Over the past year, our product team has been working to integrate additional capabilities into the GreyMatter security operations platform to provide greater operational efficiencies for our customers’ security teams and reduce risk across their organizations.
now provides even greater context and intelligence within the platform to help security teams decrease and better map to MITRE ATT&CK techniques—all within the same platform they use to get their work done today.
By integrating additional threat intelligence into the security operations platform, GreyMatter customers will get the right information, at the right time, in the right place so they can take immediate action. This ensures the security team’s workflow is not interrupted by pivoting in and out of tools or by needing to conduct additional research on their own.
So, what’s new?
IoC Detail Views
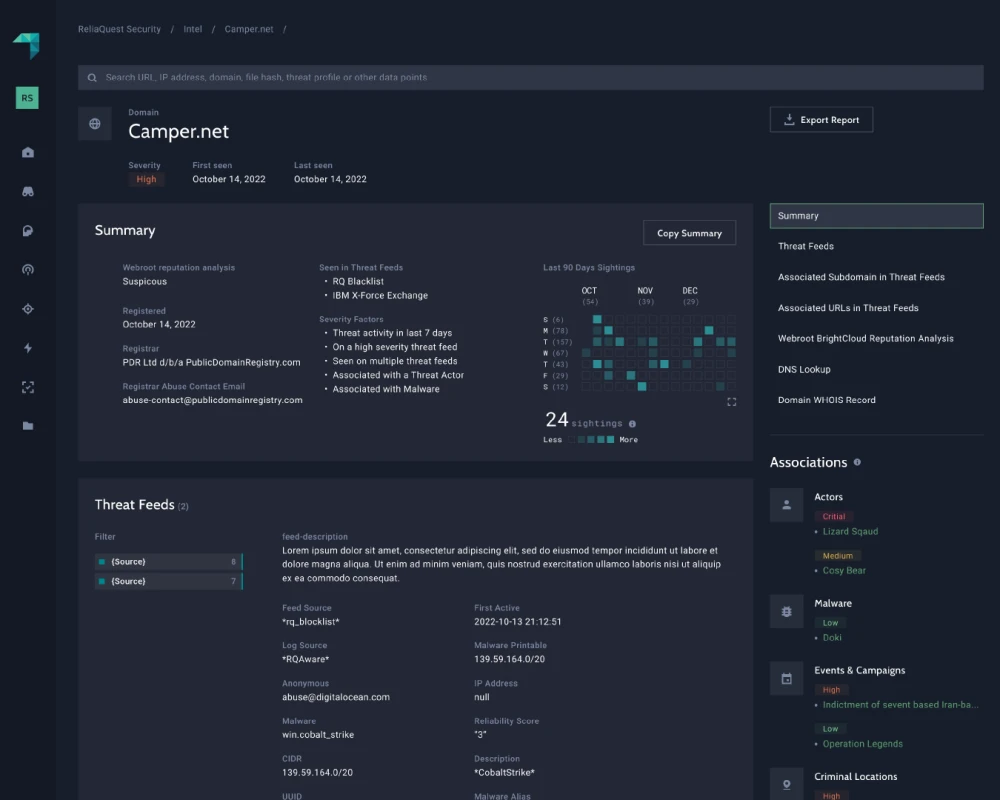
By receiving relevant intelligence from across the open, deep, and dark web, GreyMatter customers will now get a greater level of context around the indicators of compromise (IoCs) that impact their organizations. This context provides more information at analysts’ fingertips—allowing them to resolve alerts and run investigations with greater speed and simplicity.
GreyMatter now provides additional context including domain registration information from WhoIs, reputation analysis, DNS lookups, and more. This intelligence also provides information about the severity of threats both inside and outside of the organization to help security teams prioritize the work that is most important and time sensitive. Additionally, GreyMatter customers can now quickly share IoC information via a PDF report to increase efficiencies across the team and keep stakeholders in the loop.

Threat Profiles
Threat Profiles bring the power of our Threat Research Team directly into the GreyMatter platform. This includes timely and comprehensive written research around the latest threats and how to address them. Threat Profiles provide insight into the latest threat actors and how they operate, industry-specific information, and geographical correlation. This added context is mapped to MITRE ATT&CK techniques to help you reduce the risk posed to your organization—regardless of where it exists.


Unlocking the Value of Threat Intelligence
Adding even more open-source and paid threat feeds reduces visibility gaps that may leave organizations open to risk. GreyMatter Intel aggregates and correlates the data across these feeds to bring relevancy, actionability, and availability to your threat intelligence.
Relevancy – The information provided is meaningful to your specific organization—not just data.
Actionability – The information provided leads you to act on next steps to better enable your security team and protect your organization.
Availability – The information is provided at the right time and in the right place.
A Force-Multiplier for Security Teams
Adding to the GreyMatter platform provides a 360-degree view into the threats that exist inside the perimeter and across the internet.
Plus, bringing DRP into GreyMatter ensures that only the right alerts are surfaced to your security teams when they need them. Typical digital risk protection tools can be noisy with a lot of alerts for your security team to sift through. The context added by bringing DRP and GreyMatter together makes it easier to reduce alert noise and allows your team to accomplish their work from a single platform.
Learn more about GreyMatter DRP >
The threat intel and DRP capabilities provided by ReliaQuest can help you increase your threat intelligence maturity faster than what you could do on your own. Cybersecurity leader from a large airline company





