Disclaimer: Before analyzing the IC3 data, it’s important to note that the data reported by the FBI in the IC3 report is based solely on the complaints they received. The actual number of online fraud events is likely much larger, as some cases may have been reported elsewhere or gone unreported altogether.
Every year, the FBI Internet Crime Complaint Center (IC3) produces a crucial resource for tracking and analyzing internet crime trends: A report summarizing the internet crime complaints received during the previous year. The IC3’s aim is to help others understand trends in internet crime and raise awareness about the risks involved in online activities. The 2022 report has just been released, and the ReliaQuest Threat Research team found it fascinating. And alarming.
As more and more people spend time online, the risk of falling victim to internet crimes is increasing. The annual IC3 report provides valuable insights into the types of crimes that are prevalent—details of the crimes reported, financial losses incurred, victim demographics—and cybercriminals’ methods.
Let’s take a look at the report’s key findings related to business email compromise (BEC) and ransomware. How can they help individuals and organizations looking to protect themselves from internet crime?
Beating Fraudsters at the BEC Game
During 2022, the IC3 received 21,832 complaints related to BEC—that’s cybercriminals targeting organizations to commit online fraud. They do this by impersonating a trusted individual (e.g., a CEO, a CFO, another high-ranking executive, etc.) to trick an employee into transferring funds or providing sensitive information. Often, the communications convey a sense of urgency, such as a request to quickly transfer funds to a vendor or partner. If the employee falls for the scam, the funds move to a fraudulent account and disappear along with the cybercriminal.
Those 21,832 complaints to the IC3 reflected adjusted losses of more than $2.7 billion. They also reflected a slight increase in the number of cybercriminals targeting victims’ investment accounts, rather than traditional banking accounts. There was also an increase in BEC scammers’ use of spoofed phone numbers to confirm fraudulent banking details with victims.
BEC scams are particularly insidious internet crimes because they’re highly targeted. The dedicated cybercriminal often takes the time to research targets, to create convincing emails and employ other social engineering tactics. The fallout of BEC can be substantial financial loss, but also damage to the victim organization’s reputation.
Businesses should train their employees to recognize and avoid BEC scams and to implement safeguards—such as multi-factor authentication—to prevent unauthorized fund transfers or sensitive-information disclosures. The IC3 report has also revealed the need to establish procedures for staff to verify payments and purchase requests outside of email communication. An alternative is to directly call a known, verified number, rather than relying on information provided in email correspondence.
We’ll explore BEC attacks ReliaQuest has observed in an upcoming blog, so stay tuned for that.
Business Email Compromise by the Numbers
22K
Complaints
The FBI IC3 received nearly 22,000 business email compromise complaints in 2022.
2.7B
Losses
These incidents resulted in $2.7 billion in losses for businesses affected.
Ransomware: Stop the Spread
According to the FBI’s IC3 report, 2,385 complaints related to ransomware in 2022, which brought adjusted losses of over $34.3 million. According to the FBI, the top avenues of initial victim compromise were phishing emails, remote desktop protocol (RDP) exploitation, and software vulnerabilities. The FBI also confirmed that the “double extortion” technique—pressuring victims to pay by threatening them to publish stolen data online—is becoming more widespread among ransomware operators.
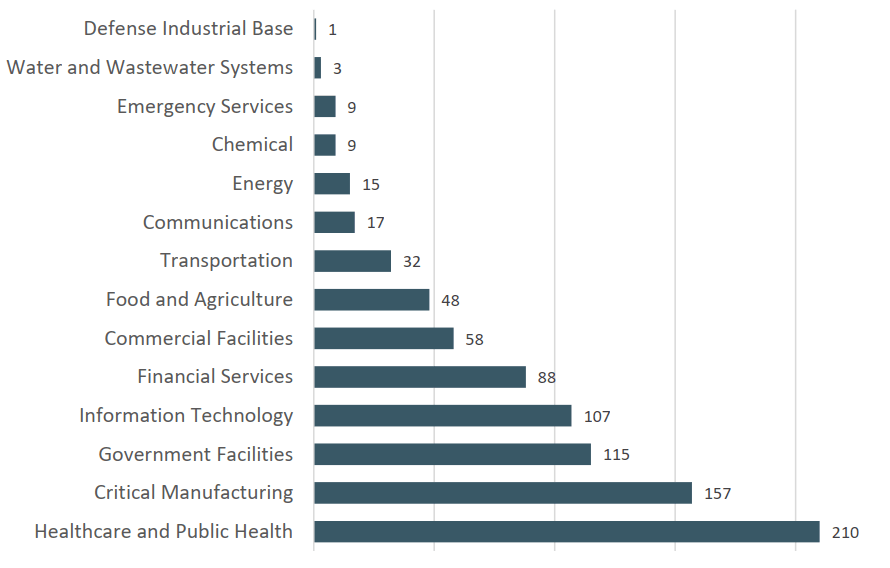
In 2022, the FBI received 870 ransomware complaints from organizations operating in critical infrastructure sectors. The top ransomware types affecting those sectors, as reported to the IC3, were “LockBit” (149 complaints), “ALPHV” (114), and “Hive” (87).
To mitigate the threat of ransomware attacks, strap in to a comprehensive backup strategy:
Regularly back up important data.
Store the backups in offsite or isolated systems.
Test the backups regularly to ensure data is recoverable.
Implementing network segmentation and access controls, using strong passwords, and applying software patches and updates are also key prevention measures. Plus, just as for BEC, your staff can be part of your anti-ransomware strategy: Ensure they can identify and report phishing emails, and disable or limit their RDP access.
In the dreaded event that you are hit with ransomware, you’ll thank yourself for having put an incident-response plan in place and will be ready to isolate infected systems so the malware doesn’t spread. But don’t forget to report the attack to the appropriate authorities, such as the FBI’s IC3; that’s how these internet crimes are investigated and attackers prosecuted.
Ransomware by the Numbers
2.3K
Complaints
The FBI IC3 received nearly 2,400 ransomware complaints in 2022.
34M
Losses
These incidents resulted in $34.3 million in losses for businesses affected.
149
Lockbit Incidents
Number of ransomware complaints from critical infrastructure sectors in 2022 that mentioned "LockBit."
Why It Matters
Understanding the risks of internet crime is essential for CISOs—not to mention online shoppers, social-media users, business owners, and anyone who’s ever used the World Wide Web. The IC3 report is an excellent place to further your education.
To keep monitoring for BEC, ransomware, and other online fraud developments, consider how ReliaQuest can use threat intelligence to support your security operations, now with the added benefit of GreyMatter Digital Risk Protection. Get more details about our threat intel, and see how we’re harnessing it to monitor the developments of these online frauds by requesting a demo.