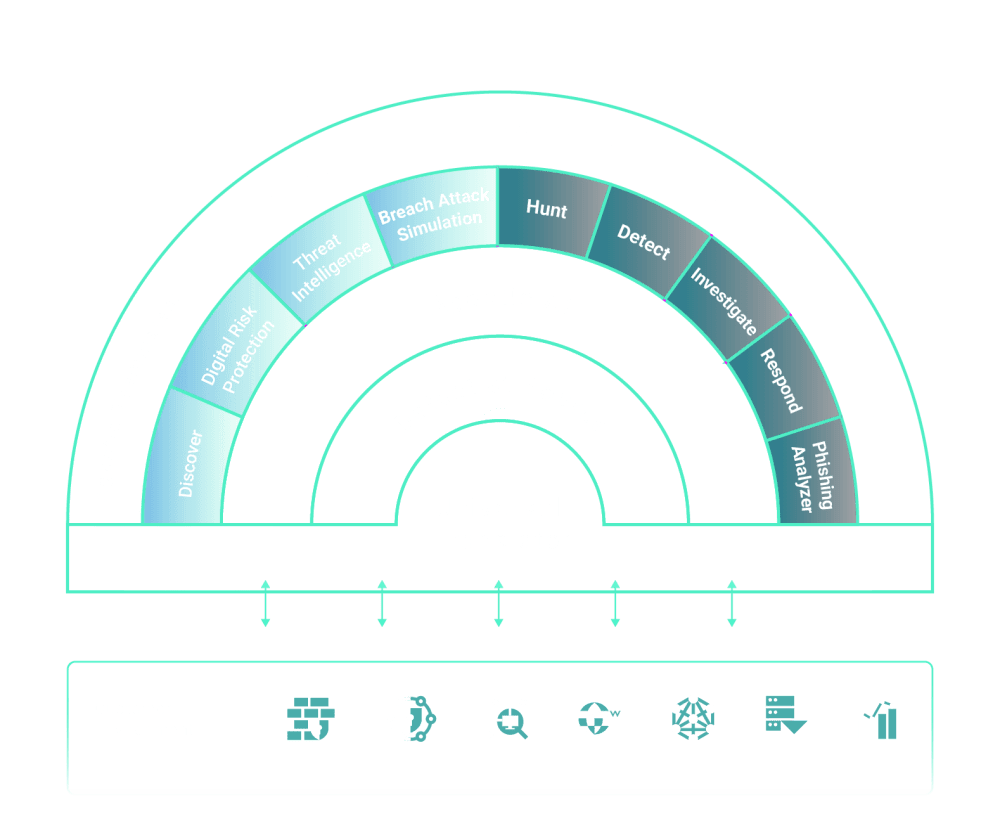
The Agentic AI Security Operations Platform
Cybersecurity is complicated, but your operations shouldn't be. Stronger security is possible with an agentic AI security operations platform that unifies your data and eliminates the chaos caused by fragmented tools.
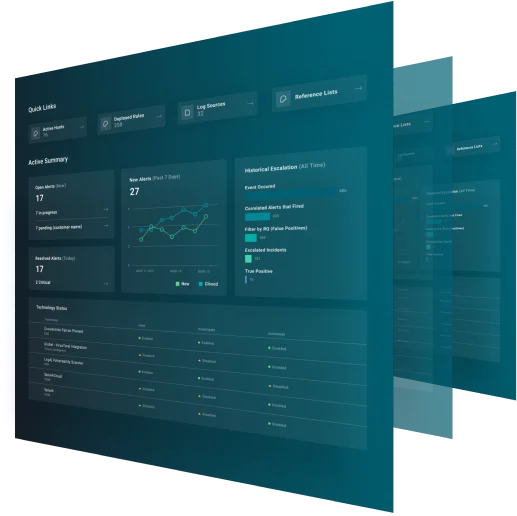
Your Security Tools, Connected by GreyMatter
GreyMatter connects telemetry from across all your technologies to accelerate your SecOps, from threat prevention to response.
Prevention
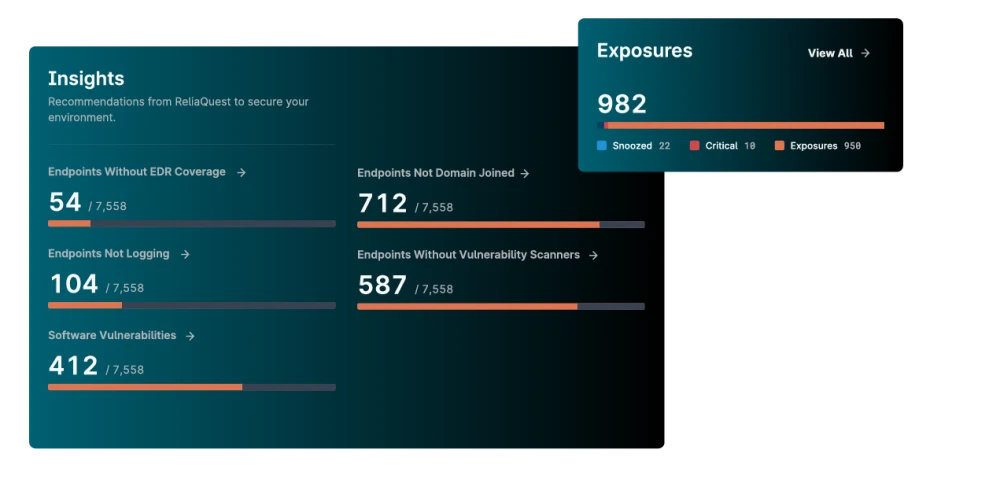
Understand and act on internal and external risks facing your environment.
- Safeguard your brand online. GreyMatter Digital Risk Protection continuously monitors the open, deep, and dark web for data leaks, malicious mentions, and more.
- Automate asset discovery, uncover gaps, and prioritize risks using AI with GreyMatter Discover.
- Protect your organization with tailored, actionable threat intelligence.
Detection
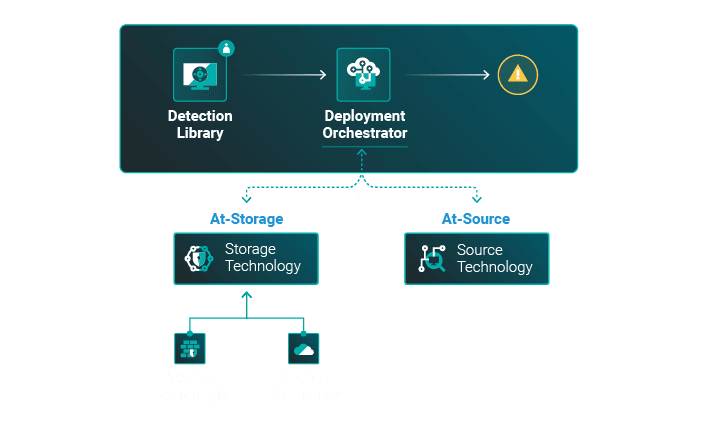
Detect at-source to bypass workflow bottlenecks.
- Skip the SIEM and uncover threats faster directly at-source.
- Build and deploy detections to all your tools with a single click using the GreyMatter Deployment Orchestrator.
- Maintain detection effectiveness before and after deployment with GreyMatter's continuous detection validation.
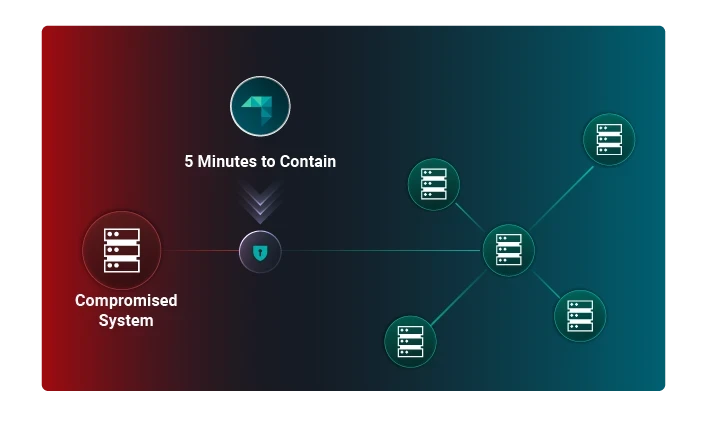
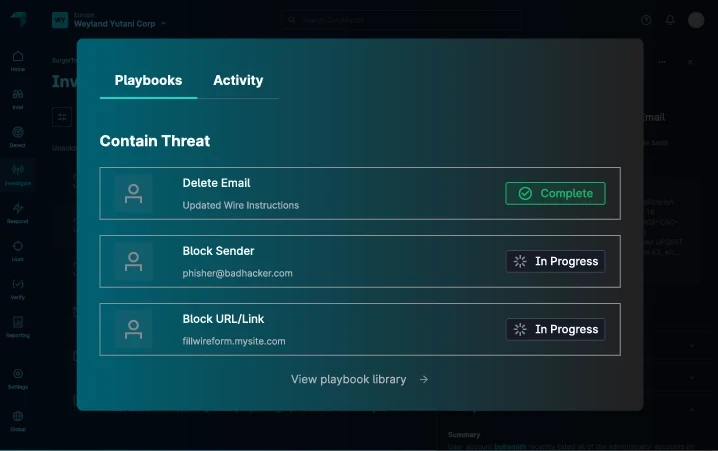
Containment
Contain threats in 5 minutes or less—43 minutes faster than most attackers achieve lateral movement.
- Isolate a host, block an IP, or ban a hash within seconds.
- Hit the ground running with pre-built containment playbooks.
- Contain threats across multiple architectures at once.
Investigation
Let GreyMatter handle the Tier 1 and Tier 2 work no human should have to do.
- Leverage an agentic AI SecOps platform for hands-free investigation and response.
- Uncover hidden threats or hygiene gaps with pre-packaged threat hunts.
- Let GreyMatter Phishing Analyzer evaluate user-reported phishing emails in seconds.
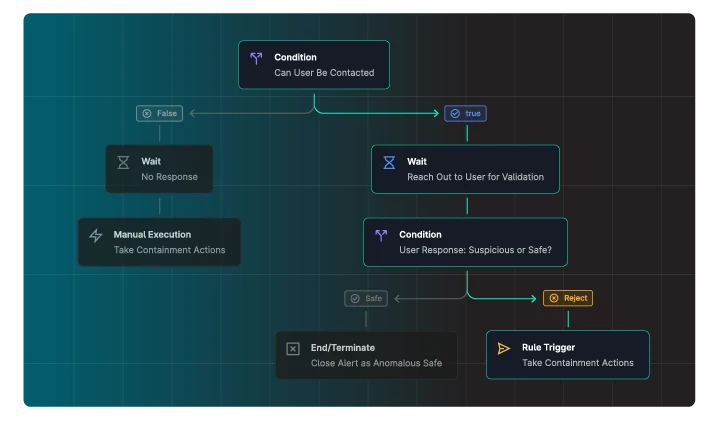
Response
Achieve rapid, consistent responses that keep your team aligned.
- Design configurable workflows to automate repetitive business processes—no coding required.
- Isolate hosts, block IPs, and more directly from your phone using the GreyMatter Mobile App.
- Get real-time insights into your environment when and where you want them using the GreyMatter Notification Center.
Why GreyMatter Is the Right Choice
The GreyMatter security operations platform helps the world's most trusted brands secure their environments using industry-leading proprietary technologies.
- At-source Detection
- Collaborative, Multi-Agentic AI
- Universal Translator
Reinforce Your Security Ecosystem with GreyMatter
Seamlessly integrate GreyMatter into your existing security operations tech stack to enhance visibility across your tools and gain the context and insights you need to operationalize security and protect your business.
See Integrations








Your AI SOC Made Possible with ReliaQuest GreyMatter
Using your existing tool set, GreyMatter applies AI and automation to alert ingestion and provides automated alert containment, all within 5 minutes of detection.