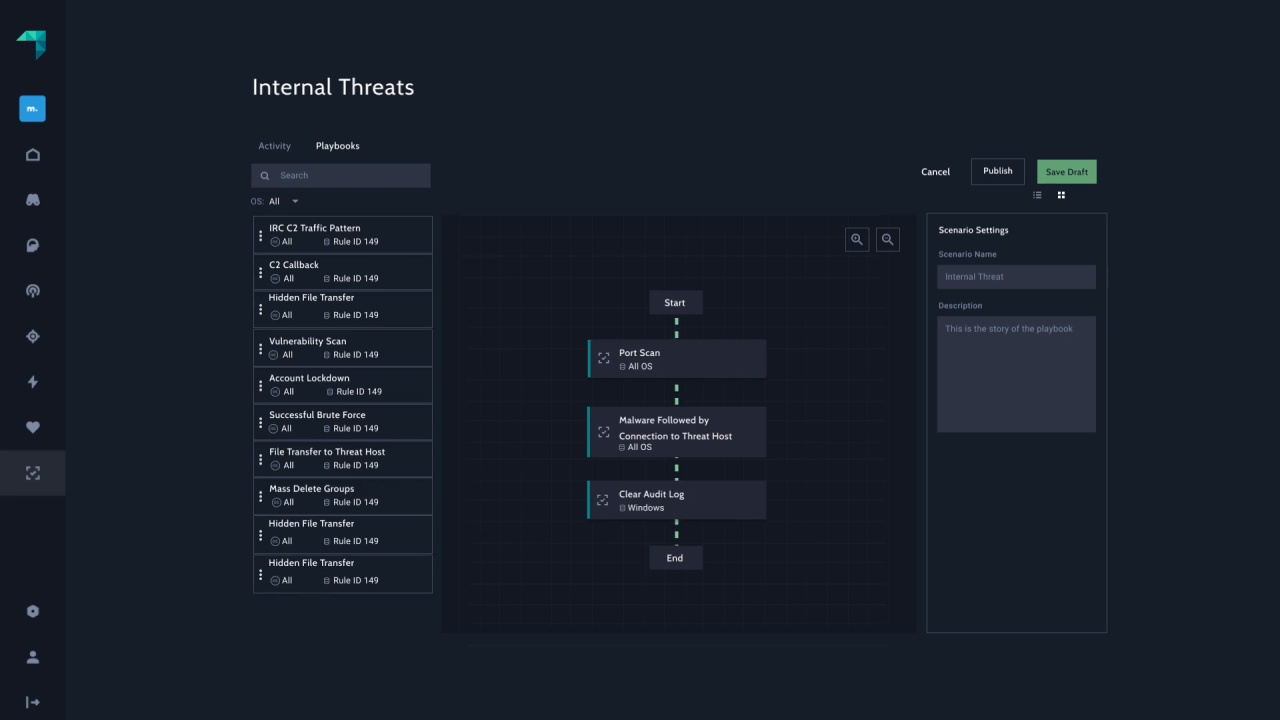
Map Coverage Against MITRE ATT&CK®
Verify maps threat coverage to security frameworks such as MITRE ATT&CK, enabling visualization of your threat coverage and gaps.
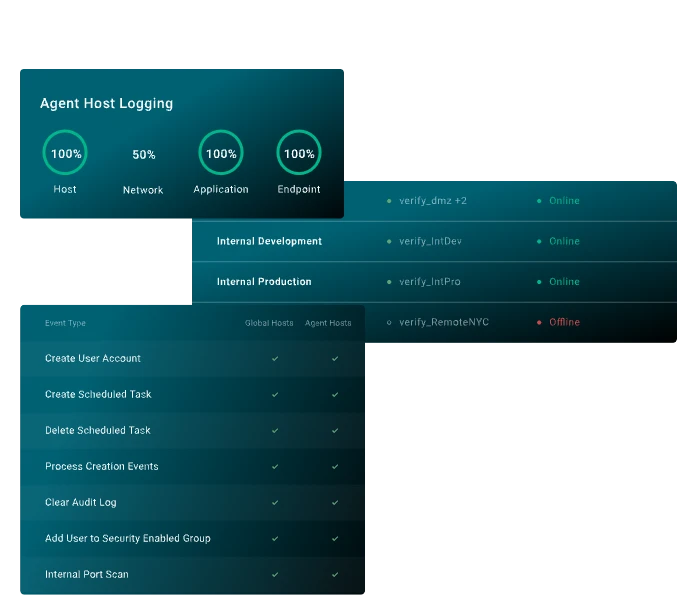
Validate Effectiveness of Your Security Controls
Confirm that your security tools are working together and are always up to date.
Scale BAS to Turn “Unknowns” Into “Knowns”
Streamline BAS by certifying integrations across 80+ security tools, cloud and on-prem infrastructure apps to understand gaps that might preclude you from responding to an attack.
Evaluate Security Investments
Effectively evaluate whether new security controls will perform and complement existing investments.