Note: As of May 2022, Conti has shut down its operations.
At ReliaQuest, we constantly monitor the internet for anything that can be used to help our customers make security possible. When we spot leaks or attacks, we’ll perform the threat research and get it integrated into our GreyMatter security operations platform.
This post is going to cover insights, tactics, and detection opportunities gleaned from materials leaked from within the Conti ransomware gang in 2021. These materials provide valuable insight into the motivations, tactics, and techniques of ransomware operators, which can be used to better defend your environment against these threats.
Conti Ransomware Operator Workflow
The leaked materials give an almost step-by-step playbook of how these operators perform actions in a compromised environment. A general workflow is performed, which closely models a typical kill chain:
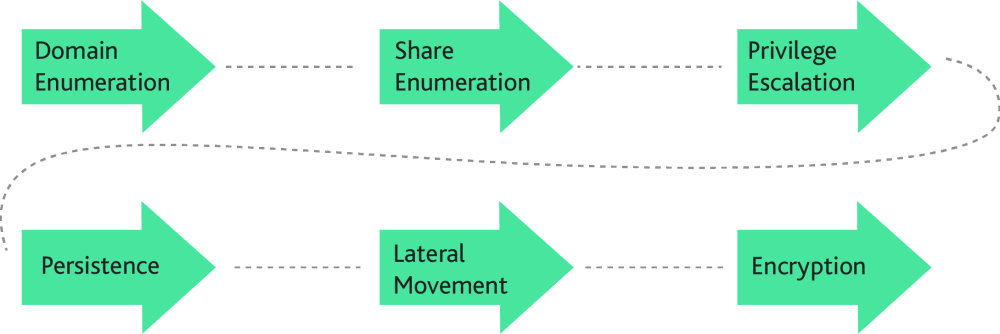
Understanding this workflow and considerations made by the operator during each phase gives us a better picture of understanding how to better secure our environments against these threats.
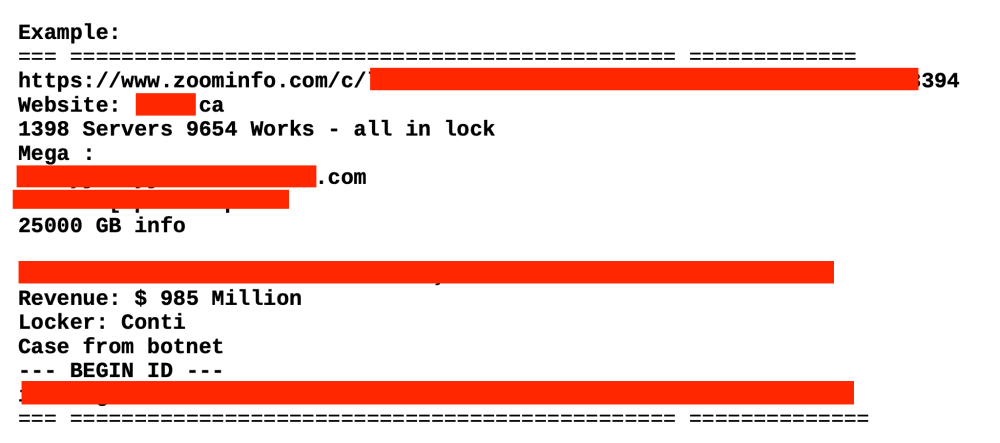
First, a company’s value is determined. This is primarily done through Google dorks, a technique that uses OSINT resources to find valuable information. For example, the operator would look up the organization’s revenue, and this would be used to determine the ransom amount.
Domain Enumeration
A ransomware threat actor’s primary motivation is to gain as much privilege as fast as possible to enable them to deploy their locker malware across the environment, so their first step once gaining a foothold is to enumerate the domain as thoroughly as possible.
As called out in the leaked materials, a primary method to do so relies on both Cobalt Strike Beacon’s net module, the native Windows , certain open source
PowerShell modules, and nltest.exe, another native Windows tool typically bundled in Active Directory servers.
These commands are focused on identifying targets of interest (e.g. backup servers, domain controllers), enumerating groups, enumerating user permissions, and identifying administrator accounts. During this phase, a tool such as Seatbelt may be used to enumerate protections in the environment that the operator will have to account for.
Share Enumeration
Next, an operator will attempt to enumerate shares within the environment. A tool like PowerSploit may be used. The training materials specifically call out looking for ADMIN$ shares available to the current user across the environment, which could highlight opportunities for lateral movement. Finding shares with the ability for the current user to write to is important as it allows the operator to both encrypt the shares, and use them as a file host.
It is specifically mentioned that shares with the following names are particularly focused on, depending on the target organization:
Finance
Accounting
IT
Clients
Projects
Privilege Escalation
Now that the operator has a decent understand of the environment they are in, their next goal is to escalate privileges. Assuming the machine they compromised doesn’t already have administrator privileges, local privilege escalation exploits are preformed. This may involve running enumeration tools like windows exploit suggester, in some other cases, misconfigurations will be abused by using a tool like SharpUp. Operators may opt to perform a kerberoasting attack using something like Rubeus.
Local user monitoring may also be performed. For example, SharpChrome could be used to collect information from a local Chrome browser, giving the operator insight into network and external resources that a user normally goes to.
Another common tool used at this point is mimikatz, a favorite tool of security practitioners everywhere, that allows for extracting of LSA secrets. It’s important to note that it’s recommenced to operators here to not necessarily rely on running mimikatz locally on the machine, but to instead create a minidump of the lsass process and process that offline.
Operators may even opt for the blunt force approach and attempt to brute force user credentials, relying on common password antipatterns such as:
Passwords like these often fulfill password security requirements, but their presence leaves your environment open to abuse.
The Conti ransomware gang has also demonstrated through this leak that they remain informed about the latest security vulnerabilities, even specifically mentioning leveraging the recent Zerologon or PrintNightmare vulnerabilities to escalate privileges.
Persistence
Conti’s playbook specifically mentions that at this stage, Atera or Anydesk can be installed on the host to provide the operator remote access to the machine, but this is dependent on the environment. Other forms of persistence may also be performed, for example:
Abusing the run key to execute a beacon:
It’s important to note that the hidden (+h) attribute is applied to these files using attrib. These tasks are typically called through the run registry key.
In memory backdoors: In the event that a an operator is in a more hardened environment, they may opt to inject an in-memory Metasploit backdoor.
Creating a scheduled task: To better blend in, the operator will give the task a generic name, such as
Adobe Update,WindowsDefender, etc.Create a backdoor user and use a sticky keys backdoor: This is typically used only on bastion hosts
Use image file execution options to attach a malicious process to a legitimate one
Register a WMI event to execute a payload at a controlled interval
Inject libraries using AppInit DLLs
Register a library in in the
lsaasprocessUse winlogon to obtain a session every time a user logs in
As you can see, the choices for persistence are abundant, and the ransomware operator is expected to select the appropriate mechanism for their targeted environment.
Lateral Movement
Once an account of sufficient privilege is obtained (such as Domain Administrator), and a share is identified that can be used to spread the locker malware, operators will begin to prepare for the encryption phase. This may or may not involve lateral movement in the traditional sense of “pivot to as many machines as possible”. In some environments, this could simply all be done from one machine, in other environments it may require lateral movement across machines to reach desired areas of the network.
Typical lateral movement techniques are used, such as abusing psexec, winrm, or wmi to pivot to other machines.
Some lateral movement methods, such as wmi pivoting, may load malicious backdoorsthough another process, such as the following case, where wmic is used to load artifact.dll via rundll32.exeon the remote machine:
wmic /node:[ip] process call create "rundll32.exe C:\Temp\artifact.dll StartW"
In addition, operators may attempt to enumerate privileges on remote machines as the current user by running commands such as:
dir \\ip_of_remote_workstation
dir \\ip_of_remote_workstation\C$
Keep in mind that, if done through a default Cobalt Strike setup, this may appear as:
cmd.exe /c dir.exe \\ip_of_remote_workstation\C$
Encryption
With the operator well impregnated in the environment, the final encryption step comes in three phases, a “final reconnaissance” phase, an “upload” phase, and the actual “lock” phase.
Final Reconnaissance
This phase focuses on maximizing the value of the ransom from the victim, where the operator will focus on identifying and hunting administrators and identifying and removing backups.
This is one of the riskiest phases for the operator, as many of the actions they will be performing here may be more likely to trigger alerts by astute administrators, so specific attention is called out to be careful here, as detection and containment at this phase can still result in failure of the ransomware operation.
To quote one of the materials itself:
This manual was written to not try to go at breakneck speeds to get a session and raise alerts from the administrators. Our job is to understand how it is arranged, not brute force everything. Everything is already hacked, you just need to look at everything through the eyes of the admin. The main task of the admin hunt is to understand where they store passwords and steal the database, excel files and text documents.
During this phase, an operator may retrieve a list of domain administrator accounts, focusing on ones belonging to individuals rather than services. From there, the operator will investigate the account details and the individual behind it, assessing what their role is, and the date of last logon. The operator may even visit this user’s LinkedIn account to verify additional information. Here they are focused on accounts that not only have access to valuable resources, but also are recently active. For example, if a domain admin account is only ever used once or twice a month, but another account is used every few days, the operator will place precedence on the account with higher activity to be able to better blend in.
OSINT is also utilized to determine which accounts to target during this phase. For example, the operator may perform a search on LinkedIn for current employees of the target organization then look for employees with titles containing phrases like:
System
Admin
Engineer
Network
IT
SharpView may be utilized here to determine which systems a user is authorized to access. Operators focus on machines where the user is currently authenticated. It is emphasized to avoid raising a session on these machines and instead, steal their token and browse their workstation remotely.
Here the operator will begin to trawl the user’s home directory looking for any custom configurations, admin tools, stealing browser data from Chrome, etc. The goal is to find where the backups and/or hypervisors are, all in hopes of increasing the chance of a ransom payout. Password databases like Keepass or Lastpass are of focused, as well as passwords to various internal services. In addition, an operator may even go as far as stealing the user’s Outlook mailbox and trawling emails for anything of value.
Upload Phase
While this phase is specific to techniques detailed in one of the leaked manuals, this is not a prescriptive method that “stops all ransomware.” Here an operator registers a mega account, then creates an rclone configuration, and uses rclone to upload any files of values, such as financial information, system configurations, etc. Finally, these documents are searched for important keywords, such as “underwriting,” “bank statement,” “insurance,” etc. It is likely these are used to determine the ransom amount.
Lock Phase
Finally, the operator prepares to perform the actual encryption across the environment. A locking binary may be copied to a share that’s easily accessed across the domain, such as a primary domain controller. This can be done through psexec, wmi, or other methods. In the event that a hypervisor such as ESXi is compromised, this locker may have the capability to kill machines on it in order to encrypt their disks.
Sample lock message. Image credit pcrisk.com
Prior to running the locker, the operator may elect to add a GPO configuration to disable antivirus such as Windows Defender or Sophos.
Finally, batch files and auxiliary programs, such as psexec, are uploaded to the domain share with the locker, so that victim machines can utilize them to spread their payloads across the network. A manual specifically mentions usage of a dll for [tobbot] to use for controlling and automating actions across victim machines.
The operator will then manually login to a few machines and evaluate whether the locker execution was successful.
Takeaways
There’s a few immediate lessons to be gleaned from the ransomware operator workflow. As defenders, our goal should be to impose as much time and difficulty cost as possible on threat actors operating within our environments. Ultimately we want to increase detection opportunities as much as possible, to be able to contain the threat as early as possible.
Through the application of the principle of least privilege, we can increase the difficulty for the operator to traverse through the network. Ultimately zero-trust is a good goal to shoot for, but starting small and working your way up can have significant benefits in reducing the impact of ransomware operations.
By monitoring process hierarchy, ideally with a well monitored EDR solution, we can gain additional detection opportunities. The Conti ransomware manuals have a heavy emphasis on blending into the environment as an administrator, but by identifying abnormal process relationships, their operations can be interrupted.
The Conti ransomware team has a heavy reliance on a variety of open source security tools. By building detections centered around the techniques these tools use, we can hopefully detect not only usage of these tools, but any custom tooling that relies on them as a foundation of knowledge to operate.
Enforcing a strong password policy, and more importantly, regularly rotating AND auditing credentials can inhibit a ransomware operator’s ability to traverse through a network.
Much like the NSA, ransomware groups hunt sysadmins. Separating sysadmin privilege, and closely auditing sysadmin activity can increase detection opportunities.
Many times where ransomware operators have had to copy a file from a local file system (for example, NTDS.dit from a domain controller), instead of copying directly from the file system (e.g. C:\Windows\NTDS\NTDS.dit), they were instead copied out of the Volume Shadow Copy, providing a solid detection opportunity.





