Key Points
Most of the critical customer incidents we responded to in 2023 involved fileless malware, accounting for 86.2% of all detections. Many of these intrusions also utilized Living off the Land (LotL) techniques, abusing legitimate Windows binaries such as Rundll32, Msiexec, and Mshta.
Fileless malware and LotL techniques help attackers blend in with legitimate activity, making detection difficult. Fileless malware executes in-memory, leaving fewer indicators of suspicious activity. LotL activity leverages legitimate operating-system binaries, which are needed for regular system functions.
We expect the abuse of fileless malware and LotL activity to continue in 2024 for conducting stealthy cyber operations. ReliaQuest offers detection rules to identify this activity.
For the interest of security decision-makers and defenders alike, this report contains mitigation recommendations focusing on monitoring LOLBins, registry changes, application control, and the abuse of legitimate Windows tools.
Fileless malware—malware running from memory or scripts (e.g., PowerShell, WScript, and Python) instead of executables—has become a popular attack vector for threat actors. In our 2024 Annual Threat Report, we discovered that 86.2% of detections associated with critical incidents in ReliaQuest customer environments from 2023 involved fileless malware. We observed the malware loader “SocGholish” particularly frequently in 2023. This loader is executed through a JavaScript payload that is typically delivered through drive-by downloads, where users are tricked into downloading fake updates. Many fileless malware threats also use living-off-the-land (LotL) techniques, which leverage trusted operating system utilities and binaries to run malicious code in the background, leaving little trace of an attack.
Advantages of Fileless Malware and LotL
Fileless malware presents many problems for security teams, making it an attractive choice for threat actors:
Fileless malware, like SocGholish, is harder to detect than traditional malware because it resides solely in memory and exhibits low-observable characteristics (LOCs)effectively evading many standard security measures.
It manipulates command lines of trusted applications, such as PowerShell, allowing malicious activities to blend in with normal, authorized operations and bypass security measures that typically allowlist these applications.
Since it leaves no malicious files on the hard drive, fileless malware makes post-incident analysis and attribution more challenging for security teams.
Remediation and detection are more complex as there are no specific files or traditional malware signatures to target, requiring more sophisticated and resource-intensive methods, like behavioral analysis.
Similarly, many sophisticated threat actors prefer to “live off the land” to reduce the risk of detection. In 2023, roughly a quarter of all critical incidents we observed in customer environments involved the use of LotL techniques. LotL is a popular attack vector for multiple reasons:
The lack of indicators of compromise (IoCs) associated with LotL activities makes it challenging for defenders to track and categorize malicious behaviors.
LotL saves resources by not having to invest in the development and deployment of custom tools.
Many organizations do not have established baselines, making it difficult to detect malicious LotL activity. This means attackers can blend in more easily with normal activities.
Defenders often face operational challenges such as working in organizational silos and sifting through large volumes of log data to identify malicious activity, making LotL tactics harder to detect.
The growing prevalence of these attacks presents a significant challenge to organizations. These threats are stealthy and can remain undetected for long periods. Therefore, these techniques have been popular with sophisticated adversaries, such as nation-state–linked threat actors and advanced persistent threat (APT) groups. Typically, the more sophisticated a threat actor is, the more likely they are to attempt to live off the land and use fileless malware. For example, the China-based threat group “Volt Typhoon” reportedly leveraged LotL and hands-on-keyboard techniques to target US critical infrastructure organizations.
Commonly Abused LOLBins
LotL binaries (LOLBins) are legitimate and trusted tools found in and signed by Windows operating systems. Threat actors often leverage these legitimate tools to perform malicious activities like executing malware while evading detection. In 2023, the most commonly exploited LOLBins we observed were rundll32, msiexec, and mshta, which are popular Windows utilities. These three LOLBins were involved in 92% of the we reported in 2023.
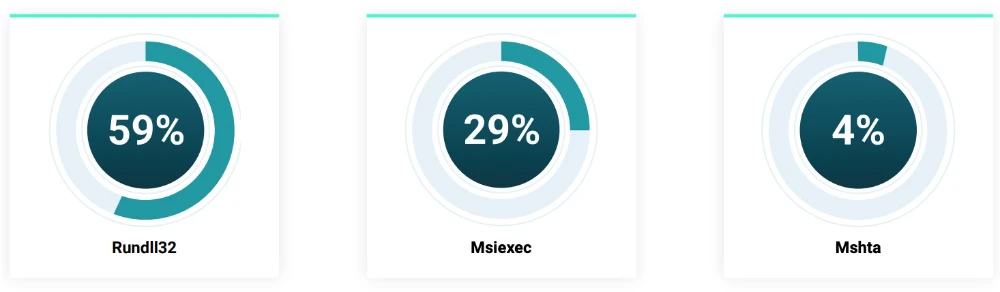
Figure 1: Percentage of the most-detected LOLBins in 2023 by ReliaQuest
These utilities are designed for legitimate purposes—rundll32 to run Dynamic Link Library (DLL) files, Msiexec to execute Windows Installer packages, and Mshta to execute Microsoft HTML Applications (HTAs)—making them ideal candidates for attackers to use for malicious script execution. For example, the malware loader Raspberry Robin utilized legitimate Windows utilities to launch rundll32 to execute malicious commands, which then started other Windows utilities such as odbcconf.exe, allowing the threat actor to continue to stay living off the land.
Below is a list of LOLBins we commonly observed in 2023, including their legitimate uses, how they are exploited, and mitigations for each.
Binary | Use | Exploitation | Mitigation(s) |
Rundll32 | Used for the execution of DLL files on Windows. | Threat actors use rundll32 to execute malicious DLLs masquerading as legitimate processes. | Monitor rundll32 for its use with unusual or obfuscated parameters and paths. Employ behavioral detection strategies and utilize application control policies. |
Msiexec | Used for the execution of Microsoft Software Installer (MSI) files on Windows. | Exploited to download and execute malicious MSI packages from remote locations. Threat actors use this binary to install malware under the guise of legitimate software installations. | Restrict and monitor the execution of Msiexec, especially from unknown or untrusted sources. Implement network controls to prevent Msiexec from downloading files from the internet. Use application allowlisting to allow only trusted MSIs. |
Regsvr32 | Used for registering DLL files on Windows. | Used by threat actors to bypass user account controls and firewall protections, executing malicious scripts or DLLs without triggering security alerts. It can remotely fetch and execute code without writing to the disk. | Monitor the use of Regsvr32, especially when it attempts to fetch code from the internet. Implement application allowlisting. Use EDR tools that can detect suspicious behavior patterns. |
MMC | Used to load snap-ins to manage Windows systems locally and remotely. | Threat actors craft malicious Microsoft Management Console Snap-Ins, which when executed within MMC, can perform elevated privilege tasks, alter system configurations, or deploy further payloads. | Limit the use of MMC to administrators and monitor its execution and the snap-ins being loaded. Educate users on the risks of executing unknown MMC snap-ins. Use security software that scrutinizes system management tools' activities. |
Regsvcs/Regasm | Regsvcs and Regasm are used to register .NET assemblies with the Windows Registry. | Threat actors register malicious .NET assemblies to execute code within a trusted process. | Monitor the use of these utilities, especially for registry activities that deviate from the norm. Implement strict controls over the registration of Component Object Model (COM) objects. Use application control policies to prevent unauthorized use. |
Netsh | A Windows tool used to display or modify the network configuration of a computer. | Threat actors exploit Netsh to manipulate network configurations, allowing for the establishment of persistent backdoors. They can use it to add firewall rules to permit malicious traffic or create VPN connections. | Monitor and restrict the use of Netsh, especially modifications to firewall rules and network configurations. Implement logging for Netsh commands to identify unauthorized changes. Employ EDR tools to alert on suspicious Netsh activity. |
Case Study
In 2023, ReliaQuest addressed an incident where the SocGholish malware, delivered by a drive-by download from a compromised site, successfully executed on a host. The malware, known as “update.js,” is classified as fileless because it operates entirely in memory, using commands from a JavaScript file, unlike typical Windows executables that write to disk and can be detected by antivirus software.Upon execution, SocGholish checked if the host was domain joined; if so, it continued its execution; otherwise, it attempted to ingress a remote access tool.
This incident highlights SocGholish’s ability to evade standard detection methods. SocGholish is also capable of deploying additional malware, such as ransomware, which makes it a high threat.
Technical Breakdown
Upon execution, the SocGholish file utilized default Windows utilities (LOLBins) to conduct several enumeration commands and then saved the output to a temporary file. This enumeration was then exfiltrated to the threat actor’s command-and-control (C2) server to provide details of the environment, including Active Directory information, account privileges, and security products. Below is a streamlined summary of the steps and commands used by the threat actor in this attack:
1. User and System Identification
whoami.exe to retrieve the current username
cmd.exe with systeminfo and findstr commands to collect host information including hostname, registered owner, boot time, system architecture, and the domain controller hostname
Query | |
cmd.exe /c "systeminfo | findstr /S /M /I /C:"Registered" /C:"System Boot Time" /C:"System Type" /C:"Logon Server |
2. Domain and Trust Analysis:
nltest /dclist and /domain_trusts to list domain controllers and trusted domains
3. Credential and Group Membership Enumeration:
cmdkey /list to list stored usernames and credentials
net group commands to query members of “Domain Admins” and “Enterprise Admins”
net localgroup Administrators to query local administrators
4. Service and Process Mapping:
Utilizing WMI (gwmi win32_service) and tasklist commands (/C tasklist) to list running services and currently active processes
Query | |||
gwmi win32_service | ?{$_.PathName -notmatch 'c:\win' -and $_.State -eq 'Running'} | select Name,DisplayName,PathName,ProcessId | ft -auto |
Used the repeated WMI query start iwbemservices::execquery – root\cimv2 : select * from win32_process to retrieve all running processes
5. Host, Hardware, and Software Inventory:
Used WMI query select * from win32_computersystem, which queries host information, including detailed system specifications
WMI queries (start iwbemservices::execquery) targeted at win32_bios, win32_process, win32_operatingsystem, and win32_computersystemproduct to gather BIOS, process, OS, and product information
6. Security Software Detection:
Specific WMI queries within root\securitycenter2 to detect installed antivirus and anti-spyware products
Queries |
start iwbemservices::execquery - root\securitycenter2 : select * from antivirusproduct |
start iwbemservices::execquery - root\securitycenter2 : select * from antispywareproduct |
Upon identifying successful execution, because SocGholish is commonly used for initial access, ReliaQuest instructed the customer to isolate the host to prevent hands-on-keyboard exploitation. The host was restored from a known-good backup, and the impacted user credentials were changed.
In addition to the steps above, organizations can take the steps below to protect themselves from similar attacks:
PowerShell
Update PowerShell to the latest version—version 5 and above contains the ability to enable script block logging and transcription to see what scripts are being executed.
Configure execution policies in PowerShell to enhance security by controlling script execution conditions.
Disable PowerShell for certain user profiles through Group Policy Object (GPO) to reduce potential exploit vectors.
Prevent PowerShell version downgrades through GPO to ensure the use of more secure, updated versions.
Limit the use of PowerShell to authorized users.
Enable constrained language mode in PowerShell to limit executable commands.
Activate script block logging to record detailed information about executed PowerShell scripts, including those invoked dynamically, for forensic analysis.
WScript
Keep WScript disabled by default and only enable it for specific trusted tasks.
Configure a GPO to open JavaScript files in Notepad, preventing their execution.
Monitor execution attempts of WScript to identify and investigate unauthorized or suspicious activities.
Visual Basic Script
Disable or limit access to unnecessary Visual Basic Script (VBS) components.
Implement application control to block execution of scripts or applications based on the “Mark of the Web” (MOTW) attribute, preventing the running of untrusted scripts downloaded from the internet.
Regularly review and update the list of authorized VBS components in line with current security policies and operational requirements.
Threat Forecast
We predict, with high confidence, that the use of fileless malware and LotL techniques will continue to be highly prevalent throughout 2024. These techniques are particularly popular with sophisticated threat actors—including nation-state–aligned threat groups—who focus on conducting stealthy operations, such as espionage. The difficulty of detecting these attacks means they pose a high threat to organizations. Organizations should prioritize the integration of behavioral analytics into their security infrastructure, which goes beyond signature-based detection and identifies unusual patterns of activity that could indicate fileless or LotL attacks. Implementing strict application allowlisting policies can also serve as a critical defense, ensuring that only approved software can execute.
What ReliaQuest Is Doing
To identify the use of fileless malware and LotL activity, ReliaQuest offers the detection rules for their customers. Implementing these rules will allow customers to identify tool abuse and unauthorized software that violates policy obligations. These rules can be calibrated to each organization’s environment to attain a higher level of fidelity and reduce false positives. In addition, we also provide containment and response plays for each detection rule. These automated plays can be executed by customers to mitigate threats if they are enabled. However, not all response plays are suitable for every customer, as the applicability depends on the specific technologies integrated with systems.
Recommendations and Best Practices
Building on the detection rules cited above, we offer the following general recommendations and best practices to establish a secure foundation against the LotL and fileless malware threats mentioned in this report.
Enhanced monitoring of script execution: Implement EDR solutions with capabilities to monitor and alert on unusual script executions, especially those involving PowerShell, WScript, and rundll32.
Restrict and audit PowerShell usage: Limit PowerShell execution to authorized personnel only and enable script block logging to audit PowerShell activities comprehensively.
Isolate critical systems: Segregate systems critical to business operations from general network access. Utilize application allowlisting on these systems to prevent unauthorized execution of scripts or LOLBins.
Monitor and control outbound connections: Utilize network monitoring tools to detect unusual outbound connections that could indicate data exfiltration or command and control communication, particularly from processes like Regsvcs/Regasm.
Analyze and restrict Windows Registry changes: Monitor and restrict changes to the Windows Registry, especially from executables like Regsvr32, to prevent malicious registrations or configurations that facilitate persistence and evasion.
Enforce Safe DLL Loading: Configure systems to use safe DLL search mode, reducing the risk of DLL hijacking, particularly for LOLBins execution scenarios.




