We often hear lines like “your past will always catch up with you, no matter how hard you try to make it go away,” stark reminders that the decisions we make today will impact the results of tomorrow. This phrase rings particularly true in the world of cybercriminals. History has served up multiple examples of crooks undone by their past mistakes. So is the criminal underground contributing to its downfall?
“Think before you register.” (Source: RaidForums)
ReliaQuest recently observed a moderator on a cybercriminal forum abruptly denying a member’s request that their account be deleted, pointing to the forum rule that accounts will not be removed for any reason, along with the tagline ,Think before you register.” This denial got us thinking: If they cannot cover up their past, are cybercriminals playing a dangerous game, waiting for their earlier mistakes to come back to haunt them?
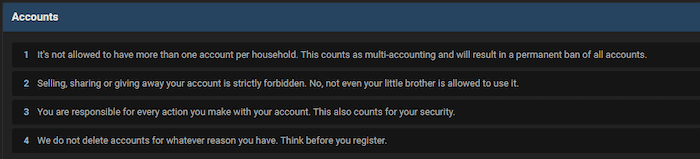
Figure 1: RaidForums account rules
Read further on our free research report, The Modern Cybercriminal Forum, here.
What’s the Big Deal with Cybercriminal Forum Accounts?
In the real world, we all develop as individuals through age, life experiences, and knowledge. To look back over our life and cringe at moments we wish hadn’t happened is only human nature. But what if some moments—especially illegal acts—haunted you for the rest of your life? Instead of learning from these moments, you might be constantly fearful that your previous self may have landed your future self in prison. This is where the issue of forum account deletions comes into the equation.
Imagine signing up for a cybercriminal forum with an email address that you thought was secure at the time. Still, it was loosely tied to your real-life identity (e.g., an email address referencing your name or an email obtained using your real-life details). As a complete newbie eager to learn, you begin to actively partake in forum life, learning whatever you can, developing your skills, and honing your trade until you start to become a member that others look up to. Loving your newfound status, you begin to join more advanced criminal forums with selected niches such as carding, fraud, and hacking, but—not wanting to lose the reputation tied to your original moniker—you sign up to these platforms under the same alias. Although the criminality level is more advanced, these sites bring more opportunities to make money and further establish yourself as a key player in the cybercriminal underworld.
One day, the forum administrator of one of these platforms is arrested for a deal gone wrong. At the point of arrest, the law enforcement agency involved manages to acquire the administrator’s credentials to the forum and extract data, including private messages, user information, email addresses, and Jabber IDs. Unfortunately for you, your username pops up on law enforcement’s radar as one of the site’s movers and shakers. But you’re not worried; you have good OPSEC practices, and you signed up to the forum with an encrypted email address separate from your real identity…
But wait, what about the username? Law enforcement officials can cross-reference this identifier to find linked accounts on other forums. Worse still, they could stumble across your account from your younger criminal days that you had completely forgotten. With a little digging, your real name and home address are uncovered thanks to this old account. With one small error of judgment from 10 years ago caused by inexperience and naivety, your life starts crumbling around you, and you are contemplating life behind bars.
This might sound a bit far-fetched, but there have been numerous instances where simple misjudgments have been the undoing of high-profile threat actors. A good example is the high-profile arrest of Canadian citizen Alexandre Cazes, the administrator of the notorious, now-defunct dark web marketplace AlphaBay. Investigations into the email headers in messages sent by Cazes to a marketplace user revealed an email address that law enforcement managed to tie back to Cazes, ultimately leading to his downfall. And who could forget Dread Pirate Roberts, the notorious Silk Road creator, undone by using a personal email that referenced his full name, Ross Ulbricht, on a forum post tied to an associated moniker asking for programming help for the marketplace. Both cases show how historical errors of judgment have come back to haunt a user who thought they would never get caught. A final example involves the creator of the popular Anubis banking trojan, arrested in 2019 following their use of a real-world IP address and how it was associated with an email address that was subsequently used to sign up for the Russian cybercriminal forum Exploit.
Figure 2: AlphaBay marketplace banner
Do Russian-language Cybercriminal Forums Delete Accounts?
While many Russian-language forums conduct “purges” to remove old accounts, it is common for unused accounts to be deactivated rather than deleted. Essentially, this means the requesting account cannot be accessed by anyone else, and the account is appropriately marked up as deactivated on the forum. Interestingly, however, the user’s profile page and posting history can still be viewed and analyzed long after they have “left” the site. So although administrators do facilitate account deletion requests to some extent, other members can still retroactively search for the deactivated user and review their forum activity.
Despite the many differences between the English and Russian-language cybercriminal communities, the two scenes appear to be aligned on the issue of account deletion. Both English- and Russian-language sites tend to favor account deactivation or disablements over deletion. Perhaps one scene follows the precedent set by another, or maybe both recognize specific issues that come with account deletions and the difficulty of facilitating these requests on an individual basis.
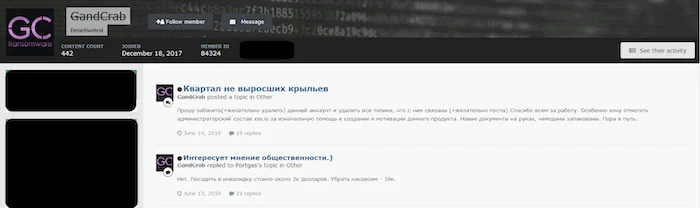
Figure 3: Deactivated user on Exploit
Why are There Problems with Deleting Accounts?
The logical conclusion here is that cybercriminal sites should allow their members to request old accounts to be deleted to clean up their Internet history. In the real world, GDPR gives us the “right to be forgotten.” Moreover, you’d think forums would be happy to “tidy up” old and unused accounts. Yet, specifically on the English side, similar posts identified across Cracked TO, Nulled, and RaidForums all who refuse account deletion requests remind us that the cybercriminal world doesn’t operate like the real world.

Figure 4: Account deletion problems
We don’t know precisely why forum account deletions are so problematic. One RaidForums post stated, “deletion generally takes high db privileges. Which in those cases means that only an admin can do it and they have enough on their hands”. This argument is supported with a similar scenario on the cybercriminal forum Cracking org. An account deletion request was denied by the administrator, who instead offered to disable the requesting account. This indicates that the issue may relate to permission levels to the underlying user databases behind a forum. If a forum’s database can only be accessed by an approved administrator, an administrator must log in each time, manually search, find, and delete the specific user entry. This not only takes time but could lead to accidentally deleting users with similar names. Therefore, the forum admin’s possible way around this is to permit forum staff members to mark up accounts as disabled or deactivated, ultimately saving time and sharing the workload.
Another reason for preventing account deletions could be account reactivation and future scam attempts. If an account is permanently deleted, then the original owner runs the risk of that reputable username falling into the hands of a scammer who might try to benefit from the username’s previous success by creating a similar-sounding or even identical moniker. If the original owner can return to an account they previously owned and reactivate it— an efficient way to solve it. We have seen this numerous times in the past when users attempt to create forum accounts in the guises of other popular accounts by slightly altering the username, e.g., “GnosticPlayers” on RaidForums and the potential copy-cat accounts “GnosticPlayers1” and “GnosticPlayers2,” all stating they were the legitimate threat actor. Even though each of these accounts was subsequently banned for “multi-accounting,” it shows the difficulty facing forum administrators in allowing full account deletions.
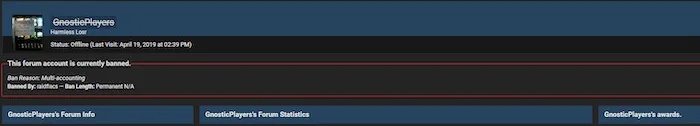
Figure 5: GnosticPlayers multi-account creation scenario
How Can This Be an Advantage to Security Practitioners?
If the cybercriminal world is aware of various high-profile arrests and how cybercriminals have been linked to associates, identifiers, and past activities through a trail of old aliases and usernames, surely forum administrators would be more than willing to make life more difficult for law enforcement?
Instead, it seems that, regardless of geography, a forum administrator’s time and resources outweigh the threat of arrest or blowback from any single user. In other words, how a threat actor conducts themselves on a forum is solely their responsibility. Though there are justifications for not facilitating account deletions (accessibility, purging, and account scammers), the risk of exposure remains prevalent as an individual responsibility to be shouldered for cybercriminals. If a user truly wants their account deleted, their only hope is for the forum to either shut down or be seized. Still, even this can be negated if a forum is brought back to life from an old forum back up years later ( e.g., the defunct forum DamageLab in its current iteration as XSS).
Though not so good if you are a reformed cybercriminal with a less-than-stellar past, this trail is spectacular intelligence for security teams. Say, for instance, a direct threat is made against your organization on a cybercriminal forum from the alias “c00kie_monster”. Threat intelligence can be gathered on the history of this alias’s activities across the deep and dark web to determine if the threat holds real risk, report on the sophistication and TTPs of the threat actor, and mitigate against the risk.
Photon continues to closely monitor the cybercriminal landscape, looking for more unique insights to understand the threat organizations’ delicate dynamics are facing. If you’d like to search the dark web and cybercriminal underworld for malicious mentions of your organization or exposed data for sale, sign up for a demo of ReliaQuest GreyMatter DRP here.
Alternatively, you can individually access a constantly-updated threat intelligence library providing insight on this and other cybercriminal-related trends that might impact your organization and allow security teams to stay ahead of the game. Just sign up for a free seven-day test drive of ReliaQuest GreyMatter DRP here.




