I’ve got some good news and some bad news.
The bad news is that I’ve been receiving a lot of phishing SMS messages over the past months. Unauthorized bank transfers, suspicious crypto account activity, DMV notices. The whole shebang.
The good news? You get to read my new cathartic blog on smishing.
What is Smishing?
Smishing involves the use of unsolicited text messages purportedly from a legitimate company requesting personal, financial, and/or login credentials (not by definition, but the FBI’s). Remediating smishing risks is a core component of many threat intelligence or brand protection programs.
Despite a smattering of arrests by law enforcement, smishing is thriving. In this year’s IC3 Report, the FBI added Smishing to it’s calculations. Combined with Phishing, Vishing and Pharming, this year’s IC3 report calculated that smishing led to losses in excess of $54 million.
Others have suggested that all this remote work has led to an uptick in the success of Smishing, with attackers experiencing greater success targeting mobile users.
Harvest Credentials
The clear and obvious primary goal for smishing attacks is to capture the credentials of a user’s account. Ideally, this would be something topical and with an element of urgency to it. This is often a bank claiming an unauthorized transaction, or suspicious activity associated with an account. In the example below, you can see an example of the latter.
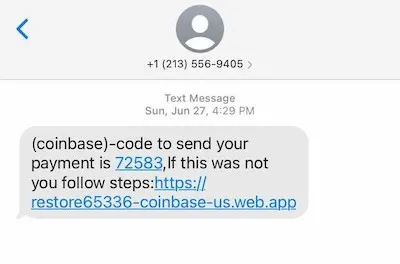
A Smishing example I received in June
Of course, more convincing phishing attempts will require more convincing URLs. For those interested, we have written a guide on domain monitoring that you can check out for all the different techniques attackers use to impersonate the domains of their victims’.
This isn’t just about cybercriminals hunting for account credentials. Back in January, CERTFA reported on a campaign by APT35 (aka Charming Kitten or Phosphorus). The group distributed smishing texts stating users would need to authenticate their Google account by following an embedded link. APT35 would harvest credentials and use the accounts to access other sensitive information.
Phishing is a proven technique for threat actors across the spectrum, and SMS is a highly effective way to deliver the malicious link.
Banking Trojans
Just last week, I received a Tipper from the Photon team about a new Android banking trojan offered on a Russian-speaking cybercriminal forum–AbereBot (screenshot below). In this case, an XSS (a criminal forum) user advertised a Telegram-hosted banking trojan that targeted hundreds of banking applications. In order to deploy malware on a mobile device, actors often rely on phishing via SMS.
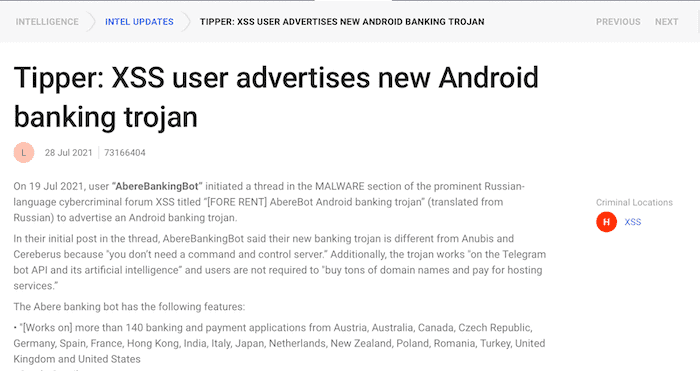
SearchLight Intelligence Tipper on a new Android Banking Trojan
This is just one recent example, and barely a month goes by without another Android malware making news headlines. Back in January, for example, FluBot was reported to have spread quickly and significantly across targets. This malware was installed by SMS, in this case purporting to be from a delivery company providing a package tracking link. Users were prompted to download an application that would enable them to track the package, however, the malicious application enabled the attacker to capture banking credentials.
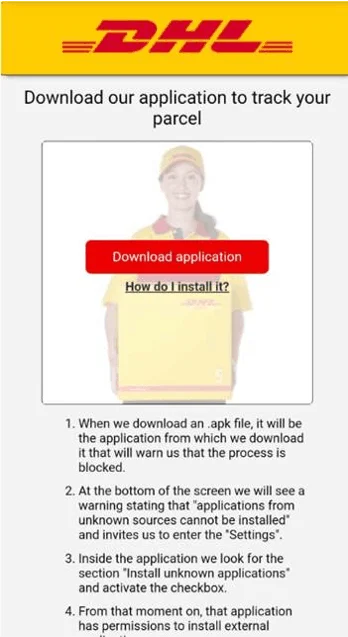
A screenshot of the prompt to download the fake delivery app
Combatting Smishing Risks
For users concerned about smishing attacks, the NCSC have produced some great guidance as part of the FluBot alert. This includes:
Only download apps from App Stores, such as the Android Play Store.
If you suspect you have clicked on a malicious link, reset your device to factory settings and reset credentials of any accounts that you have entered since the infection.
Even non-Android users should be cautious of clicking on links that may be attempting to capture credentials.
Beware of unsolicited texts using high pressure tactics that introduce urgency, such as closing accounts or transferring funds, for example. When in doubt, go to the full website of the company and check notifications for your accounts there.
Beware of anything that forces you to log in to unrelated services, such as entering banking credentials to receive a package.
Always treat a message offering “something for nothing”, such as winning money or prizes, as suspect, especially when you need to provide financial or other sensitive information.
For organizations that wish to protect their customers, there are additional steps. The good news is that these domains can be taken down, as well as the telephone numbers associated with them. A mature domain monitoring program will clearly have added benefits to those impersonating domains delivered via SMS.
Security teams can also access a feed of malicious domains associated with banking trojans, such as Flubot shown below.
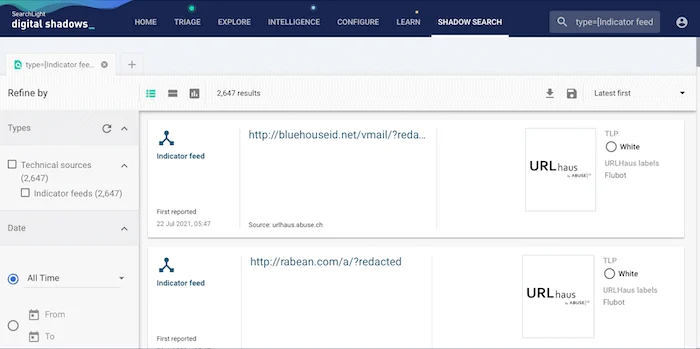
Consuming threat intelligence feeds pertaining to Flubot within ReliaQuest GreyMatter DRP
Smishing may be an effective extension of traditional phishing, but there is still plenty organizations and end users can do to reduce the risk posed by actors using SMS as part of their campaigns.
To learn more about the latest malware advertised across criminal forums, and other threat intelligence, you can sign up for Test Drive to explore ReliaQuest GreyMatter DRP yourself free for seven days.





