After a seemingly slow quarter of ransomware activity during the late-2022 festive-holiday season, an alarming surge occurred. The first quarter of 2023 was the most prolific the ReliaQuest Threat Research Team has ever observed in terms of double-extortion ransomware groups. More victims were named on data-leak sites than in any other quarter to date—despite increased law enforcement operations and other challenges ransomware operators faced in 2022.
The Threat Research Team monitors the activity of ransomware groups on the dark web and keeps track of all victims named on ransomware data-leak websites. We also keep track of major developments and trends in the ransomware threat landscape. Let’s rewind to take a look at the most important ransomware-related events that happened during Q1 2023, plus metrics of ransomware groups and steps organizations can take for protection.

Key Ransomware Events
Probably the most notable event in Q1 2023 was an attack campaign by “Clop,” exploiting a GoAnywhere managed file transfer (MFT) zero-day vulnerability (CVE-2023-0669) to breach over 130 organizations. This wasn’t Clop’s first large-scale supply-chain attack. In February 2021, Clop exploited an Accellion file transfer application (FTA) zero-day vulnerability to breach over 100 organizations.
There were many similarities between these two campaigns; both exploited zero-days in file-transfer platforms, and in both Clop chose to steal data from victims and not drop ransomware. By skipping encryption, Clop could conduct these attacks at lightning speeds, reportedly taking only ten days to steal data usingGoAnywhere MFT.
Another important story this quarter was the FBI’s significant seizure of servers of the “Hive” ransomware gang. On 26 January 2023, the US Department of Justice announced a months-long disruption campaign targeting Hive. The FBI reportedly infiltrated the group’s infrastructure in late July 2022, accessing decryption keys and preventing the payment of $130 million in ransom.
Ransomware Runs Rampant
In Q1 2023, we observed close to 850 organizations being named on ransomware and data-extortion websites on the dark web. This was a 22.4% jump from the previous quarter, which had a total number closer to 700. Unsurprisingly, “LockBit” remained the most active group, by a wide margin. But the number-two spot came from a last-minute contender: Clop, with its GoAnywhere exploitation.
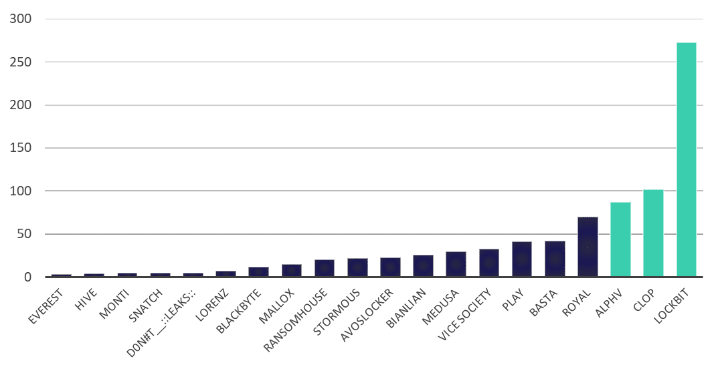
Figure 1: Number of victims named on top 20 ransomware data-leak sites, Q1 2023
March 2023 set the record for the most active month we have ever recorded in the history of double-extortion ransomware. More than 400 organizations were named on ransomware data-leak sites; that’s 35% more than the previous monthly record.
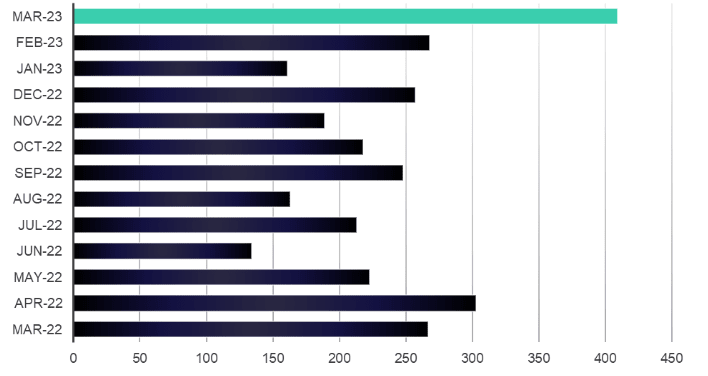
Figure 2: Ransomware activity by month since March 2022
Extortionist Exclusivists Take a Break
Despite the bonanza of ransomware attacks, extortion-only attacks diminished substantially: by 90%. We’re talking about threat groups that steal data, threaten to leak it on data-leak sites, and then don’t end up encrypting files. The break in extortion-only activity can probably be explained by the leading extortion group, “Karakurt Hacking Team,” being largely inactive.
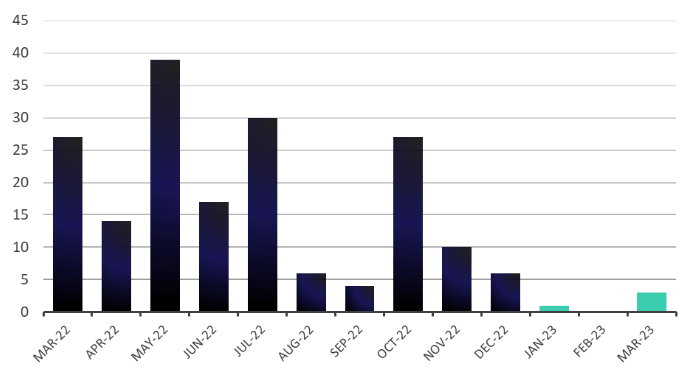
Figure 3: Extortion activity by month since March 2022
This doesn’t mean that extortion-only attacks are out of style. The numbers analyzed are limited to confirmed extortion groups that name victims on data-leak sites, and there are hundreds of threat actors who steal data and instead expose organizations on underground cybercriminal forums, such as XSS or Exploit. Plus, Clop’s most recent campaign, targeting GoAnywhere flaws, could be considered an extortion-only campaign.
Who Fell Victim?
Consistent with previous quarters, the lion’s share of ransomware attacks targeted organizations operating in the US: 45.6% of all ransomware victims named on data-leak sites were in the US. Canada and European countries took the remaining four spots in the top-five most-targeted countries list.
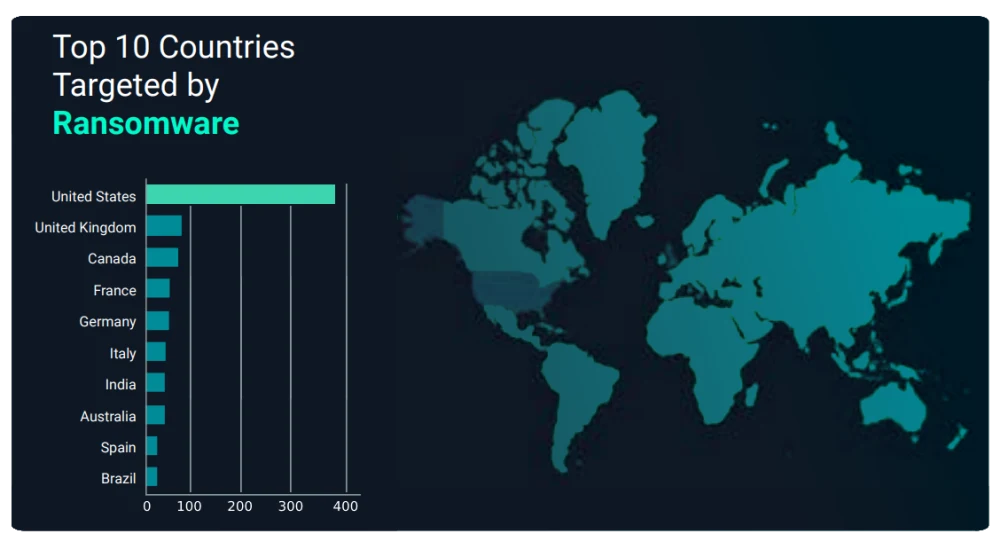
Figure 4: Most targeted countries by ransomware attacks in Q1 2023
The distribution of victims by sector was more equal, although the industrial goods and services sector remained the hottest target with 21.1% of all victims. A rise in healthcare industry attacks was a notable finding; over 30 healthcare organizations were named on data-leak sites in March 2023. That’s more than we’ve observed over the past four quarters.
Digging Deeper
Our full quarterly ransomware report offers:
Comprehensive analysis of ransomware activity in Q1 2023
Intelligence on the most active ransomware groups this quarter, including background information, TTPs, and victimology
MITRE ATT&CK techniques to provide insight into the TTPs used by top ransomware groups
Breakdown of ransomware targeting, by sector
Analysis of the most targeted countries
General recommendations to protect against ransomware
Ways to protect yourself against ransomware with ReliaQuest’s help
You can also check out other ransomware-related blogs, such as our analysis of a Qbot campaign that ended with Black Basta ransomware and a SocGholish FakeUpdates campaign aimed at deploying ransomware. In addition, our threat research podcast, ShadowTalk, provides weekly discussions of new ransomware and cybercrime.