2022 was predictably unpredictable for the Russian-language cybercrime scene. This underground world continued to grow and evolve, and many events that unfolded in 2021 made an impact in 2022, as expected. The 2021 ransomware-content ban on top cybercriminal forums spurred many creative workarounds to the restrictions in 2022. Infighting on prominent underground platforms and a takeover of the carding-focused forum Verified during 2021 led to far fewer posts from wary users in 2022.
There were some surprises. Who could have foreseen repeated law-enforcement operations from Russian security agencies targeting Russia-based cybercriminals? This shattered the long-held belief that Russia-based threat actors were safe if they avoided attacking their own backyard. Let’s take a look at three of the most noteworthy and surprising trends or developments we observed in 2022.
Trend 1: Forum Users Take a Stand on Russia–Ukraine War
Russia’s invasion of Ukraine in February 2022 sent waves through the cybercrime community that have continued as the war has worn on. This has occurred even as established platforms have strongly discouraged discussions about the conflict. Several major Russian-language forums’ regulations prohibit political content and racist or xenophobic insults, limiting the potential for cybercriminal discussions about the war in Ukraine.
Users have mostly complied. Forum members have spoken up about threads containing anti-Ukrainian slurs. And site moderators have closed unsuitable threads and banned rule-breakers. One forum user, who probably tried to initiate discussion about the conflict, requested that their own thread be closed, writing: “I only asked a question, to which I did not expect to find such violent answers. I apologize to anyone who felt offended.” Other threads seeking to generate debate went entirely unanswered.

The Rise of Two Platforms
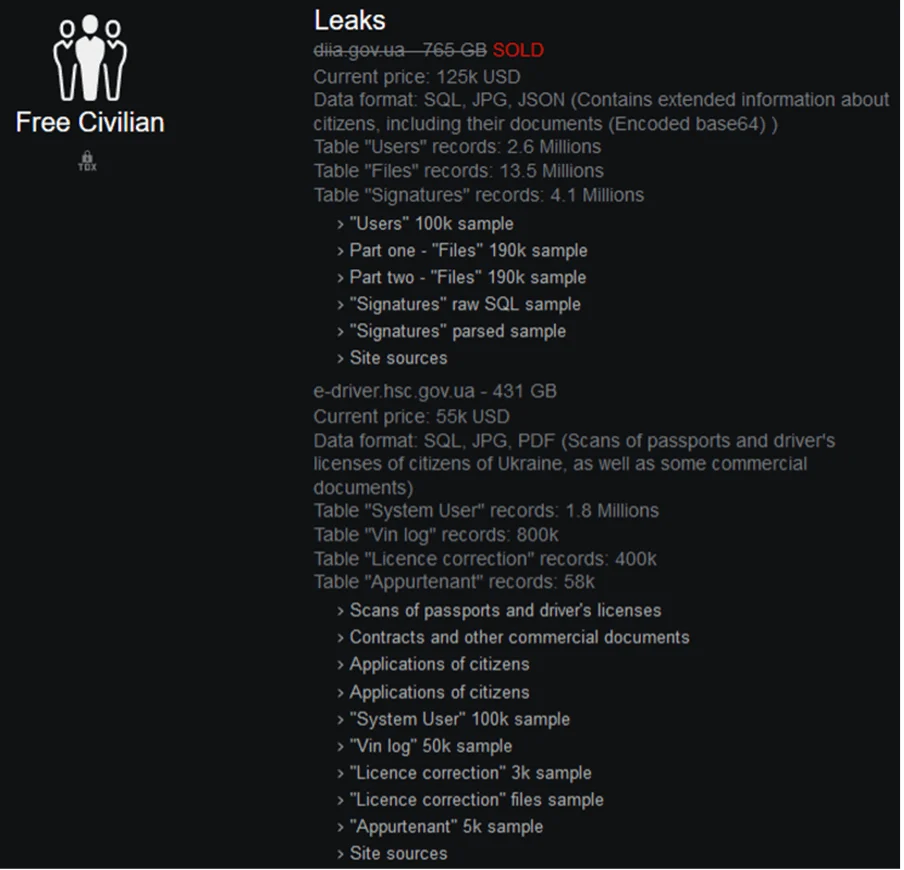
Also in the context of the war, two opposing cybercriminal platforms emerged. The first came in January 2022: the pro-Russia Free Civilian data-leak website, advertising “personal data of citizens of Ukraine” and “data from several government departments” in Ukraine. Given the exclusive targeting of Ukraine-based victims, it’s highly likely that the site’s administrator is geopolitically motivated, but so far there’s no indication of how or why the data is acquired, or whether it’s legitimate.
We couldn’t find much information about Free Civilian on other cybercriminal sites either. Free Civilian hasn’t been updated since the early days of the war. Several promised leaks were never published, and the leak page’s content hasn’t changed in months.
In May 2022, the second platform appeared: a pro-Ukraine Russian-language forum called DumpForums. That site allows its users to share leaked data plus probiv (information services) and other offerings intended to stymie Russian and Belarusian military action against Ukraine. DumpForums users have shared data from several Russia-based governmental and private institutions, including the FSB, Gazprom, Rostelecom, Roskomnadzor, Sberbank, and THS-Energo. Some site members have advertised probiv services targeting Russian and Belarusian government agencies, financial institutions, and mobile network carriers, plus the register of Russia-based individuals convicted of illegally possessing weapons.
In June 2022, DumpForums’ administrator announced that a forum member had hacked and defaced the Russian Ministry of Construction, Housing, and Communal Services’ website and was holding the site’s data ransom for USD 15,000. Despite its strong pro-Ukrainian intent, though, the forum hasn’t significantly impacted the Russian-language cybercrime scene. The site been rarely discussed on other forums and has failed to become noticeably bigger.
Anti-Anglo Sentiment
In a less direct consequence of the war, hostility against English speakers on Russian-language forums seems to have intensified. For years, Russian cybercriminals had generally distrusted “foreigners”—many of their forum posts demanded to transact only with Russian speakers—but a substantial proportion was always willing to work with English speakers, respecting their technical knowledge. But more and more anti-Western posts appeared on prestigious Russian-language forums throughout 2022—prompted by the West’s open support for Ukraine or anti-Russia sanctions (or both).
We’ve seen threat actors calling for “useless” English speakers to receive automatic bans from cybercriminal platforms, reporting they have “suffered for many years from English-speaking liars,” and alleging that American cybercriminals tend to change terms of contracts, alter prices, and sue for discrepancy, displaying a complete lack of morality, dignity, or honor. Even in the face of such sentiments, though, English was still common across high-profile Russian-language forums at the end of 2022. Many Russian-speaking threat actors probably see the need for trade partners as enough incentive to bypass their xenophobia.
Trend 2: Legitimate Software as a Secret Weapon
Cybercriminals have advertised non-criminal software before 2022, but last year we observed an increase in both advertisement threads and tools up for sale. This included a range of system security tools, adversary-simulation or penetration-testing tools, and security scanners. This buying and selling legitimate software reflects deep research: Adversaries are carrying out reconnaissance on their targets, discovering how to move laterally within systems and learning how to evade defenses, allowing more streamlined and effective attacks.
What’s for Sale?
System security solutions, scanners, and pen-testing tools are useful not just for reconnaissance but also the offensive stage of an attack. With them, the attacker siphons knowledge about a system’s security and, hopefully, what their victim looks like. In this sense, threat actors aren’t going after just the lowest-hanging fruit (companies with the weakest security systems). No company should let its guard down, even if its security systems are better than average.
Throughout 2022, we saw increasingly frequent threads advertising tools like the endpoint security solution VMware Carbon Black, the web application security scanner Invicti Professional (Netsparker), and the enterprise security information and event management (SIEM) product IBM QRadar—often the original licensed versions of the software.

Legitimate attack-simulation or pen-testing tools are also popular; they negate the need to create custom software to plan or wage attacks. And they may help avoid system detections, even during malicious activity. We’ve seen threads buying, selling, or even freely sharing the latest versions of pen-testing or red-teaming tools like Cobalt Strike, Core Impact, Brute Ratel, and Metasploit Pro; asking prices sometimes stretch into the thousands of dollars.
Security scanners were another hot commodity on forums in 2022. Companies typically use scanners to highlight vulnerabilities and weaknesses in their systems; cybercriminals use them to work out where and how to carry out targeted attacks. We found advertisements for a lifetime license for the Rapid7 web application security testing tool AppSpider, the Burp Bounty scan check builder (unspecified license length), and a two-year license to the vulnerability scanner Nexpose.

Trend 3: Zero-Day Trade Boost (Not Just for Nation-States)
Threads posted for the trade of zero-days are now very common on top-level Russian-language cybercriminal forums, as the zero-day exploit market seems to have blossomed. Before 2022, interested buyers were fewer and not necessarily credible, but now established buyers are offering hundreds of thousands—or even millions—of US dollars for zero-days.
On one prominent forum in July 2022, a user advertised an alleged remote code execution (RCE) exploit for a Chrome browser vulnerability. They set the price at USD 2 million, and later reported a sale. Although such fees seem hefty, they align with the current context: Whatever legitimate bug bounty programs offer, cybercriminals must offer more to compete, given the risks of jail time and added requirements of illicit activity (such as money laundering).

There are other signs of credibility (on top of exploit vendors marking their high-value listings as sold). Zero-day buyers are making very large forum deposits—sometimes over USD 1 million. These users often pay for their threads to be pinned in the forums’ Virusology/Malware trade sections, meaning that they will always be visible on the front page. Some of the zero-day buyers with large forum deposits offered up to USD 10 million for the right vulnerability or exploit in 2022.
No Deposit? No Problem
Amid all the heavy hitters dropping large sums for exploits, there is a formidable group of would-be purchasers with no clear forum deposits, seeking zero-day exploits for sometimes millions of US dollars on top cybercrime platforms. Even without deposits, they may still be credible threat actors: Many of them offer to work via the forum escrow systems. Regardless, exploit buyers without a deposit are less likely to receive responses to their buying threads, and are more likely to be banned.
Some exploit buyers may not want to make a deposit, or they can’t afford to before a purchase—they’d lose a commission and other fees if they were to then withdraw their deposit without a successful purchase. This is less of a problem for smaller deposits, where fees may only amount to tens of dollars. But with deposits in the hundreds of thousands or millions, the fees can be up to tens of thousands of dollars. Even if a buyer can afford a million dollars for a zero-day exploit, their pockets might not be big enough (or they might not have the financial savvy) to manage the fees. As exploit buyers increase their profits and reputation, they can more easily afford to make a forum deposit.
Zero-Clicks on the Rise
In 2022 the number of users seeking to trade zero-click exploits also went up. These exploits are particularly dangerous, because there are no means of defense. The exploits require no action on the part of the victim, such as opening an email or clicking a link. This type of highly effective exploit is used by government security services, such as the US National Security Agency, and private security companies, such as Israel’s NSO Group.
Being very difficult to develop, zero-click exploits typically warrant a high price, which used to render them out of reach for low-budget cybercriminals. But as budgets have expanded, so has cybercriminals’ desire for these exploits. Vendors also seem to have noticed a market demand for zero-click exploits, prompting them to begin noting this capability in their exploits. Other exploit vendors have begun specifying when their exploit does require victim action, when selling “one-click” or “n-click” exploits.
CVE Hunting
2022 also saw the continued trend of users seeking exploits for specific vulnerabilities, as tracked by CVE numbers. We detected a certain level of confidence that newly discovered vulnerabilities will not be universally patched. When making requests for particular CVEs, buyers tend to provide little information, likely to avoid giving away their targeting scope. In addition to seeking full exploits for known vulnerabilities, buyers also offered to purchase “raw” proofs of concept (PoCs), which they would then likely turn into a working exploit themselves.

Conclusion
These major trends from 2022 exemplify the volatility of the Russian-language cybercrime scene. Russia’s full-scale invasion of Ukraine in February 2022 came as a surprise to many, accompanied by threat-actor blowback. And the trade of legitimate software and zero-day exploits or vulnerabilities both really skyrocketed, for no neatly explainable reasons. Who knows which other commodities—regularly but quietly traded on cybercriminal platforms for years—may explode in the coming months?
Two things are almost guaranteed in 2023. 1) Cyber criminals will continue to grapple with the war’s consequences, especially if a weakened Russian economy lures more people into making money through cybercrime. 2) Ransomware-related content will dominate cybercriminal platforms—bans or no bans; new operators join the ransomware game all the time, and their consistent success offers no reason to stop targeting companies, for a bonanza or a mere morsel.




