Key Points
The cyber threat landscape has seen a significant increase in information-stealing (infostealer) malware activity, with a 30.5% rise in marketplace listings for “stealer logs” from Q3 to Q4 of 2023.
This malware type has evolved to encompass more sophisticated tools that aim to harvest sensitive information such as usernames, passwords, and credit card details. These malicious programs often operate as part of botnets, utilizing various methods to spread and evade detection.
The ReliaQuest Threat Research team identified “LummaC2,” “RedLine,” and “Raccoon” as the most prevalent infostealers in 2023, with LummaC2 nearly doubling credential sales quarter-over-quarter. We attribute their success primarily to their unusual distribution methods.
Successful data theft by infostealers can lead to severe consequences for organizations, including financial loss, intellectual property theft, and compromised sensitive data. This stolen data can also serve as initial access for further attacks.
To combat the use of infostealers, the ReliaQuest Threat Research team recommends implementing security enhancements such as certificate-based authentication for enhanced user access security, utilizing enterprise browsers with advanced security features, and establishing a Digital Risk Protection (DRP) strategy to monitor for exposed credentials.
Infostealer malware, which covertly infiltrates systems and harvests sensitive information, poses a significant risk to individual and organizational security. Infostealers have been a persistent threat for many years, with the earliest variant, ZeuS, emerging in 2006. Since this early example, infostealers have become increasingly sophisticated and widespread. Cybercriminal activity involving infostealers spiked significantly from Q3 to Q4 2023: ReliaQuest noted a 30.5% increase in cybercriminal forums marketplace listings for “stealer logs” (data harvested by infostealer malware).
This report provides an overview of common infostealer variants; describes their targeted geographies and sectors and tactics, techniques, and procedures (TTPs); and outlines general mitigation steps and best practices.
Infostealers Overview
The ever-increasing complexity and prevalence of infostealer malware is fueled by the lucrative nature of stolen data, which is commonly sold on cybercriminal forums, marketplaces, and messaging applications like Telegram. Once adversaries extract valuable information, they sometimes share stealer logs for free on these platforms; subsequent resharing on other forums allows even more threat actors to access the data at no cost.
Infostealers are designed to infiltrate computers and transmit sensitive data, including:
Usernames and passwords
Cookies
Credit card data
Cryptocurrency wallets
Browser history
Hardware/software information
This malware typically targets credentials from online banking websites, social media platforms, email accounts, and file transfer protocol (FTP) accounts. Modern infostealers often function as part of botnets, enabling attackers to remotely connect to an infected host and transmit data via command-and-control (C2) servers. These malicious entities spread infostealers through methods like spam email attachments, compromised websites, and malware advertising, often in conjunction with other malware types such as downloaders, Trojan droppers, and keyloggers.
Stealer malware can pose big risks with profound impacts, illustrating the critical need for heightened awareness and sophisticated defense strategies. For example, the now-notorious Change Healthcare cyber attack was initiated through compromised credentials that can be sourced from infostealer malware.
Infostealers can disproportionately affect different sectors, geographies, and technologies. Sectors handling significant sensitive information like healthcare, finance, and retail are particularly at risk. Geographically, regions that are commonly targeted for ransomware, such as the US, UK, and Canada, seem to be most at risk. The reason behind the geographical targets is highly likely due to the higher demand in compromised credentials being purchased for these regions.
Here’s a more specific look at how threat actors can maliciously leverage stolen information:
Initial access for further attacks: Once threat actors obtain initial access through stolen data, they can use this foothold to extract more sensitive information or to introduce other malicious software, such as ransomware, into the system.
Credential stuffing attacks: Threat actors may use stolen credentials to perform credential stuffing attacks on corporate accounts, exploiting the common issue of password reuse across multiple platforms.
Bank account access: Threat actors might attempt to access bank accounts using the stolen credentials and drain the funds or use the accounts for money laundering purposes.
While infostealer malware has historically targeted individuals, the threat to corporate organizations is significant and growing. The ramifications of an infostealer malware infection for organizations are profound, encompassing not only financial loss and intellectual property theft but also severe data breaches that could impact the entire organizational structure. This malware type not only facilitates financial exploitation but also serves as a gateway for further attacks, potentially leading to widespread ransomware infections.
Most Common Infostealers in 2023
The ReliaQuest Threat Research team has compiled an overview of the most common infostealers we observed in 2023: LummaC2, RedLine, and Raccoon.
LummaC2
LummaC2 was most prevalent infostealer in 2023, according to ReliaQuest’s collection of dark web marketplace listings. In addition, the number of LummaC2-obtained logs listed for sale increased by 110% from Q3 to Q4 2023. LummaC2’s rising popularity among adversaries is likely due to its high success rate, which refers to its effectiveness in successfully infiltrating systems and exfiltrating sensitive data without detection. Additionally, its intuitive user interface (UI) makes the tool accessible to threat actors across a wide spectrum of skill levels.
The pricing model for a LummaC2 subscription ranges from $250 to $1,000 per month, depending on the subscription tier selected.
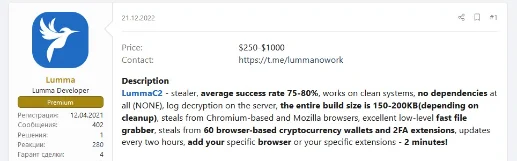
Figure 1: LummaC2 subscription service and description
LummaC2 is best known for using unconventional distribution tactics, including the deployment of trojanized software files and spearphishing emails equipped with deceptive links or attachments. This method allows LummaC2 to bypass some standard security measures designed to catch more common phishing attempts or drive-by downloads.
Furthermore, LummaC2 targets a comprehensive array of sensitive data not limited to traditional credentials. It focuses on cryptocurrency wallets, browser extensions, and two-factor authentication (2FA) details. This targeted approach makes LummaC2 particularly perilous for businesses that manage digital assets or utilize extensive online financial services.
LummaC2 sets itself apart in the landscape of infostealers through its broad targeting capabilities and systematic extraction methods. Capable of infiltrating a range of systems from Windows 7 to Windows 11 and compatible with at least ten different web browsers, LummaC2’s adaptability is unmatched. Its ability to target and exfiltrate data from applications related to cryptocurrency and extensions further distinguishes it as a significant threat, especially given the rising prominence of digital currencies in business operations.
The stealthy nature of LummaC2’s operations makes it particularly dangerous, as it can siphon sensitive information without immediate detection, multiplying the potential damage.
Redline
RedLine ranked as the second most prevalent infostealer ReliaQuest identified in 2023, with a 44% rise in listings from Q3 to Q4 2023. This growth is noteworthy, yet it falls far short of LummaC2’s growth rate. The popularity of RedLine can likely be attributed to its high success rate of exfiltrating financial data such as cryptocurrency wallets. While not as prolific as LummaC2, RedLine has made a name for itself in the cybercriminal world due to its high infection rate and more affordable malware-as-a-service (MaaS) subscription starting at $100 per month, as compared to competitors, most of which start at $250.
Since its inception in March 2020, RedLine has been utilized by initial access brokers and other malicious actors on Russian-language cybercriminal forums. It specializes in exfiltrating passwords, credit card details, instant messages, and cryptocurrency wallet information. Over time, RedLine’s distribution methods have evolved from phishing emails themed around COVID-19 to using adware through malicious Google ads, weaponizing Microsoft Office documents, and targeting digital artists in the NFT space. More recently, it has adapted by masquerading as a Windows 11 upgrade tool, demonstrating its ability to exploit current trends to enhance its dissemination.
RedLine’s extensive technical capabilities enable it to perform a variety of malicious activities that are particularly disruptive to organizations. RedLine allows adversaries to harvest system information such as browser types, FTP client details, and hardware configurations. It can perform a range of malicious activities, including uploading and downloading files, executing commands, and relaying information about compromised systems back to the attackers. Such functionalities not only allow for the theft of sensitive data but also potentially facilitate deeper network penetration and lateral movement within a corporate environment, leading to more extensive breaches and data compromise.
RedLine differentiates itself from other prominent infostealers like LummaC2 and Raccoon through its targeting strategy and distribution techniques. RedLine has a broader target spectrum and uses more varied distribution methods. Compared to Raccoon, which also operates on a MaaS model, RedLine’s ability to adapt quickly to current trends and its lower entry price point make it accessible and dangerous.
Raccoon
ReliaQuest identified Raccoon Stealer, sometimes rendered as “Racoon,” as the third most common information stealer in 2023. Despite its ranking, mentions of Raccoon on the dark web saw a drastic decrease from Q3 to Q4 2023, largely due to the arrest of Mark Sokolovsky, a pivotal figure behind Raccoon, in late 2022. This arrest disrupted operations temporarily and led to significant law enforcement scrutiny, which temporarily halted Raccoon’s activities.
Raccoon Stealer is adept at stealing a wide range of data from over 60 different applications, including sensitive information such as login credentials, credit card details, browsing history, and cryptocurrency wallet data. In August 2023, the developers released an updated version based on user feedback and market trends. This version introduced features like an innovative URL search method for quick data access, automatic bot detection and blocking, and detailed log statistics.
Raccoon Stealer’s subscription was initially priced at $200 per month but increased to $275 in August 2023. It is also offered at $125 per week, making it accessible for short-term use.
Raccoon Stealer is differentiated by its user-friendly interface and robust functionality, catering to less technically skilled cybercriminals. Raccoon focuses on providing a simple yet effective tool for extensive data harvesting, making it particularly dangerous for organizations. The stealer’s ability to target a vast range of applications and its enhancements aimed at evading detection make it a formidable tool for extracting corporate data.
The resilience and adaptability of Raccoon Stealer, despite significant disruptions such as the arrest of its key developer, highlight the persistent threat posed by such cybercriminal tools. Organizations must remain vigilant and proactive in their cybersecurity efforts to defend against such sophisticated malware.
LummaC2 Case Study
In October 2023, ReliaQuest observed in a customer environment the execution of the unauthorized file “Passwrd-2023_Setup.rar,” which is associated with LummaC2. Shortly before the malicious file was downloaded, the user attempted to install a cracked license key from the license key download service “hdlicense[.]com.” This redirected the user to “hxxps://1july[.]com/rMKNqt3S,” where the user was prompted to download the malicious RAR file. After clicking the download prompt, the user was redirected to multiple domains, including “sustac[.]com” and a free file-hosting server that initiated the LummaC2 malware download.
“Passwrd-2023_Setup.rar” contained multiple files, including a legitimate, signed copy of the cross-platform media player “VLC Player” renamed as “Setup.exe” and the LummaC2 executable. The executable used a technique called Dynamic Link Library (DLL) side-loading to import a copy of the VLC Player library (“libvlc.dll”), which then imported a malicious version of the library (“libvlccore.dll”). libvlccore.dll loaded the LummaC2 payload. Using DLL side-loading enabled the adversary to bypass security measures, execute the malware, and establish a C2 connection to “hxxp://ebalkayiu[.]fun/api.”

Figure 2: Passwrd-2023_Setup.rar file contents
In this case study, ReliaQuest communicated to the impacted organization our recommendation to first isolate the impacted endpoint to disable any communication or active connections. We then deleted the “Passwrd-2023_Setup.rar” file and blocked all associated indicators of compromise (IoCs). The impacted organization rotated the user’s credentials, reimaged the endpoint, and notified the user of the organization’s acceptable use policy (AUP). Further communication with the impacted customer confirmed that no additional IOCs or C2 traffic were identified following these steps.
This incident showcases characteristic hallmarks of LummaC2, including the use of legitimate software to disguise malware activities and the exploitation of less secure third-party download sites. To prevent similar incidents, organizations should implement stringent controls on software downloads and installations, which in this case allowed the initial download of a cracked software key.
Below is a list of IoCs we observed in this case study:
IOC | Type |
7a35008a1a1ae3d093703c3a34a21993409af42eb61161aad1b6ae4afa8bbb70 | Hash |
a9e9d7770ff948bb65c0db24431f75dd934a803181afa22b6b014fac9a162dab | Hash |
hxxp://ebalkayiu[.]fun/api | URL |
hxxps://1july[.]com/rMKNqt3S | URL |
hxxps://download2361.mediafire[.]com/kz5hd3dkenwgED02vBaT_kwGFdmwQ1 iAY4QGf3SAcLidcmbEn-K1HrKyPpR6ADOq7VjezmdEoNhZJFB_Wze08J1MU0iH_ oPWGS6Myj12LuXef9l7y_Em63yxedx88ezRHTt44POY858wKHjwxqr2errwIun SIHwCNMWQNQPY4_0FkZKD/wt0hho282tuxy9d/Passwrd-2023_Setup.rar | URL |
sustac[.]com | Domain |
Threat Forecast
We predict that in 2024, LummaC2 and RedLine activity will continue to grow. With the sales of credentials obtained via LummaC2 more than doubling from Q3 to Q4 2023, the stealer shows no signs of slowing down. RedLine, with its 44% rise in dark web marketplace presence in the same period and a diverse range of associated tactics for distribution and data theft, is highly probable to continue to grow. Its adaptability and affordability make it an attractive option for cybercriminals looking to harvest sensitive information efficiently.
On the other hand, the usage of Raccoon will likely continue to decline throughout 2024. The drastic decrease in mentions and sales of Raccoon stealer logs on cybercriminal forums toward the end of 2023 suggests threat actors’ waning interest in this tool. This downturn may result from its outdated evasion tactics, the emergence of more advanced stealers like LummaC2 and RedLine, and the arrest of a key figure behind Raccoon in late 2022. This arrest not only disrupted Raccoon’s operations but also exposed the vulnerabilities within its infrastructure, likely diminishing its appeal to cybercriminals.
Mitigations, Recommendations, and Best Practices
While ReliaQuest Digital Risk Protection can alert customers when credentials appear in breaches or are sold on sites like Russian Market, we also take a more proactive approach. To identify the use of stealer malware, ReliaQuest offers detection rules. Implementing these rules will allow defenders to identify unauthorized software that violates policy obligations. These rules can be calibrated to each organization’s environment, to attain a higher level of fidelity and reduce false positives. In addition, we also provide containment and response plays for each detection rule. These automated plays can be executed by customers to mitigate threats if they are enabled.
The ReliaQuest Threat Research team offers the following inexhaustive list of recommendations and best practices to protect against infostealers’ impact.
Prevent saving of passwords in browsers: Implement strict network policies or Group Policy Objects (GPOs) to disable the saving of passwords in web browsers. This security measure is crucial as many infostealers target saved credentials in browsers to exfiltrate sensitive information. Regular audits should be conducted to ensure compliance and effectiveness.
Shorter session cookie timeouts: Configure shorter session cookie timeouts to reduce the risk of session hijacking. By limiting the duration of sessions, even if an attacker gains access to session cookies, their window of opportunity is significantly reduced. This enhances overall security by forcing users to re-authenticate more frequently.
Cert based authentication: Adopt certificate-based authentication to strengthen the security of user access. Certificates provide a higher level of security compared to traditional passwords and are less susceptible to phishing attacks. Implementing this method can significantly improve the security posture by ensuring that only authenticated users can access sensitive systems.
Enterprise browsers: Utilize enterprise browsers that offer enhanced security features tailored for organizational needs. These browsers often provide better management and security controls, including the ability to enforce policies, monitor usage, and protect against malicious websites. Integrating enterprise browsers can bolster security while maintaining user productivity.
DRP for monitoring for exposed credentials: Establish a Digital Risk Protection (DRP) strategy to continuously monitor for exposed credentials. DRP solutions can scan the dark web, paste sites, and other sources to detect if any corporate credentials have been compromised. Rapid detection allows for swift remediation actions, such as password resets and user notifications, to mitigate potential damage.
Employee training and awareness: Conduct regular training sessions to educate employees about the risks associated with infostealers. Training should cover the identification of phishing emails, suspicious links, and unusual requests that may be attempts to install malware. An informed workforce is a critical defense against social engineering attacks.





