Staying on top of vulnerability trends is crucial, as cyber-threat actors frequently exploit new and old vulnerabilities for wide-scale attacks, not to mention data theft and extortion. These über-exploiters are also known to collaborate. Knowing the trends of their behavior can reveal which Common Vulnerabilities and Exposures (CVEs) to prioritize.
The ReliaQuest Threat Research Team monitors vulnerabilities daily, assessing their impact and formulating steps to mitigate the risks they pose. Over the first quarter of 2023 (Q1 2023), we identified 6,977 newly created vulnerabilities. Scroll on for a comprehensive analysis of the key flaws that have surfaced—and created a buzz on forums—in 2023 so far. Their impact on the overall cyber-threat landscape is undeniable.
Vulnerabilities Snapshot
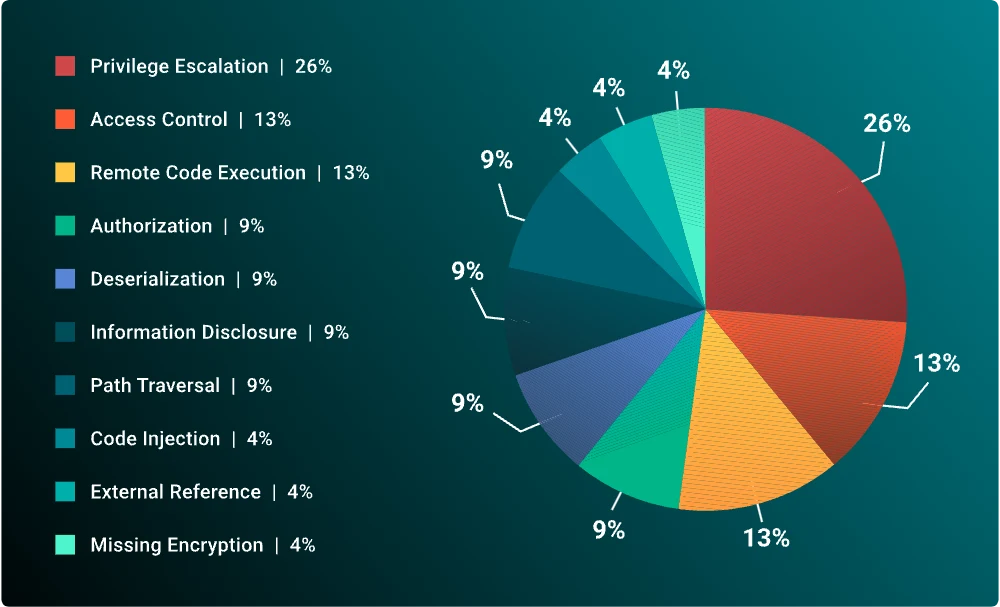
In Q1 2023, almost 7,000 new CVEs were discovered, and threat actors continued to exploit older vulnerabilities in unpatched systems. Privilege escalation was the most exploited type, surpassing memory corruption (the leader in Q4 2022).
6,977 new CVEs were identified, an 11% increase from Q4 2022.
ReliaQuest GreyMatter Digital Risk Protection revealed that threat actors had exploited 29 of these new vulnerabilities in the wild (on public, real-world machines), a 16% increase from Q4 2022.
The US Cybersecurity and Infrastructure Security Agency (CISA) added 37 vulnerabilities to its Known Exploited Vulnerabilities Catalog.
Microsoft had the greatest number of new known exploited CVEs (8), followed by Fortra (3).
Threat actors focused on exploiting new classes of CVEs this quarter, most commonly privilege escalation vulnerabilities (26%), followed by access control vulnerabilities (13%) and remote code execution vulnerabilities (13%). Exploitation of all three types jumped since Q4 2022. Exploitation of memory corruption and type confusion vulnerabilities dropped.
Exploitation in Q1 2023
We observed vulnerabilities being exploited by nation-state threat groups, such as “APT28” (aka Fancy Bear), and ransomware groups, including “Clop” and “IceFire.” Clop’s exploitation of a GoAnywhere vulnerability led to 100-plus organizations being compromised and data leaked.
Breakdown of the top 10 vulnerabilities in Q1 2023
Hot Target: CVE-2023-23397
One of the most significant new vulnerabilities to emerge in Q1 2023 was the Microsoft Outlook Elevation of Privilege Vulnerability (CVE-2023-23397). It’s found in all versions of the Microsoft Outlook desktop application, on any Windows system.
This one’s especially dangerous because it’s so simple to abuse, and it’s also a zero-click exploit—no user interaction is needed to trigger exploitation. An attacker need only get their hands on sensitive credential hashes to send a malicious email to the target.
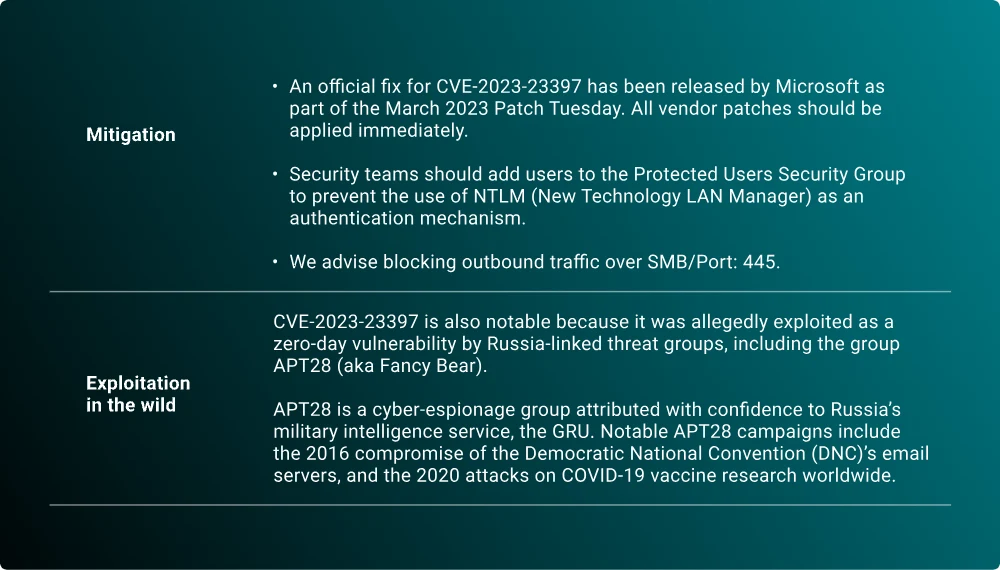
This flaw’s best-known exploiter is APT28, a highly sophisticated advanced persistent threat group attributed to Russia’s General Staff Main Intelligence Directorate (GRU). The nation-state group has reportedly been active since as early as 2004, waging attacks aligned with Russia’s strategic political interests.
Remember the 2016 compromise of the Democratic National Convention (DNC)’s email servers? APT28. And the 2020 attacks on COVID-19 vaccine research organizations worldwide? APT28 again. We see this group as a highly capable threat to organizations in a whole host of sectors—aerospace, defense, energy, government, and media among them.
Finding Flaws
Protecting against vulnerabilities is more than just patching. Organizations should also be implementing a defense-in-depth strategy, to reduce the risk of cyber attacks that exploit vulnerabilities.
The robust ReliaQuest GreyMatter Detect library covers all phases of the attack lifecycle, and helps customers strive for comprehensive coverage. Post-exploitation, we’ve discovered a handful of techniques that threat actors favor; use the following insights to identify coverage gaps in your environment and pursue detection.
PowerShell Execution Policy Modified
Attackers often need to modify the registry to execute malicious scripts on recently compromised machines. This can be a precursor to post-exploitation activity.
T1112 – Modify Registry
T1562 – Impair Defenses
0001 – Disable or Modify Tools
RDP Enabled via netsh
An attacker might use the netsh utility to open remote desktop protocol (RDP) on a host, to gain remote access to that host. Opening RDP with netsh can trigger detections that should be placed under heavy scrutiny, as RDP should only be enabled on a case-by-case basis.
T1059 – Command and Scripting Interpreter
001 – PowerShell
003 – Windows Command Shell
004 – Disable or Modify System Firewall
Local Admin Created
Administrator (admin) accounts created or enabled locally may mark unauthorized attempts to create persistence in a system. This alert detects when an admin account has been created or enabled locally on a system.
003 – Local Accounts
T1098 – Account Manipulation
001 – Local Account
Recon Commands
Threat actors often use PowerShell or the command prompt to enumerate device, domain, and user information. Detection rules can be built around these uses to identify attackers.
T1007 – System Service Discovery
T1057 – Process Discovery
T1087 – Account Discovery
Digging Deeper
Our full quarterly vulnerabilities report offers:
Comprehensive analysis of vulnerabilities
Overview of the most mentioned CVEs
Analysis of cybercriminal discussions
Data on the active exploitation of new vulnerabilities
Insights into vulnerabilities targeting certain technologies
General recommendations to protect against vulnerability exploitation
Ways to protect yourself against vulnerabilities with ReliaQuest’s help
You can also follow our threat research podcast, ShadowTalk, for weekly discussions of new vulnerabilities and cybercriminal activity.