As the new year has reached the end of its first quarter, it’s time for us to go back and take a look at all the most important ransomware-related events that happened during Q1 2022. The beginning of the year has shown that ransomware gangs have remained motivated—despite increased pressure from law enforcement—but we have observed a drop in activity compared to the previous quarter.
Despite a lower level of activity, there were many noteworthy stories in this quarter, including the “Conti” chat leaks, groups pretending to be ransomware, and a shift in targeting that puts medium-sized organizations at risk. The war between Russia and Ukraine has also led to many conflicts for ransomware groups, some of which decided to show support for Russia, while others are doing everything they can to distance themselves from the topic.
In this blog, we will cover some of the key stories that happened in the ransomware world between 01 Jan – 31 Mar 2022, and we will discuss how recent events are likely to affect the next quarter (Q2 2022).
KEY RANSOMWARE STORIES IN Q1 2022
The War in Ukraine – Taking Sides
When discussing ransomware groups in 2022, it is important to also talk about the external factors that may affect the operations of these groups. Most high-profile ransomware gangs are known to operate from the Commonwealth of Independent States (CIS) region, with many affiliates from Russia and Ukraine. The recent war between the two countries has likely put many of these ransomware gangs in an uncomfortable position, and many groups have likely felt the need to “pick a side”.
The Conti ransomware group was one of the first groups to speak out, announcing its “full support” for the Russian government, and warning that any attacks against Russia will result in retaliation using “all [our] possible sources”. This statement was later changed to retract some of the stronger language. Another ransomware group that chose to support Russia was the “STORMOUS” group, who used similar language to Conti. The extortion group “CoomingProject” also posted a message on its Telegram channel saying that it would support Russia against cyber attacks.
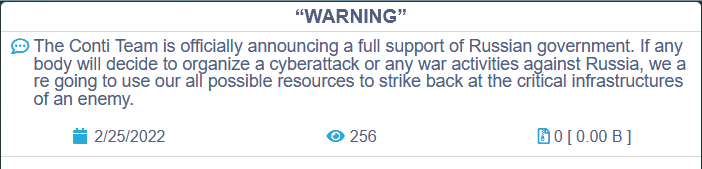
Conti Initial Statement on Conti.news
These statements did not come without consequences. Shortly after Conti expressed their support for Russia, a security researcher from Ukraine, in retaliation, exposed internal communications from the Conti group, containing more than 60,000 messages allegedly taken from the backend of a Jabber server. These chats revealed how the group worked, who were their leaders, how they handled ransom negotiations, and more. You can see our full analysis of the Conti chat by reading our recent blog.
One ransomware group who surprisingly took another route was “LockBit 2.0”, who released a statement saying that the group had members worldwide, including Russians and Ukrainians, and LockBit would “not engage in any international conflicts” as it was “apolitical”. LockBit likely understood that taking a side in this matter could result in internal conflicts, unwanted attention, and possibly even retaliation, like we observed with Conti.
Ransomware or not?
Another group who came on the scene and grabbed many headlines in Q1 2022 was “Lapsus$”. Like LockBit, Lapsus$ claimed to be an apolitical group who was only interested in making a profit. In its first attacks, Lapsus$ defaced the website of victims and said “you have suffered a ransomware attack” (translated from Portuguese). The group also claimed to have exfiltrated data from victims and created a Telegram channel where it would proceed to publicly advertise its attacks and leakages.
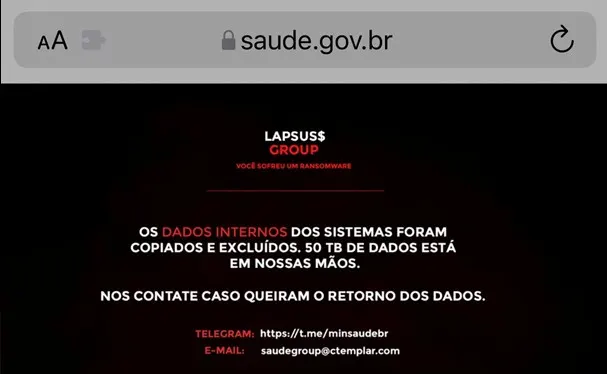
Lapsus$ defacement of the Ministry of Health of Brazil
The group also made many large claims, such as stealing 50TB from the Ministry of Health of Brazil, 1TB of data from Nvidia, and more. However, as the group began gaining more popularity, their claims began to be questioned. For example, the group leaked an 18.8GB file for Nvidia, but the leakage was small compared to the claimed 1TB of data. In fact, Lapsus$ operators became so frustrated from users asking for the Nvidia “part 2” breach that it became a rule in their Telegram to “stop asking about Nvidia”.
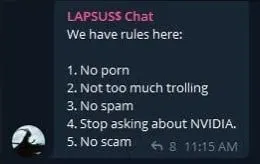
Lapsus$ rules in their second Telegram Channel (saudechat)
While Lapsus$ claimed to have used ransomware in its early attacks, there was no evidence of the group ever using any encrypting malware in its attacks. In a recent report released by Microsoft, it was revealed that the group used stolen credentials and social engineering techniques to gain access to victims, which was followed by attempts to exfiltrate or destroy data. Lapsus$ was also observed naming companies who experienced connectivity issues on its Telegram channel, such as Discord and BleepingComputer, suggesting that the group was responsible for the sites being down, despite there being no evidence of any attacks.
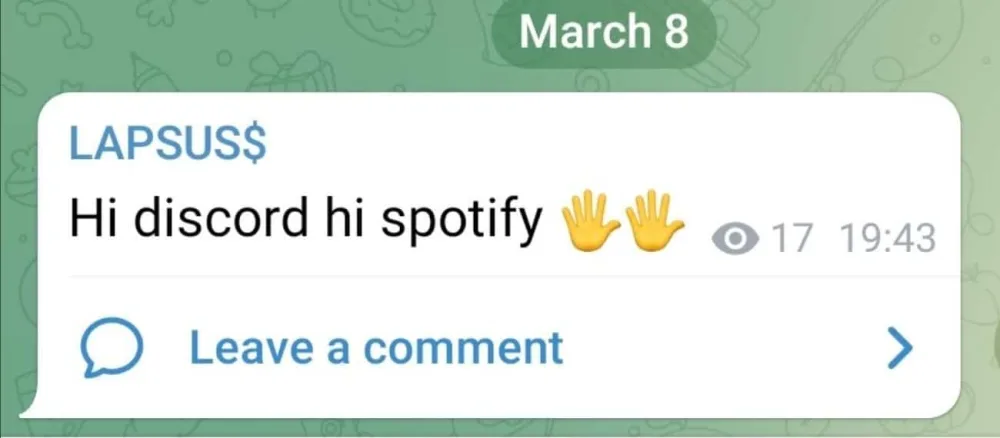
Lapsus$ names companies experience connectivity issues to its Telegram
Although Lapsus$ is certainly a threat group who should be taken seriously, they are also a good example of how some threat actors may exaggerate their attacks to make them appear bigger or more impactful than they actually are. It is likely that Lapsus$ claimed to be a ransomware group to draw attention from the media and put further pressures on victims. However, the group appears to be an extortion group similar to “ShinyHunters”, “Karakurt Hacking Team”, “Marketo”, and “CoomingProject”. Extortion groups steal files and attempt to extort victims, but do not encrypt any data.#
Shift in Targeting
Another topic of discussion in Q1 2022 is a shift in targeting that has been recently observed. Since double-extortion ransomware attacks became popular in early 2020, most ransomware groups switched to “big-game hunting”, where threat actors primarily target high-value enterprises or those that provide critical services. The advantage of big game hunting is that ransomware gangs can make extortionately high ransom demands, as these organizations typically face a heightened threat from data loss and exposure, and they can afford to make larger ransom payments.
In February 2022, the Cybersecurity & Infrastructure Security Agency (CISA) released an alert on the trends of ransomware over the past year, which warned that ransomware gangs are shifting away from big game hunting. According to CISA, the FBI reported that many ransomware groups are now targeting mid-sized organizations in the United States. The Australian Cyber Security Centre (ACSC) and the National Cyber Security Centre (NCSC) in the United Kingdom also reported that organizations in the UK and Australia are facing threats from ransomware targeting organizations of all sizes.
While big game hunting can result in the highest payouts for ransomware groups, it also comes with many risks. As we have seen with attacks such as the Colonial Pipeline (by DarkSide), JBS (REvil), and Kaseya (REvil), attacks against high-profile targets attract the attention of law enforcement and the media. Both DarkSide and REvil seized operations shortly after launching these attacks, which was likely due to heightened pressure from law enforcement agencies. REvil members were later reported to have been arrested in January 2022 in Russia. By avoiding attacks that draw too much attention, ransomware groups can guarantee longer longevity and less risk to operators and affiliates.
ANALYSIS OF Q1 RANSOMWARE VICTIMS
In this quarter, ransomware continued to be one of the biggest threats to organizations worldwide. Data-leakage sites (DLSs) have remained highly active, and we observed the creation of many new ransomware groups in Q1 2022. At ReliaQuest, we monitor the data-leakage website of more than 70 ransomware gangs daily, but only 31 of the ransomware groups data-leak sites remain active at the time of writing. We also monitor data-leak sites from extortion groups like “CoomingProject” and Lapsus$; however, these are excluded from the analysis presented in this blog.
ReliaQuest has been monitoring ransomware sites since the creation of data-leak sites, and we have observed more than 4,600 organizations being named to these sites since 2019. In this past quarter, we observed 582 organizations being named on ransomware leak sites, a decrease of 25.3% compared to Q4 2021. This decrease was caused by a lower number of victims posted to data-leak sites of large ransomware gangs. For example, Conti saw a 31.8% decrease in the number of victims and PYSA did not name any victims in Q1 2022.
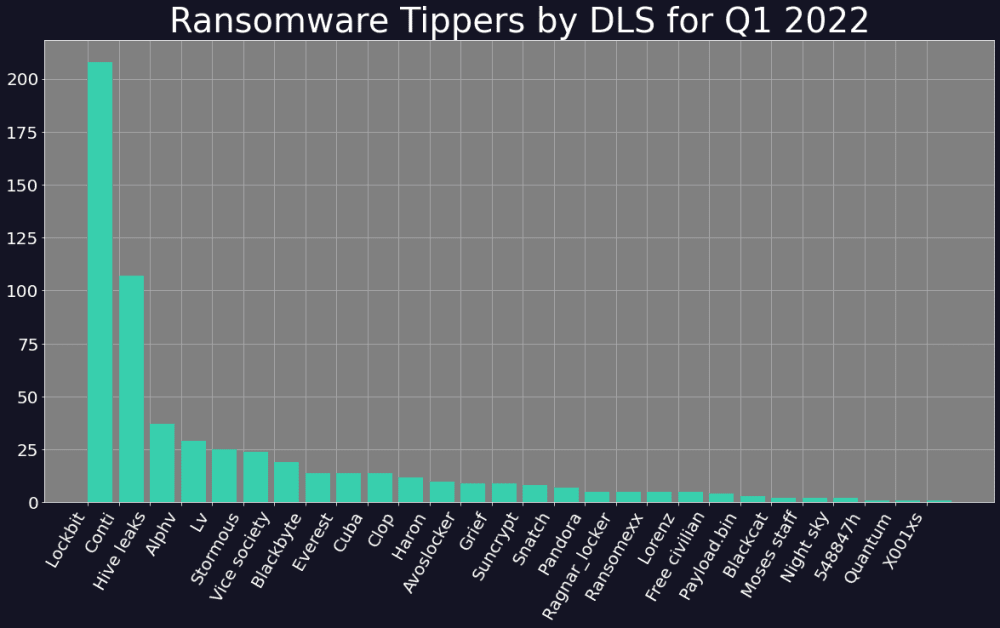
Ransomware activity by group Q1 2022
As was observed in the previous two quarters, LockBit 2.0 and Conti remained the top 2 most active ransomware gangs in Q1 2022, accounting for 57.8% of all incidents reported in the quarter. LockBit continued to establish its dominance in the ransomware threat landscape by having nearly double the number of victims as Conti and 37.9% of all victims reported in Q1 2022. LockBit is the only ransomware gang to have leaked more than 200 victims in a quarter since the release of data-leak sites, and it has done so consistently since Q3 2021.
Breakdown by Sector
Consistent with the last quarter, the Industrial Goods & Services sector was the most targeted sector for ransomware groups in Q1 2022, accounting for 20.1% of all targeted sectors. In second place came the Financial Services sector (7% of all victims), then Construction & Materials (6.5%), Technology (6.2%), and the Government sector (5.2%).

Most targeted sectors in Q1 2022
Many sectors saw a notable decrease in targeting this quarter, which is consistent with the overall trend observed in Q1 2022. The Construction & Materials sector had 42.3% less victims in Q1 2022 (compared to Q4 2021), Travel & Leisure sector saw a 39.4% decrease, and targeting of the Technology sector lowered by 24.5%. However, ReliaQuest did observe a significant increase in targeting of the Financial Services sector (by 75%) and the Government sector (66.7% raise).
Breakdown by Geography
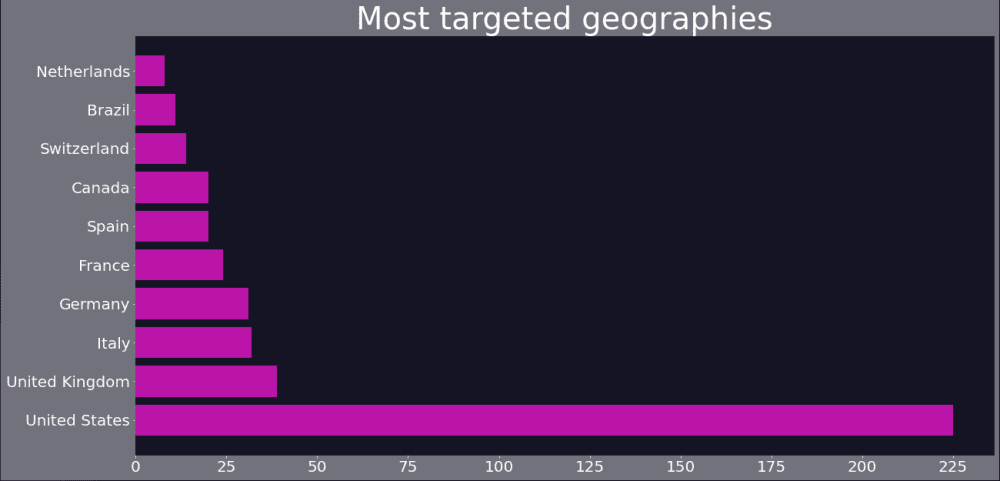
Most targeted geographies in Q1 2022
The United States continued to be the most targeted country in ransomware attacks by a wide margin. In Q1 2022, 38.5% of all organizations posted to ransomware data-leak websites were located within the US, more than five times the number of victims as the UK, which came in second. The high targeting of US organizations is likely driven by the perceived wealth of US organizations and previous success in ransomware groups receiving payments from US companies. The US, UK, Germany, Italy, and France remained in the top 6 most targeted geographies, the same as Q4 2021.
New Kids on the Block
In the first quarter of 2022, ReliaQuest observed the creation of many new ransomware groups and data-leak sites. These included STORMOUS, Night Sky, Zeon, Pandora, Sugar, and x001xs. A trend that is typically observed between quarters is that new ransomware groups are created at a similar rate to groups being shut down. This is likely because affiliates frequently move from groups that are no longer active to those that are emerging. Groups also often shut down operations and rebrand, to avoid raising attention from law enforcement agencies.
This quarter also saw the disappearance of the PYSA ransomware group, who had been a veteran of the ransomware threat landscape. PYSA was the third most active ransomware group in Q4 2021, and the group was known to frequently target the Education sector. Another key event in this quarter was the arrest of REvil affiliates in Russia, which was the first time members of a high-profile ransomware group were arrested in Russia. While it does not appear that REvil members will be extradited to the US, these arrests sent a powerful message to ransomware gangs—Russia may not be a safe haven for ransomware operators. It is possible that these arrests may have been a contributing factor to some groups shutting down operations in Q1 2022.
Q2 2022 Forecast
Q1 2022 was a slow quarter for ransomware groups. There were no large-scale or highly publicized ransomware events, but this is no indication that the ransomware game is slowing down. When comparing Q1 2022 with Q1 2021, we can see that this quarter has generally been slow for ransomware groups over the years, but the level of activity does appear to be increasing compared to 2021. As we saw it occur last year, activity is expected to pick up speed in Q2 2022, and continue to do so until the end of the year.
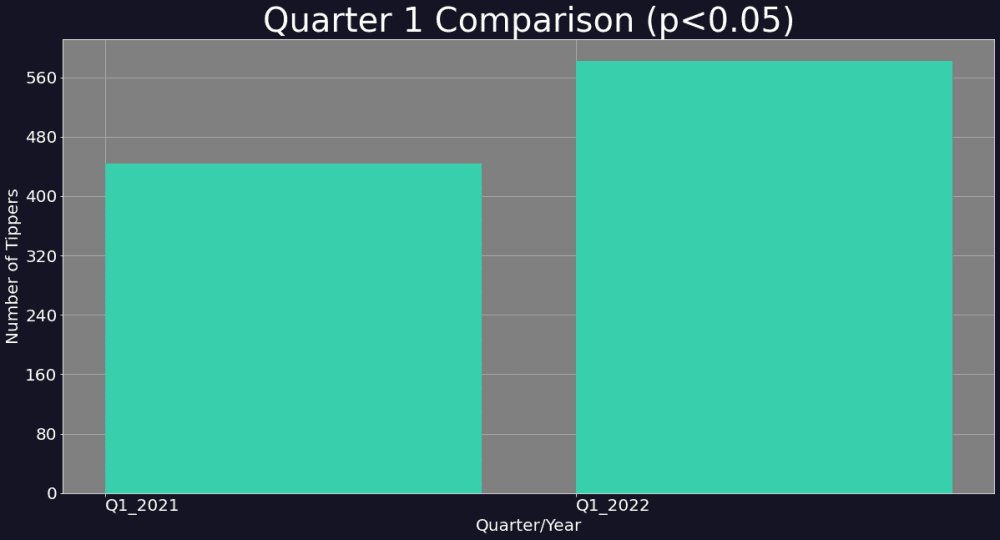
Comparing Ransomware Victims in Q1 2022 and Q1 2021
Another key change that may result in a higher number of incidents is the shift in targeting that was discussed earlier in this blog. As ransomware groups begin to widen their targeting to include mid-sized and smaller organizations, it is likely that the number of victims will also increase, given that attacks are now being conducted indiscriminately. This change in targeting may also result in a greater variety of sectors and geographies being targeted in ransomware attacks.
It is also likely that the war between Russia and Ukraine may continue to spill into the cyber world. We have already observed Russia using wiper malware against organizations in Ukraine, and we can expect that these conflicts will continue to occur. As many ransomware gangs have already offered support to Russia, it is possible that we could see cooperation between operators of high-profile ransomware developers and Russia. This, in turn, could result in heightened threats to critical sectors.
Regardless of the external factors and shifts in targeting, ransomware is likely to remain one of the biggest threats to organizations worldwide over the next quarter. New ransomware groups are going to be created, some will shut down, and groups are going to continue improving their Tactics, Techniques, and Procedures (TTPs). ReliaQuest monitors these changes on a daily basis and you can sign up for our SearchLight platform to stay up-to-date with ransomware threats.
You can get a comprehensive look at the data that we used to build this blog and our quarterly ransomware reporting with a free demo request of SearchLight here. You can additionally get a customized demo of ReliaQuest GreyMatter DRP to gain visibility of your organization’s threats and potential exposures, including access to a finished threat intelligence library with MITRE associations and mitigations from Photon Research.

REvil’s Threat Intelligence profile in Searchlight
For further info—our previous blog article Tracking Ransomware Within SearchLight shows you how ReliaQuest GreyMatter DRP tracks emerging variants, enables you to export and block associated malicious indicators in various formats, instantly analyze popular targets, and map to your security controls with ease.




