This year’s SANS Cyber Threat Intelligence (CTI) Summit took place on January 30–31, in National Landing, Virginia. The event is now in its 11th year, and I’ve been fortunate to be involved since its inception. It was also our first in-person event in several years, so it was wonderful to reconnect with the threat-intelligence community. We also had a virtual track to accommodate people from across the globe, and we had attendees from more than 100 countries! There were 36 publicly available talks, and I will recap a handful of them in this blog.
CTI Summit Talk Teaser
As mentioned above, there were numerous talks and I’m able to highlight just a few of them. So, I’m focusing on presentations that are also relevant to the teams that Threat Intelligence Analysts collaborate with, such as Incident Responders and Threat Hunters. Choosing only five talks that fit this bill was tricky. But don’t worry, you’ll find details on how to access all the publicly available talks later in the blog.
Chris Sanders: “Deconstructing the Analyst Mindset.” Chris was our keynote speaker, and his talk applies to anyone who performs analysis—intel analysts, threat hunters, and incident response analysts. Chris’s concept of the importance of the “opening move” during an investigation resonated with me. Where you start impacts the rest of the investigation: begin in the right place. Another great quote: “A question well-stated is a problem half-solved.” If you follow Chris on Twitter, you can take part in his weekly “Investigation Scenario.” He posts a scenario every Tuesday and then shares his thoughts on Friday.
John Doyle: “Developing The Analyst—Creating Career Roadmaps for Intelligently Progressing in CTI.” John’s talk applies to all of us: career planning is something we must actively engage in. You can take his guidance and use it for any role in cybersecurity. His suggestions on finding champions and mentors are right on the mark. Another “pro tip” of John’s that I’d recommend is to have a “brag sheet.” Keeping track of accomplishments throughout the year will make performance reviews and promotion justifications much easier.
John Grim: “The Report Writing Grimoire.” Over the years, we have had some great presentations on writing, and John’s talk continued the tradition. If we can’t effectively deliver and communicate the results of our analysis, then what purpose does it serve? We have failed. John aligns reporting writing to the Intelligence Cycle, with practical examples you can implement. I also recommend checking out these talks for more excellent writing content: Lenny Zeltser’s “Hack the Reader” and Christian Paredes’ “Pen-To-Paper and The Finished Report.”
Joseliyo Sánchez and Pedro Drimel: “Practical CTI Analysis Over 2022 ITW Linux Implants: Extending Detection Over Blind Spots.” We had several great case study presentations at this year’s conference, but I selected Joseliyo and Pedro’s because it focused on Linux, which doesn’t feature as prominently on the research circuit. The Linux attack surface is an under-represented topic, and you likely have more Linux in the environment than you realize. Joseliyo and Pedro did an excellent job setting up Windows analogies for those who weren’t as familiar with the Linux side of the house, with conclusions to help you prioritize defending Linux estates.
Sydney Jones: “How to Use CTI No Matter the Size of Your Organization.” Sydney gave a helpful program-level talk that laid out the inputs, outputs, and focus areas for CTI teams of various sizes. She takes us from a one-person team to a team of 10+. Security leaders responsible for CTI can use her talk to gauge where their team is today and look for missed opportunities. Leaders responsible for new intelligence functions can use it to help build their programs.
Where to Find SANS CTI Summit Content
There are several ways to get your hands on CTI Summit content. First, you can get the slides from the CTI Summit Access Page, requiring you to log in with your SANS Portal Account. Once authenticated, you can download a PDF of the presentation.
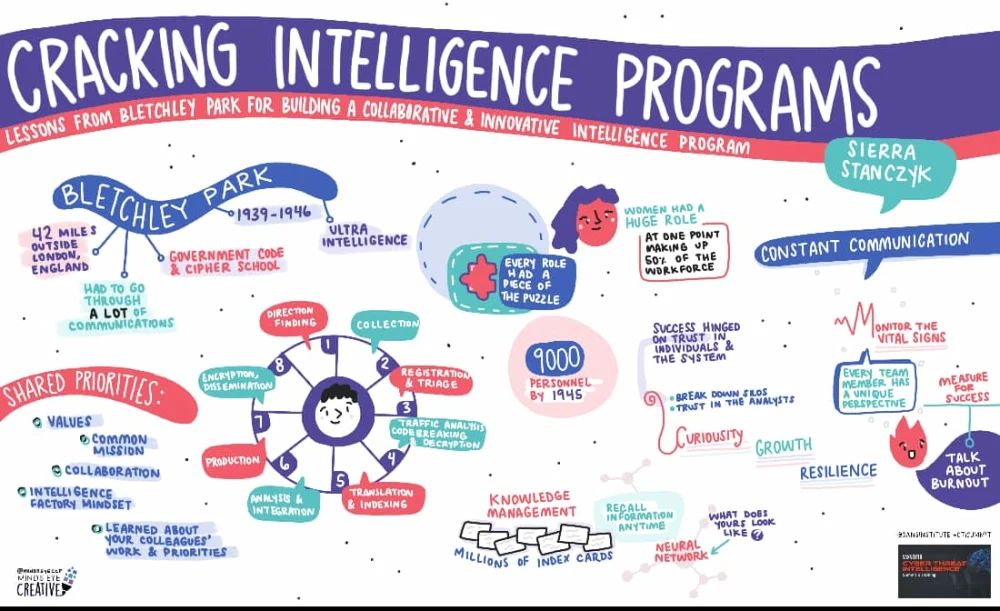
Second, Ashton Rodenhiser continues to create fantastic graphic recordings of our CTI Summit presentations, like this one from Sierra Stanczyk.
Finally, you can view talks on the SANS Digital Forensics and Incident Response YouTube channel. SANS will release recordings over the following months. There aren’t any talks available yet, but subscribe to the channel and turn on notifications to be ready for when they are. In the meantime, you can watch archives of previous CTI Summit talks like this one CIA veteran Carmen Medina did several years ago: “Survival Heuristics: My Favorite Techniques for Avoiding Intelligence Traps.”
I want to thank Jennifer Santiago, Katie Nickels, Lillian Teng, and Rebekah Brown for all the behind-the-scenes work to make this happen. I would also like to thank the CTI Summit Advisory Board members: Gert-Jan Bruggink, Kristen Dennesen, Lina Lau, Ryan Kovar, Samara Williams, and Scott Roberts. Finally, I want to express appreciation for all our speakers and everyone that attended in person and virtually.

Where to Find ReliaQuest Threat Intel Content
If the type of content from CTI Summit interests you, check out our weekly ReliaQuest podcast—ShadowTalk—where we talk about the latest cybersecurity news related to security operations and threat intelligence. You can find it on all the podcasting platforms. Finally, to see how ReliaQuest leverages threat intelligence to support security operations, click here for more details.





