeks as more users migrate to other forums.