Over the past ten years, cryptocurrencies have become the go-to form of payment for the less law-abiding citizens of the world due to their secure and anonymous nature. The now-defunct dark web marketplace Silk Road pioneered Bitcoin’s use back in 2011, and other cybercriminal platforms soon followed. Even today, the use of cryptocurrencies shows no sign of abating; Forbes reported that the total value of Bitcoin transacted on the dark web grew by 340% over the past three years, with an increase of 65% in the past year alone. While Bitcoin has generally been the most popular cryptocurrency among cybercriminals since its launch in 2008, several thousand alternative cryptocurrencies (“altcoins”) have been created in the intervening years, and names such as Litecoin, Ethereum, and Monero have become familiar terms in the dark web scene. Monero, in particular, has represented a real challenge to Bitcoin’s crown since its creation in 2014, mainly in part due to its core belief in security and the increased demand for anonymity. But are these offerings presented by Monero enough to knock Bitcoin off its throne?
In this blog, we will explore cybercriminals’ discussions about using these two cryptocurrencies and look at three key factors that might tip the scale in favor of one over the other, showing that strength in numbers when it comes to accessibility and usability, likely outweighs the benefits of anonymity.
Choosing a Cryptocurrency
Digital Shadows (now ReliaQuest)’ research identified three key factors that influence the cybercriminal community when deciding between Bitcoin and Monero: accessibility, usability, and anonymity.
Accessibility
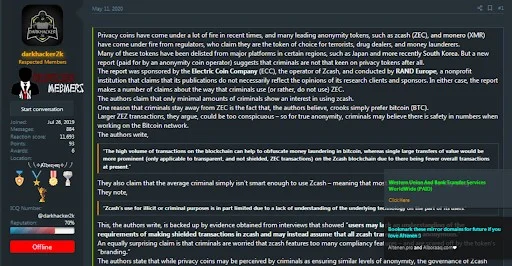
Before deciding on their go-to cryptocurrency, users must consider how they can acquire the coins in the first place. All the anonymity features count for very little if they can’t get their hands on it. While the Cryptocurrency sections of English-language forums, such as Nulled and Altenen, contain plenty of dubious methods on how to acquire cryptocurrencies for free (one example being a 4-step method on how to “Earn free bitcoins on idle every day!” shared on Nulled), most threat actors probably opt for more legitimate methods, including cryptocurrency exchange services, crypto-mining, and ATM machines.
Figure 1: User offering method for obtaining “free bitcoins”
Cryptocurrency Exchange Services
Cryptocurrency exchange services are digital marketplaces where traders can buy and sell Bitcoin and altcoins using fiat- or crypto-currencies. Digital marketplaces issue crypto-wallets, software that allows cryptocurrency users to store and retrieve their digital assets. These digital marketplaces are easy to access, easy to use, and contain plenty of information and step-by-step guides. Users on the English-language cybercriminal forum RaidForums have recommended these services as the right place for “newbies” to start their cryptocurrency journey.
There are many cryptocurrency exchange services to choose from, including Coinbase, Binance, and Bittrex, who all offer various cryptocurrencies for users to choose from, including Bitcoin and Monero.
The main issues with exchange services are commission fees and formal identification requirements. As a result, methods promising to enable users to obtain cryptocurrencies without ID verification are often shared on cybercriminal forums. Although Monero can be bought on cryptocurrency exchange services and require some form of ID verification, just like Bitcoin, the methods being shared on cybercriminal forums for obtaining cryptocurrencies without ID verification primarily apply to Bitcoin only. There is little, if any, discussion on such practices relating to Monero (or other altcoins) and might indicate that Monero is not in the same demand with cybercriminals as Bitcoin just yet. This is not to say that Monero is never sought after; due to its ease of access, many cybercriminals procure Bitcoin first (hence being consistently in demand), then transfer the Bitcoin funds into Monero, thus avoiding any obstacles of procuring Monero directly.
Cryptomining
Cryptomining enables users to introduce new coins into the existing circulating supply by verifying transactions between users and adding them onto the blockchain public ledger. Mining is key to cryptocurrencies functioning as a decentralized peer-to-peer network, without the need for a third-party central authority. Guides and tools for mining cryptocurrencies, Bitcoin, in particular, are sometimes shared on cybercriminal forums. More recent comments indicate that cryptomining is now viewed as a less cost-effective option to acquire Bitcoin. In the early days, it was possible to mine Bitcoin using the average computer CPU or a high-speed video processor card; however, today, mining for Bitcoin requires dedicated Bitcoin mining hardware to make it a profitable endeavor. It’s even less ideal for obtaining Monero because Monero is designed to be more resistant to the application-specific integrated circuit (ASIC) mining, typically used to mine other cryptocurrencies such as Bitcoin. As a result, Monero can only be mined on consumer-grade hardware.
ATMs
Some larger cities have ATM machines via which users can easily acquire Bitcoin and Monero. Several RaidForums users have recently suggested that these machines are a slightly more anonymous way of acquiring Bitcoin or Monero. Still, the lack of frequent discussions on this issue on cybercriminal forums indicates threat actors are unlikely to use this method on a large scale. Using ATMs requires users to physically travel to known locations, which risks threat actors being identified on CCTV. And of course, this is not the most useful method for those who live far away from such ATM machines, which in general are still few and far between. Additionally, these ATM machines can charge relatively large fees for the transactions, making this a less desirable option.
Usability
Users must consider the usability of their go-to cryptocurrency before going through the process of purchasing coins. For cybercriminals, the usability of cryptocurrencies is likely measured against the number of vendors and the number of criminal platforms that accept the respective cryptocurrencies as payment. In the end, users will probably opt for a cryptocurrency that is accepted by their favorite marketplace or vendors. In this context, cryptocurrencies’ usability has improved since they became the default payment method on cybercriminal platforms, but the degree of usability still varies between different cryptocurrencies.
Vendors
Because of Bitcoin’s status as the most popular cryptocurrency on cybercriminal platforms, many buyers are forced to use Bitcoin to purchase goods and services on the dark web, even if they prefer other altcoins. But some vendors appear to be becoming more flexible as other cryptocurrencies, particularly Monero, have gained more popularity. Recently, vendors on the Russian-language forums Exploit and XSS have stated that they accept payment in both Bitcoin and Monero, indicating that Monero has become more accepted as a standard payment form among vendors. For instance, the known threat actor “Unknown” on XSS associated with the Sodinokibi ransomware group announced in March 2020 that they were switching to Monero: “We are extremely worried about the anonymity and security of our adverts, therefore we have started a “forced” transition from BTC to Monero. In connection with this, we inform you that in a short time BTC will be removed as a method of payment.”
Forum Registration and Paid Upgrades
Bitcoin is still the most widely accepted cryptocurrency on cybercriminal platforms; sites such as Altenen, Canada HQ, and Deep Sea Market will only accept Bitcoin. However, there have been two recent developments that challenge the status quo.
Firstly, more and more cybercriminal platforms now accept several cryptocurrencies and Bitcoin, including Monero, Litecoin, Ethereum, and Zcash. This may be a way to attract a more extensive user base by not restricting payment methods. Popular English- and Russian-language forums, such as Raidforums, Nulled, and Verified, have chosen this approach. Icarus Market, a possible candidate to become the next number one cybercriminal marketplace after Empire’s recent downfall, has also opted for this approach. Secondly, some platforms have decided to only accept Monero as a form of payment to strengthen their users’ security and anonymity, such as White House Market.

Figure 2: A VIP upgrade on RaidForums which can be bought with a number of altcoins
Anonymity
Users must also consider the level of anonymity offeredwhen choosing which payment method to opt for when selling or purchasing illicit goods. This is to limit the risk of getting caught; the more anonymous a payment method is, the better. Cryptocurrencies offered an unprecedented level of anonymity for cybercriminals when they first became mainstream due to their decentralization. Security researchers and law enforcement now have an increased understanding of cryptocurrency technology, partly due to Bitcoin’s popularity, and it has enabled them to improve their tracing capabilities. As cryptocurrency technologies are always developing, it is still the most anonymous payment option available. Additionally, cybercriminals always try to stay one step ahead by either creating additional services that further obfuscate transactions or only conducting transactions using altcoins that endorse anonymity, e.g. Monero.
Cryptocurrency Mixers and Exchange Services
Security researchers and law enforcement agencies have always been able to trace cryptocurrency transactions through the blockchain and their respective public ledgers. Of all the available cryptocurrencies out there, law enforcement and security researchers have primarily focused on Bitcoin transactions due to its popularity. They can trace wallet addresses listed in these transactions, possibly linking them to an IP address, physical location, or even the email address behind the account linked to the online wallet on a cryptocurrency exchange. Additionally, an increasing number of exchange services now require formal ID to use the services, which in turn allows law enforcement to potentially trace wallets and transactions to the people behind them. However, there are several ways to further anonymize Bitcoin to avoid this type of information being revealed, including Bitcoin mixer services.
These services mix the originating coins to obfuscate their origins and make tracing back transactions more arduous, which is why they are often recommended by cybercriminals. Threat actors on several platforms have also recommended first acquiring Bitcoin and then converting it into Monero using a cryptocurrency exchange service, which provides added anonymity. Taking this even further, one user on Dread discussed their method of using Monero to “clean” their Bitcoin trail, by using a script to convert Bitcoin to Monero, and then back again to Bitcoin. The downside of these methods, however, are the exchange fees.
Monero – Not As Anonymous As You Think
The cybercriminal community has recently shared media reports that the US-based company, Ciphertrace, has developed a tool that will enable law enforcement to trace Monero transactions, despite Monero’s added measures to increase anonymity, such as raising funds taken during a transaction to obfuscate the actual figure in a transaction. CipherTrace’s tool will reportedly not allow law enforcement agencies and researchers to trace Monero to the same degree as Bitcoin. Still, CipherTrace is aiming “for future implementation of entity transactions clustering, wallet identification, exchange attribution, and other functionality that will provide law enforcement with even more tools for investigating Monero transactions and addresses.”
Is Complete Anonymity Really That Important?
Despite the report on Monero now being, to some degree, traceable, the cybercriminal community does not appear to be too fussed about this development, at least not yet. The reports of CipherTrace’s tool does not appear to be widely discussed within the community. When a message on this was shared by a user on the cybercriminal forum, Crimemarket, forum members’ replies seemed unperturbed, possibly indicating that at least on Crimemarket, users simply weren’t as concerned about the anonymity aspect of Monero as one might have thought. One member simply thanked the user for sharing the news and asked for more information on the topic to be shared. One other user simply stated that “Monero is still anonymous and private, but to really take advantage of Monero, it is necessary to have [their] own Monero daemon.”
In May 2020, a user on the cybercriminal forum Altenen shared an article discussing why cybercriminals reportedly preferred “less anonymous” cryptocurrencies such as Bitcoin, over “privacy coins” offering more anonymity. The user highlighted a point made in the report saying that “criminals may believe there is safety in numbers when working on the Bitcoin network.” Although not discussing Monero, but another “anonymous” cryptocurrency, Zcash, it was highlighted that despite offering more anonymity, only “1% of dark web postings referring to crypto payment make mention of zcash, and […] 0.15% of dark web-associated wallets are ZEC accounts”. This might indicate that overall, the cybercriminal community as a whole understands the limitations imposed by privacy-based cryptocurrency coins, with services opting not to widely implement the payment methods at this time when there is limited demand.
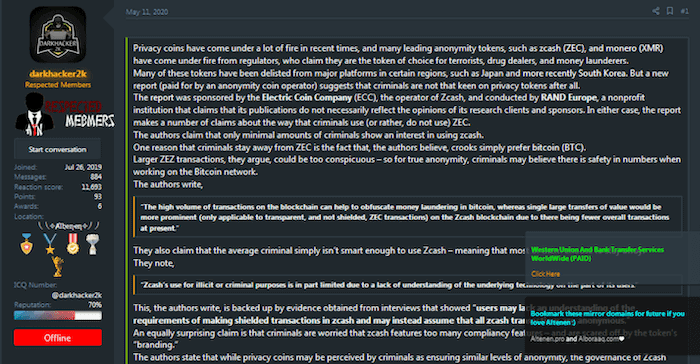
Figure 3: Altenen user discussing “privacy coins”
And the Winner Is…
Being the original decentralized cryptocurrency, Bitcoin has been the staple of the cryptocurrency world since the beginning. This has naturally led to more media exposure and time to become the majority’s go-to cryptocurrency; it is popular, easy to get a hold of, and largely accepted across an array of platforms. A textbook case of supply-and-demand. However, Bitcoin’s level of exposure has come at the risk of anonymity and law enforcement becoming more adept at tracing the blockchain.
This is where Monero has had its advantage. As the most anonymous cryptocurrency on the market, Monero has represented a safe haven for threat actors recognizing Bitcoin’s value and its weaknesses due to its exposure and traceability. Monero has been seen as a way forward in an even more anonymous and secure payment method. As the demand for Monero has increased, both vendors and cybercriminal platforms have reacted accordingly. High profile takedowns of forums and marketplaces also highlight that maybe anonymity and security needs to take precedence over ease of access and usability if cybercriminals want to improve. Still, Monero might not be the answer the cybercriminal community has been looking for; after six years on the market, Monero has yet to reach the same level of exposure as Bitcoin, and the recent announcement of Monero reportedly being to some degree traceable might slow down its recent surge in popularity.
Again, this goes back to supply and demand. Bitcoin is still the most accessible and widely accepted cryptocurrency within the dark web community and is not likely to go away anytime soon. This is primarily due to its market share hold and the visible effort by threat actors to develop methods, tools, and services to make Bitcoin secure. The case of Monero has shown that there are an array of alternative cryptocurrencies lining up which, if striking the balance of demand and security right, might eventually topple Bitcoin from the top — but only when the cybercriminal community starts to fully unite behind more anonymous and secure cryptocurrencies, such as Monero, will we begin to see a real shift.