What Happened?
Last week’s collapse of California’s Silicon Valley Bank (SVB) has companies keeping a watchful eye on future threats. The United States’ 16th-largest bank collapsed after cautious investors triggered a liquidity run, leaving its customers—mostly from the technology, private equity, venture capital, and life sciences sectors—in limbo.
SVB is now controlled by the Federal Deposit Insurance Corporation (FDIC), and the American government has secured deposits, but uncertainty for the financial services sector remains high. In the United Kingdom, HSBC’s £1 purchase rescued the British arm of SVB, but European banking stocks have still taken a hit.
Now named Silicon Valley Bridge Bank (SVBB), its new CEO has said that the bank is “open for business” and has called for SVB’s former customers to return. American banking stocks have regained ground since the collapse, but the storm isn’t over: the credit rating service Moody’s has downgraded its outlook of the United States banking system from “stable” to “negative.”
In the wake of SVB’s collapse, ReliaQuest has been keeping an eye on cyber threats to business and consumers. Read on for our assessment of the current situation, as well as some scenarios we might see next.
Suspicious Activity
Using ReliaQuest’s Digital Risk Protection (DRP) capabilities, we’ve been tracking a surge in newly registered domains referencing SVB. These include domains potentially impersonating legitimate SVB services, like SVB customer support. They also include potential examples of typo-squatting, where attackers use similar characters to register new domains and trick unsuspecting victims: can you spot the difference between upper-case “I” and lower-case “l”?
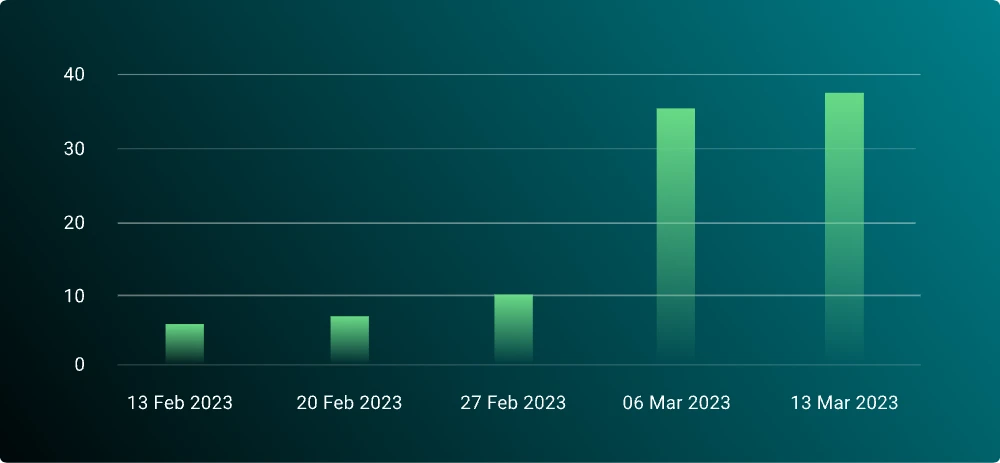
Newly registered domains referencing SVB have risen sharply: from March 6–12, 2023, we observed 95 new domains likely impersonating SVB, none of which are registered to registrars previously used by SVB. This is an 11x increase in comparison to the rolling average of potential impersonating domains over the past three months.
Although these domains aren’t hosting content at the time of writing, they may be placeholders for future threats. Impersonating domains are often used in phishing attacks. They can be used to increase the legitimacy of phishing emails, to encourage victims to click on malicious links, or to create fake login pages to capture banking—or other—credentials.
Cybercriminals React
Not ones to procrastinate, cybercriminals have already begun exploiting SVB’s collapse. Phishing scams impersonating the bank have been observed targeting cryptocurrency users. Attacks have also been observed impersonating financial services companies, promising cryptocurrency users a payout because of the collapse.
We’ve been monitoring cybercriminal forums for reaction to the event. At the time of writing, reaction has been limited—SVB was not a retail bank, so cybercriminals are less likely to have pre-made phishing kits ready to impersonate SVB. However, for at least some cybercriminals, interest has been piqued: one forum user noted that the collapse leaves former customers vulnerable to targeting (see Figure 2).

At the time of writing, we have not associated any SVB exploiting attacks with cybercriminal users on the forums we monitor. We will continue to monitor reactions on open and closed cybercriminal sources.
What to Expect
To help our customers respond to threats, we’ve compiled sample threat actor scenarios, as well as recommendations for how best to defend in today’s uncertain environment. These scenarios are not exhaustive, but exercises in thinking “how would a threat actor respond?”
Scenario 1: Exploitation for Initial Access
It’s been hard to miss SVB headlines over the past week. Savvy threat actors will exploit this notoriety to encourage victims to click on phishing emails, open malicious attachments, or enter credentials into a spoofed website. Malware disguised as a friendly attachment is a favorite tactic for cybercriminal and state-backed threat actors seeking to gain an initial network foothold. Once access is obtained, threat actors are likely to deliver additional malware such as ransomware, cryptocurrency jackers, or credential scrapers.
Cybercriminals aren’t the only ones trying to loot and pillage; advanced persistent threats (APTs) are known to target financial services in cyber-espionage or disruptive attacks, using phishing to gain an initial foothold. Events like SVB’s collapse will realistically be exploited to conduct attacks.
Some APTs (looking at you, North Korea) are also known to conduct financially motivated attacks. SVB’s collapse may serve as an avenue to steal cryptocurrency and other funds from unsuspecting victims. SVB customers with uncertain banking situations, as well as individual cryptocurrency users and cryptocurrency companies, are likely to be attractive targets for these groups.
Scenario 2: Business Email Compromise
Phishing attacks and fraud attempts exploiting SVB’s collapse in the near future (next few weeks) are almost a given. Cybercriminals are opportunistic and SVB is low-hanging fruit. Of greater concern to businesses are targeted attacks like business email compromise (BEC). BEC attacks have targeted small and large businesses in every American state and were responsible for over $43 billion in business losses worldwide from 2016 to 2021.
In BEC attacks, threat actors impersonate, or sometimes compromise, employee email addresses to trick other employees into transferring them money. High-ranking employees, like CEOs or CFOs, are particularly likely to be impersonated. With former SVB clients currently finding new banks and conducting large-scale money transfers, they are particularly at risk.
BEC campaigns instill a sense of urgency around money transfers. They can be difficult to identify for victims, particularly when email accounts have been hijacked. Individuals responsible for making financial payments should be aware of common BEC tactics and should ensure payment requests are valid before transferring funds. Companies should inform employees of their business relationship with SVB and give employees instructions on how to verify whether emails are legitimate.
Scenario 3: Insider Threats
Businesses hit with financial uncertainty may have to make the difficult decision to restructure in the coming months. Technology sector layoffs have increased sharply over the past six months and are only likely to get worse faced with difficult banking conditions.
In the event of layoffs, shrinking security teams and internal disruption are likely to leave systems vulnerable to threat actors. Delays to implementing critical patches are likely, and overburdened employees are more likely to make mistakes or be negligent, failing to follow security best practices. Strong security cultures in businesses will help mitigate this threat.
With restructuring also comes an increasing likelihood of malicious insiders. These could be financially motivated, such as selling proprietary information to competitors, or selling sensitive data or network access to cybercriminals. Destructive attacks are also realistically possible, like deleting sensitive code or files, or purposefully leaving open vulnerable systems. Businesses should segment employee data access and quickly revoke system access for former employees.
How to Defend
ReliaQuest recommends that businesses take the following steps to defend against threats arising from the SVB collapse.
ReliaQuest leverages threat intelligence to support security operations, now with the added benefit of Digital Risk Protection. Click here for more details about ReliaQuest threat intel. To see our threat intel in action, request a demo here.





