Do you and your team want to start proactively threat hunting in your environment?
If so, it’s time to dive into the threat hunting steps below, starting with performing research on what you want to hunt for before digging into the data. It can be tempting for security teams to want to dive right in without a plan and instead start ad-hoc threat hunting. According to the SANS 2020 Threat Hunting Survey, almost half (45%) of respondents run an ad hoc hunting process that is dependent on their needs. However, this often leads to hours or even days wasted chasing down loose ends.
We have experienced it ourselves! Through multiple iterations of building out our threat hunting team and capabilities – across numerous industries and environments – we’ve continually refined and matured the process. Now, we’d like to share our lessons learned and steps that you can use as a base to build your own threat hunts.
At ReliaQuest, we follow these threat hunting steps when building a new threat hunting plan:
STEP 1: IDENTIFY A CYBER THREAT HUNTING TEAM.
It’s important to identify the right people to do hunting in your environment. You can have new members perform hunting, but they will need a more defined process. We suggest having a team that is familiar with how an attacker thinks and to have a threat centric mindset when hunting in the environment. Typically, someone that has been an analyst for 2-3 years will be able to have an efficient approach to threat hunting.
STEP 2: DEFINE A TIMELINE FOR THE THREAT HUNT BASED ON YOUR TEAM’S BANDWIDTH.
What we have seen is that most organizations only have around five hours to really dedicate towards a threat hunt. However, we typically spend anywhere from 10 to 30 hours performing hunts. Due to the time commitment, we’d recommend building a hunt that can be accomplished in 10 hours – this way, your team member(s) performing threat hunts can accomplish more in their busy schedule. Finding one good take away, whether a hygiene fix or a threat, is a successful hunt (avoid boiling the ocean).
Common Pitfall: Some teams spend time over-analyzing threat hunts instead of focusing on key findings. It’s better to identify five actionable items versus a lengthy report that will fall to the wayside. The analyst in you will want to detail out every finding; however, in order to maximize your threat hunts, it’s important to take a step back and identify the most impactful findings.
STEP 3: OUTLINE A HIGH-LEVEL MISSION.
This document should explain what you are looking for overall and you should be able to tie multiple objectives to it. We typically recommend starting with a baseline hunt, then moving to a threat-based hunt. It’s important to identify what’s normal and any potential hygiene issues or logging gaps before hunting down threats. A good way to plan out hunts once you have a solid baseline would be reviewing gaps that your threat detection content can’t or won’t cover – these can be aligned with threat groups that target your industry.
Common Pitfall: Teams to want to dig into advanced TTPs (Tactics, Techniques, and Procedures) before understanding what’s normal. For the most effective threat hunts, we recommend starting small and building up to that level of threat hunting.
STEP 4: DOCUMENT THE OBJECTIVES FOR THE THREAT HUNTING MISSION.
The objectives are what you look for during your hunt. These should align to your high-level mission and include technical documentation on the how.
Start by mapping the objectives to a framework such as MITRE ATT&CK or the Cyber Kill Chain. Mapping the objectives in this way enables you to cover more gaps that your alerts or detections are missing. It also sets the foundation for a structured approach on coverage. Let’s take a look at an example for threat hunting using DNS queries:
DNS Query: MITRE T1048 & T1094
Note if the objective is hygiene or threat related for tracking purposes. This way, you can prioritize your goals for the threat hunt and set up multiple levels per objective if needed. Following the same DNS query example from above, this could look like:
Hygiene: Identify common domains queried in the environment.
Threat: Look at high DNS request volume to multiple sub domains of a domain from a single host.
Logging! Know what log sources and the type of logging you may need for the objective. This is a common pitfall for threat hunting teams. By identifying the required log sources first, you won’t waste time threat hunting for something that you have no visibility into.
To learn more, check out the Threat Hunting Use Case Blog series, or get the white paper:Threat Hunting 101.
BONUS STEPS: TRACK, ACCELERATE, AND IMPROVE YOUR THREAT HUNTING PLAN THROUGH RELIAQUEST GREYMATTER
Following the steps above, your team will be ready to build a foundational threat hunting plan that can be repeated, scaled, and refined over time. At ReliaQuest, we take our threat hunts a few steps further using GreyMatter, the security operations platform.
**1. Standardized Queries.**Part of the research and development process is creating queries that will automatically run against all available technologies and pull back the relevant data for the threat hunt. Within GreyMatter, it’s easy to select the hunt campaign you are looking for and load the query so that the hunt is ready to go. You can also modify the campaigns on the fly if you want to exclude or include items, such as adding a list of executive users that you want to target for the hunt.
**!35DXSLdmLo0F3gUJ1Y5ht1! **
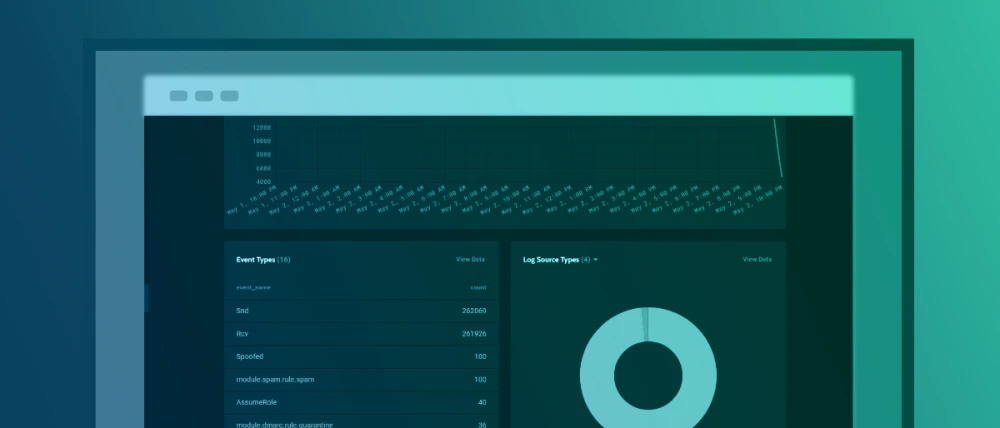
**2. Create customized dashboards on the data set.**Through ReliaQuest GreyMatter, the data is visualized in dashboards so that it is repeatable and easy to find the answers to the objectives. This also provides an easy way to get screen shots around findings for documentation. Below are some screen shots from GreyMatter that illustrate how important and efficient visualizations are when cyber threat hunting.
**!6qnVHMyUzp6kU5LaSM8hmd! **
3. Machine Learning! GreyMatter leverages machine learning algorithms. This helps identify abnormal activity and provides sample data sets to see how accurate the models are. All of these are battle-tested in our own environment.
With GreyMatter, proactively identify threats with click-and-go threat hunting. ReliaQuest customers have access to machine learning, threat hunting dashboards, and guided hunt campaigns, as well as custom-developed queries that pull your target data set.
Learn more about ReliaQuest GreyMatter.