Key Points
Search engine optimization (SEO) poisoning helps cyber-threat actors entice internet users to visit malicious webpages, download malware, and, often, unwittingly provide initial access to a larger network. That initial access can be sold to other threat actors, including ransomware operators and other cybercriminals.
Threat actors perform SEO poisoning by manipulating search-engine algorithms, causing malicious websites to ascend lists of search results. Internet users then click on the links, mistakenly perceiving the sites as legitimate because they have been designed that way.
ReliaQuest observed a 10% increase in SEO poisoning-related malware detections each month from August 2023 to January 2024, resulting in an overall 60% increase over the six-month analysis period. Malware-as-a-service toolkits are making SEO poisoning relatively easy, and popular. The success of attacks is also boosted by attackers’ exploitation of trending topics, the perception of a site’s legitimacy, and certain psychological factors.
Attacks on the US healthcare and legal sectors are especially common. However, SEO poisoning poses a significant risk of cyber attack to businesses of all sizes and sectors, if employees cannot discern between a malicious search result and a legitimate one.
ReliaQuest is skilled at finding evidence of SEO poisoning in customer environments. In this report we share key indicators pulled from our hunts, and targeted recommendations for a proactive approach at defense.
Search engines, such as Google and Bing, use SEO techniques to determine which content is most likely to be pertinent to a user, presenting those results at the top of the list. Threat actors understand how search engines rank content, and can manipulate search algorithms to boost their own websites’ search rankings. This increases their ability to lure unsuspecting users to interact with malicious content.
Intensifying the threat is malware-as-a-service (MaaS), such as “Solarmarker” and “Gootloader,” which use SEO poisoning to achieve initial access to larger networks. This invites greater compromise that can end in data exfiltration and extortion. MaaS has increased the ease with which threat actors can carry out their deceptive tactics, leading to a significant uptick in these attacks: Over the past six months, ReliaQuest observed a 10% increase in SEO poisoning-related malware detections, month over month.
In our experience hunting for indicators of this threat, we found that analyzing a combination of forward proxy logging and endpoint telemetry can reveal likely SEO poisoning within a given environment. To help security defenders perform their own hunts and—ultimately—remove malware and remediate any subsequent compromise, this report explains SEO poisoning’s intricacies, shows its effectiveness in a case study, and offers defense recommendations.
How Does SEO Poisoning Work?
Techniques
SEO poisoning is achieved through various techniques to undermine the integrity of search-engine results. The use of link farms and keyword stuffing stand out as the most prevalent we have observed in real-world incidents. They are specifically designed to exploit search engines’ algorithms, which aim to prioritize websites based on factors like relevance, content quality, and site authority.
Link Farms
When ranking content, search engines consider the number of site visits to determine its relevance and authority. Essentially, the more a website is linked to, the higher it appears in a search result. Link farms are networks of websites that exist solely to increase the number of visits. Threat actors create link farms to trick search engines into perceiving a site as relevant and legitimate.
Keyword Stuffing
Search engines also scan content for keywords, to gauge relevance to a search topic. Threat actors perform keyword stuffing to boost the ranking of a site, by loading a broad range of keywords and phrases into the site’s content. This technique can be enhanced if the threat actor uses scripts to create auto-generated content: pages filled with snippets of relevant results from other sources, likely to match a search query. Search engines may initially rank these pages highly, fooled by the density of keywords and the likelihood of an exact match.

Figure 1*: Example of auto-generated content created for keyword stuffing, with underlining indicating three legitimate snippets from respective sources, now aggregated to maximize the chance of matching a given search term (Source: Zscaler)*
Attack Chain
SEO poisoning typically involves several stages:
1. Research: A threat actor analyzes search trends to identify popular keywords and topics, such as related to breaking news or seasonal events. This research empowers the threat actor to make their malicious content relevant to a popular subject, and capture the interest of a large audience.
2. Setup: The threat actor builds their malicious content by either hijacking a legitimate site or creating a counterfeit site that mimics a legitimate one. In either case, the result is searchable content that seems benign but conceals harmful content.
3. Optimization: The threat actor now uses advanced SEO techniques, such as those described above, to trick search engines and rapidly elevate their site’s ranking.
4. Distribution: Once the malicious site achieves a high search ranking, it becomes a trap for users of search engines. The user enters a targeted keyword into the search field and sees the malicious site at or near the top of the results that appear. They are likely to trust the site because it seems legitimate, and click the link that leads them to visit it. On the site, the user will be prompted to download the disguised malware and, potentially, grant initial access to their device.
5. Monetization: The threat actor’s ultimate objective is to profit from their activity, and they do this primarily by selling the means to access a compromised user workstation. Access brokers are willing to buy this access, and can resell it to other cybercriminals, including ransomware operators
Why Is SEO Poisoning So Successful?
SEO poisoning is often more effective than traditional social engineering tactics, like phishing, in aiding initial access to a host. With SEO poisoning, there are more potential victims: Anyone entering the right search terms can be led to poisoned results. In addition, search-engine users are more likely to interact with, and download, malicious content, because they are actively seeking information rather than receiving unsolicited communications.
Certain psychological factors also benefit SEO poisoning:
Implicit trust in search-engine rankings: Users’ confidence in high-ranking search results makes them more susceptible to clicking on, and engaging with, malicious sites that appear at the top.
Perceived legitimacy through association: When a user sees a malicious site ranked amid legitimate ones, the malicious site gains an unwarranted legitimacy, and they are less likely to question its credibility.
Navigation by choice: The voluntary action of clicking on a search result lends a deceptive sense of security; trusting their own judgment, the user often does not realize they are being manipulated.
What Does It Look Like?
To bring this concept to life, let’s consider a real-world example that demonstrates the efficacy of SEO poisoning. A Google search for “army award ceremony protocol pdf” (see Figure 2) might lead users to a counterfeit PDF download page (see Figure 3). Designed to look authentic, the page actually contains an information stealer called Solarmarker. If the visitor interacts with elements of the page, Solarmarker downloads to the user’s device.
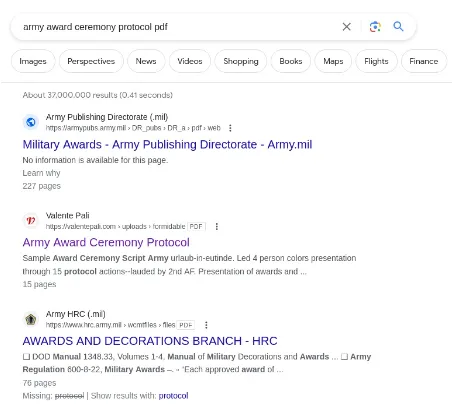
Figure 2: Google results showing malicious PDF download page in second position (Source: Google)
In that example, the success of the SEO poisoning is attributed to the implicit trust users have in top search results, and the perception of legitimacy through association: The malicious link appears amid listings of legitimate military websites. This placement likely bolsters trust in the poisoned link and increases the chances that users searching for official documents will click it.
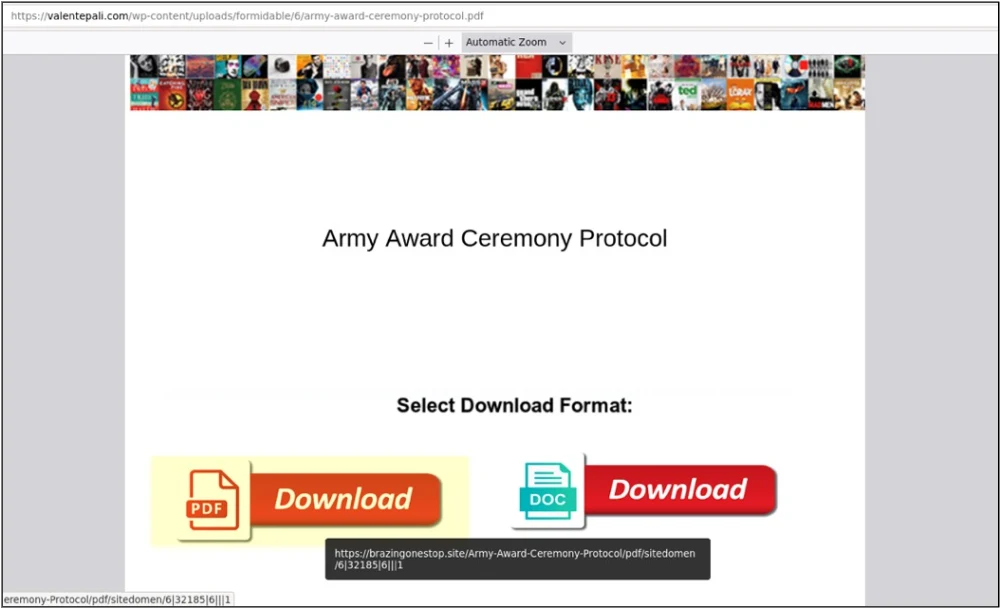
Figure 3*: The malicious PDF download page (Source: Google)*
Case Study: Gootloader via SEO Poisoning
In May 2023, the ReliaQuest Threat Hunting Team responded to a “Gootloader” malware infection, and found that it had begun with SEO poisoning, allowing initial access to a customer’s environment
How the Deception Worked
The user had performed a search, “what is the difference between legal ruled and wide ruled paper?” One of the top search results led the user to a seemingly benign forum. That page featured a comment from an alleged forum user, inviting the visitor to download a PDF that would answer their question.
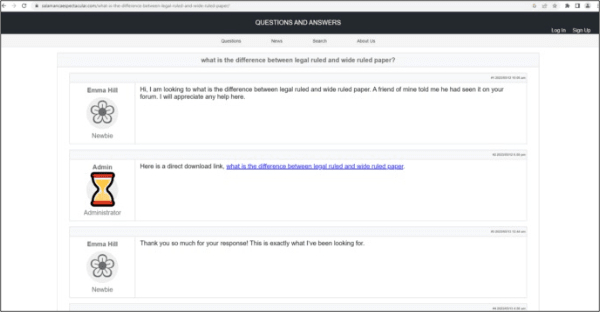
Figure 4*: Malicious webpage posing as a forum and containing a PDF download link*
The HTML source code of the page revealed the malicious download link. Such simple deceptiveness is the hallmark of SEO poisoning: Having landed on the page, the user was just one click away from downloading a ZIP file that harbored the Gootloader malware.
Figure 5*: HTML source code of malicious page*
Inside the downloaded ZIP file was a JavaScript-based payload, whose filename corresponded with the user’s search query: what_is_the_difference_between_legal_ruled_and_wide_ruled_paper_29094.js. When a user interacts with a JavaScript file, by default, Windows executes it via Windows Script Host (wscript.exe), leading to execution of the first-stage malware.
Once executed, the malware established persistence and initiated command-and-control (C2), preparing to deploy a second-stage payload: in this instance, the “SystemBC” remote-access trojan (RAT). The RAT would enable attackers to remotely access and extract credentials from the compromised environment.
The initial access the attackers gained to this device eventually led to lateral movement to a server, the dumping of credentials from memory, and an FTP connection being established for exfiltration. This occurred before the affected devices were isolated from the network and account access was disabled, removing the attackers’ access to the environment.
Hunting for SEO Poisoning
To effectively hunt for malware linked to SEO poisoning in our customers’ environments, our approach involves collecting two data types:
Search-engine queries, from forward proxy logs
File download event, from endpoint telemetry
We have observed that the name of a downloaded file almost always mirrors the search terms in the user’s query. Presumably this is done to reinforce the user’s belief that they the download matches exactly what they are looking for.
Because the similarity is such a strong indicator, we focus on looking for search terms that correspond with downloaded files’ names, particularly files with potentially malicious extensions (e.g., .exe, .zip). For example, if a user searched for “declaration of independence july 4th 1776 pdf” and subsequently downloaded a file named declaration-of-independence-july-4th-1776-pdf.exe, this is a strong indicator of successful SEO poisoning.
Search Engine Queries
Our methodology begins with gathering forward proxy events with “full URL” data (including the path and parameters of the URI) of traffic to the “search” endpoints for various search engines (e.g., google.com/search?q=my+search+term). We export this data into CSV files to analyze offline, as most SIEM tools do not natively support the algorithm that would allow us to compare similarities in our two data types.
File Download Data
File downloads are a more difficult data point and can come from multiple sources. The strongest data sources represent a file write explicitly—Sysmon Event ID 11 or data from an EDR, for example. For devices without dedicated file write logging, we can infer a file was downloaded: We look for the execution of a potential payload through (more commonly logged) process-creation events whose command lines refer to a file in the Downloads folder. We then export this data as another component in our offline analysis.
Comparison of Data
Once data has been collected, we employ a Python script to remove duplicates, and extract the points of interest: filenames, search terms, and timestamps for both. We compare the search terms with download filenames within a specific timeframe, typically ten minutes, to identify any direct correlations. We use the Jaccard Index to score the matches, enabling us to quantify the overlap between the search terms and filenames; a higher score indicates a greater likelihood of SEO poisoning.
We look for instances of at least three words matching between the search terms and filenames. If the match ratio meets or exceeds a certain threshold, we record the search terms, filenames, file URL, and the Jaccard Index score.
For example, the following results of such analysis are shown for a simulated environment with mock data; they show that malware purporting to be a severance agreement file was downloaded via SEO poisoning after a relevant Bing search.
Search time: 2023-11-16 12:18:41+00:00
Search URL:
Extracted search terms: Severance agreement offer letter
Filename: Severance_agreement_in_offer_letter_53561.zip
File time: 2023-11-16 12:22:47+00:00
File URL:
File path: C:\Users\vagrant\Downloads\Severance_agreement_in_offer_letter_53561.zip
Score: 96
Recommendations and Best Practices
SEO poisoning poses an enduring cyber threat, and the US healthcare and legal sectors are frequent targets. Our focus at ReliaQuest is mitigating the malware used in combination with this technique; in observing the continued success of Gootloader, Solarmarker, and other malware spread through SEO poisoning, it has become clear that the real danger lies not just in the initial deception but in the subsequent “downstream” malware infections that can compromise systems.
There are limited options for mitigating SEO poisoning itself: Either the poisoned search result needs to be deprioritized or removed (by the search engine), or the domain must be categorized as malicious more quickly (at the proxy/DNS level, or via external threat intelligence). In most cases, SEO poisoning cannot be confirmed as the source of a file solely by the logs; it requires looking at the content of the page that was presented. The difficulty of mitigation makes it almost certain that SEO poisoning will continue to be used effectively into the mid-term future (three months to one year).
The recommendations below concentrate on enhancing detection capabilities and implementing preventive measures, focusing on the delivered malware. These strategies are not only vital for current defense; they also form the backbone of a resilient posture against future threats that may arise as SEO poisoning techniques evolve. The following actions are designed to protect our customers from the downstream effects of SEO poisoning, ensuring that their digital environments remain secure.
Enable File Extension Display
By default, Windows hides file extensions from users, which can help prevent non-technically savvy users from accidentally renaming a file and rendering it unopenable. But this setting aids malware operators by concealing the nature of malicious files. To mitigate the risk of users unknowingly executing those files, enable the display of file extensions within Windows operating systems.
This helps users identify potentially harmful files masquerading as innocuous, such as a malware executable (.exe) disguised as a PDF file. Implementing a Group Policy across your organization can ensure that this setting is consistently applied to all users.
Change Default Script Executor to Notepad
Altering the default program that executes script files, specifically JS (JavaScript) and VBS (Visual Basic Script) files, can significantly reduce the risk of script-based malware running on a user’s system. Setting Notepad as the default application for these file types means any attempt to execute the scripts will result in the code being displayed as a text file rather than executed.
This prevents the automatic execution of potentially malicious scripts, offering an additional layer of scrutiny. Use a Group Policy to instruct Notepad to open JS and VBS files by default.
Implementing these two recommendations can serve as part of a broader defense-in-depth strategy, enhancing your organization’s resilience against SEO poisoning and other cyber threats that rely on deceiving users into executing harmful code.