
Read The Case StudyWith GreyMatter, my team doesn’t have to do a lot of chair swiveling; we can see everything happening on one platform, which has enabled us to quickly identify and respond to threats.Christine VanderpoolCISO, Florida Crystals
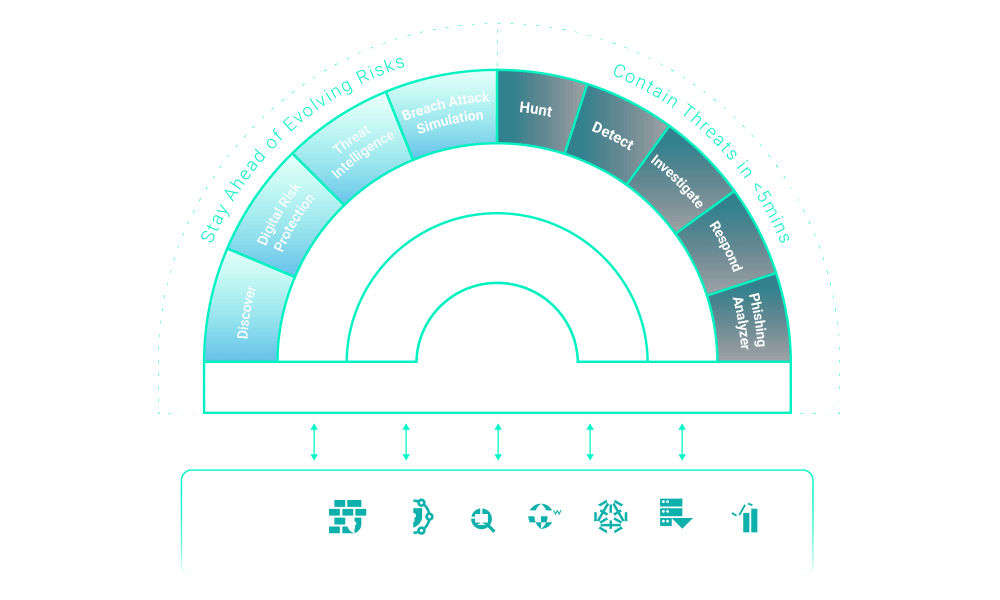
Contain Threats in Under 5 Minutes
The only technology-independent agentic AI platform designed to contain cyber threats across any architecture.
ReliaQuest GreyMatter contains threats in under 5 minutes so you can stay ahead of evolving risks. And it's built with the modularity to work with your unique architecture—now and in the future.
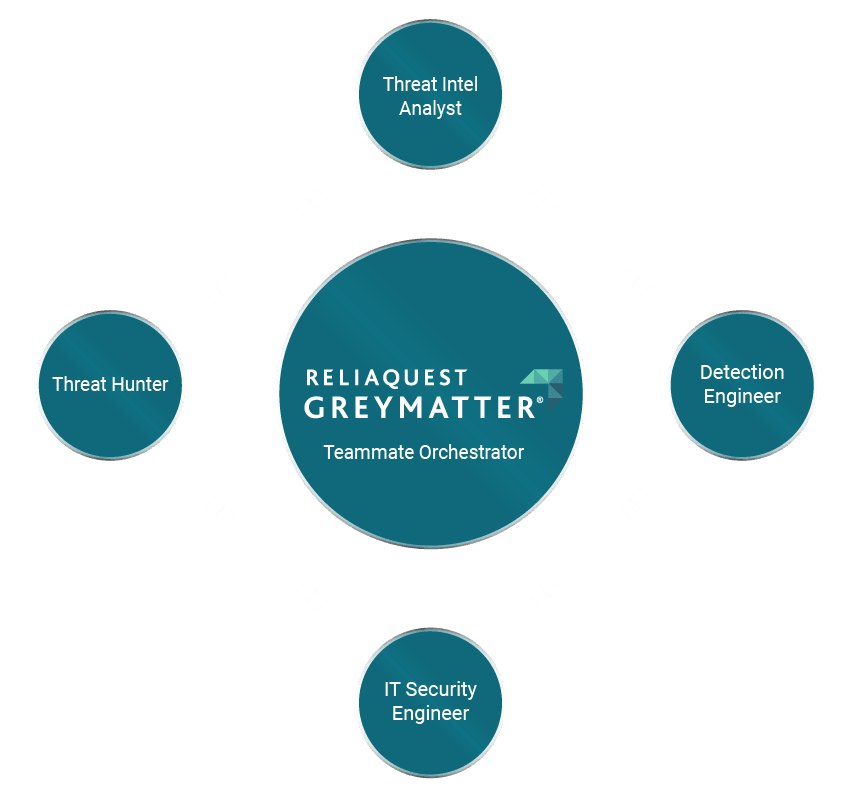
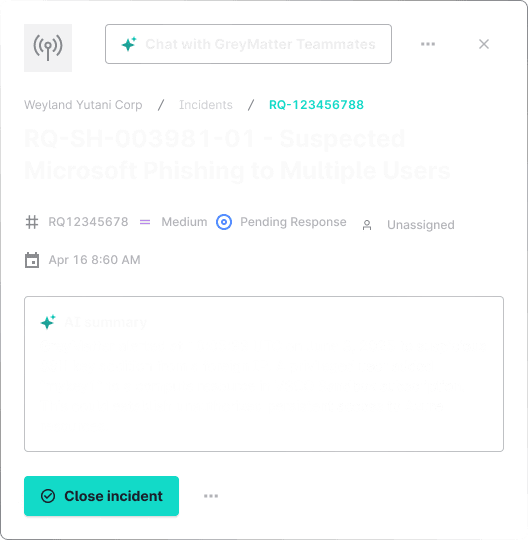
Put autonomous Agentic Teammates to work to exponentially expand the impact of your security operations team
Detect faster by uncovering threats at the source—no storage tools needed
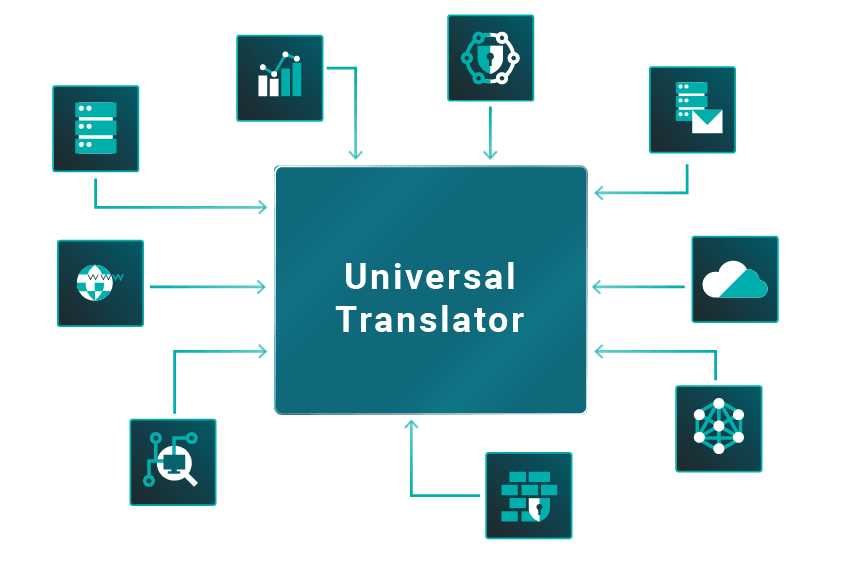
Turn fragmented telemetry into unified context by connecting your tech from one unified source


GreyMatter’s Universal Translator automatically normalizes, stitches, and correlates data from across your stack to deliver full-context detection and response.
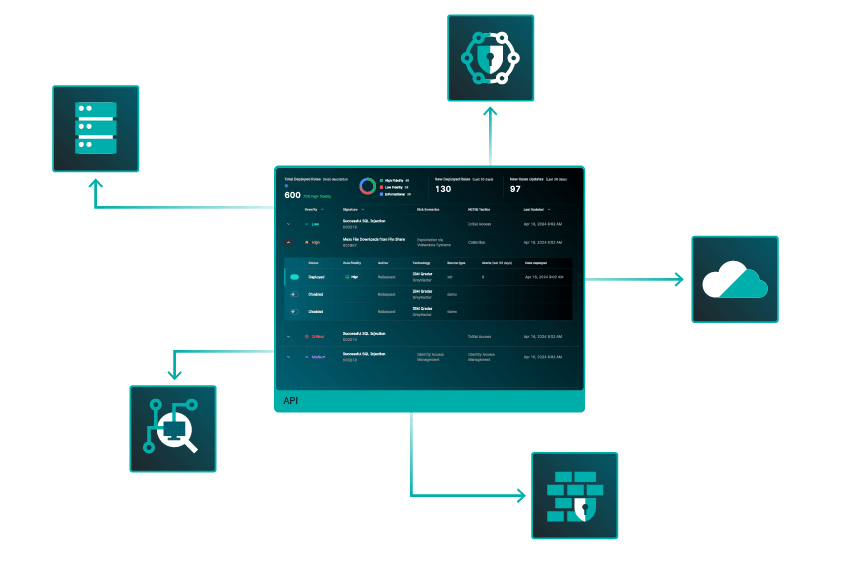
GreyMatter is the agentic AI security operations platform that breaks you from reactive SecOps and frees you to focus on what matters.
GreyMatter connects directly to your source technologies, reducing storage costs and expensive queries with smarter at-source detection.
You’ve held the line long enough. It’s time to lead the offense with GreyMatter’s Agentic Teammates—role-based AI agents that exponentially scale security operations teams.
Automated Security. Optimal Results.
Return on Investment
Reduction in MTTR
Mean Time to Contain

Learn How GreyMatter Measures and Improves Your Security Operations
The GreyMatter security operations platform removes duplicates and delivers unified detection content and coverage for high-fidelity, enriched alerts. GreyMatter enables your team to boost its efficiency, reduce burnout, and better manage risk.
