I’m not one for cheesy belief statements, but one of Warren Buffet’s, “It takes years to build a reputation and seconds to destroy it,” certainly rings true in information security. Though Warren Buffet was not likely referring to information security, the reality is that the loss of customer trust, which often stems from breaches or cyberattacks, can derail an organization entirely. These days, derailment is made even more likely as a result of the digital economy.
Organizations are now required to have an online presence for the purposes of growing the brand, increasing reach and overall exposure, or face going offline for failing to do so. While this can be incredibly exciting from the perspective of the brand and marketing teams (and business leaders), this presents a new type of security challenge for information security professionals – who must create defense off the back of any threats emanating from social media and the internet, in general. The reality is that being online creates new threats – and those responsible for protecting the organization must react with increased speed and skill to stay ahead of the game.
Online Brand Protection Defined
Effective online brand protection requires continual monitoring and remediation of threats to a company’s brands across social, mobile, websites, and other external sources. This approach often requires the involvement of the security, marketing, brand, and legal teams.
While approaches to online brand protection once amounted to tracking negative sentiment on Twitter, this is no longer enough.
This blog will outline the top threats to brands we see online, and some of the best practices for protecting them. Before this, however, let’s first remind ourselves why we should even care at all.
Top 3 Impacts of Brand Attacks
Brand damage occurs when there is a loss of customer trust or when the image of the brand is tarnished. Such an outcome can be driven by counterfeit products, negative publicity and, more significantly, breaches.
A notable example of a brand affected by brand damage is Equifax, who were responsible for allowing one of the largest breaches in 2017 to occur, affecting 143 million individuals. Damage for Equifax took form in financial loss and reputational crisis. For example, a financial statement issued by Equifax in 2019, highlighted that in the first half of 2019, company revenue was down 2 percent, compared to the first quarter of 2018, as a result of the 2017 cybersecurity incident. Overall, the breach cost the company $1.23 billion. The scale of the breach and the financial damage has meant Equifax’s cyber incident has not escaped scrutiny.
Attacks on brands have other, tangible impacts on both the organization and the individual. Here are the top three:
Loss of Customer Trust: It’s estimated that for global brands, a lack of trust can cost up to $2.5 trillion per year. Lack of trust directly impacts a firm’s reputation – and this counts for everything in the digital era. Trust can be composed of several factors – such as customer service, reliability, vision and security. In terms of security, a breach can significantly affect how customers perceive the brand – and as a result, consumers may choose to look elsewhere, for safer and more viable options. To support this notion, Ping Identity revealed that consumers would make drastic changes to the way they interact with a brand following a breach.
Financial Loss: In addition to customer trust, brand attacks can result in direct financial loss – for the customer and the organization! It’s estimated that business email compromise attacks, typically identified as a scam to entice organizations to transfer funds illegitimately, cost $26 billion in 2019 – and that’s just business email compromise. In the European Union, too it’s worth taking into account the regulatory fines, such as the General Data Protection Regulation that stems from a breach – something which shouldn’t be overlooked, with maximum fines of €20 million euros or 4% of global turnover. To date, GDPR has led to more than $126 million in fines.
Competitive Disadvantage: Two of the aforementioned examples can directly impact how a company performs – and depending on the competitiveness of industry – such factors can stifle competitiveness within the market.
Brands Under Attack: Impersonation
The film Catch me if you can can teach us a thing or two about impersonation, which sees Leonardo Dicaprio impersonate a pilot. In its true form, impersonation is the act of pretending to be something or someone, in order to entertain or defraud. While not all impersonation looks as glamorous as Leonardo Di Caprio in Catch Me if You Can, the reality is that brand impersonation employs similar tactics, and can come in many guises, so let’s take a look at some examples.
1.Domain Impersonation
The most commonly known form of impersonation is a spoof domain, which sees a threat actor use a domain to mimic a brand. In its most basic form, a spoof domain can simply involve using the brand name or can extend to hosting content that mimics the brand. Attackers will employ such a tactic to engineer the end user into thinking that the content is legitimate. A spoof domain can be created for anything, even political candidates, as Digital Shadows Photon Research identified (who do, yes, count as brands), but – perhaps more commonly known – domain spoofs are widely associated with and created to impersonate organizations, regardless of how renowned the brand is.

*Figure 1:*Domain Impersonation examples
That said, while any brand can be impersonated, some brands are impersonated (and potentially used for malicious purposes) more than others, as a result of the industry and brand presence. Notably, research conducted by Digital Shadows Photon Research team observed, on the criminal forums and marketplaces, that phishing templates, for investment firms, were the most expensive phishing templates on offer – proving that some industries are more valuable than others. In addition to this, research independent of Digital Shadows, conducted last year, indicated that Paypal remained one of the most-spoofed brands in phishing, suggesting that brands with global reach face unprecedented brand attack. Both the type of brand and the industry in which they reside, can therefore be seen likely to determine the likelihood of impersonation.
2. Social Media Account ImpersonationFake social media accounts are not the only phenomenon causing the social media giants a bit of grief.Organizations are seeing their brands used by threat actors to entice customers by promising them a deal that’s too good to be true. Much like a domain, the social media profile will use the brand name and/ or logo, however, the extent of impersonation depends on the willingness of the threat actor to make the impersonation like-for like.This type of impersonation is all too common; adversaries will mimic support accounts on Twitter in an attempt to redirect customers to malicious sites. You can read more about a twitter account impersonation tactic here.
3. CEO or Company Executive ImpersonationThis type of impersonation relies on a company executive to entice lower-level employees into releasing funds or sensitive documents. That said, it doesn’t even have to be a company executive; even suppliers can be impersonated.One notable and recent illustration of the damages an organization can incur, as a result of executive impersonation, is the case of Nikkei,. 2019, Nikkei lost $29 million to scammers who tricked an employee into thinking the sender was a business executive. Nikkei is not alone in this – impersonation can happen to any organization, even Digital Shadows!Figure 2: Example of a typical BEC attemptWhile spoofing of executives is common in email campaigns, it also surfaces on social media. Attackers and fraudsters often register fake social media profiles, which can be highly valuable for targeting employees and customers.
4. Mobile Application Impersonation
As the usage of mobile devices continues to increase, organizations are turning to mobile applications that enable them to better interact with their customers and provide new tools for employees. Unfortunately, cybercriminals also want to communicate with your customers and create spoof mobile applications that seek to harvest their information.
Brand Protection: Is It a Job for the Information Security Team or Marketing?
So far, we’ve identified the potential impacts and most common threats around online brand protection. However, which stakeholders should own protecting the brand – information security professionals or marketing gurus? To identify this, it’s worth understanding the true goals of each stakeholder:

Figure 3: How the security, marketing and compliance teams should work together (An Example)
While every organization does have a different organizational makeup, loosely identifying goals of each department, as we did above, helps build a clearer image of who should be taking ownership of brand protection. Given that protecting the organization falls under the umbrella of security, and that brand protection is now regarded as a security issue, the job of protecting the brand can be owned by those within the security department. That said, such responsibilities should not be siloed to the security department, but rather the marketing team – who will be responsible for increasing exposure, via marketing campaigns – must work with the security department. Collaboration and cross-functional team work is key. Later, we’ll outline how the various departments should work together via a scenario.
Threat Intelligence and Online Brand Protection
MITRE PRE-ATT&CK: How your brand can be used to gain a foothold in your network
Before walking through a scenario, it’s worth looking at how the brand might be targeted by a threat actor – and we’ll use the MITRE ATT&CK (and PRE-ATT&CK) framework, something we typically embed into Digital Shadows’ research where we can, with the goal to provide actionable intelligence.
PRE-ATT&CK, in particular, has a strong social media flavor to many of the tactics and techniques. For example, look at this list below (which is by no means exhaustive) and try to imagine a world in which social media would not be an absolute goldmine for attackers.
Of course, social media often plays a critical role beyond the PRE-ATT&CK stage. Gaining access to social media accounts may be a goal itself. Notably, this occurred to Barcelona FC’s Twitter account, when the hacking collective OurMine took over the social media account, using a third-party social media tool.
Online Brand Protection Scenario
Using the MITRE frameworks, in the previous section, has shown us how the brand may be exploited by an attacker. However, for the purposes of this section, we’ll adopt a hypothetical scenario to outline how a brand can be managed and protected by the organization.
**!103u7w1xaH3qeaBxTLI0Bu! **
Figure 4: Hypothetical timeline of events for Molnnet Brand Protection campaign
STAGE 1: Planning
To illustrate the best practices of brand protection let’s consider the following hypothetical scenario, involving the same dummy global paper supply company, Molnnet.
Sept 2020: the marketing team for Molnnet launches a global digital media and advertising campaign to build awareness of the release of the new product, PaperLite. This product will also be showcased at the global trade show, Paper Expo April 2021, which gathers thousands of suppliers and buyers across the world.
Months prior to Paper Expo April 2021, the marketing team launches a press release, in addition to several digital media and TV advertisements. On the software development side, a brand new mobile app is being developed which will enable Molnnet customers to purchase supplies with less friction. The mobile app will also be supported by a new website, available via desktop.
Consequently, Molnnet’s brand exposure has increased – and so too has its attack surface. The brand is being googled as a result of the marketing campaigns, and website traffic increases threefold. On top of this, the holiday season means that customers are purchasing more than usual, as they need paper supplies to wrap presents – this means more visitors to the products page and online orders doubling in sales.
Sept 2020: the marketing team informs the security department of the upcoming campaigns, monthly meetings are held to update various stakeholders of the various activities. In return, the security teams have a departmental meeting, every week, to update one another of various developments.
STAGE 2: Security team monitors the external environment
Now that the security department is aware of the upcoming campaign and its desired outcomes, Molnnet monitors the external environment, using a digital risk management tool, Digital Shadows SearchLight. In order for the tool to monitor effectively, company assets are added, which increases coverage.
*!47FItTo6IOqMUu9h8eSwe2! *
Figure 5: Molnnet reviews company assets
The Molnnet security team reviews the assets internally, discussing what their team wishes to monitor – but also consults the marketing team for the assets that they would like to monitor for. Company assets include domains (including test and staging domains), IPs, brand names, code snippets – Molnnet’s security team populates all the assets.
The marketing team ensures the brand names are populated, but also makes a special request to add a staging domain and secret project name based on the upcoming marketing campaign. The staging domain is used by the marketing team’s in-house web developer, who is currently building a dedicated site for Paper Expo 2021. This website should not be publicly accessible according to the marketing department – so monitoring for it is critical.
STAGE 3: Detection
All assets have been reviewed and populated into the digital risk solution: now 24/7 monitoring begins. Within the first few weeks of monitoring, alerts trickle through and the internal Molnnet security operations analysts observe and triage. The built-in risk scoring functionality enables the internal SOC analysts to prioritize and assess risk.
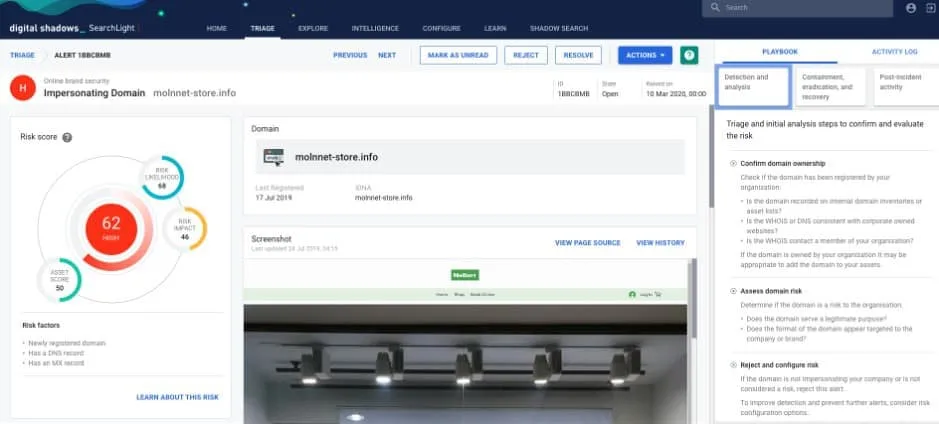
Figure 6: Impersonating domain detected for Molnnet asset
One SOC analyst’s attention is grabbed when an incident comes through: a mention of client systems information on github public repository. Already this doesn’t look like it should be there. The SOC analyst investigates the detected incident, ascertains that the system’s information, which contains username and an encrypted password for an internal website (jira.molnnet.com), is public when it should not be. Immediately, the SOC analysts grab their manager and inform him or her of the development, which results in an escalation to the marketing, legal, and compliance teams.
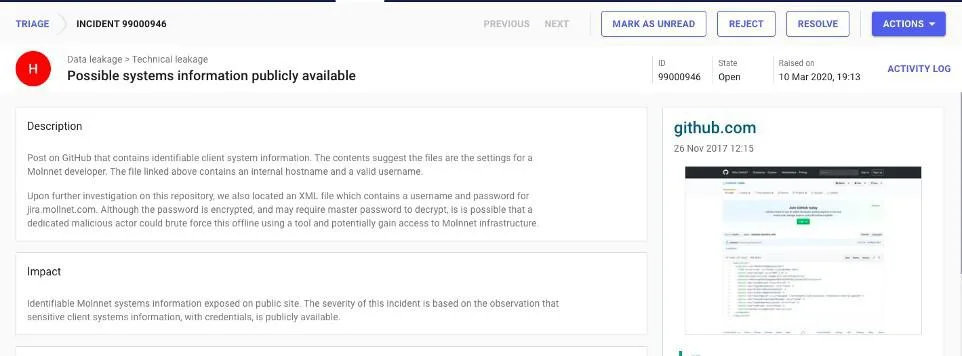
Figure 7: Impersonating domain detected for Molnnet asset
Stage 4: Actioning
Having escalated the incident to the marketing team and conferred internally, it is deemed that the GitHub incident that was detected by Digital Shadows is in fact a true positive.
Within the hour of escalating, the SOC analyst focuses on removing the exposed content. There are two parts to this: First, an employee has publicly committed the domain to the code repository – so the SOC analyst must contact the software engineering department to identify them and make them aware of this case. Second, the content needs to be removed, so the SOC analyst uses the built-in template to initiate the hosting site (GitHub), to issue a content removal on the basis that it shouldn’t be there.
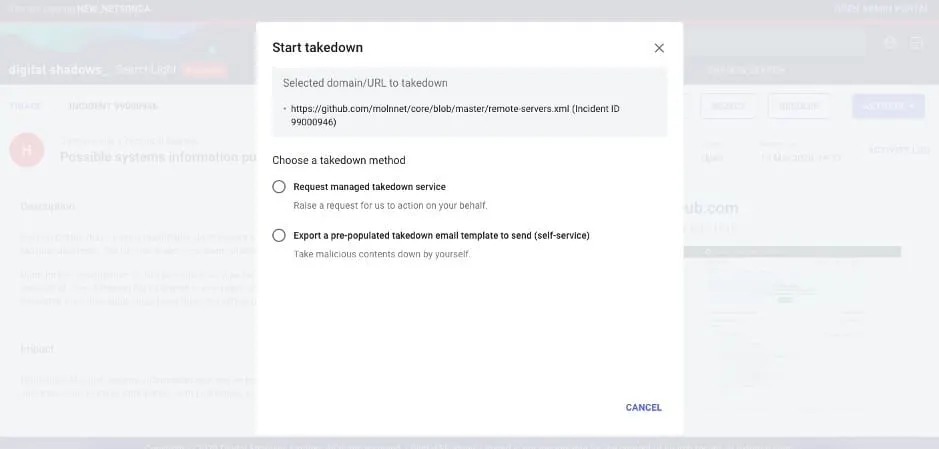
Figure 7: Molnnet SOC analyst initiates a takedown
In the meantime, the information security manager works with the marketing, legal, and compliance teams to discuss the wider implications of the exposure including the system’s information, which could be used to access Molnnet’s infrastructure, having been publicly listed for approximately 3 hours at the time of detection.
While the various stakeholders confer, the incident response team have issued a takedown to Github. At the same time, the SOC team identifies the software developer who initiated the commit publicly.
It unfolds that the software developer had unintentionally exposed the system’s information, along with username and encrypted passwords. The team issues the data exposure policy book, reminding that all sensitive company data, even systems information, must be made to private repositories on Github, not public as this breaches company policy.
Further efforts are also made to ensure that the IP associated with the website in the github post (jira.molnnet.com) would be whitelisted to ensure only Molnnet employees can access the site.
As a precaution, the password associated with the website, although encrypted, is reset.
Overall, the impact was largely minimal, and business operations were minimally disrupted. Though this did have the potential to disrupt had it gone undetected for longer.
4 Essentials of a Good Online Brand Protection Plan
With the proliferation of the digitized economy, which sees brands become bigger online, it is essential to have the following:
Identify key stakeholders: It’s recommended that an organization create a path for escalation so these various stakeholders can be pulled in when required. Such a path of escalation could be tracked in handbook policy.
Monitor business assets and review configuration: Identify key assets, as these are an organization’s “crown jewels”. This can be achieved by detecting whether they’re exposed across the open, deep, and dark web. Next, ensure you continuously review and update assets.
Create internal playbooks with scenario planning: All the aforementioned recommendations can go out the window without practice and training. Test response and refine processes by undertaking scenario planning and running exercises. Ensure all the key stakeholders are involved throughout this too.
Brand attack awareness: Establish a policy for which all employees should be able to recognize and avoid brand attacks where possible. This can extend to establishing strong password policies for stakeholders managing social media accounts to avoid social media account takeover. Such a policy shouldn’t be episodic, it should be ingrained into the company culture: regular brand awareness training sessions, online training and/or documents listing the potential impact – but more importantly, how employees can detect and prevent it.
4 Free Tools to Get Started and Build Maturity
At Digital Shadows, we speak to a large number of security teams about their approaches to Online Brand Protection. You’ll be unsurprised to learn that this fluctuates from organization to organization – some have really well-defined processes in place that involve multiple departments, whereas others ignore it and leave the issue of brand to the marketing or brand team. Based on these conversations and observations, it’s possible to outline five stages of maturity for Online Brand Protection.

Figure 8: Maturity model for Online Brand Protection
For those just getting started on the journey, we’ve outlined some free tools to get started below:
DNS Twist.https://github.com/elceef/dnstwist
Phish Catcherhttps://github.com/x0rz/phishing_catcher
URLCrazyhttps://tools.kali.org/information-gathering/urlcrazy
Looking to learn more about how we help discover attackers impersonating your domains, social accounts, and mobile applications? Learn more about Digital Risk Protection here.




